Dr Rajiv Desai
An Educational Blog
Spying
Spying:
_
Clockwise from top left: Orlin Roussev, Katrin Ivanova, Ivan Stoyanov, Biser Dzhambazov, Vanya Gaberova and Tihomir Ivanchev. These six Bulgarians have been sentenced to lengthy prison terms for spying for the Kremlin in the UK and across Europe.
___
Section-1
Prologue:
The old phrase ‘gentlemen don’t read each other’s mail’ was unfortunately the dominant U.S. attitude before the Second World War — with catastrophic consequences at Pearl Harbor. … America learned the hard way: In reality, that was what everyone else was doing, and America was being not only naïve, but putting itself at risk by not doing so. Throughout history, espionage has shaped the dynamics of power, politics, and security. Throughout history, adversaries have routinely taken their competitive efforts beyond the battlefield. Nazi spies during World War II tried to penetrate the secrets behind American aviation technology, just as Soviet spies in the Cold War targeted American nuclear and other military secrets. As nations vie for dominance, the sophistication of espionage tactics and techniques has evolved, reflecting the complexities of modern conflicts and technological advancements. Understanding these methods is crucial for comprehending the underlying motivations and strategies of intelligence agencies.
_
Hidden deep within the daily workings of governments and civilizations is a secret world of mystery, danger, and intrigue. A world where deception is a form of art. Where people are never who they say they are. Where the tiniest observation has the power to save an empire or spark a global war. Welcome to the world of the spy—a world that most of us associate with popular fiction and film but the true story of which is more fascinating, surprising, and important than you could possibly imagine. For thousands of years, espionage and covert operations have been powerful but shadowy forces. Much of world history has been shaped by the dramatic exploits of men, women, and organizations devoted to the perilous tasks and undercover missions that are part of a spy’s life.
Consider that covert operations have played critical roles in
- epic conflicts such as the Trojan War, the Crusades, World War II, and the War on Terror;
- political upheavals such as the American, French, and Russian revolutions;
- cultural moments such as the quest to colonize the New World, the 19th-century expansion of empires;
- race to build the world’s first atomic bomb.
Indeed, to truly comprehend the forces at work in international politics, whether at the dawn of civilization or among today’s sophisticated world powers, one must understand the secret role of espionage and the shadowy world of covert operations.
_
Spying means to watch someone or something secretly, often in order to discover information about him, her, or it. Espionage or spying is the act of obtaining secret or confidential information (intelligence). The practice is clandestine, as it is by definition unwelcome. In some circumstances, it may be a legal tool of law enforcement and in others, it may be illegal and punishable by law. Espionage has existed for a long time. In fact, it is often referred to as the “world’s second oldest profession.” Mentions of spies can be found in the Bible, in ancient Greece, and in ancient China. Espionage continued to persist and evolve, with now over a hundred global intelligence agencies responsible for related activities, operated by countries across the economic development spectrum. The art of spying has a peculiar dual identity. On one hand, states openly acknowledge their own intelligence agencies and deem their activities legitimate and necessary to protect national security. On the other hand, states aggressively denunciate foreign espionage and criminalize any domestic support of foreign espionage. As one commentator puts it, the mentality appears to be: “we and our friends merely gather information; you and your type violate sovereignty.” International law struggles with clarity in the face of this strange “doublethink” tension, plagued with seemingly ideological contradictions.
_
Espionage traditionally refers to human spies and spying. Intelligence is much broader. It can mean human intelligence, but it also can mean technical intelligence operations, like signals intelligence, or code-breaking, or imagery intelligence. Intelligence is not mysterious: It is secret information, which, by definition, requires secret means to obtain. Sometimes there’s not that much difference between publicly available information in The New York Times, for example, or in the Harvard Gazette, and in intelligence briefings — and when that happens, policymakers rightly ask what’s the point of intelligence briefings if they can read the same or similar information in the press? The purpose of intelligence is to provide policymakers, decision-makers, with something extra — something they can’t obtain, read, or see on the news or some other way. So, at its most basic, the purpose of intelligence is to help policymakers make their decisions. It’s to be able to know about enemies’ intentions and capabilities, and it is to be able to know about threats on the horizon.
_
Like many other fields, espionage is being transformed by the “cyber” prefix or descriptor. Cyber space simultaneously makes offensive information gathering more valuable and cyber defense protections more necessary because of the sheer volume of data now available. Cyber intrusions have become a frequent concern and are aimed at a diverse range of targets. There are now more than 100 daily cyber intrusion attempts on NATO headquarters, and over 1,000 daily cyber intrusion attempts on U.S. military and civilian networks. These attacks originate from over 100 countries, showing that this is a dispersed phenomenon, not restricted to a handful of capable states. The 2016 hacking of the U.S. Democratic National Committee’s (DNC) emails, allegedly by Russian actors, highlights cyber intrusions’ creeping invasion into significant public matters. Cyber espionage can lead to the theft of trade secrets, intellectual property, and sensitive data, impacting various industries and organizations. Knowledge is power, especially in the hands of your competitors. Information about your company, its products and services, finances, sales, and marketing strategy is a weapon in the ruthless world of espionage in business. That’s why it’s important to ensure that your organization’s data is well-protected.
_
Magic and espionage are really kindred arts. In magic, as in spycraft, nothing is quite as it seems. Deception and illusion are tricks of both trades. Distracting the adversary, concealing intentions, donning disguises, making evidence disappear, and escaping unnoticed… CIA has been applying the magician’s craft to the world of espionage for decades. The arts of misdirection, sleight-of-hand, and recognition signals are all conjurers’ tricks used for covert intelligence operations. Tony Mendez, CIA’s former Chief of Disguise championed the use of illusions in a variety of intelligence operations during the Cold War. The most famous operation was probably ARGO, which was made into a Hollywood blockbuster. Mendez—along with his close associate Ed Johnson—snuck six Americans out of Iran by disguising them as a Hollywood film crew. Any sufficiently advanced technology is indistinguishable from magic. The tricks and techniques needed to create believable deceptions will inevitably change as technology evolves. Things like artificial intelligence, ubiquitous surveillance, and biometric data are already changing the intelligence landscape. Just as the art of the magician has evolved over the years—incorporating more advanced technologies with the tried-and-true techniques of illusionists’ past—so too does the art of spycraft.
_
The U.S. government, through the National Security Agency, spied on millions of Americans, their phone calls, and their Internet interactions, allegedly looking for connections to “terrorists.” Former intelligence worker Edward Snowden revealed himself as the source of documents outlining a massive effort by the NSA to track cell phone calls and monitor the e-mail and Internet traffic of virtually all Americans. He says he just wanted the public to know what the government was doing. “Even if you’re not doing anything wrong, you’re being watched and recorded,” he said. He had “a very comfortable life” that included a salary of roughly $200,000, a girlfriend with whom he shared a home in Hawaii, a stable career, and a family he loves. “I’m willing to sacrifice all of that because I can’t in good conscience allow the US government to destroy privacy, internet freedom and basic liberties for people around the world with this massive surveillance machine they’re secretly building.” Russia granted Snowden the right of asylum and became naturalized in 2022. He has been charged with three felony counts, including violations of the U.S. Espionage Act, over the leak.
_
Military analyst Daniel Ellsberg leaked the 7,000-page Pentagon Papers in 1971. The top-secret documents revealed that senior American leaders, including three presidents, knew the Vietnam War was an unwinnable, tragic quagmire. Further, they showed that the government had lied to Congress and the public about the progress of the war. Ellsberg surrendered to authorities and was charged as a spy. During his trial, the court learned that President Richard Nixon’s administration had embarked on a campaign to discredit Ellsberg, illegally wiretapping him and breaking into his psychiatrist’s office. All charges against him were dropped. Since then, he has lived a relatively quiet life as a respected author and lecturer.
_
There’s an old saying in intelligence business that there are never policy failures, there are only intelligence failures. The terrorist attacks of September 11, 2001 was intelligence failure when intelligence community missed opportunities to pool and analyze information across agencies leading up to the attacks. The withdrawal from Afghanistan was an intelligence failure. Not only did the CIA and other U.S. intelligence agencies wildly underestimate the speed of the Taliban advance, they also appeared to have been blind to the political dealings of the Taliban and the military prepositioning the Taliban had achieved. Meeting in the White House in 2002, CIA director George Tenet told President Bush, the evidence that Iraq possesses weapons of mass destruction amounts to a slam dunk case. And of course, America invaded the next year, and WMDs weren’t there. My life is a classic case of intelligence failure. American leaders have asked CIA to spy on me and Indian leaders have asked Indian intelligence agencies to spy on me. So, I decided to research ‘Spying’ to learn about the subject and this article is a tribute to countless innocent people worldwide subjected to spying by their governments.
______
______
Glossary:
Agent:
A person unofficially employed by an intelligence service, often as a source of information. An agent is another word for a spy: someone who volunteers or is recruited to pass secrets to an intelligence agency, sometimes taking risks to spy on their own country. They may be recruited through money, ideology, coercion, greed, or for another reason, such as love. They trust their handler (a professional intelligence officer) to protect them. You’ll find agents in other parts of government as well, but that’s a different use of the term: FBI agents and special agents, for example, work in law enforcement.
Asset:
A clandestine source or method, usually an agent.
Birdwatcher:
Slang used by British Intelligence for a spy.
Black Operations:
Covert operations that are not attributable to the organization performing them.
CI:
Counterintelligence
CCI:
Cyber counterintelligence
CIA:
Central Intelligence Agency; U.S.’s foreign intelligence gathering service.
Clandestine Operation:
An intelligence operation designed to remain secret.
Code:
A system for disguising a message by replacing its words with groups of letters or numbers.
COMINT:
All intelligence gathered from intercepted communications.
Counterintelligence:
The business of thwarting the efforts of foreign intelligence agencies; includes but is not limited to spy-catching. Spy agencies need to play defense. Counterintelligence activities, such as espionage or covert action, aim to prevent other spies from obtaining secrets, and to protect secrets and security against the efforts of other spies.
Cover:
The purported occupation or purpose of an agent; it must be consistent with the agent’s background and presence in the target area.
Dead Drop:
A secret location where materials can be left for another party to retrieve.
Double Agent:
A spy who pretends to act as a spy for one country or organization while in fact acting on behalf of an enemy. A double agent is essentially someone who works for two sides. In the intelligence world, a true double agent is loyal to one side before being “turned” and transferring loyalties to the other side.
Espionage:
The practice of spying or using spies to obtain secret or confidential information about the plans and activities of a foreign government or a competing company.
FBI:
Federal Bureau of Investigation; U.S.’s domestic counterintelligence service and federal law enforcement agency.
FSB:
Federal’naya Sluzhba Bezopasnosti in Russian which translates to Federal Security Service in English
Handler:
A case officer who is responsible for handling agents in operations.
Honey Trap:
Slang for use of men or women in sexual situations to intimidate or snare others.
HUMINT:
Intelligence collected from human sources.
Intelligence (intel):
In the spying world, intelligence means information collected by a government or other entity that can help guide decisions and actions regarding national security.
IC:
Intelligence Community
IO:
Intelligence Officer
IMINT:
Imagery intelligence.
Intelligence Officer:
Intelligence officers are professionals trained by their governments. Called case officers, operational officers, or handlers, they run operations and recruit and manage the actual spies.
KGB:
Komitet Gosudarstvennoy Bezopasnosti in Russian which translates to the Committee for State Security in English
MASINT:
Measurement and signature intelligence; a form of technical collection that uses signatures that do not fit into the traditional scope of IMINT and SIGINT.
MI5:
The British domestic counterintelligence service; officially known as the Security Service.
MI6:
The British foreign intelligence service; officially known as the Secret Intelligence Service.
MI5 focuses on domestic security and works closely with local law enforcement to handle threats on home soil. MI6, on the other hand, is a foreign intelligence agency. Its role is to gather information from outside the UK, focusing on international threats.
Mole:
An agent of one organization sent to penetrate a specific intelligence agency by gaining employment; a term popularized by John Le Carre.
NSA:
National Security Agency; branch of the U.S. Department of Defense responsible for ensuring the security of American communications and for breaking into the communications of other countries.
OSINT:
Open source intelligence; intelligence information derived from publicly available sources.
PHOTINT:
Photographic intelligence, usually involving high-altitude reconnaissance using spy satellites or aircraft.
Pig:
Russian intelligence term for traitor.
Raven:
A male agent employed to seduce people for intelligence purposes.
Shoe:
A false passport or visa.
SIGINT:
Signals intelligence; consists of COMINT (communications intelligence) and ELINT (electronic intelligence).
SIS:
Secret Intelligence Service; the official name of Britain’s MI6.
Sleeper Agent:
Agent living as an ordinary citizen in a foreign country; acts only when a hostile situation develops.
Spilling:
The key concept in defining spilling is lack of intent. Spies engaged in espionage have specific goals in mind, whereas spilling is the inadvertent, unintended disclosure of information to uncleared environments, organizations, or people.
Spy:
A “spy” is a person who secretly gathers information, often for a government or organization. They may work undercover, using deception and secrecy to collect intelligence about another country, organization, or even an individual. Of course, the term “spy” also is used much more broadly, often to refer to anyone or anything connected to “spy agencies” (from intelligence analysts to hidden cameras), or any activity done secretly (spy missions, use of malicious computer software).
Spycraft:
“Spycraft” generally refers to the techniques, skills, and methods used in espionage and intelligence gathering. It encompasses a wide range of activities, from traditional methods like surveillance and disguise to more modern techniques involving technology and cyber warfare.
Spymaster:
The leader of espionage activities, and an agent handler extraordinaire.
TECHINT:
Technical intelligence are gathered from analysis of weapons and equipment used by the armed forces of foreign nations, or environmental conditions.
Timed Drop:
A dead drop that will be retrieved by a recipient after a set time period.
_____
_____
Section-2
Introduction to spying:
The world of spies is an ancient art, born from the need to obtain information, and has become a fundamental pillar of national security and business strategy in the Modern society. This field extends beyond the shadows and dark alleys that popular culture has led us to imagine; it has merged with advanced technology and taken a seat in cyberspace, often changing the course of history from behind a screen. The Spies, the enigmatic figures at the center of this universe, are highly-skilled individuals who can perform in a variety of roles and circumstances. They may be undercover government agents, secretly working to protect their country, or they may be corporate spies, seeking competitive advantages for their companies. Some spies may even operate independently, selling their skills to the highest bidder. At its core, espionage deals with the acquisition of secret information and its use or protection. However, more than that, it is a delicate and dangerous dance that requires cunning, wits and courage. For a spy, there is no margin for error. Each movement must be measured, each decision weighed. And while the stakes are high, the rewards are too: the information a spy can obtain can change the course of a war, decide the fate of a company, or even alter the direction of history.
_
Espionage or spying is the act of obtaining secret or confidential information (intelligence) from non-disclosed sources or divulging of the same without the permission of the holder of the information for a tangible benefit. A person who commits espionage is called an espionage agent or spy. Any individual or spy ring (a cooperating group of spies), in the service of a government, company, criminal organization, or independent operation, can commit espionage. The practice is clandestine, as it is by definition unwelcome. In some circumstances, it may be a legal tool of law enforcement and in others, it may be illegal and punishable by law. It is a subset of intelligence gathering, which otherwise may be conducted from public sources and using perfectly legal and ethical means. It is crucial to distinguish espionage from intelligence gathering, as the latter does not necessarily involve espionage, but often collates open-source information. Espionage is often part of an institutional effort by a government or commercial concern. However, the term tends to be associated with state spying on potential or actual enemies for military purposes. Spying involving corporations is known as industrial espionage. One of the most effective ways to gather data and information about a targeted organization is by infiltrating its ranks. This is the job of the spy (espionage agent). Spies can then return information such as the size and strength of enemy forces. They can also find dissidents within the organization and influence them to provide further information or to defect. In times of crisis, spies steal technology and sabotage the enemy in various ways. Counterintelligence is the practice of thwarting enemy espionage and intelligence-gathering. Almost all nations have strict laws concerning espionage and the penalty for being caught is often severe. However, the benefits gained through espionage are often so great that most governments and many large corporations make use of it.
_
“Espionage by definition is intended to occur without detection;” therefore, it is safe to assume that defining and regulating it brings significant complications (Deeks 2015, 314). The forms and aims of espionage differ significantly, especially with the advent of technology; however, espionage can roughly be defined as a “tool for the execution of policy as well as a tool to inform policy” (Scott and Jackson 2004) This definition adequately splits espionage into its two categories: covert operations (a tool for the execution of policy) and intelligence (a tool to inform policy).
The first category, covert operations, consists of active operations and cyber operations, which are actions a state takes to influence or affect a foreign sovereign that lack public endorsement by the state and usually remain classified (Fatouros 1976, 193; Jackamo 1992, 992). The forms covert operations take can be divided into three classifications: coercive covert operations, political action, and propaganda (Treverton 1988, 13). The methods of these types of covert operations differ, primarily through the use of active forces and the use of cyber programming, which have an effect on the aim of the forms they take, but ultimately have either a forceful or influential element.
The second category of espionage, covert intelligence, can also be divided into two strands: collection of information and analysis of that information (Radsan 2007, 599; Sulmasy and Yoo 2007, 625). With respect to international law, the initial collection of information is what raises serious and significant legal questions, making it, rather than analysis, of utmost importance as well as highly contested (Sulmasy and Yoo 2007, 625). Intelligence collection itself can be divided into three variants: human intelligence (HUMINT), such as active agents collecting information through networking and interaction; signals intelligence (SIGINT), such as electronic surveillance or communication interception; and photographic or imagery intelligence (IMINT), such as satellite reconnaissance (Sulmasy and Yoo 2007, 625; Chesterman 2006, 1074; Jackamo 1992, 935). These methods of intelligence collection provide the information states use to guide its decision-making, plan its foreign policy, and predict, influence, or understand the future behavior of its constituents (Warner 2009, 9; Chesterman 2006, 1074; McDougal et al. 1973, 365). Therefore, it can be understood that intelligence is an important part of state practice, and the secrecy attached to it, further implies that intelligence is a crucial part to informing state decision-making.
_
People are fascinated by espionage. The sheer volume of fiction and non-fiction books and movies dedicated to the subject of spying attests to this, as well as private citizens’ enthusiasm for news reports on cases of espionage and their thirst for mere fragments of insight into those engaged in it. This is probably in no small part due to the fact that so much of what we consider espionage occurs in a world inaccessible to most people. Even for those who have years of service in the intelligence community, however, one question remains difficult to fully explain: Why spy? History shows that most countries have at one time or another made the decision to seek out secret information regarding other countries, groups, or even their own people through clandestine means…that is, to spy. Still, except for irrational behavior on the part of unaccountable dictators, the decision to spy is usually based on the consensus of a country’s political leadership regarding national security goals and how to achieve them. This consensus decision may be complex but still more or less discernible to outsiders.
_
Spies usually come in two main types: those that gather intelligence themselves and those who recruit others to gather information for them. The former are typically nurtured and watched over by a handler (intelligence officer). The latter typically have worked under cover as diplomats, journalists and foreign businessmen. Spies of the type portrayed in movies traditionally adopted a cover identity that was not their own and lived a life of lies. The best spies are often inconspicuous, scholarly types that are comfortable chatting up potential recruits at bars and parties and establishing friendships with them. Good spies also have skills in observation, analysis and surveillance. Double agents are spies who work for both sides, usually pretending to be a spy for one side but actually working for another side. Moles are double agents whose identity is so secret and his access and position are so deep that the analogy is made to an underground-living mole. On Spying today, Joe Sharkey wrote in the New York Times: “Spying has become just another business-travel tool, thanks to cheap, comprehensive technology and to a soaring demand for dependable real-time information about day-to-day conditions in the world.
______
______
Difference between espionage and spying:
Definitions:
Espionage:
– Referring to the act of gathering secret information or intelligence by a government or organization.
– Talking about the use of spies or undercover agents to obtain confidential information.
– Describing the practice of covertly monitoring or infiltrating an enemy or rival nation for strategic purposes.
Spying:
– Referring to the act of secretly observing or monitoring someone or something.
– Talking about the use of undercover agents or informants to gather information.
– Describing the practice of covertly obtaining sensitive information or trade secrets from a competitor or adversary.
List of Similarities:
- Both involve the gathering of information or intelligence.
- Both can be carried out by individuals, organizations, or governments.
- Both are often done secretly or covertly.
- Both can have legal and ethical implications.
- Both can be used for strategic or competitive advantages.
List of differences:
- Scope: Espionage is typically associated with government or national security matters, while spying can refer to a broader range of activities, including corporate or personal matters.
- Purpose: Espionage is often carried out for national security or political reasons, while spying can be motivated by various factors, such as personal gain or curiosity.
- Agents: Espionage usually involves the use of trained agents or operatives, while spying can involve anyone who gathers information without authorization.
- Legality: Espionage can be legal or illegal depending on the circumstances and jurisdiction, while spying is generally considered illegal or unethical.
- Connotation: Espionage has a more formal and serious connotation, while spying can have a more playful or mischievous connotation.
In this article, the terms espionage and spying are used synonymously.
_
Difference between a detective and a spy:
A spy collects secret information, often with a motive, while a detective investigates crimes to uncover the truth and bring perpetrators to justice. Spies prioritize secrecy and may betray trust for their own or their organization’s gain, whereas detectives uphold the law and are generally motivated by a desire to uphold justice.
Key Differences:
- Focus: Spies focus on gathering information, often clandestinely, while detectives focus on solving crimes.
- Motive: Spies may have motivations like ideology, greed, or coercion, while detectives are primarily motivated by a desire for justice.
- Ethical Considerations: Spies may be involved in activities that violate ethical principles, such as betraying trust or using deceptive tactics, while detectives are bound by ethical guidelines and the law.
- Role in Society: Spies operate in the shadow of intelligence agencies, while detectives work within the legal framework of law enforcement.
Although work of detective may involve spying, detectives are not spies.
_
Intelligence officer versus spy:
One problem is that in both news reporting and English vernacular, the word “spy” is used to describe both intelligence officers and those they recruit but the intelligence officer and the recruited spy are not the same. Perhaps the most crucial difference is that an intelligence officer has chosen a career. A potentially dangerous career for a few, but a job nevertheless. Traditionally, intelligence officers have often enjoyed diplomatic cover, providing them with immunity from arrest and prosecution. Some have served without such immunity, and indeed been sentenced to lengthy prison terms. But they have often been released to their home countries well before the end of their mandated terms by swapping them for people imprisoned by the other side. Such was the fate of Soviet intelligence officer Konon Molody, also known as Gordon Lonsdale in the 1960s, who was returned in a prisoner exchange after serving a mere three years of his 25-year sentence. In 2010, Anna Chapman, a Russian intelligence agent and model, and her compatriots were exchanged for ten Russians (among them Sergei Skripal, who would later barely escape a Russian assassination plot).
Intelligence officers have been selected on the basis of their talents and then trained to hone their skills. In particular, those tasked with recruiting sources tend to be socially adept, likeable and smooth talkers. For example, Richard Sorge, a journalist with a doctorate in political science who was secretly a Soviet intelligence officer, used his German roots to successfully infiltrate German diplomatic circles in Tokyo in the 1930s. A bit like James Bond, he was described as having an irresistible charm. Sorge became close friends with the German military attaché (later ambassador) while simultaneously seducing his wife. Sorge also used to race around Tokyo on a motorcycle, in another reflection of the overlap between truth and fiction.
Recruited spies, on the other hand, are selected solely on the basis of what kind of information they have access to and are willing to hand over. Thus, recruited spies are typically expected to betray their own countries. Even if there is moral justification in some cases, such as Ryszard Kuklinski’s handing over of Warsaw Pact military secrets to the west during the cold war, it remains a more extreme choice than that of the career professional.
______
______
One of the most effective ways to gather data and information about the enemy (or potential enemy) is by infiltrating the enemy’s ranks. This is the job of the spy (espionage agent). Spies can bring back all sorts of information concerning the size and strength of an enemy army. They can also find dissidents within the enemy’s forces and influence them to defect. In times of crisis, spies can also be used to steal technology and to sabotage the enemy in various ways. Counterintelligence operatives can feed false information to enemy spies, protecting important domestic secrets, and preventing attempts at subversion. Nearly every country has very strict laws concerning espionage, and the penalty for being caught is often severe. However, the benefits that can be gained through espionage are generally great enough that most governments and many large corporations make use of it to varying degrees. In the past, the focus of espionage was typically on obtaining political and military intelligence. With the increase in technology the focus has broadened to include such things as communications technologies as well as energy, scientific research, aviation and other fields.
_
Following the end of World War II, the UKUSA Agreement marked a new era of intelligence operations comradeship. The agreement currently involves Australia, Canada, New Zealand, the United Kingdom, and the United States, which are collectively known as the Five Eyes. These five powers agreed to share their sensitive intelligence, and in turn, probably not spy on each other. This agreement was kept so secret that it wasn’t made public until 2010, almost 60 years after its founding. But for that whole time, these five nations, and specifically the UK and the US, have worked together and shared their intel for the “greater good.” It was revealed in 2013 that the members of the UKUSA Agreement very well might spy on each other, but not necessarily out of mistrust. Since there are many laws prohibiting governments from spying on their own citizens, some countries have used shady workarounds to gather such intel. Max Boot, a writer for Commentary said, “this intelligence sharing allows them to do an end-run around prohibitions on domestic surveillance: the Brits can spy on our citizens, we can spy on theirs, and then we can share the results.” In 2013 the National Security Agency denied these accusations, saying, “any allegation that NSA relies on its foreign partners to circumvent U.S. law is absolutely false. NSA does not ask its foreign partners to undertake any intelligence activity that the U.S. government would be legally prohibited from undertaking itself.”
_
Espionage is the practice of obtaining confidential information through spying; a practice that often employs covert, clandestine, illegal or unethical behavior. Spies have been used to create political, military, and economic advantage through most of history. Espionage in the military is typically referred to as “military intelligence,” while espionage in the corporate world is termed “industrial espionage.” Most countries have both military intelligence organizations as well as civilian espionage and intelligence organizations. As the world has advanced and human society has changed, the separation into “friend” and “foe” has blurred and changed, and thus the role of espionage has also changed. Ultimately, it may be that nations and organizations find themselves able to cooperate in achieving common goals for the good of humankind, rather than using unethical means to steal each other’s secrets in order to further their own self-centered desires.
_
The use of espionage dates back well into ancient history. The Hebrew Bible describes the Hebrews’ use of espionage in the Book of Joshua with the story of Rahab, a prostitute who harboured two Hebrew spies. Ancient Egyptian hieroglyphs and papyri describe the existence of court spies. Spies were also prevalent in the Greek and Roman empires. In Asia, the importance of deception and subversion were discussed by Chinese military tactician Sun Tzu around 500 B.C.E. in his famous work The Art of War. Two hundred years later, The Arthashastra, an ancient Indian treatise on statecraft, emphasizes the importance of espionage as a tool for national security and maintaining control. Ninjas were often employed as mercenary spies in feudal Japan, and were known for their skill at infiltrating the enemy. In Europe during the Middle Ages, espionage played a large role in both The Crusades and the Inquisition. During the Renaissance, the political philosopher Niccolo Machiavelli strongly advocated the use of espionage by the ruling class. Elizabethan England was known for the effectiveness of its espionage system, which employed linguists, scholars, and scientists. From the eighteenth century onwards, espionage gained even more importance. Industrialization, colonialism, and complicated world politics all fueled the quest for information. Informants during the French Revolution were used to track down traitors for trial and execution. Colonial governments used espionage to quell uprisings. The art of espionage was transformed as technology and information systems grew. Inventions like the camera and telegraph revolutionized the clandestine collection and transmission of information, and gave rise to new levels of cryptography and gadgetry. Cameras were made smaller and smaller, and new means were constantly being developed to help spies covertly collect intelligence.
_
Modern Espionage:
World War I was responsible for a marked change in the development and scope of many countries’ espionage programs. Due to the complicated global political climate and numerous, often secret, allegiances between countries, espionage became a valuable and necessary means of obtaining essential information. It was not until World War I that some countries, including the United States, organized agencies solely devoted to the collection of intelligence. World War I also prompted the formation of the United States’ Espionage Act in 1917. The act imposed up to twenty years in prison and $10,000 in fines for interfering with the recruiting of troops or the disclosure of information relating to national defense.
_
World War II espionage activities were characterized by the use of cryptography, or codes. One of the most well known codes was the German “Enigma” machine, a machine first marketed commercially in 1923, but then adopted and refined by the German military, which used it extensively during World War II. The machine consisted of a series of rotors and electric wiring that were capable of producing a seemingly unlimited variation of codes. German U-boats were equipped with Enigma machines, and codes were changed daily. The British, with help from the Poles, cracked the “impenetrable” Enigma code, enabling them to defend against German attacks.
_
The Cold War involved intense espionage activity between the United States, the Soviet Union, and allies on both sides; in particular, information related to nuclear weapons secrets was sought after. During the Cold War, both American and Soviet intelligence agencies expanded considerably, employing thousands of agents. SIGINT technology also grew; satellites made real-time observations possible, and computers aided in the collection of information. No longer were agents the primary source of information; while there were still tasks only performable by humans, satellites and SIGINT were responsible for the penetration of the Soviet Union.
_
With the end of the Cold War, the focus of espionage changed. While the designations of “friend” and “foe” continued to blur for many countries, they became based more on economic relationships than historical and cultural alliances. Intelligence agencies continued to use espionage to collect intelligence on both friends and enemies, but the targets of spies changed from people to information. SIGINT systems continued to grow in complexity and ability. Programs like the United States’ “Echelon” have been used to monitor electronic communications, including mobile and international land-line calls and fax transmissions. The focus of espionage also shifted from governmental and political targets to terrorist organizations and threats.
_______
Organization:
A spy is a person employed to seek out secret information from a source. Within the United States Intelligence Community, “asset” is more common usage. A case officer or Special Agent, who may have diplomatic status (i.e., official cover or non-official cover), supports and directs the human collector. Cut-outs are couriers who do not know the agent or case officer but transfer messages. A safe house is a refuge for spies. Spies often seek to obtain secret information from another source.
In larger networks, the organization can be complex with many methods to avoid detection, including clandestine cell systems. Often the players have never met. Case officers are stationed in foreign countries to recruit and supervise intelligence agents, who in turn spy on targets in the countries where they are assigned. A spy need not be a citizen of the target country and hence does not automatically commit treason when operating within it. While the more common practice is to recruit a person already trusted with access to sensitive information, sometimes a person with a well-prepared synthetic identity (cover background), called a legend in tradecraft, may attempt to infiltrate a target organization.
These agents can be moles (who are recruited before they get access to secrets), defectors (who are recruited after they get access to secrets and leave their country) or defectors in place (who get access but do not leave).
Spies may also be used to spread disinformation in the organization in which they are planted, such as giving false reports about their country’s military movements, or about a competing company’s ability to bring a product to market. Spies may be given other roles that also require infiltration, such as sabotage.
Many governments spy on their allies as well as their enemies, although they typically maintain a policy of not commenting on this. Governments also employ private companies to collect information on their behalf such as SCG International Risk, International Intelligence Limited and others.
_
Spies are recruited in a number of ways. Some join the intelligence agencies of their home countries, receive training and move on to jobs within the agency. If their background and training fit a certain profile, they may be sent abroad to take on a cover identity. The best field agents are those with access to high-ranking officials or secret information in other countries. Spy agencies employ recruiters, people who target citizens of other countries who are likely to turn against their homeland and become spies. These defectors are invaluable spies, since they already have a cover and can provide information almost immediately. On rare occasions, no recruiting work is needed at all. Someone who wants to provide information walks in to an embassy or consulate and offers to become a spy. These walk-ins may be viewed with distrust as potential sources of misinformation from the enemy, but they can also become valuable spies.
Once a recruiter has recruited someone willing to gather information, the new spy will be put in contact with a controller. The controller will offer some training in spying methods and issue instructions for obtaining and transmitting information. The spy will usually have contact with no one else, never learning the names of any other spies or officials. This is known as compartmentalization. Each spy works within his own compartment, so if he is captured and interrogated, he can’t reveal vital information or the identities of other spies.
______
Espionage may seem like a far-fetched concept straight out of novels, but a real-world spy can cause serious harm to the government and its citizens. If someone gave classified documents or other secret information to the wrong person, that would result in various unpleasant outcomes:
- Weapons could fall into the wrong hands.
- Military efforts and national security programs could be compromised.
- Businesses could lose money.
- Government’s diplomacy, economic position, and state security would be weakened.
______
______
The Moscow Rules:
At the height of the Cold War, the CIA developed unwritten rules of engagement for their spies to use against the KGB known as The Moscow Rules. In his book, The Master of Disguise, Tony Mendez (CIA Chief of Disguise/Technical Operations Officer) wrote, “Although no one had written them down, they were the precepts we all understood. They were dead simple and full of common sense…”.
Here are the Moscow Rules:
-1. Assume nothing.
-2. Never go against your gut.
-3. Everyone is potentially under opposition control.
-4. Do not look back; you are never completely alone.
-5. Go with the flow, blend in.
-6. Vary your pattern and stay within your cover.
-7. Lull them into a sense of complacency.
-8. Do not harass the opposition.
-9. Pick the time and place for action.
-10. Keep your options open.
______
______
Open and Closed Societies:
During the Cold War it was easier for spies from the Soviet Union and its allies to work in the United States, Western Europe, and Japan than it was for American or other Western spies to gather information in the Soviet Union, China, and the Eastern-bloc nations. The Soviet Union was a closed society. Every area of public life was under government control, and private lives were always subject to government surveillance. All publications were monitored, and there was little access to information that the government did not want released. For any nation to set up an elaborate spy network within the Soviet Union was virtually impossible.
The United States, Canada, the nations of Western Europe, Japan, Australia, and New Zealand were and are open societies. Nearly all of their political, social, and economic activities are carried out under the glare of public scrutiny and media reporting. Open societies have few secrets except for those they find necessary to classify for security reasons. Under these conditions agents from hostile nations find it relatively easy to establish spy networks. Foreign spies operate out of embassies, consulates, business headquarters, and the United Nations. Spies working in an open society have access to all government and private publications. They are able to attend industrial expositions, business conferences, and meetings of scientific groups. They may even get jobs working for the government or in highly sensitive industries that do business with the Department of Defense. Many industries have poor internal-control, or security, procedures, thus enabling spies or their collaborators to steal blueprints, design plans, or pieces of equipment.
_
Stealing technology and getting it to the end user is a task that frequently calls for collaboration. Advanced technology that can have military applications is a prime target. One means of getting computers or other sophisticated machinery to the desired destination is to send it by way of a neutral country and then have it shipped on to its real destination. This often requires the assistance of an intermediary to make the actual purchase and to arrange for shipment. The intermediary can be a member of the firm that manufactures the technology, or it may be a middleman who deals with a number of firms.
In southern California in the late 1970s, an American named Christopher John Boyce stole satellite technology from TRW Corporation and sold it to the Soviets. He was caught and imprisoned only after the Soviets had the information. (A feature film entitled ‘The Falcon and the Snowman’ was made about Boyce’s exploits.) Another collaborator, William H. Bell, took designs in 1981 for fighter plane radar from Hughes Aircraft in California and gave them to an intelligence officer from Poland who then relayed them to the KGB. It is impossible to estimate the number of collaborators working for foreign governments. In 1985 alone a sizable number were caught in the United States. Of particular interest was a spy ring that included three members of one family: John Walker, Jr., a retired Navy warrant officer; his son Michael, a Navy yeoman; and his brother Arthur Walker, a retired Navy lieutenant commander. Other arrested spies included Sharon Scranage, a clerk in the CIA office in Ghana; Edward Howard, a former CIA officer; Jonathan Jay Pollard, an employee of the Naval Intelligence Service who was charged with spying for Israel; and Larry Wu-tai Chin, a retired CIA analyst who was accused of spying for China for 30 years.
______
______
Misconceptions about Spying:
-1. Countries only spy on their enemies.
Spies spy on bad guys. That seems like the no. 1 rule of spying. If the goal is to painstakingly obtain important intel about a foreign group, military, or government, the best use of all those resources and money would be if that intel involved a potentially dangerous country—not one of our closest allies. That hasn’t always been the case, though. Even the strongest of friendships comes with a healthy dose of paranoia. Countries spy on their allies all the time. This has been a practice since the dawn of espionage, and it’s never been more relevant than it is today. Intelligence operations are always most concerned with the safety of their own nation first, so if it’s in their best interest to spy on a country that’s technically their ally, so be it. The world was outraged when the U.S. was accused of bugging the German chancellor’s phone less than 10 years ago. But then it was later revealed that German intelligence officers had “accidentally” eavesdropped on the U.S. secretary of state. Charles Kupchan, professor of international affairs at Georgetown University, put it simply: “Everybody spies on everybody, including friends on friends.”
-2. All espionage is focused on national security.
Corporate espionage is very active forms of intelligence gathering; money is a pretty big motivator to commit crimes, after all. These are conducted for commercial purposes instead of national security, and can include stealing trade secrets, snooping around for info on industrial manufacturing techniques, nabbing customer datasets, getting a peek into research and development, and finding out about prospective deals.
-3. Espionage is a sophisticated, fool-proof government tactic.
Professional espionage is not without its failures. History is littered with very unintelligent uses of intelligence. During World War I, the British decrypting center Room 40 acquired useful intel about the enemy fleet during the Battle of Jutland. The intel was promptly ignored, and the battle, which could have been handily won, came to a costly draw. In 1941, Russian spy Richard Sorge gained intel about an approaching German invasion of Russia while sleuthing in Germany’s Embassy in Japan. Stalin rebuked the information, even going so far as to threaten anyone who believed it. This decision cost an untold number of lives.
-4. Spying, or espionage, is generally illegal under international law and the domestic laws of most countries:
Intelligence agencies like the CIA operate under a different framework that often involves a complex interplay of legality, national security, and international relations. Here are some key points to understand this situation:
(1. National Sovereignty: Each country has the right to protect its own national interests, which includes gathering intelligence. Countries often accept that espionage is a reality of international relations, even if it’s technically illegal.
(2. Legal Framework: The CIA operates under U.S. law, which provides it with the authority to conduct intelligence activities abroad. These activities are often justified under national security interests and are subject to oversight by the executive branch and Congress.
(3. Reciprocity and Tolerance: Many countries engage in espionage, and there is a tacit understanding that while spying is illegal, it is a common practice. Countries may turn a blind eye to espionage activities conducted by other nations, recognizing that they also engage in similar actions.
(4. Geopolitical Context: In a world where intelligence can provide significant advantages in diplomacy, military operations, and economic competition, countries often prioritize national security over strict adherence to laws against spying.
(5. International Agreements: There are some international treaties and agreements that address issues of espionage, but they are often vague and subject to interpretation. Countries may agree on certain norms but still engage in espionage activities.
In summary, while espionage is illegal in theory, in practice it is a widely accepted part of international relations, with intelligence agencies operating under specific legal and political frameworks that justify their actions.
______
______
The old way of spying has become obsolete and the culprit is technology:
The CIA’s decades-old spying model has been overtaken by technology, according to a former CIA officer who studied the matter for the agency. “The very idea of a globally dispersed cadre of undercover officers operating in the shadows, away from prying eyes, is obsolete,” said Duyane Norman, who retired in 2019 after a 27-year career at the CIA that included a special project examining the future of espionage. For Norman, the devastating penetrations of CIA spying networks in recent years were not mainly about incompetence or inattention. Instead, he believes they were the logical result of a technology revolution that makes it all but impossible to maintain false identities and disguise relationships. Norman’s view that the CIA’s traditional human intelligence model can’t survive the digital age is an outlier among his current and former colleagues, but nearly everyone agrees that social media, cell phones, facial recognition technology and super computers that crunch big data have dramatically complicated the business of espionage. As many as 20 CIA informants were executed after China compromised a secret communications system the CIA used to talk to sources, with the help of a CIA turncoat recruited to spy for China. It’s not a new problem. The agency over the years has lost many sources in Iran, American officials have said, and a number of CIA assets were compromised in Lebanon a decade ago thanks in part to cell phone geolocation analysis that allowed Hezbollah spy-hunters to identify people meeting with American operatives. In Milan, an Italian prosecutor was able to identify CIA officers who kidnapped a cleric by sifting through cell phone records. The main culprit, Norman says, is technology. Everyone spews “digital dust” that reveals key facts about their movements, patterns of life and associations. And the number of sensors spitting out data — phones and cars, thermostats and smart watches — is growing by the year. However, many current and former intelligence officials counter that digital dust can be spoofed, and that nobody is better than American services at using cyber tools to advance human spying. Norman doesn’t dispute the skills of U.S. intelligence agencies. But he doesn’t believe American hackers can keep up with the explosion of sensors and surveillance, especially with the advent of 5G networks and the so-called internet of things, which will usher in a dizzying number of new web-linked devices. “The number of digital data points on your activities is growing exponentially every year,” Norman said. “You can’t stay ahead of that.” “Humint is not dead, but you need to be much more careful,” said former CIA Director John Brennan.
On the other hand, technology significantly enhances espionage methods, providing innovative tools for intelligence gathering and political influence. Advanced surveillance systems, data analytics, and artificial intelligence facilitate the collection and analysis of vast amounts of information, enabling operatives to anticipate political movements effectively. In recent years, cyber espionage has emerged as a critical element in global politics. State-sponsored hacking has become a common tactic for gathering sensitive information from rival nations, influencing political decisions, and undermining adversaries. Such activities exemplify how technology reshapes traditional espionage practices. Furthermore, the proliferation of smart devices contributes to vulnerabilities in national security. With the Internet of Things connecting numerous devices, espionage actors exploit these connections to infiltrate government and corporate systems, jeopardizing sensitive data. This evolution demonstrates the pivotal role technology plays in modern espionage and political influence.
______
______
What you know about America’s intelligence community:
Americans love spy movies. But few understand what the U.S. intelligence community does to help political leaders navigate a dangerous and changing world. Secrecy is inherent to their work, like monitoring foreign military operations, courting sources in hostile governments or surveilling terrorist organizations. But what’s happening behind the curtain? Here’s the breakdown.
$106.3 billion
The intelligence community’s annual budget — more than the Afghan war at its peak — funds 18 specialized agencies and elements within other departments, like Energy and Treasury. The CIA recruits foreign agents and runs covert operations overseas. The NSA intercepts data and decrypts codes. The National Geospatial-Intelligence Agency analyzes and predicts how events play out on physical terrains. All coordinate with the director of national intelligence, whose office briefs the president daily. CIA now has about 21,575 employees, including field agents, analysts and covert operatives.
Executive Order 11905
President Gerald Ford banned political assassinations in 1976, after the Senate’s “Church Committee” uncovered CIA plots to kill Fidel Castro and others. It reported that the CIA abetted a coup in Chile, drugged and tortured Americans in mind control experiments, infiltrated civil rights groups and recruited 50 journalists as propaganda assets. It also learned that the NSA was digging through the general public’s telephone traffic. More reforms followed in subsequent administrations, limiting intel work for a generation.
7 in 10 misinformed
At least 71 percent of Americans inaccurately believe that the NSA builds spy satellites, interrogates detainees or targets foreign terrorists. Half don’t know that codebreaking is still a core mission. And it’s still not entirely clear what data or metadata the NSA collects on Americans — much of it likely stored at the Utah Data Center near Salt Lake City. One of the agency’s four such facilities nationwide, it is perhaps the world’s biggest in storage capacity.
_____
_____
Spying resemblances:
The differences between stalking, spying and surveillance are mostly semantic and contextual. All three of these activities involve watching someone or collecting data from them or about them.
_
Spying vs stalking:
Stalking is a crime that involves a pattern of behaviour that makes someone feel scared, threatened, or in danger. Stalking can take many forms, including following someone, sending threatening messages, or showing up at someone’s home or workplace unannounced. In most states, stalking is a criminal offence that can result in fines, imprisonment, or both.
Spying is the act of gathering information about someone or something without their knowledge or consent. Spying can be done for many reasons, including for national security, to gather evidence in a criminal investigation, or to gather information for competitive advantage. Unlike stalking, spying is not necessarily illegal, but it can be if it involves breaking the law, such as hacking into someone’s computer or intercepting their communications.
While both stalking and spying involve monitoring someone, there are some key differences between the two. Stalking is a crime that is committed with the intent to cause fear or harm, while spying is typically done for a specific purpose, such as gathering information. Another difference between the two is the level of intrusion. Stalking often involves a high level of intrusion into someone’s life, such as following them or showing up at their home unannounced. Spying, on the other hand, is often done from a distance, such as through the use of technology or by observing someone from a distance.
_
Spying vs surveillance:
Spying and surveillance refer to different types of actions undertaken by individuals in order to gather information about someone. Spying is generally considered an illegal activity, while surveillance is often done legally with the goal of protecting public safety.
Spying usually involves spying on someone without their knowledge or consent, while surveillance typically involves observing an individual without interfering with their privacy. Surveillance can involve taking photographs or videos, listening to conversations, or tracking the movements of an individual.
Many people mix spying and surveillance, surveillance is used for monitoring activities, and it is used for the security purpose of any building, house, office, or shopping center to have a record of activities performed under a roof. This is very useful for having a proper record of tracked activities that can be used in any emergency by the police and law enforcement agencies. Surveillance serves an important role in investigations. It is a lawful activity and is considered as evidence in court.
There are significant differences between spying and surveillance that should be taken into account when assessing whether one behavior is more harmful than the other. Spying can be invasive and destructive, while surveillance can be helpful and protective. Spying can also lead to identity theft, blackmail, and other crimes, while surveillance cannot always guarantee privacy or anonymity.
Yes, surveillance can potentially cross the line into spying, particularly when it involves covert or illegal activities, or when it infringes on privacy without a legitimate purpose.
Sometimes the issue arises of when legal, permitted surveillance crosses the line into stalking. A rule of thumb is to analyze one’s motive for conducting surveillance. If the performed surveillance serves a purpose for obtaining information, courts will generally uphold rigorous surveillance. Both surveillance and stalking involve observing or following a person’s activities. However, the intent, legality, and professional conduct behind these actions differ significantly.
_
Spying vs snooping:
In essence, snooping and spying both involve gathering information secretly, but snooping is often more casual and less intentional than spying. Snooping can be a casual observation of someone’s activity, like glancing at their computer screen, while spying is a deliberate and often more sophisticated effort to gather information.
A parent checking their child’s phone without their knowledge could be seen as snooping, while a parent using a monitoring app to track their child’s location could be considered spying.
A coworker casually glancing at someone’s email on their screen might be snooping, while a manager secretly recording employees’ conversations would be spying.
Governments using surveillance technology to track citizens’ movements and communications could be seen as spying, while a journalist overhearing a politician’s private conversation might be snooping.
_
Spying vs reconnaissance:
Reconnaissance and spying, while both involve gathering information, differ in their purpose, methods, and scope. Reconnaissance is a broader term, often used in a military context, where the goal is to observe and collect information about an area or enemy forces for strategic planning or tactical purposes. Spying, on the other hand, is a covert activity focused on stealing specific information from an adversary, often for national or political gain. In essence, reconnaissance is a broader term for information gathering, while spying is a specific type of information gathering that is often covert and illegal.
_
Spying vs monitoring:
Monitoring means watching or keeping track of things to make sure they are safe and working well. People do this in different parts of life, like at home, at work, or in their daily routines. The key thing is that monitoring is often done with consent. There is no watching someone secretly. For example, parents monitor their children’s online activity. These apps can block bad content, limit screen time, and show where the child is. In the same way, many workplaces use monitoring tools to check work hours, internet usage, or how much work gets done. Employers tell their employees about these tools. This ensures transparency and a positive work environment. So, the important part of monitoring is trust. Monitoring with consent keeps things safe and helps without bothering anyone.
Spying is when someone secretly monitors people without their consent. Often, people do this to get personal information without permission. Not only people but also companies, especially hackers, operate secretly, so others remain unaware of their monitoring. Often, spying is done for negative purposes, like information theft and data breaches. No matter the reason, spying is a serious invasion of individual privacy and can make people feel unsafe.
When monitoring turns into spying, it does more harm than good. So, instead of pushing employees to perform better, it pushes them away. Because how you track your employees says a lot about how much you trust them.
______
______
Spying vs treason:
Espionage and treason are two distinct but closely related concepts in the realm of national security and intelligence. Espionage and treason are two terms often associated with acts of betrayal and secrecy. While they both involve activities that undermine national security, they differ in their nature, intent, and legal implications.
Espionage:
Espionage, commonly known as spying, refers to the act of gathering confidential or classified information without authorization ‘from or for’ a foreign government or organization. It involves covert operations, intelligence gathering, and the transmission of sensitive data to benefit the spying party. Espionage can be conducted by individuals, groups, or even state-sponsored agencies.
One of the primary motivations behind espionage is to gain a strategic advantage over other nations or organizations. Spies may seek information related to military plans, technological advancements, political strategies, or economic secrets. The information obtained through espionage can be used to inform decision-making, protect national interests, or even disrupt the operations of rival entities.
While espionage is generally considered illegal, it is often an integral part of a nation’s intelligence activities. Governments employ intelligence agencies to carry out espionage operations to protect their national security and interests. However, when individuals or organizations engage in espionage against their own country, it is seen as a betrayal and can lead to severe legal consequences. Espionage against one’s own country can become treason.
When caught, spies can face charges such as espionage, unauthorized disclosure of classified information, or violation of the Official Secrets Act. Punishments for espionage vary depending on the jurisdiction, but they can include imprisonment, fines, or even capital punishment in extreme cases.
Treason:
Treason, on the other hand, is a broader term that encompasses acts of betrayal against one’s own country or sovereign. It involves actions that undermine the government, its authority, or the security of the nation. Treason can take various forms, including espionage, but it extends beyond mere spying. The motivations behind treason can be diverse and complex. Individuals who commit treason may be driven by ideological beliefs, personal grievances, desire for power, or even financial gain. Unlike espionage, treason often involves overt acts that are intended to harm the state or assist its enemies. These acts can include acts of violence, sabotage, or providing aid and comfort to enemies during times of war. Treason is considered one of the most serious crimes in many legal systems. The consequences for committing treason can be severe, including lengthy prison sentences, life imprisonment, or even the death penalty. The severity of punishment reflects the gravity of the offense, as treason strikes at the core of a nation’s stability and security.
_
Comparison:
|
Attribute |
Espionage |
Treason |
|
Definition |
The practice of spying or obtaining secret information without the permission of the target |
The act of betraying one’s country or government, typically by aiding an enemy or attempting to overthrow the government |
|
Intent |
To gather information for a foreign government or organization |
To betray one’s own country or government |
|
Legal Consequences |
Can be illegal depending on the jurisdiction and circumstances |
Generally considered a serious crime with severe legal consequences |
|
Targets |
Foreign governments, organizations, or individuals |
One’s own country or government |
|
Methods |
Covert operations, intelligence gathering, surveillance, infiltration |
Conspiracy, sabotage, aiding enemies, disclosing classified information |
|
Motivation |
Political, ideological, financial gain, or personal reasons |
Political, ideological, personal reasons, or betrayal |
|
Perception |
Can be seen as both heroic and villainous depending on the context |
Generally seen as a betrayal and a serious offense |
_______
_______
Espionage versus intelligence:
In the domains of national security, law enforcement, corporate compliance, and cyber defense, the terms “espionage” and “intelligence” are often used interchangeably, sometimes even synonymously. While they are intimately connected, they are not identical. Each occupies a distinct conceptual and operational space within the broader architecture of strategic information gathering and security policy. Understanding the differences and overlaps between espionage and intelligence is not merely a semantic exercise; it is essential for effective risk assessment, legal classification, ethical governance, and regulatory compliance in a world where information itself has become both a target and a weapon.
_
Intelligence is the collection of information that have military, political, or economic value. According to the Aspin–Brown Commission (that was chartered by US Congress in October 1994 to conduct a comprehensive review of American intelligence), “it is preferable to define intelligence simply and broadly as information about “things foreign”— people, places, things, and events — needed by the government for the conduct of its functions.”
Intelligence refers to both:
– information about “things foreign” that is collected by clandestine means,
– information available through conventional means.
According to the Central Intelligence Agency, “reduced to its simplest terms, intelligence is knowledge and foreknowledge of the world around us—the prelude to decision and action by US policymakers.”
Espionage is a set of intelligence gathering methods.
The Oxford’s English Dictionary defines espionage as “the practice of spying or of using spies, typically by governments, to obtain political and military information.”
The Merriam-Webster’s Dictionary has a slightly different opinion. Espionage is “the practice of spying or using spies, to obtain information about the plans and activities especially of a foreign government or a competing company.”
MI5, the intelligence agency of the United Kingdom, defines espionage as “the process of obtaining information that is not normally publicly available, using human sources (agents) or technical means (like hacking into computer systems). It may also involve seeking to influence decision-makers and opinion-formers to benefit the interests of a foreign power.”
The US defines espionage towards itself as “the act of obtaining, delivering, transmitting, communicating, or receiving information about the national defence with an intent, or reason to believe, that the information may be used to the injury of the United States or to the advantage of any foreign nation”.
According to the 2019 Situation Report of the Swiss Federal Intelligence Service (FIS): “Espionage is driven by a variety of different motives and has more than one aim. For example, states strive, using information obtained by their intelligence services, to gain a fuller picture of the situation in order to improve the effectiveness of their actions.
It can furthermore be observed that information is increasingly being procured with the aim of influencing (in so-called influence operations) or damaging the actions of rivals. Both can be achieved through the selective publication of information. The aim of such activities is often to weaken the cohesion of international groups or institutions and thereby to restrict their ability to act.
Intelligence gathering involves human intelligence (HUMINT – information collected and provided by human sources), signals intelligence (SIGINT – information collected by interception of signals), imagery intelligence (IMINT), measurement and signature intelligence (MASINT), geospatial intelligence (GEOINT), open-source intelligence (OSINT), financial intelligence (FININT), etc.
HUMINT is the oldest form of intelligence gathering. Cyber-HUMINT refers to the strategies and practices used in cyberspace, in order to collect intelligence while attacking the human factor.
Cyber-HUMINT starts with traditional human intelligence processes (recruitment, training, intelligence gathering, deception etc.), combined with social engineering strategies and practices.
_
Espionage traditionally refers to human spies and spying. Intelligence is much broader. It can mean human intelligence, but it also can mean technical intelligence operations, like signals intelligence, or code-breaking, or imagery intelligence. Intelligence is not mysterious: It is secret information, which, by definition, requires secret means to obtain. Sometimes there’s not that much difference between publicly available information in The New York Times, for example, or in the Harvard Gazette, and in intelligence briefings — and when that happens, policymakers rightly ask what’s the point of intelligence briefings if they can read the same or similar information in the press? The purpose of intelligence is to provide policymakers, decision-makers, with something extra — something they can’t obtain, read, or see on the news or some other way. So, at its most basic, the purpose of intelligence is to help policymakers make their decisions. It’s to be able to know about enemies’ intentions and capabilities, and it is to be able to know about threats on the horizon. It doesn’t always work, as we’ve seen recently, but that’s the aim.
_
World leaders are faced with making important decisions every day, and information is the key to making the right decision. How many troops does your enemy have? How far are they in developing their secret weapons? Are they planning to negotiate a trade deal with another country? Are some of their generals planning a military coup? While some of this information (known as intelligence) may be readily available, most countries keep information that could be used against them secret. Of course, this secret information is often the most valuable. To gain access to secret information, governments use espionage, a blend of subterfuge, deception, technology and data analysis. Espionage can also be used to counteract the spying efforts of the enemy, mainly be supplying them with false information.
_
For centuries, there has been no single definition of intelligence, nor indeed espionage. The definition depends on the scholar, the practitioner, the government, the citizen, or any of the other stakeholders who might be making remarks upon the practices of spies or intelligence agencies. Some scholars have written that the definition of intelligence is confused by the fact that intelligence agencies today are engaged in many more activities than intelligence gathering, and ask whether Sabotage, Deception, Counterintelligence, Analysis, Financial intelligence, Propaganda, and even Assassination might be considered all forms of espionage. Is intelligence a product, or process? For producers of intelligence, however, the equation intelligence = information is too vague to provide real guidance in their work. To professionals in the field, mere data is not intelligence; thus these definitions are incomplete. Think of how many names are in the telephone book, and how few of those names anyone ever seeks. It is what people do with data and information that gives them the special quality that we casually call intelligence.
_
At its core, intelligence is the lawful and structured process of collecting, evaluating, and analyzing information that is relevant to decision-making. Intelligence can be collected from a variety of sources, including open public data, voluntary disclosures, human sources, technical surveillance, and cyber operations. Its primary purpose is to reduce uncertainty about adversaries, threats, opportunities, and operational environments.
Intelligence can be both tactical and strategic. It may support national security decisions, military operations, diplomatic negotiations, regulatory enforcement, or commercial strategy. Intelligence exists across multiple domains—military, political, economic, environmental, technological—and functions as a continuous cycle: from planning and collection, to analysis, dissemination, and review.
_
Espionage, by contrast, is the covert and unauthorized acquisition of protected or restricted information—most often for the benefit of a foreign entity, competing interest, or adversarial actor. It is inherently clandestine, typically illegal, and often conducted in violation of trust, law, or institutional security policies. Espionage involves breaching confidentiality barriers: through infiltration, recruitment, deception, surveillance, or digital intrusion. It is, in effect, a subversive act designed to obtain information that would not otherwise be accessible through legitimate or transparent means. While espionage may feed into the intelligence cycle, its methods and intent distinguish it as a more aggressive, risk-laden, and frequently criminalized activity.
_
This distinction becomes particularly relevant in legal contexts. Intelligence, when gathered through open-source research or lawful surveillance with proper authorization, is typically compliant with national and international norms. Intelligence agencies, law enforcement, and compliance professionals routinely collect intelligence within the boundaries of their mandates. Espionage, however, is frequently classified as a criminal offense under national law. In most jurisdictions, espionage includes unauthorized access to classified information, the theft of trade secrets, or the transmission of sensitive data to foreign governments or hostile actors.
_
Espionage, commonly known as spying, is the practice of secretly gathering information about a foreign government or a competing industry, with the objective of placing one’s own government or corporation at a strategic or financial advantage. However, espionage is not synonymous with all intelligence-gathering disciplines. All espionage produces intelligence, but not all intelligence arises from espionage. Lawful intelligence gathering can rely entirely on legal sources—open-source intelligence (OSINT), public satellite imagery (IMINT), or communications metadata within the scope of lawful SIGINT programs. Espionage, however, involves crossing a threshold: violating permissions, breaching systems, deceiving individuals, or circumventing security controls. It is this violation—this infringement upon secrecy or confidentiality—that gives espionage its legal and ethical charge.
_
In the corporate world, this distinction has profound implications. A compliance officer conducting due diligence or an internal investigation is engaged in intelligence gathering. But a competitor who bribes an employee to disclose confidential R&D plans, or who deploys spyware to intercept internal communications, is engaged in corporate espionage. Both seek information, but the means and the legal standing of those efforts determine whether they are defensible strategies or prosecutable acts.
_
Complicating this distinction further is the emergence of cyber-enabled espionage, where the boundaries between traditional espionage and modern intelligence blur. Advanced Persistent Threat (APT) groups, often state-sponsored or state-tolerated, conduct long-term cyber intrusions to steal intellectual property, strategic planning documents, defense blueprints, and foreign policy intelligence. These operations may be masked as intelligence collection, but they are, in most jurisdictions, legally defined as espionage, particularly when directed at classified or proprietary information.
_
The convergence of human and technical methods further blurs the line. For example, a state actor may use Human Intelligence (HUMINT) to recruit a corporate insider, then support that insider with cyber capabilities to exfiltrate sensitive files. Alternatively, a cyber intrusion may identify a target, who is then approached in person for further exploitation. In such hybrid scenarios, it becomes clear that espionage and intelligence are not separate silos but interdependent components of a unified operational strategy.
_
The international legal framework for espionage and intelligence is equally complicated. Unlike armed conflict, terrorism, or piracy, espionage is not uniformly codified in international law. It is tolerated as a matter of statecraft, but rarely admitted openly. While espionage between states is almost universally practiced, it is also nearly always denied. This duality creates a legal grey zone, where actions that would be criminal domestically are often managed diplomatically when perpetrated by foreign agents. In contrast, intelligence collection through OSINT or interagency cooperation may be conducted openly and with legal legitimacy.
_
The relationship between espionage and intelligence is defined by both convergence and contrast. Both involve the pursuit of information for strategic advantage. Both require analytical discipline and operational tradecraft. But espionage is inherently transgressive, operating in violation of legal or ethical boundaries, while intelligence, when lawfully conducted, serves as a core instrument of informed and responsible governance. For legal, compliance, and risk professionals, recognizing the distinction is critical—not only to protect against espionage, but to ensure that internal intelligence activities remain within lawful, ethical, and reputational limits. In an age where the control and protection of information define power, sovereignty, and security, understanding the nuances between these two terms is not academic—it is imperative.
______
______
Targets of spying:
Espionage Targets:
The targets of espionage are many. The agents are trained under supervision, and they are experts in their respective fields. Generally, data collection is the main objective of the espionage strategy. These are some of the targets for any espionage agent:
- Natural resources: strategic production identification and assessment (food, energy, materials). Agents are usually found among bureaucrats who administer these resources in their own countries.
- Popular sentiment towards domestic and foreign policies (popular, middle class, elites). Agents often recruited from field journalistic crews, exchange postgraduate students and sociology researchers.
- Strategic economic strengths (production, research, manufacture, infrastructure). Agents recruited from science and technology academia, commercial enterprises, and more rarely from among military technologists.
- Military capability intelligence (offensive, defensive, manoeuvre, naval, air, space). Agents are trained by military espionage education facilities and posted to an area of operation with covert identities to minimize prosecution.
- Counterintelligence operations targeting opponent’s intelligence services themselves, such as breaching the confidentiality of communications and recruiting defectors or moles
Note:
Targets of Cyber Espionage will be discussed in the section on cyber espionage.
______
Spyware must target crime, not opposition.
Spying on political opponents, journalists or lawyers is illegal and against fundamental EU values. When security forces use spyware, it must be within clearly defined borders. The abuses of spyware in Poland and Hungary have been flagrant violations of the rule of law. Member States must possess effective tools to protect national security and fight serious crime. The legal use of spyware should, therefore, have defined conditions and must be in line with the law and standards set out by the Court of Justice of the European Union and the European Court of Human Rights case law. Spyware must not be used as a political weapon against democratic institutions, politicians or journalists. The security forces need advanced technological tools in order to face threats such as terrorism, organised crime or attacks against the constitutional order. However, we need to make sure that these spyware tools are used while respecting fundamental rights and in accordance with the principles of the rule of law.
_____
_____
Motivations for Espionage: How ordinary people are convinced to become spies:
When studying notorious spies, the initial questions that arise are:
- Why in the world would someone do such a thing?
- What would cause someone to share classified materials with an enemy of their country or risk federal prison to steal state secrets?
Different things motivated different spies: money, excitement, patriotism. Russian President Vladimir Putin’s ambition to join the KGB, he said, was sparked by the 1968 film “The Sword and the Shield”, a romanticized view of Soviet intelligence agents in World War II. He also liked to read thrillers about the adventures of KGB agents. In 1988 the KGB defector, Stanislav Levchenko, described an American mnemonic, MICE, which stands for “money”, “ideology”, “coercion/compromise” and “ego”. Susceptibility to these factors, he claimed, was a target’s key weakness that could be exploited.
- Money:
This is a general category that would include such selfish motivation as avarice (extreme greed for wealth or material gain) as well as what might be considered more noble motives such as the need to pay for a family member’s medical treatment or a child’s education. In any event, the spy comes to the personal conclusion that espionage is the best or perhaps only means of obtaining the money desired. CIA research psychologist Terry Thompson suggests there are a number of additional factors that may contribute to the spy’s vulnerability to the offer of money, to include a cultural tendency toward acquainting success with material gain, the social power and prestige that come with material success, the ego gratification effect of receiving money, as well as the relief the spy in financial need feels upon receiving their pay. Thompson also makes the intriguing suggestion that a willingness to take risks, one of the personality traits that might attract an individual to a career as an intelligence collector, may also inadvertently contribute to poor financial decisions that place an individual in a state of financial need and to view espionage as a plausible remedy.
Officials in debt are ripe targets for recruiters. For instance, in 1935, Captain John Herbert King, a cypher clerk for the British Foreign Office, had a problem. He was estranged from his wife, harboured expensive tastes, had a son and mistress to maintain, and only took home a small salary – and no pension. As such, he proved a ripe target for recruitment by Soviet intelligence. He was approached by Henri Pieck, a Soviet spy, who pretended to be a businessman and high-society flyer. Pieck convinced the cypher clerk that, if he wished to support his family, money was required. King agreed to supply Foreign Office secrets, which he was led to believe would be used to provide Pieck and a Dutch bank a stock market advantage. King was promised a share of these profits amounting to £100 a month. The arrangement came to an end in 1937, when his handler was recalled to Moscow during Stalin’s purges. King was arrested in 1939 and sentenced to ten years in prison.
- Ideology:
An ideology is simply a shared set of beliefs about how the world is or ought to be. Psychiatrist and author Steven Pinker writes, “An ideology cannot be identified with a part of the brain or even with a whole brain, because it is distributed across the brains of many people.” Since it represents a shared belief system, an ideology is adopted by an individual to the degree that it reflects the individual’s ego. In that sense, an ideology is like another motivation – money – in that it serves as a vehicle for the individual to express a personal value or belief; an ideology is chosen in order to confirm conscious or unconscious beliefs the individual has already internalized. In the case of espionage, a particular ideology may serve as either the actual motivation for a spy to breach the trust placed in them or simply as a means of rationalizing that behavior. The so-called Cambridge Five were likely “true believers” whose motivation for working with the Soviets against their native United Kingdom was based largely (but not exclusively) in a utopian belief in Communist ideology. Donald Maclean already had left-wing views which grew into an ideological belief in the justness of the Soviet’s communist cause. In his final year, in 1934, he was recruited by the NKVD (a Soviet secret police agency, a forerunner of the KGB) and instructed to give up on his political activism and enter the British establishment. He soon sat the civil service exams and joined the Foreign Office, where he acted as one of the most damaging spies of his generation. Maclean was not alone, he was a member of the Cambridge Ring of Five, which included Kim Philby, Guy Burgess, Anthony Blunt and John Cairncross. Each of whom was recruited into Soviet service during or shortly after their time at Cambridge. As a result of their orthodox, respectable Cambridge educations, each was able to enter the most sensitive areas of the British state, not least the Foreign Office, the Cabinet Office, MI5, MI6 and GCHQ (GC and CS at the time). Before the Cold War ended, however, ideology appeared to play a decreasing role in Soviet recruitment, forcing the KGB to seek other motives. Nevertheless, Cold War-era political beliefs were only one form of ideology, and its demise certainly does not rule out the use of ideology as motivation in the present or future.
- Coercion or compromise:
This is a negative rather than positive form of motivation and can be equated with what one might think of as “blackmail” or perhaps even torture. Unlike the other general forms of motivation offered in MICE, in this case the spy does not act of his or her own free will but, rather, is effectively forced to commit espionage through fear of punishment, exposure of wrongdoing, or some other undesirable outcome. From a psychological perspective, it is the least reliable method of recruitment since the spy’s primary motivation is to escape punishment rather than to please his or her handler. The spy is likely to cooperate only to the extent necessary and may attempt to break free of control as soon as practicable. An infamous example of compromise is the so-called “Honey Trap,” in which a foreign intelligence service would direct a man or woman to seduce a targeted individual in order to obtain their cooperation through threat of exposure. Another scenario that can lead someone to committing espionage is a romantic relationship. Foreign intelligence organizations often target and turn individuals to pass classified material who have become romantically involved with a foreign agent.
In 1946, John Vassall took a job as the assistant to the naval attaché in Britain’s Moscow embassy. He was, however, harbouring a secret. Vassall was a gay man at a time when homosexuality was illegal in Britain. Those convicted of homosexuality faced custodial sentences. The KGB discovered Vassall’s secret and orchestrated several compromising photographs to use as blackmail. Shortly after, in 1956, Vassall was transferred back to London and into naval intelligence. From there he could provide a steady stream of secret information, including technical secrets regarding radar and weapons. This arrangement, for which Vassall was well remunerated, lasted until 1962 when Vassall was arrested following the defection of the KGB officer, Anatoli Golitsyn. In 1962, following a massive scandal that rocked the Macmillan government, Vassall was sentenced to 18 years in prison and was released in 1972.
- Ego:
This could be considered the all-inclusive category, since an individual’s opinion of his- or herself and the effort he or she puts into enhancing or defending that opinion is fundamental to their decision-making. Levchenko’s use of the term was more focused and meant to highlight the potential spy’s desire for challenge, adventure, and excitement. Later efforts that went beyond MICE would identify personality traits such as narcissism or attitudes such as employee disgruntlement that are manifestly ego-related but perhaps more insightful than Levchenko’s risk-taking behavior. In fact, with the exception of coercion, all of the MICE categories may fall under ego, inasmuch as money and ideology serve as vehicles for the expression of ego.
For some, espionage is an opportunity to secretly manipulate people around them and to prove their superiority. An FBI agent and Soviet spy from 1976 to 2001, Robert Hanssen clearly fit that category. Hanssen seemingly enjoyed an ordinary life as a happily-married suburbanite yet lived a double life as a spy – complete with an affair with an exotic dancer whom he lavished with expensive gifts. He also secretly filmed his sex life with his wife and invited others, without telling her, to watch. Money was an initial motive, Hanssen received $1.43 million (£1 million) in cash and diamonds from his handlers. However, he was an attention-seeker who felt snubbed by an FBI which, in his estimation, failed to recognise his abilities. His two-decade career as a double agent, which included revealing the identities of at least nine US assets in the Soviet Union, was an opportunity for excitement and to demonstrate his superiority over his colleagues in the FBI. Hanssen is currently serving 15 consecutive life sentences and his espionage has described by the US Department of Justice as “possibly the worst intelligence disaster in US history”.
_
While still popular and oft-cited, MICE is of somewhat limited value in predicting who will or will not commit espionage. First, the categories are too general and lack nuance, so they fail to identify in a practical manner the myriad and complex motivation of individual spies. Furthermore, as limited, general categories, employing them runs the risk of making the behavior fit the category, resulting in ascribing oversimplified motivation such as “Ames was greedy” or “Hannsen was arrogant.” Finally, being an expression of conventional wisdom or common sense, they are not based on any actual scientific research.
____
Personnel Security Research Center (PERSEREC) research on motivations for spying:
PERSEREC’s initial effort was to establish a database on all Americans involved in espionage against the US since World War II based on media reports, trial records, and unclassified official documents. The database would “make it possible to systematically collect, quantitatively code, and statistically analyze basic information. This included such things as personal background, the methods and motivations of the offender, and pertinent facts about the crime itself — situational features, what was lost or compromised, and consequences for the subject.” Drawing from a database that included (at the time) 120 cases of espionage, PERSEREC issued a May 1992, report entitled, “Americans Who Spied Against Their Country Since World War II”, which identified six key motivations. In addition to adding substance to the old MICE categories of money, ideology, and coercion, PERSEREC researchers suggested three additional motivations, disgruntlement/revenge, ingratiation, and thrills/self-importance, which were in effect more refined views of the MICE category ego.
- Disgruntlement/revenge – The spy is motivated by a non-ideological resentment or anger directed toward their country or their employer for some perceived injustice, such as a lack of recognition or inadequate appreciation, failure to achieve promotion, inadequate pay or other compensation, or any number of other perceived personal slights. As a result, the spy seeks revenge by engaging in espionage. A key point is that the injustice may or may not be real, but it is perceived by the spy as both real and personal. CIA research psychologist Thompson suggests that unrealistic expectations of workplace fulfilment, the depersonalization of large bureaucracies, overestimation of an individual’s actual talent, and a culture of disgruntlement fostered by a constant stream of negative media reporting all contribute to disgruntlement. Psychiatrist David Charney, who has interviewed several convicted spies, makes the counterintuitive observation that spies who act out of disgruntlement toward their own agency often continue to view themselves as patriotic citizens and claim it was never their intention to do damage to their country.
- Ingratiation – The spy is motivated by a desire to please another person. While it would seem unlikely that an individual would choose to spy simply in order to please another person, ingratiation may be a contributing factor in that decision. For example, if a spy is ideologically motivated, they may work especially hard to please their handler in an effort to demonstrate their commitment to the cause. Navy Seaman Michael Walker, son of John Anthony Walker and part of his father’s spy ring, testified that he became a spy in 1983 “for the money and to please my father.” Ingratiation may also have played a role in the so-called “Romeo” operations conducted by the East German Stasi, in which a Stasi agent would establish a romantic relationship with a lonely, female secretary in a target West German organization. Unlike coercive “Honey Traps,” the espionage was often based on genuine bonds of affection between the target and her “Romeo.”
- Thrills/self-importance – This motivation is likely what Levchenko had in mind by the term ego. In its purest form, it might be considered the most egocentric of motivations, since it does not necessarily include a desire for personal gain or revenge against some perceived slight. In practice, it is likely a significant contributing factor but not necessarily the key motivation. The spy chooses espionage because of the feeling of excitement it brings, as well as the sense of superiority the spy derives from “putting one over” on their colleagues or their organization. Rather than a manifestation of high self-esteem, it may be the result of the low self-esteem experienced by the would-be-spy suffering some personal or professional setback. Ironically, the very desire for thrills that attracts some IC employees to the profession may also make them particularly susceptible to the thrill of espionage. Likewise, the power and ego enhancement that comes with keeping secrets from others may add to the feeling of superiority the spy obtains by keeping his or her espionage a secret from their co-workers and organization.
______
Taylor and Snow’s research:
In one of the first publicly-available studies on spying, a BYU professor and graduate student discovered the changing motivations of people who become spies and betray their nation’s confidence. Stanley A. Taylor, professor of political science, and Daniel Snow, an international relations student at the time, compiled a study showing that in recent decades, money has surpassed ideology as the primary reason for spying.
Taylor notes that during World War II and the early Cold War, motivation was primarily ideological, but monetary motivation began to take over by the 1960’s. “A lot of Americans by 1960 were aware of the evils of communism. They had seen the horrors of Stalin. They weren’t quite as fooled by communism as were some of those who started spying in the 1930s and ’40s and through the war.” Additionally, the Soviet Union was America’s ally through World War II, and spies typically found it easier to justify spying for an ally. Then the Soviet Union became our Cold War enemy, and ideological reasons faded into monetary motivators. “I suspect, too, that society has just become more materialistic,” Taylor says.
Money and ideology were among the four recurring dominant motivators that surfaced in Taylor and Snow’s research. Disgruntlement and ingratiation were the other two. Monetary gain, appearing in 55.4 percent of cases since 1940, has increased dramatically since 1960. Ideology, on the other hand, is the primary motive in 23.7 percent of cases but has dropped dramatically since the famous atomic spy cases of the early 1950s. Disgruntlement–a sense of personal dissatisfaction from feeling unappreciated–is the only other motivator that is increasing, although it accounts for only 2.9 percent of cases. Ingratiation–betraying information to fulfill friendship or love obligations–accounts for 5.8 percent of cases and has declined in importance.
Snow cites the 1994 case of Aldrich H. Ames as an example of money as the motivator. An employee of the CIA, Ames received $2.5 million from the Soviet Union to reveal the names of Soviet and U.S. agents who were spying for the United States–all of whom were put to death. “He didn’t just spy for the Soviet Union,” says Snow, now an MBA student at BYU. “He spied for Russia. So after the fall of the Soviet Union, it’s Russia–this kinder, gentler Russia–that is still very actively spying on the United States. People aren’t spying for ideology anymore because there’s not really any ideology there to spy for. It’s just money.”
Taylor and Snow began their analysis in fall 1996. Searching through books, magazine articles, newspaper articles, and government publications, they found 139 people who had been officially charged with spying since the 1940s. They then assessed 40 variables associated with treason, such as date of birth, date of arrest, personal habits, sexual preferences, and recruitment methods.
_____
Charney’s theory:
“People who join the intel community spent years preparing themselves — school, applying, screening — there’s a huge amount of drive and ambition, identification, pride,” says Dr. David L. Charney, a psychiatrist with the National Office of Intelligence Reconciliation, known as NOIR, a nonprofit dedicated to educating the intelligence community on the management of insider threats. This would include people with access to sensitive information who flip, such as Edward Snowden or Reality Winner. “They’re not coming in to be spies; they join for loftier reasons. The question is what makes a person go bad. That’s when you have to get more psychological.” According to Charney, at the core of espionage can be an intolerable sense of personal failure, and not necessarily a shifting ideology. “Going back to the ideological spies of the 1930s and ’40s, we run across people all the time who you know have personal demons that are driving them, but they wrapped their demons into the current issue of the day to give it a higher-minded packaging. Any time you try to understand you have to dig a little deeper.”
In a 2010 article, psychiatrist David Charney took a step beyond traditional screening models, proposing that regardless of motivation, once insider spies have crossed the line into espionage, they tend to follow similar thought patterns that manifest in predictable behaviors. Based on personal interviews with incarcerated spies, Charney postulated that the decision to spy is based on “an intolerable sense of personal failure, as privately defined by that person.” Once the spy has made the decision to engage in espionage, Charney identifies what he calls The Ten Life Stages of the Insider Spy: 1) the sensitizing stage, 2) the stress/spiral stage, 3) the crisis/climax/resolution stage, 4) the post-recruitment stage, 5) the remorse-morning-after stage, 6) the active spy career stage, 7) the dormancy stage(s), 8) the pre-arrest stage, 9) the arrest and post-arrest stage, and 10) the brooding in jail stage. Each stage represents a development in the spy’s effort to deal with their sense of personal failure by taking what they consider decisive action to boost their sense of worth. This is initially effective, but eventually the spy succumbs to second thoughts, feelings of regret, of being trapped, loneliness, and dependence on their handler. Charney’s theory also postulates that certain stages present windows in which, given specific incentives, the spy may choose to reveal their activities to an appropriate authority.
______
Personality elements:
According to Dr. Ursula Wilder, a clinical psychologist with the Central Intelligence Agency, four personality elements are essential to the entry into espionage: psychopathy, narcissism, immaturity and grandiosity.
“A psychopathic person is a person whose approach to reality is ruthless and cold,” she stated in an interview at the International Spy Museum in Washington, D.C. “They have no conscience, or they have very limited capacity to feel guilt. So, their whole approach to life is predatory. They’re excitement seeking. They love to con people. It’s a game. This is all they can do to connect with other human beings. So that kind of person will commit espionage either flat-out for self-interest or because it’s fun, or both.”
“The next is narcissism,” she explained. “A narcissistic person is fundamentally ego-centric. They can only experience the world with themselves at the center. They are very much needy for and will provoke circumstances that will permit them to be at the center of attention. They believe that what they need, want and desire, is truth. They will get greedy for attention. That kind of person will commit espionage as a grab for fame. Someone like that will commit espionage because it makes them feel big and important.”
Regarding immaturity, Wilder explained an individual prone to commit acts of espionage (in comparison to a professional intelligence agent), either for or against their nation, is “an adult who can only function as an adolescent. These people live their lives in a blend of fact and fantasy. They do have a conscience, they can feel deep guilt afterwards, but fantasy is much more real to them than it is to adults who are grounded to reality, so to them committing espionage is a bit of a game, a fantasy, and online they have this illusion that if they do it online, if they just turn off the machine it goes away. They have a fantasy about the implications of their actions, and although on some level they might grasp the reality of it, it’s not real to them. The grandiosity applies to all three.”
______
______
The Tools of Modern Espionage:
Gone are the days of exploding pens and shoe phones. Modern spies rely on a mix of high-tech tools and old-school methods to gather intelligence.
- Technology: Drones, encrypted communication devices, and satellite imagery are essential in today’s espionage. Cyber espionage has also become a critical component, with operatives hacking into networks or protecting sensitive information.
- Tradecraft: Spies still use classic methods like dead drops (leaving items in hidden locations), surveillance, and covert meetings. These techniques remain invaluable for human intelligence (HUMINT) gathering.
- Disguises: From prosthetics to simple wardrobe changes, the art of disguise is still a crucial skill.
The equipment and gadgets used by spies can vary greatly depending on their mission and specialty. However, some of the most commonly used equipment in espionage include:
- Surveillance Devices: This may include hidden cameras, audio recording and GPS trackers. Spies can use these devices to gather information without being detected.
- Secure Communications Equipment: Spies need to be able to communicate securely with their agency and other contacts. This may involve the use of encrypted phones, secure messaging software, and other secure communication devices.
- Cybersecurity Tools: For spies working in cyber espionage, cybersecurity tools are essential. This can include software for encryption and decryption of information, tools for ethical hacking, and software to protect against cyberattacks.
- Concealment Devices: Spies often need to hide documents or equipment. This may involve the use of hidden compartments, concealment devices, and other gadgets to safely conceal and transport information.
It’s important to remember that while these gadgets may look like something out of a James Bond movie, the equipment used by spies in real life is often far less glamorous. The true art of espionage lies in the spy’s ability to collect and analyze information, not in the technology he uses.
_
How do spies protect their identity?
Protecting your identity is a crucial part of a spy’s job, and there are several techniques spies use to keep their true identity a secret.
First, spies often adopt a “cover identity”. This is a fake identity that the spy uses in her work, complete with a backstory and credible personal details. This identity can be as simple as a new profession and name, or it can involve taking on a completely new persona.
Second, spies adhere to strict information security standards. This means that they are very careful about what information they share and who they share it with. They avoid talking about their work and are aware of the possibility of being watched or recorded at all times.
In addition, spies use a variety of techniques to avoid detection and surveillance. This can include changing your appearance and routine frequently, using counter-surveillance (techniques to detect and evade surveillance), and using secure and encrypted communications.
Finally, it is important to note that spy agencies also play an important role in protecting the identity of their agents. They provide training and support to their spies and take steps to protect information about their staff.
_
The Moral Dilemmas:
The life of a spy isn’t just about gathering secrets; it’s about navigating a world of gray areas. Spies often operate in morally ambiguous territory, where the ends justify the means.
- Trust and Betrayal: Building relationships with informants often involves manipulation. Spies must earn trust while knowing they may need to exploit or abandon their sources.
- The Greater Good: Espionage sometimes involves actions that would be unacceptable in other contexts, such as lying, stealing, or even assassination. Operatives must reconcile these actions with their moral compass.
- Psychological Toll: Living under constant stress and secrecy takes a toll. Many spies struggle with anxiety, guilt, or the fear of being discovered.
______
______
Cover, Covert and Clandestine:
Cover:
In intelligence, “cover” refers to the false identity or persona an agent adopts to conceal their true affiliation and activities during a covert operation. It’s a crucial element in espionage, allowing agents to operate undetected and gather information or conduct sabotage. A cover can range from a legitimate professional role, like a diplomat or journalist, to a fabricated identity, like a businessperson or student. A cover in foreign, military or police human intelligence or counterintelligence is the ostensible identity and role or position in an infiltrated organization assumed by a covert agent during a covert operation.
Official cover:
In espionage, an official cover operative is one who assumes a position in an organization with diplomatic ties to the government for which the operative works such as an embassy or consulate. This provides the agent with official diplomatic immunity, thus protecting them from the steep punishments normally meted out to captured spies. Upon discovery of an official cover agent’s secret hostile role, the host nation often declares the agent persona non grata and orders them to leave the country.
Non-official cover:
In espionage, operatives under non-official cover (NOC) are operatives without official ties to the government for which they work who assume covert roles in organizations. This is in contrast to an operative with official cover, where they assume a position in their government, such as the diplomatic service, which provides them with diplomatic immunity if their espionage activities are discovered. Operatives under non-official cover do not have this “safety net”, and if captured and charged as spies are subject to severe criminal punishments, up to and including execution. Operatives under non-official cover are also usually trained to deny any connection with their government, thus preserving plausible deniability, but also denying them any hope of diplomatic legal assistance – or official acknowledgment of their service. Such an operative or agent may be referred to as a NOC. Sometimes, front companies or strawman entities are established in order to provide false identities for agents.
_
Covert Action:
The U.S. government defines covert action as activities aimed at influencing political, economic, or military conditions abroad, all while concealing the U.S. role. In the United States, such actions are only pursued at the direction of the president. Covert action hinges on the principle of plausible deniability, which enables governments to deny involvement in specific measures. When it comes to covert action, leaders can see it as an attractive foreign policy tool. Covert action circumvents the high costs of war and other criticism associated with controversial public actions.
The CIA has long served as the primary agency behind U.S. covert action. Those activities have included assassination attempts, efforts to spark coups, cyberattacks, and drone strikes. Experts organize covert action into several categories:
- Lethal action: Perhaps the most notorious genre of covert action includes assassination and lethal force. Sometimes those actions take place within the context of conflict, while other times they involve a political motive. For example, governments use covert action to go after foreign leaders or other important figures they believe threaten their interests. Since 1976, the U.S intelligence community has been banned from using assassination as a foreign policy tool.
- Paramilitary action: Covert action can also involve arming and training surrogate forces abroad to carry out foreign policy objectives.
- Political or economic action: Not all covert action involves force. Some forms entail economic or political interference. This form of covert action, includes eradicating crops, tampering with elections, or channelling funds to rival political groups.
- Propaganda: Covert action also involves using information to manipulate people and advance a particular cause. For instance, governments can utilize the media to turn public opinion against an issue or leader.
Many countries use covert action to achieve foreign policy goals. For example, after the Soviet Union invaded Afghanistan in 1979, the CIA helped drive the occupying force out of the country by arming and funding anti-communist Muslim insurgency groups collectively known as the mujahideen. (However, that same case shows how complicated the covert action’s consequences can be. Many of those insurgents would go on to enforce a radical vision of Islam across the country and eventually fight U.S. forces years later.)
In 2011, the United States sent a team of Navy SEALs on a covert raid in Abbottabad, Pakistan. This instance of violent covert action resulted in the killing of al-Qaeda leader Osama bin Laden. The downsides of covert action can be significant. Assassination attempts can lead to retaliatory attacks, and coups can usher in repressive regimes. Where the United States has succeeded in overthrowing governments, research by some political scientists indicates countries have become less democratic. Moreover, these nations are more prone to civil conflict and mass killing.
_
Covert versus clandestine:
The terms clandestine and covert are not synonymous. As noted in the definition (which has been used by the United States and NATO since World War II) in a covert operation the identity of the sponsor is concealed, while in a clandestine operation the operation itself is concealed. Put differently, clandestine means “hidden”, where the aim is for the operation to not be noticed at all. Covert means “deniable”, such that if the operation is noticed, it is not attributed to a group. The term stealth refers both to a broad set of tactics aimed at providing and preserving the element of surprise and reducing enemy resistance. It can also be used to describe a set of technologies (stealth technology) to aid in those tactics. While secrecy and stealthiness are often desired in clandestine and covert operations, the terms secret and stealthy are not used to formally describe types of missions. Some operations may have both clandestine and covert aspects, such as the use of concealed remote sensors or human observers to direct artillery attacks and airstrikes. The attack is obviously overt (coming under attack alerts the target that he has been located by the enemy), but the targeting component (the exact method that was used to locate targets) can remain clandestine.
_
Clandestine Operation:
Clandestine operation is an operation sponsored or conducted by governmental departments or agencies in such a way as to assure secrecy or concealment. A clandestine operation (op) is an intelligence or military operation carried out in such a way that the operation goes unnoticed by the general population or specific enemy forces. Until the 1970s, clandestine operations were primarily political in nature, generally aimed at assisting groups or nations favored by the sponsor. Examples include U.S. intelligence involvement with German and Japanese war criminals after World War II or the botched Bay of Pigs Invasion in 1961. Today these operations are numerous and include technology-related clandestine operations. The bulk of clandestine operations are related to the gathering of intelligence, typically by both people (clandestine human intelligence) and by hidden sensors. Placement of underwater or land-based communications cable taps, cameras, microphones, traffic sensors, monitors such as sniffers, and similar systems require that the mission go undetected and unsuspected. Clandestine sensors may also be on unmanned underwater vehicles, reconnaissance (spy) satellites (such as Misty), low-observability unmanned aerial vehicles (UAV), or unmanned detectors (as in Operation Igloo White and its successors), or hand-placed by clandestine human operations.
______
______
Spying and its importance:
There are several reasons why spying is considered necessary or desirable by certain individuals, organizations, or governments. Some of these reasons include:
- National security: Governments may engage in spying to gather intelligence about potential threats to national security, such as terrorist plots, cyberattacks, or foreign military operations.
- Economic competitiveness: Companies may engage in industrial espionage to gain a competitive advantage in the marketplace by obtaining information about their rivals’ strategies, products, or trade secrets.
- Diplomatic relations: Governments may engage in spying to gain insights into the diplomatic strategies of other nations and to negotiate more effectively in international affairs.
- Criminal investigations: Law enforcement agencies may use spying to gather evidence in criminal investigations, such as monitoring the activities of suspected terrorists, drug traffickers, or other criminal organizations.
- Personal safety: Spying can be used to protect individuals from harm, such as monitoring the activities of potential stalkers or abusive partners.
While spying can be justified for reasons such as those listed above, it is also controversial and can have negative consequences. Spying can violate privacy rights, undermine trust between individuals and organizations, and create tensions between nations. Additionally, the methods used in spying can often be unethical or even illegal. Therefore, it is important to carefully consider the reasons and potential consequences of spying before engaging in such activities.
______
______
Examples of espionage:
Throughout the Cold War, the United States and the Soviet Union worked to recruit double agents. These agents work behind enemy lines and smuggle secrets from under the nose of their opponent. Today, the United States, China, France, India, Israel, Pakistan, Russia, and the United Kingdom all have widely respected intelligence services.
New debates have surged over spying in 2023 when a Chinese spy balloon was shot down by U.S. officials while flying over the United States. U.S. lawmakers have also accused Chinese company, Byte Dance, which owns the popular social media app TikTok, of intelligence harvesting. Byte Dance allegedly offers tools for Chinese officials to use U.S. citizens’ personal information for their intelligence purposes. Russia has also accused U.S. citizens of spying. U.S. government officials refute this—as in the controversial case of U.S. citizen Paul Whelan’s imprisonment in Russia.
But countries don’t just spy on rivals. In 1984, for instance, Israeli operatives trained an American Navy intelligence analyst, Jonathan Pollard, on ways to collect and share U.S. intelligence with Israel. They did this despite the fact that the two countries were, and remain, close partners. Moreover, in 2015, WikiLeaks revealed that the United States had been tapping German Chancellor Angela Merkel’s phone calls for decades, despite Germany’s alliance with the United States.
The reality is that all countries spy; however, some countries are better equipped for the practice than others. One expert said the United States, for instance, has the equivalent of a “nuclear weapon” in its intelligence armoury compared to most other countries, which are stuck with the equivalent of cannons.
_
Notable spies:
-1. Ian Fleming, Creator of James Bond and Intelligence Professional:
The list of famous spies must include Ian Fleming, who popularized the world of intelligence by creating the fictional secret agent, James Bond. What others may not know is that beside the creation of James Bond for the spy genre, Fleming did intelligence work for the British during World War II. His imagination, keen sense of detail, and focus on aligning intelligence activities and planning to support intelligence operations were critical to Britain’s success against Nazi Germany.
-2. Dusan Popov:
A big source of inspiration for Ian Fleming and his spy novels, Dušan Popov was a Serbian-born double agent who worked for MI6 during World War II. In addition to charming exotic women and going on dangerous missions, Popov became famous for warning the FBI as early as August 1941 that Japan was planning an attack on Pearl Harbor. Unfortunately, his warning went unheeded since FBI Director Edgar Hoover mistrusted him. Popov died in his home in France in 1981 at the age of 68.
-3. Tony Mendez:
Even though Tony Mendez didn’t normally work in the field himself, he was considered a master of disguise for crafting all the documents, costumes, and personas that his fellow spies would need to travel undetected behind enemy lines. His skills were so impressive that he was able to make an Asian man and a black CIA agent look like two ordinary white businessmen to avoid being suspected by Laos counter-intelligence. Mendez most successful operation is now also his most famous thanks to the Oscar-winning cinematic treatment that Ben Affleck gave it in the 2012 film Argo. In the late 1970’s he had the ingenuity to come up with a fake movie production and use it as cover to help exfiltrate a group of American and Canadian ambassadorial hostages from Iran.
-4. Mata Hari:
Margaretha Geertruide MacLeod was a Dutch exotic dancer who went by the stage name Mata Hari. During World War I, the French Army recruited her as a spy, thinking that she would have many contacts from her days as a dancer and courtesan. She agreed to use her seductive methods to gather intelligence from German commanding officers, however, she was arrested by the French authorities in 1917 after they allegedly intercepted communications that identified her as a spy for the Germans. She was imprisoned, found guilty of espionage, and executed by firing squad in Paris. Yet, Mata Hari’s espionage activities remain a matter of debate, chiefly because the evidence used against her was vague and circumstantial. But according to many historians, she was likely a double agent working for the Germans. An account of Mata Hari’s life can be found in the biography Femme Fatale: Love Lies, and the Unknown Life of Mata Hari.
-5. Virginia Hall:
Virginia Hall was an American volunteer working in Paris when World War II broke out. After France’s surrender, she escaped to Britain where she joined the Special Operative Executive (SOE). Not long after, she was sent back to France and worked as a correspondent for the New York Post while she helped to coordinate the activities of the resistance in Vichy. Hall was allegedly regarded by the Germans as “the most dangerous of all Allied spies” and appeared on the Gestapo’s “most wanted” list as “the limping lady” — referring to the fact that she had shot herself in the foot in 1932, eventually resulting in her lower leg being amputated and replaced with a prosthetic limb. She named her wooden leg Cuthbert, and used it to hide numerous documents over the course of her spy career.
Figure above shows Fake birth certificate used by Virginia Hall during the Second World War; it gave her the alias of a Frenchwoman named Marcelle Montagne.
When the war was over, Hall joined the CIA and worked as an intelligence agent until her retirement in 1966. She died in 1982 at age 76.
-6. Oleg Penkovsky:
When the U.S. discovered Russian missile silos off the coast of Cuba, the Cold War heated up pretty quickly. Thankfully, the nuclear stand-off was de-escalated and we didn’t blow the planet to smithereens, but things could have been much worse if the Americans never discovered those weapons — and the only reason they did was thanks to the work of Oleg Penkovsky. Codenamed HERO, Penkovsky was a colonel with Soviet military intelligence who remained active in the field for decades and risked his life countless times leaking secrets to both the Americans and the British. But because the CIA believed he was constantly being watched, transmission of the sensitive materials proved extremely difficult. As it would happen the CIA was probably right. After shining a light on the Cuban missile situation, Penkovsky was apprehended by Soviet authorities, questioned, and shot.
-7. Richard Sorge:
Richard Sorge was a German-born Soviet spy who became a passionate communist while recovering from an injury he sustained in World War I. During World War II, he operated out of Japan and provided the Soviets with vital information regarding the intentions of both Japan and Nazi Germany. From the intelligence gathered by Sorge, the Soviets learned that Japan wasn’t planning an attack on Russia, but the Germans were. It’s even thought that he reported the impending Japanese attack on Pearl Harbor, although the message may have never actually reached the Allied forces. The information supplied by Sorge was thought to be so valuable that he could have been almost single-handedly responsible for halting the Nazis advance in 1941. Which is probably why Ian Fleming referred to him as “the man whom I regard as the most formidable spy in history.” Sadly, when Sorge was captured by Japanese forces, Stalin refused to secure his release, resulting in his execution in 1944. 20 years later, in 1964, Sorge was posthumously awarded the Hero of the Soviet Union distinction, the highest honorary title one can receive in the Soviet Union.
-8. Elyesa Bazna:
Elyesa Bazna was the Albanian valet to the British ambassador in 1943. He went to the German embassy in Ankara, Turkey, with an offer to provide sensitive military information. Bazna had virtually unfettered access to state secrets and was paid more than a million British pounds by Germany, much of which later proved to be counterfeit money. Banza photographed military information and gave it to members of the Third Reich. Between 1943 and 1944, he revealed key intelligence, including:
- Documents about stalled Anglo-Turkish negotiations about Turkey entering the war
- Details about Britain’s military weaknesses
- U.S. weapons being delivered to the Soviet Union
Bazna also gave the Germans a key piece of intelligence by revealing Allied plans for the D-Day invasion. This information included telegrams between Winston Churchill, Franklin D. Roosevelt, and Joseph Stalin about the planned attack. Bazna escaped capture by moving abroad, but he was later arrested and sent to prison on other charges.
-9. The Rosenbergs:
Figure above shows Julius and Ethel Rosenberg.
In the mid-1950s, the Intelligence Community mostly focused on people who spied on behalf of the Soviet Union. Ethel and Julius Rosenberg were Communist party members and Soviet spies who gave information about the atomic bomb to the Soviet Union. In 1942, Julius Rosenberg worked for the Army Signal Corps Engineering Laboratories and was recruited by the Soviet Union as a spy. However, Ethel Rosenberg’s involvement has been debated by historians for many years. Records and testimony indicate that she was aware of her husband’s activities but was not an active participant. Others say she played an active role in the espionage ring. In 1950, Julius and Ethel Rosenberg were arrested as part of an alleged spy ring that included Ethel Rosenberg’s brother David Greenglass. Greenglass admitted to stealing nuclear intelligence while working as a machinist at Los Alamos during the development of the nuclear bomb. According to Greenglass, he stole information at the direction of the Rosenbergs. Rosenberg provided the Soviet Union with sketches of the cross-section of an implosion-type atom bomb, the “Fat Man” bomb dropped on Nagasaki, Japan, as opposed to a bomb with the “gun method” triggering device as used in the “Little Boy” bomb dropped on Hiroshima.
Figure above shows the diagram of the atomic bomb provided by David Greenglass to the Soviets.
A federal court in New York found the Rosenbergs guilty of conspiracy to commit espionage and they were later executed. They are the only U.S. citizens to have been executed on espionage charges. David Greenglass was sentenced to 15 years in prison for his role in providing material related to the atomic bomb to the Russians.
-10. Aldrich Ames:
Aldrich Ames, a spy for the Soviet Union, was a long-time CIA case officer specializing in Russian intelligence. Under financial pressure, he succumbed to greed and began secretly worked on behalf of the KGB in 1975. Ames was reportedly paid $50,000 for his initial work passing classified information about FBI and CIA sources as well as technical operations to the Soviet Union. Some of those sources were apprehended and killed by Soviet authorities. The KGB later paid Ames nearly $2 million over four years. He used “dead drops” – hiding places where he would leave documents for KGB officers. When the FBI learned that Ames was working for the Russians, agents opened an investigation. During a lengthy surveillance operation, they observed Ames meeting with his Russian contacts and found documents connecting him to the KGB. In 1994, Ames and his wife were arrested on espionage charges and pled guilty. He was found guilty and sentenced to life in prison without the possibility of parole. His wife, Rosario Ames, was sentenced to 63 months in prison.
-11. Robert Hanssen:
Robert Hanssen was an FBI agent and counterintelligence officer for decades. During his career, Hanssen sold national security information to Russia and received over $1.4 million in cash and gems for his activities. Hanssen had access to classified information, which he shared with the KGB. The details he shared put lives at risk, including people working as FBI sources. In 2000, the FBI and CIA became aware of Hanssen’s espionage. The FBI swiftly initiated an investigation and gave him a bogus assignment at FBI headquarters so agents could actively monitor his activities. After discovering that Hanssen made a dead drop at one of his drop sites in Virginia, the FBI swooped in. Hanssen was arrested, pled guilty to 15 counts of espionage charges, was sentenced to life without parole, and died in prison in 2023.
-12. Linwei Ding:
Linwei Ding was a Chinese national and California resident, who was caught attempting to steal trade secrets from Google® about its artificial intelligence (AI) technology. Ding took proprietary information from Google and gave it to two Chinese AI organizations. A federal grand jury returned a superseding indictment this year charging Linwei Ding, also known as Leon Ding, 38, with seven counts of economic espionage and seven counts of theft of trade secrets in connection with an alleged plan to steal from Google LLC (Google) proprietary information related to AI technology. If convicted, Ding faces a maximum penalty of 10 years in prison and up to a $250,000 fine for each trade-secret count and 15 years in prison and $5,000,000 fine for each economic-espionage count.
______
______
Spy fiction:
Spies or secret agents are characters often found in literature, film, and television, known for their roles in intelligence and covert operations. They typically work for a government or organization, gathering and analyzing information, conducting surveillance, and undertaking secret missions, often involving risk and subterfuge. Spies are characterized by their skills in deception, combat, and intelligence gathering, operating under the guise of various cover identities. In narratives, they navigate complex plots involving espionage, political intrigue, and international conflicts. Their portrayal explores themes of loyalty, ethics, and the gray areas of morality in the world of international relations. The depiction of spies and secret agents often reflects societal attitudes towards security, patriotism, and the clandestine aspects of governmental operations.
_
The portrayal of spies and secret agents in fiction has its roots in early 20th-century literature, where they first appeared as intriguing characters in espionage and adventure stories. These early depictions often mirrored the geopolitical climate of the times, focusing on themes of war, patriotism, and international intrigue. During the Cold War era, the genre gained significant popularity, reflecting the era’s tensions and the fascination with espionage. Characters like James Bond became cultural icons, epitomizing the spy as a suave, skilled agent involved in high-stakes missions. Over time, the portrayal of spies evolved to include more complex and morally ambiguous figures, reflecting changing perceptions of international politics and espionage.
_
Spies have long been favourite topics for novelists and filmmakers. An early example of espionage literature is Kim by the English novelist Rudyard Kipling, with a description of the training of an intelligence agent in the Great Game between the UK and Russia in 19th century Central Asia. An even earlier work was James Fenimore Cooper’s classic novel, The Spy, written in 1821, about an American spy in New York during the Revolutionary War. During the many 20th-century spy scandals, much information became publicly known about national spy agencies and dozens of real-life secret agents. These sensational stories piqued public interest in a profession largely off-limits to human interest news reporting, a natural consequence of the secrecy inherent in their work. To fill in the blanks, the popular conception of the secret agent has been formed largely by 20th and 21st-century fiction and film. Attractive and sociable real-life agents such as Valerie Plame find little employment in serious fiction, however. The fictional secret agent is more often a loner, sometimes amoral—an existential hero operating outside the everyday constraints of society. Loner spy personalities may have been a stereotype of convenience for authors who already knew how to write loner private investigator characters that sold well from the 1920s to the present.
_
Spy fiction has permeated the video game world as well, in games such as Perfect Dark, GoldenEye 007, No One Lives Forever, Tom Clancy’s Splinter Cell and the Metal Gear series. Espionage has also made its way into comedy depictions. The 1960s TV series Get Smart, the 1983 Finnish film Agent 000 and the Deadly Curves, and Johnny English film trilogy portrays an inept spy, while the 1985 movie Spies Like Us depicts a pair of none-too-bright men sent to the Soviet Union to investigate a missile. Black Widow is also a fictional agent who was introduced as a Russian spy, an antagonist of the superhero Iron Man. She later became an agent of the fictional spy agency S.H.I.E.L.D. and a member of the superhero team the Avengers. Real espionage is actually quite boring work.
_____
_____
Ethical Considerations in Espionage:
Civilisations have engaged in espionage since biblical times — but the ethics of spying remain as murky as ever. States need information on what their enemies are thinking. But — since “hostile” and “allied” are fluid categories — this applies to friends too. Hence spying has been inseparable from civilisations. It even has a biblical pedigree. As Christopher Andrew writes, the “first major figure in world literature to emphasise the importance of good intelligence was God” — ordering Moses to send undercover agents ahead to “spy out the land of Canaan”, a place divinely promised, yet unknown. The spooks, it seems, have always been among us. The ancient origins of intelligence networks are rarely discussed. Yet, while their modern manifestations share the same fundamental rationale for existence as those biblical envoys, they are — in the permanence of their establishments and the size of their budgets — far from the scrappy, if talented, groups who made up the “secret services” before professionalisation in the 20th century. The greater destructiveness of wars and the added Armageddon quality of nuclear weaponry; the increased, lethal power of terrorism, especially jihadism — whose leading figures, such as the late Osama bin Laden, sought weapons of mass destruction; and the appearance of new challenges, such as cyber terrorism — all these bolster the case for the intelligence services, and the resources allotted to them. Along the way, the secret services have become more valued, more visible — and more controversial. Public concern over the ability of spooks to monitor communications was roused by the leaks from the US National Security Agency, and deepened by the revelations of torture practised on terrorist suspects by the CIA, an agency that had claimed a high ethical ground.
_
Ethical considerations in espionage involve the complex interplay between national security interests and individual rights. Espionage tactics and techniques can infringe upon privacy and civil liberties, raising questions about the morality of spying and its impact on innocent individuals. The justification for espionage typically rests on national security imperatives. However, the legitimacy of invading personal or organizational boundaries can lead to significant ethical dilemmas. The potential for abuse increases, particularly when states conduct covert operations without proper oversight. Furthermore, the rise of cyber espionage presents new ethical challenges. The delicate balance between gathering intelligence and upholding ethical standards becomes increasingly intricate in the digital realm. Unchecked surveillance or hacking could threaten not only state security but also global trust and stability.
_
National security concerns significantly intersect with espionage, as the risks associated with covert activities pose substantial threats to a nation’s stability and integrity. Espionage can lead to intelligence breaches, undermining both governmental authority and public safety. Threats posed by espionage may include unauthorized access to classified information and the use of gathered intelligence to manipulate political landscapes. Such activities not only compromise security but also jeopardize the safety of citizens and allies. The balance between security and privacy emerges as a critical issue in addressing espionage risks. As governments enhance surveillance and intelligence capabilities to counter threats, they must also safeguard individual rights and freedoms, creating a complex dynamic. Mitigation strategies for espionage risks involve a multi-faceted approach, including enhancing cybersecurity measures, conducting regular threat assessments, and fostering international cooperation. These strategies aim to bolster national security while navigating the delicate terrain of ethical governance.
_
Espionage, though often deemed necessary for national security, raises significant legal and ethical questions.
Legally, espionage operates in a gray zone, as countries may adopt laws that vary widely regarding surveillance and intelligence gathering techniques. This disparity can lead to international disputes over legitimacy.
Ethically, the practice of espionage can infringe on personal privacy and sovereignty. Ethical considerations include the potential harm caused to innocent individuals and the broader implications on civil rights. A few focal points are:
-1. The justification for covert actions versus the potential for collateral damage.
-2. The need for oversight to prevent abuse of power.
-3. The moral implications of influencing foreign political systems.
While espionage may serve governmental interests, the legal frameworks surrounding it must balance security with human rights. Understanding these considerations is essential in analyzing the role of espionage and political influence in contemporary society.
_
Espionage involves a set of practices—such as deception, betrayal, and intrusion—that are ethically contentious in most other contexts. Key ethical challenges include:
Deception as a Core Strategy:
Spies routinely lie about their identities, intentions, and affiliations. While deception is necessary for operational success, it undermines trust and raises questions about the morality of lying for a perceived greater good (Bok, 1978).
Exploitation of Vulnerabilities:
Emotional manipulation often involves exploiting personal or professional weaknesses, which can cause significant psychological harm to targets (Herman, 1996).
Breach of Privacy:
Intelligence operations often involve surveillance and the collection of sensitive personal information, raising concerns about violations of privacy and civil liberties (Singer & Friedman, 2014).
Collateral Damage:
Espionage operations can have unintended consequences, such as harming innocent bystanders or destabilizing communities, further complicating their ethical justification (Bailey, 2016).
_
Real-Life Examples:
The Double-Cross System (World War II): During World War II, British intelligence ran the Double-Cross System, in which captured German spies were turned into double agents. While the system was highly effective in feeding false information to the Nazis, it also raised ethical questions about the manipulation and potential endangerment of these operatives, many of whom were coerced into cooperation (Andrew, 1999).
Targeted Assassinations by Mossad: Israel’s Mossad has been involved in numerous targeted killings, such as the assassination of Ali Hassan Salameh, a key planner of the Munich Olympics massacre. While these actions are often framed as justice, critics argue that they constitute extrajudicial killings and violate international law (Klein, 2007).
Mass Surveillance by the NSA: The National Security Agency’s mass data collection programs, revealed by Edward Snowden in 2013, sparked global debates about the balance between national security and individual privacy. While proponents argued that the programs were necessary to prevent terrorism, critics condemned them as an overreach of government power and a violation of human rights (Gellman, 2014).
_
Years after the Snowden revelations on mass surveillance and after the emergence of extraordinary rendition scandals, the debate on the role of ethics in intelligence gatherings has never been as prominent, and is dominated by opposing perspectives. On the one hand is the view that the very nature of intelligence work is unethical, but such work needs to be done to protect national security. On the other is the view that it is precisely this unethical nature that undermines the legitimacy and security of democratic states, and therefore is unacceptable. The response from the public and civil society actors to scandals around extraordinary rendition and mass surveillance has been a resurgence of a fundamental debate on the extent to which democratic laws and values are being compromised to protect national security. Espionage may have been defined once primarily as an external activity of a state but by now that meaning has long since been overwhelmed by other forms of espionage, including industrial espionage perpetrated by corporations and individuals, as well as by states. The data targeted in cyber-attacks is often personal and sensitive. Cyber security professionals have access to the sensitive personal data they were hired to protect. So it’s imperative that employees in these fields have a strong sense of ethics and respect for the privacy of your customers. Many companies focus only on the technical abilities of a candidate for hire, but it’s not enough that the staff have knowledge of technology and hacking techniques. They must also demonstrate the ability to maintain their moral standards while processing customer data or handling other grey areas of data management and cyber security.
_
Unauthorized disclosure of sensitive or proprietary information to the media for political purposes is an age-old feature of political life and will remain a permanent fixture of any democratic society with a free press. Those seeking political advantages through such disclosures generally partner with established media outlets, both to ensure an extensive audience and to gain legitimacy; they presume that audiences will assume the media partner has screened and verified the information before using it. Less well known is that professional members of the media usually seek comment from relevant members of the Intelligence Community before making public classified information they have acquired. Sometimes they will revise their drafts to mitigate credible risks described to them by the Intelligence Community or may even withhold a story when they are convinced that risks to national security, US citizens, or US allies or innocent persons are too high.
_
Justifications in Espionage: Do the ends justify the means?
The ethical dilemmas at the heart of espionage ignite fierce debates among scholars, policymakers, and the public. Central to these discussions is the question: do the ends justify the means? Can acts of deception, manipulation, or even betrayal be excused if they serve a greater good? While some argue that the stakes in intelligence work necessitate such measures, others contend that crossing ethical boundaries risks undermining the very values and principles espionage is meant to protect. This ongoing debate highlights the need for transparency, accountability, and a revaluation of the moral compass guiding intelligence operations in an increasingly complex world.
What is the ethical limit of intelligence gathering? The ethical limits of intelligence gathering remain one of the most contested issues in modern espionage. How far can operatives go in the name of national security or global stability? At what point does the pursuit of intelligence cross into moral violations, such as invading privacy, exploiting vulnerabilities, or inflicting psychological harm? Striking a balance between safeguarding interests and maintaining ethical integrity requires a nuanced approach, where transparency, accountability, and respect for human rights guide decision-making. Defining these limits is paramount in ensuring intelligence operations serve justice without compromising the values they are meant to protect.
How should accountability be enforced? Enforcing accountability in intelligence operations requires a multifaceted approach. Robust oversight mechanisms, both internal and external, are essential to ensure that actions align with ethical standards and legal frameworks. Independent review boards, transparent reporting, and checks on power can help prevent abuses while maintaining operational effectiveness. Additionally, whistleblower protections must be strengthened to allow individuals within the system to report misconduct without fear of retaliation. Ultimately, accountability must be ingrained in the culture of intelligence agencies, balancing secrecy with responsibility to uphold the values they aim to protect.
______
______
Antidote to spying:
Spies have a terrible reputation. As agents of deception and theft, they arouse suspicion and anger wherever they go. States that employ spies risk a hostile response, suggesting that espionage is a precursor to war. Perhaps this is one reason why they have been held in such disdain for so long. Ancient Greek generals were heroic figures; ancient Greek spies were subject to torture and execution. The Arabic tradition viewed foreign intelligence agents as beneath contempt, and the Arabic word for spies, jasous, was originally a slur. The French word espion was a pejorative in Ancien Régime France, associating spies with agents provocateurs who destabilised governments and opened the door to foreign aggression. The Catholic and Anglican churches formerly referred to the day before Passover as ‘Spy Wednesday’, in commemoration of Judas Iscariot’s efforts to see how much money he could receive for betraying Jesus. Historians have linked enthusiasm for espionage to rapacious authoritarian regimes such as the Mauryan and Mogul Empires. Their leaders found inspiration in Kautilya’s Arthashastra, which includes ruthless recommendations on the dark arts.
For liberal statesmen at the turn of the twentieth century, the antidote to secret intelligence was transparent diplomacy. Transparency alone would not guarantee international stability, but it would make it easier for leaders to work together. Resisting the urge to hoard secrets helps reduce fear that others are cheating on agreements, shirking their obligations or plotting military aggression. International institutions, not secret intelligence agencies, were the safest places to gather information. National security did not flow from espionage and subterfuge but from open diplomacy. It is no accident that Woodrow Wilson’s post-war vision rested on ‘Open covenants of peace, openly arrived at’. Of his 14 points, this was the first and most vital.
_
The Future of Espionage:
As global dynamics shift, the future of espionage will likely be shaped by rapidly advancing technologies and evolving geopolitical landscapes. State and non-state actors will increasingly employ sophisticated espionage tactics and techniques to gather intelligence and maintain national security.
A significant trend is the rising prominence of artificial intelligence in espionage, enhancing data analysis, and streamlining information collection. This technology could facilitate real-time surveillance and predictive analytics, allowing agencies to anticipate threats more effectively than ever before.
Moreover, the integration of quantum computing will redefine encryption methods, creating unprecedented challenges for traditional counterintelligence measures. As cyber espionage becomes more complex, ethical considerations surrounding privacy and individual rights will need to be addressed thoughtfully.
The future of espionage will also see an increased focus on collaboration across national borders. International coalitions may emerge to tackle common security threats, necessitating a re-evaluation of established espionage tactics and techniques. Emphasizing transparency and accountability will be vital in navigating this evolving landscape.
As the landscape of espionage continues to evolve, understanding the intricate espionage tactics and techniques employed by various entities becomes crucial. Modern espionage encapsulates a blend of traditional methods and innovative technologies that shape the future of intelligence gathering.
The ongoing development of covert operations, surveillance methods, and cyber espionage underscores the necessity for continuous adaptation. Ethical considerations and counterintelligence measures play pivotal roles in determining the effectiveness and legality of these operations, ultimately influencing international relations and security dynamics.
_____
_____
Section-3
History of spying:
_
Evolution of Espionage:
Spies, or scouts, have had to communicate secretly since time immemorial. In ancient Greece, Histiaeus, the ruler of Miletus, shaved a slave’s head, tattooed it with a message, and waited for the hair to grow back. He then sent the messenger on the long journey from Persia to Greece to urge revolt. Upon arrival, the messenger’s head was shaved again to read the message.
Espionage has undergone significant changes throughout history, adapting to the political, technological, and social landscapes of various eras. Initially practiced by ancient civilizations, espionage tactics and techniques were rudimentary, often relying on human intelligence gathered through informants and spies.
With the rise of nation-states, particularly during the Renaissance, espionage began to evolve into a more organized practice. Diplomats and military commanders increasingly utilized covert means to gain insights into enemy strategies, paving the way for sophisticated methods of intelligence gathering. The adoption of cryptography was a notable advancement in clandestine communication.
The 20th century marked a drastic transformation in espionage, driven by technological innovation. The World Wars saw the emergence of complex operations, including signal intelligence and aerial reconnaissance. During the Cold War, agencies like the CIA and KGB honed their espionage tactics, employing undercover operations and advanced surveillance techniques.
In the modern era, cyber espionage has emerged as a crucial aspect of national security. The integration of technology into espionage tactics and techniques has shifted focus to online platforms, where information is collected and analyzed at unprecedented speeds. This evolution continues to shape the landscape of intelligence operations today.
_____
Early history:
No single person has had a bigger impact on the intelligence discipline as Sun Tzu. It is rare to find an intelligence professional who does not have a copy of the Art of War and many can quote directly from it. There is a lot of disagreement surrounding the life of Sun Tzu, but most scholars believe he lived in the fifth century BCE and served as a general to the king of the Wu kingdom. The Art of War is believed to be a compendium of his thoughts on war based on his successes as a general. However, there is some debate as to whether or not The Art of War is solely the work of Sun Tzu, or a compilation of work from many different authors. Irrespective of the origins of The Art of War, in the book Sun Tzu lays out many strategy and intelligence ideas still followed today. Sun Tzu’s ancient treatise The Art of War has inspired leaders from Napoleon to Fidel Castro, Joseph Stalin, and former CIA director General David Petraeus. “Sun Tzu’s classic work is, in short, a fascinating mixture of the poetic and the pragmatic, and every bit as relevant now as when it was written,” General Petraeus writes in his introduction to The Art of War’s 2018 edition. Hollywood and Wall Street’s Gordon Gekko are also fans. “I don’t throw darts at a board. I bet on sure things,” Gekko (Michael Douglas) tells Bud Fox (Charlie Sheen). “Read Sun Tzu, The Art of War. Every battle is won before it’s ever fought.”
_
Figure above shows bamboo version of The Art of War, written by Sun Tzu in ancient China explores espionage tactics.
_
Efforts to use espionage for military advantage are well documented throughout history. Sun Tzu, a theorist in ancient China who influenced Asian military thinking, still has an audience in the 21st century for the Art of War. He advised, “One who knows the enemy and knows himself will not be endangered in a hundred engagements.” He stressed the need to understand yourself and your enemy for military intelligence. He identified different spy roles. In modern terms they included the secret informant or agent in place, (who provides copies of enemy secrets), the penetration agent who has access to the enemy’s commanders, and the disinformation agent who feeds a mix of true and false details to point the enemy in the wrong direction, (to confuse the enemy). He considered the need for systematic organization, and noted the roles of counterintelligence, double agents (recruited from the ranks of enemy spies) and psychological warfare. Sun Tzu continued to influence Chinese espionage theory in the 21st century with its emphasis on using information to design active subversion.
_
Chanakya (also called Kautilya) wrote his Arthashastra in India in the 4th century BC. It was a ‘Textbook of Statecraft and Political Economy’ that provides a detailed account of intelligence collection, processing, consumption, and covert operations, as indispensable means for maintaining and expanding the security and power of the state. The Arthashastra is taught prolifically around the world today. Kautilyan doctrine, a core component of the Arthashastra, has experienced a particularly notable resurgence in popularity. In the one hundred and fifty parts that make up this document, over 50 of them have references to espionage and the use of spies. In the work, ancient Indian thinker Kautilya lays out the precise ways in which a king is to rule, including modes of administration, means of warfare, diplomatic strategy and economic policies. He provides what is perhaps the first ever professional classification for spies. There are two primary types of spies in his framework, both of whom directly report to the king. They are the Samstha, or stationary spies, and the Sanchara, or roaming spies. The Samstha are usually stationed in other kingdoms, suspicious areas and forest lands. Intelligence gathering seems to be their primary objective, having infiltrated into critical areas under the guise of civilians. They send reports and updates to their home base on the capabilities of rival States and internal suspects. The Sanchara, on the other hand, were used for more violent purposes. They were meant to be adept in science, the use of poisons, combat, and disguise. The Sanchara class of spies would be more akin to the ‘James Bond’ stereotype and the glamorized version of spies found in fiction. The categorization does not end there however. Kautilya meticulously describes the various sub-types that fall under each class of spy, as well as their functions. These go even further in helping us understand the genesis of spy networks. Under the Samstha, classifications derive from the segments of society the spies were recruited from: Kapatika (students), Udashita (recluses), Grihapatika (landlords), Vaideheka (merchants) and Tapasa (ascetics). The Sanchara, or roaming spies, on the other hand, were categorized based on their specialties: Satri (secret agents), Tikshna (mercenaries), Rasada (poisoners) and Bhiksuki (nuns).
_
Ancient Egypt had a thoroughly developed system for the acquisition of intelligence. The Hebrew used spies as well, as in the story of Rahab. Thanks to the Bible (Joshua 2:1–24) we have in this story of the spies sent by Hebrews to Jericho before attacking the city, one of the earliest detailed report of a very sophisticated intelligence operation. Spies were also prevalent in the Greek and Roman empires. No civilization in the ancient world relied more heavily on intelligence information, nor furthered the development of espionage more than ancient Rome. Over a millennium, the Romans created the largest empire of the ancient world, necessitating the governance of the most expansive infrastructure, military, and bureaucracy or the period. Rome’s most famous case of espionage and intrigue culminated in the assassination of Julius Caesar on March 15, 44 BC. The exact details of the assassination conspiracy remain a mystery to historians, but records have established that the Roman intelligence community knew of the plot and even provided information to Caesar or his assistants providing the names of several conspirators. The information from the intelligence community was ignored. The ever-expanding Roman Empire often spied on its neighbors. Not only did intelligence forces provide comprehensive reports on the military strength and resources of those outside the empire, but the Roman military also employed intelligence forces to infiltrate tribal organizations and convince leaders to join in alliance with Rome. If populations were judged hostile by informants, the military was informed, and engaged the opposing forces.
During the 13th and 14th centuries, the Mongols relied heavily on espionage in their conquests in Asia and Europe. Feudal Japan often used shinobi to gather intelligence.
A significant milestone was the establishment of an effective intelligence service under King David IV of Georgia at the beginning of 12th century or possibly even earlier. Called mstovaris, these organized spies performed crucial tasks, like uncovering feudal conspiracies, conducting counter-intelligence against enemy spies, and infiltrating key locations, e.g. castles, fortresses and palaces.
Aztec used Pochtecas, people in charge of commerce, as spies and diplomats, and had diplomatic immunity. Along with the pochteca, before a battle or war, secret agents, quimitchin, were sent to spy amongst enemies usually wearing the local costume and speaking the local language, techniques similar to modern secret agents.
_____
Early Modern Europe:
In the Middle Ages, the birth of large nation-states, such as France and England, in the ninth and tenth centuries facilitated the need for intelligence in a diplomatic setting. Systems of couriers, translators, and royal messengers carried diplomatic messages between monarchs or feudal lords. Literacy was a rarity, even in the early royal courts, so messages were carefully delivered verbatim by couriers, or clergy acted as scribes. Espionage remained mostly limited to battlefield operations, but the development of the feudal system, in which lords swore fealty to monarchs, created a complicated allegiance network. The web of allegiances gave rise to laws prohibiting treason, double allegiances, and political espionage against allied lords.
_
Many modern espionage methods were established by Francis Walsingham in Elizabethan England. His staff included the cryptographer Thomas Phelippes, who was an expert in deciphering letters and forgery, and Arthur Gregory, who was skilled at breaking and repairing seals without detection. The Catholic exiles fought back when the Welsh exile Hugh Owen created an intelligence service that tried to neutralize that of Walsingham.
In 1585, Mary, Queen of Scots was placed in the custody of Sir Amias Paulet, who was instructed to open and read all of Mary’s clandestine correspondence. In a successful attempt to expose her, Walsingham arranged a single exception: a covert means for Mary’s letters to be smuggled in and out of Chartley in a beer keg. Mary was misled into thinking these secret letters were secure, while in reality they were deciphered and read by Walsingham’s agents. He succeeded in intercepting letters that indicated a conspiracy to displace Elizabeth I with Mary. In foreign intelligence, Walsingham’s extensive network of “intelligencers”, who passed on general news as well as secrets, spanned Europe and the Mediterranean. While foreign intelligence was a normal part of the principal secretary’s activities, Walsingham brought to it flair and ambition, and large sums of his own money. He cast his net more widely than anyone had attempted before, exploiting links across the continent as well as in Constantinople and Algiers, and building and inserting contacts among Catholic exiles.
______
18th Century
The 18th century saw a dramatic expansion of espionage activities. It was a time of war: in nine years out of 10, two or more major powers were at war. Armies grew much larger, with corresponding budgets. Likewise the foreign ministries all grew in size and complexity. National budgets expanded to pay for these expansions, and room was found for intelligence departments with full-time staffs, and well-paid spies and agents. The militaries themselves became more bureaucratised, and sent out military attaches. They were very bright, personable middle-ranking officers stationed in embassies abroad. In each capital, the attached diplomats evaluated the strength, capabilities, and war plans of the armies and navies.
_
France
France under King Louis XIV (1643–1715) was the largest, richest, and most powerful nation. It had many enemies and a few friends, and tried to keep track of them all through a well organized intelligence system based in major cities all over Europe. France and England pioneered the cabinet noir whereby foreign correspondence was opened and deciphered, then forwarded to the recipient. France’s chief ministers, especially Cardinal Mazarin (1642–1661) did not invent the new methods; they combined the best practices from other states, and supported it at the highest political and financial levels.
To critics of authoritarian governments, it appeared that spies were everywhere. Parisian dissidents of the 18th century thought that they were surrounded by as many as perhaps 30,000 police spies. However, the police records indicate a maximum of 300 paid informers. The myth was deliberately designed to inspire fear and hypercaution; the police wanted opponents’ people to think that they were under close watch. The critics also seemed to like the myth, for it gave them a sense of importance and an aura of mystery. Ordinary Parisians felt more secure believing that the police were actively dealing with troublemakers.
Britain
To deal with the almost continuous wars with France, London set up an elaborate system to gather intelligence on France and other powers. Since the British had deciphered the code system of most states, it relied heavily on intercepted mail and dispatches. A few agents in the postal system could intercept likely correspondence and have it copied and forwarded to the intended receiver, as well as to London. Active spies were also used, especially to estimate military and naval strength and activities. Once the information was in hand, analysts tried to interpret diplomatic policies and intentions of states. Of special concern in the first half of the century were the activities of Jacobites, Englishmen who had French support in plotting to overthrow the Hanoverian kings of England. It was a high priority to find men in England and Scotland who had secret Jacobite sympathies.
One highly successful operation took place in Russia under the supervision of minister Charles Whitworth (1704 to 1712). He closely observed public events and noted the changing power status of key leaders. He cultivated influential and knowledgeable persons at the royal court, and befriended foreigners in Russia’s service, and in turn they provided insights into high-level Russian planning and personalities, which he summarized and sent in code to London.
Industrial espionage
In 1719 Britain made it illegal to entice skilled workers to emigrate. Nevertheless, small-scale efforts continued in secret. At mid century, (1740s to 1770s) the French Bureau of Commerce had a budget and a plan, and systematically hired British and French spies to obtain industrial and military technology. They had some success deciphering English technology regarding plate-glass, the hardware and steel industry. They had mixed success, enticing some workers and getting foiled in other attempts.
The Spanish were technological laggards, and tried to jump start industry through systematized industrial espionage. The Marquis of Ensenada, a minister of the king, sent trusted military officers on a series of missions between 1748 and 1760. They focused on current technology regarding shipbuilding, steam engines, copper refining, canals, metallurgy, and cannon-making.
American Revolution, 1775–1783
During the American Revolution, 1775–1783, American General George Washington developed a successful espionage system to detect British locations and plans. In 1778, he ordered Major Benjamin Tallmadge to form the Culper Ring to collect information about the British in New York. Washington was usually mindful of treachery, but he ignored incidents of disloyalty by Benedict Arnold, his most trusted general. Arnold tried to betray West Point to the British Army, but was discovered and barely managed to escape. The British intelligence system was weak; it completely missed the movement of the entire American and French armies from the Northeast to Yorktown, Virginia, where they captured the British invasion army in 1781 and won independence. Washington has been called “Americas First Spymaster”.
French Revolution and Napoleonic wars, (1793–1815)
Britain, almost continuously at war with France (1793–1815), built a wide network of agents and funded local elements trying to overthrow governments hostile to Britain. It paid special attention to threats of an invasion of the home islands, and to a possible uprising in Ireland. Britain in 1794 appointed William Wickham as Superintendent of Aliens in charge of espionage and the new secret service. He strengthened the British intelligence system by emphasizing the centrality of the intelligence cycle – query, collection, collation, analysis and dissemination – and the need for an all-source centre of intelligence.
Napoleon made heavy use of agents, especially regarding Russia. Besides espionage, they recruited soldiers, collected money, enforced the Continental System against imports from Britain, propagandized, policed border entry into France through passports, and protected the estates of the Napoleonic nobility. His senior men coordinated the policies of satellite countries.
_______
19th century
Modern tactics of espionage and dedicated government intelligence agencies were developed over the course of the late 19th century. A key background to this development was the Great Game, a period denoting the strategic rivalry and conflict that existed between the British Empire and the Russian Empire throughout Central Asia. To counter Russian ambitions in the region and the potential threat it posed to the British position in India, a system of surveillance, intelligence and counterintelligence was built up in the Indian Civil Service. The existence of this shadowy conflict was popularised in Rudyard Kipling’s famous spy book, Kim, where he portrayed the Great Game (a phrase he popularised) as an espionage and intelligence conflict that “never ceases, day or night.”
Great Game cartoon from 1878:
Figure above shows political cartoon depicting the Afghan Emir Sher Ali with his “friends” the Russian Bear and British Lion (1878). The Great Game saw the rise of systematic espionage and surveillance throughout the region by both powers.
_
Although the techniques originally used were distinctly amateurish – British agents would often pose unconvincingly as botanists or archaeologists – more professional tactics and systems were slowly put in place. In many respects, it was here that a modern intelligence apparatus with permanent bureaucracies for internal and foreign infiltration and espionage was first developed. A pioneering cryptographic unit was established as early as 1844 in India, which achieved some important successes in decrypting Russian communications in the area. The establishment of dedicated intelligence organizations was directly linked to the colonial rivalries between the major European powers and the accelerating development of military technology.
An early source of military intelligence was the diplomatic system of military attachés (an officer attached to the diplomatic service operating through the embassy in a foreign country), that became widespread in Europe after the Crimean War. Although officially restricted to a role of transmitting openly received information, they were soon being used to clandestinely gather confidential information and in some cases even to recruit spies and to operate de facto spy rings.
_
Counterintelligence:
As espionage became more widely used, it became imperative to expand the role of existing police and internal security forces into a role of detecting and countering foreign spies. The Austro-Hungarian Evidenzbureau was entrusted with the role from the late 19th century to counter the actions of the Pan-Slavist movement operating out of Serbia.
Russia’s Okhrana was formed in 1880 to combat political terrorism and left-wing revolutionary activity throughout the Russian Empire, but was also tasked with countering enemy espionage. Its main concern was the activities of revolutionaries, who often worked and plotted subversive actions from abroad. It created an antenna in Paris run by Pyotr Rachkovsky to monitor their activities. The agency used many methods to achieve its goals, including covert operations, undercover agents, and “perlustration” — the interception and reading of private correspondence. The Okhrana became notorious for its use of agents provocateurs who often succeeded in penetrating the activities of revolutionary groups including the Bolsheviks.
Figure below shows St. Petersburg Okhrana group photo, 1905.
The Okhrana was founded in Russia in 1880 and was tasked with countering enemy espionage.
________
20th century
Civil intelligence agencies
In Britain, the Secret Service Bureau was split into a foreign and counter intelligence domestic service in 1910. The latter was headed by Sir Vernon Kell and was originally aimed at calming public fears of large scale German espionage. As the Service was not authorized with police powers, Kell liaised extensively with the Special Branch of Scotland Yard (headed by Basil Thomson), and succeeded in disrupting the work of Indian revolutionaries collaborating with the Germans during the war.
Integrated intelligence agencies run directly by governments were also established. The British Secret Service Bureau was founded in 1909 as the first independent and interdepartmental agency fully in control over all government espionage activities.
_____
First World War
By the outbreak of the First World War in 1914 all the major powers had highly sophisticated structures in place for the training and handling of spies and for the processing of the intelligence information obtained through espionage. The figure and mystique of the spy had also developed considerably in the public eye. The Dreyfus Affair, which involved international espionage and treason, contributed much to public interest in espionage from 1894 onwards.
The spy novel emerged as a distinct genre of fiction in the late 19th century; it dealt with themes such as colonial rivalry, the growing threat of conflict in Europe and the revolutionary and anarchist domestic threat. The “spy novel” was defined by The Riddle of the Sands (1903) by author Erskine Childers, which played on public fears of a German plan to invade Britain (an amateur spy uncovers the nefarious plot). In the wake of Childers’s success there followed a flood of imitators, including William Le Queux and E. Phillips Oppenheim.
The first World War (1914–1918) saw the honing and refinement of modern espionage techniques as all the belligerent powers utilized their intelligence services to obtain military intelligence, to commit acts of sabotage and to carry out propaganda. As the progress of the war became static and armies dug down in trenches, the utility of cavalry reconnaissance became of very limited effectiveness.
Information gathered at the battlefront from the interrogation of prisoners-of-war typically could give insight only into local enemy actions of limited duration. To obtain high-level information on an enemy’s strategic intentions, its military capabilities and deployment required undercover spy rings operating deep in enemy territory. On the Western Front the advantage lay with the Western Allies, as for most of the war German armies occupied Belgium and parts of northern France amidst a large and disaffected native population that could be organized into collecting and transmitting vital intelligence.
British and French intelligence services recruited Belgian or French refugees and infiltrated these agents behind enemy lines via the Netherlands – a neutral country. Many collaborators were then recruited from the local population, who were mainly driven by patriotism and hatred of the harsh German occupation. By the end of the war the Allies had set up over 250 networks, comprising more than 6,400 Belgian and French citizens. These rings concentrated on infiltrating the German railway network so that the Allies could receive advance warning of strategic troop and ammunition movements.
_
Figure below shows Mata Hari:
In 1917, French authorities executed Mata Hari, a famous exotic dancer, on charges of espionage for Germany.
_
Two new methods for intelligence collection were developed over the course of the war – aerial reconnaissance and photography, and the interception and decryption of radio signals. The British rapidly built-up great expertise in the newly emerging field of signals intelligence and codebreaking.
Room 40, under Director of Naval Education Alfred Ewing, formed in October 1914, was the section in the British Admiralty most identified with the British crypto analysis effort during the war. The basis of Room 40 operations evolved around a German naval codebook, the Signalbuch der Kaiserlichen Marine (SKM), and around maps (containing coded squares), which were obtained from three different sources in the early months of the war. Alfred Ewing directed Room 40 until May 1917, when direct control passed to Captain (later Admiral) Reginald ‘Blinker’ Hall, assisted by William Milbourne James.
Room 40 played an important role in several naval engagements during the war, notably in detecting major German sorties into the North Sea that led to the battles of Dogger Bank and Jutland when the British fleet was sent out to intercept them. However its most important contribution was probably in decrypting the Zimmermann Telegram, a telegram from the German Foreign Office sent via Washington to its ambassador Heinrich von Eckardt in Mexico.
In the Telegram’s plain text, Nigel de Grey and William Montgomery learned of the German Foreign Minister Arthur Zimmermann’s offer to Mexico to join the war as a German ally. The telegram was made public by the United States, which declared war on Germany on 6 April 1917. This event demonstrated how the course of a war could be changed by effective intelligence operations.
Figure below depicts Codebreaking:
The interception and decryption of the Zimmermann telegram by Room 40 at the Admiralty was of pivotal importance for the outcome of the war.
______
Second World War
The Enigma machine is a cipher device developed and used in the early- to mid-20th century to protect commercial, diplomatic, and military communication. It was employed extensively by Nazi Germany during World War II, in all branches of the German military. The Enigma machine was considered so secure that it was used to encipher the most top-secret messages. The Enigma has an electromechanical rotor mechanism that scrambles the 26 letters of the alphabet. In typical use, one person enters text on the Enigma’s keyboard and another person writes down which of the 26 lights above the keyboard illuminated at each key press. If plaintext is entered, the illuminated letters are the ciphertext. Entering ciphertext transforms it back into readable plaintext. The rotor mechanism changes the electrical connections between the keys and the lights with each keypress. The security of the system depends on machine settings that were generally changed daily, based on secret key lists distributed in advance, and on other settings that were changed for each message. The receiving station would have to know and use the exact settings employed by the transmitting station to decrypt a message.
Figure above shows Military Model Enigma I, in use from 1930.
_
Operation magic
Operation Magic was the cryptonym given to United States efforts to break Japanese military and diplomatic codes during World War II. The United States Army Signals Intelligence Section (SIS) and the Navy Communication Special Unit worked in tandem to monitor, intercept, decode, and translate Japanese messages. Intelligence information gathered from the messages was sent to military command at the Office of Strategic Services (OSS). The ability to decipher and read Japanese communications was one of the key components of the Allied victory in the Pacific.
Even before the outbreak of World War II in Europe in 1939, the United States began its efforts to decode Japanese diplomatic and military communications. In 1923, a United States Navy intelligence officer obtained contraband copy of the World War I era Japanese Imperial Navy Secret Operating Code. Photographs of the codebook were passed on to the cryptologists at the Research Desk, where code was placed in red folders after the additive code keys were fully discovered. The simple additive code became known as “Red,” after the folders in which it was stored.
For high-level communications, the Japanese replaced Red with Blue, a more sophisticated code in 1930. However, the new code too closely resembled its predecessor, allowing United States cryptologists to fully break the new cipher in less than two years. At the outbreak of World War II, the Japanese were still using both Red and Blue for various communications. U.S. military intelligence established listening stations throughout the Pacific to monitor ship-to-ship, command-to-fleet, and land-based communications.
After war broke out in Europe, the Japanese received encryption and security help from Nazi Germany. The Germans had discovered that U.S. intelligence was monitoring and decoding Japanese communications as early as 1935, but they did not immediately inform the Japanese. Later, Germany sent a copy of their infamous Enigma encryption machine, with a few modifications, to help secure Japanese communications. As a result, U.S. intelligence could no longer read Japanese intercepts. The painstaking work of U.S. cryptologists began anew.
U.S. cryptanalysts named the new code Purple. Applied to several variations of the initial Enigma code, Purple provided the most significant challenge to both United States and British intelligence during the war.
With the aid of information from Polish and Swedish cryptologists, the British military intelligence cryptanalysis unit at Bletchley Park first broke the German Enigma code. They then developed sophisticated decoding bombes and the first programmable computer to facilitate the deciphering of the complex Enigma code. By 1943, British intelligence was able to utilize almost real-time intelligence information received from translated Enigma intercepts.
In the United States, cryptologists struggled to break the Purple by hand. However, the structure of Japanese messages, always beginning with the same introductory phrase, aided code breakers in determining the sequencing of the multi-rotored Japanese cipher machine. United States code breakers had made significant progress on the Purple code by 1941, gaining the ability to read several lines of intercepts. The process remained slow, and the information gained from Purple was usually outdated by the time it was translated.
Aware of British successes against the German Enigma machine, United States military intelligence asked their ally to share code-breaking information. The British sent top Bletchley Park cryptographers and engineers to the United States to help train code breakers and build decoding bombes. However, they closely guarded, and did not share, the secret of Enigma code breaking efforts (code named Operation Ultra) that involved Colossus, the Bletchley Park decoding computer.
With the aid of the British, United States intelligence made significant progress against Purple in a short time. A replica of the Japanese Purple machine, built in 1939 by American cryptologist William Friedman, was used to adapt a German Enigma bombe to decode Japanese Purple. Although the settings for each message had to be determined by hand, United States intelligence gained the ability to read Japanese code with greater ease, in a more timely manner, by 1942, six months after the Japanese bombing of Pearl Harbor and the entry of the United States into World War II.
Utilizing their extensive network of listening stations in the Pacific, United States intelligence intercepted and decoded several other types of messages. Diplomatic Purple messages, paired with JN-25 intercepts, another broken Japanese Navy code, gave U.S. military command vital information about Japanese defenses at Midway. Operation Magic intercepts provided useful information during the ensuing Battle of Midway, turning the tide of the war in the Pacific in favor of the allied forces. A year later, Purple intercepts gave the U.S. information about a diplomatic flight on which Japanese General Yamamoto, the mastermind behind the Pearl Harbor attack, was traveling. U.S. planes shot down the Japanese aircraft.
Operation Magic provided critical intelligence information in both the Pacific and European theaters of war. Diplomatic messages between Berlin and Tokyo, encoded with Enigma and Purple, yielded British and United States intelligence information regarding German defenses in France. The information helped commanders plan the DDay invasion of Normandy in June 1944.
The Japanese government remained unaware that the United States broke the Purple code. Japanese Imperial forces continued to use codes broken by Operation Magic throughout the war and in the weeks following the Japanese surrender in 1945.
_
United States OSS
President Franklin Roosevelt was obsessed with intelligence and deeply worried about German sabotage. He turned to William (Wild Bill) Donovan to run a new agency the Office of the Coordinator of Information (COI) which in 1942 became the Office of Strategic Services or OSS. It became Roosevelt’s most trusted source of secrets, and after the war OSS eventually became the CIA. The COI had a staff of 2,300 in June 1942; OSS reached 5,000 personnel by September 1943. In all 35,000 men and women served in the OSS by the time it closed in 1947.
The “Research and Analysis” branch of OSS brought together numerous academics and experts who proved especially useful in providing a highly detailed overview of the strengths and weaknesses of the German war effort. In direct operations it was successful in supporting Operation Torch in French North Africa in 1942, where it identified pro-Allied potential supporters and located landing sites. OSS operations in neutral countries, especially Stockholm, Sweden, provided in-depth information on German advanced technology. The Madrid station set up agent networks in France that supported the Allied invasion of southern France in 1944. Most famous were the operations in Switzerland run by Allen Dulles that provided extensive information on German strength, air defenses, submarine production, and the V-1 and V-2 weapons. It revealed some of the secret German efforts in chemical and biological warfare. Switzerland’s station also supported resistance fighters in France and Italy, and helped with the surrender of German forces in Italy in 1945.
_
Counterespionage:
The MI5 in Britain and the FBI in the U.S. identified all the German spies, and “turned” all but one into double agents so that their reports to Berlin were actually rewritten by counterespionage teams. The FBI had the chief role in American counterespionage and rounded up all the German spies in June 1941. Counterespionage included the use of turned Double Cross agents to misinform Nazi Germany of impact points during the Blitz and internment of Japanese in the US against “Japan’s wartime spy program”. Additional WWII espionage examples include Soviet spying on the US Manhattan project, the German Duquesne Spy Ring convicted in the US, and the Soviet Red Orchestra spying on Nazi Germany.
_
Interceptor and other devices of the disbanded secret service of communist Czechoslovakia were exhibited at the Czech Center in Moscow in 2003. One of the exhibits was Vitez II reel tape recorder as seen in figure below.
Cold War,1947 to 1991
One of the most famous cases of Cold War espionage became known in the early 1950s, when US intelligence uncovered that American communists Julius and Ethel Rosenberg had provided secrets about the United States’ atomic bomb to the Soviet Union during the 1940s. For committing espionage and treason against their country, the Rosenbergs were executed in 1953. All major powers engaged in espionage, using a great variety of spies, double agents, and new technologies such as the tapping of telephone cables. The most famous and active organizations were the American CIA, the Soviet KGB, and the British MI6. The East German Stasi, unlike the others, was primarily concerned with internal security, but its Main Directorate for Reconnaissance operated espionage activities around the world. The CIA secretly subsidized and promoted anti-communist cultural activities and organizations. The CIA was also involved in European politics, especially in Italy. Espionage took place all over the world, but Berlin was the most important battleground for spying activity.
_
The USSR and East Germany proved especially successful in placing spies in Britain and West Germany. Moscow was largely unable to repeat its successes from 1933–45 in the United States. NATO, on the other hand, also had a few successes of importance, of whom Oleg Gordievsky was perhaps the most influential. He was a senior KGB officer who was a double agent on behalf of Britain’s MI6, providing a stream of high-grade intelligence that had an important influence on the thinking of Margaret Thatcher and Ronald Reagan in the 1980s. He was spotted by Aldrich Ames a Soviet agent who worked for the CIA, but he was successfully exfiltrated from Moscow in 1985. Biographer Ben McIntyre argues he was the West’s most valuable human asset, especially for his deep psychological insights into the inner circles of the Kremlin. He convinced Washington and London that the fierceness and bellicosity of the Kremlin was a product of fear, and military weakness, rather than an urge for world conquest. Thatcher and Reagan concluded they could moderate their own anti-Soviet rhetoric, as successfully happened when Mikhail Gorbachev took power, thus ending the Cold War.
_____
Post-Cold War
In the United States, there are seventeen (taking military intelligence into consideration, it’s 22 agencies) federal agencies that form the United States Intelligence Community. The Central Intelligence Agency operates the National Clandestine Service (NCS) to collect human intelligence and perform Covert operations. The National Security Agency collects Signals Intelligence. Originally the CIA spearheaded the US-IC. Following the September 11 attacks the Office of the Director of National Intelligence (ODNI) was created to promulgate information-sharing.
Since the 19th century new approaches have included professional police organizations, the police state and geopolitics. New intelligence methods have emerged, most recently imagery intelligence, signals intelligence, cryptanalysis and spy satellite.
Iraq War 2003
The most dramatic failure of intelligence in this era was the failure to discover of weapons of mass destruction in Iraq in 2003. American and British intelligence agencies agreed on balance that the WMD were being built and would threaten the peace. They launched a full-scale invasion that overthrew the Iraqi government of Saddam Hussein. The result was decades of turmoil and large-scale violence. There were in fact no weapons of mass destruction, but the Iraqi government had pretended they existed so that it could deter the sort of attack that in fact resulted
Israel
In Israel, the Shin Bet unit is the agency for homeland security and counter intelligence. The department for secret and confidential counter terrorist operations is called Kidon. It is part of the national intelligence agency Mossad and can also operate in other capacities. Kidon was described as “an elite group of expert assassins who operate under the Caesarea branch of the espionage organization.” The unit only recruits from “former soldiers from the elite IDF special force units.” There is almost no reliable information available on this ultra-secret organisation.
European Union
In 1993, during the construction of the Justus Lipsius building in Brussels, buggers were installed in the walls. These wiretaps were discovered ten years later. This building is very sensitive, as it is the main place for decision-making between European heads of state.
In 2013, Edward Snowden revealed that the NSA was behind the wiretapping of the Justus Lipsius and a large-scale listening system for European institutions.
______
______
Section-4
Introduction to intelligence:
Intelligence, in government and military operations, is evaluated information concerning the strength, activities, and probable courses of action of foreign countries or nonstate actors that are usually, though not always, enemies or opponents. The term also is used to refer to the collection, analysis, and distribution of such information and to secret intervention in the political or economic affairs of other countries, an activity commonly known as “covert action.” Intelligence is an important component of national power and a fundamental element in decision making regarding national security, defense, and foreign policies. Intelligence in its traditional form is the product of collection, evaluation, analysis, and synthesis of information. Thus, intelligence is produced to assist policy makers and planners to make effective decisions. Intelligence is information that agencies collect, analyze and distribute in response to government leaders’ questions and requirements. The IC strives to provide valuable insight on important issues by gathering raw intelligence, analyzing that data in context, and producing timely and relevant products for customers at all levels of national security-from the war-fighter on the ground to the head of the state.
_
Information versus Intelligence:
Intelligence is a type of information. It is data or facts regarding current, past, or future events or associations. Intelligence collection can be thought of as a part of the follow-up phase of investigation. However, in many cases, intelligence is collected as an ongoing process, not after a specific event. One reason for collecting intelligence is to be proactive, to be able to see problems developing rather than investigating them after they have occurred.
It’s important to note that information does not equal intelligence. Without giving meaning to the data we collect, open-source findings are considered raw data. It is only once this information is looked at from a critical thinking mindset and analyzed that it becomes intelligence. For instance, conducting OSINT is not simply saving someone’s Facebook friends list. It’s about finding meaningful information that is applicable to the intelligence question and being able to provide actionable intelligence in support of an investigation. Another way to look at it is to answer, “why does this data matter” and provide meaningful intelligence about the data collected.
_
Actionable intelligence:
Actionable intelligence is information that is processed and analyzed to provide actionable insights, enabling individuals or organizations to make informed decisions and take specific actions. It goes beyond raw data and provides context and understanding that can be immediately used to improve performance, solve problems, or gain a strategic advantage. Actionable intelligence refers to useful information that can be quickly acted upon within a specific time frame, typically between 12 to 72 hours. This valuable intelligence has the potential to change the course of battles and save lives.
In the domain of computer science, actionable intelligence is sought after by experts who analyze digital media, such as cell phones and computer hard drives, to find information that can be immediately used to prevent planned attacks or enhance operational effectiveness.
_
Why we use secret intelligence:
Although publicly available information can be helpful, usually the best way to find out about the threats posed by an organisation or individual is to obtain secret intelligence about their activities. Individuals planning terrorist attacks, funding terrorism or conducting espionage will rarely advertise what they are doing and will often attempt to hide their activities. Secret intelligence is often the only way to learn more about people and organisations of interest. This could include information about personnel, infrastructure, intentions, plans, and capabilities. If intelligence is valuable, we ensure that it is recorded accurately and that it can be retrieved from our systems swiftly. If we assess that a particular threat warrants more investigation, we deploy resources to obtain further intelligence, continually adjusting our assessments in light of updated intelligence or events.
Principal techniques for gathering intelligence are:
- Covert Human Intelligence Sources (CHIS) or “agents” – agents are people who can provide secret information about the target of an investigation. Agents are not intelligence agency employees;
- Directed surveillance, such as following and/or observing someone;
- Interception of communications, such as monitoring emails or phone calls;
- Communications data (including use of bulk communications data) – information about emails, messages and phone calls, such as “how and when” they were made, which is usually obtained from communications service providers;
- Bulk personal data, datasets – such as the electoral roll or telephone directories- containing information about a large number of people which can be accessed in a targeted way to identify or find information about a subject of interest;
- Intrusive surveillance, such as putting eavesdropping devices in someone’s home or car; and
- Equipment interference, such as covertly accessing computers or other devices.
_
The Different Levels of Intelligence:
Because intelligence can serve different purposes and audiences, it has been classified into three different levels: Strategic, Tactical, and Operational. These levels have a hierarchical nature to them, with strategic intelligence situated at the top and operational intelligence at the bottom.
_
Strategic intelligence is forward thinking, heavily reliant upon estimations and is used to look at long-term trends. As such, it is often produced by analysts with profound subject-matter expertise and high adaptability.
Tactical intelligence provides an evaluation of a rival’s current capabilities, with a focus on their strengths, weaknesses, and intentions. This type of intelligence allows an effective allocation of resources, appropriate planning, and timely engagement with the adversary.
Operational intelligence requires real time, or near real-time information to be produced, for it is used in day-to-day activities and decision making. As such, it is mostly obtained from technical sources and has a short Time To Live (TTL).
Although knowing what level of intelligence is needed will help make it more relevant and actionable for the end user, their hierarchical nature allows them to feed off and impact each other. In fact, a comprehensive analysis will be comprised of intelligence from all levels.
Given that intelligence is used to drive decision-making, and decisions are only as good as the data that supports them, collection thus becomes one of the pillars of intelligence-led activities. As such, it is highly relevant to understand the scope and capabilities of each of the intelligence collection disciplines.
_
Counterintelligence is aimed at protecting and maintaining the secrecy of a country’s intelligence operations. Its purpose is to prevent spies or other agents of a foreign power from penetrating the country’s government, armed services, or intelligence agencies. Counterintelligence also is concerned with protecting advanced technology, deterring terrorism, and combating international narcotics trafficking. Counterintelligence operations sometimes produce positive intelligence, including information about the intelligence-gathering tools and techniques of other countries and about the kinds of intelligence other countries may be seeking. Counterintelligence operations sometimes involve the manipulation of an adversary’s intelligence services through the placement of “moles,” or double agents, in sensitive areas. In authoritarian and totalitarian states, counterintelligence also encompasses the surveillance of key elites and the repression of dissent.
_
Governments often direct their intelligence services to perform covert actions to support diplomatic initiatives or to achieve goals that are unattainable by diplomatic means alone. The U.S. Central Intelligence Agency (CIA), for example, organized the overthrow of the government of Guatemala by military coup in 1954 and helped to undermine the government of President Salvador Allende (1908–73) of Chile prior to the military coup there in 1973. More recently, U.S. covert actions have included providing military and financial support to the mujahideen (from Arabic mujāhidūn, “those who engage in jihad”), who fought Soviet troops in Afghanistan during the 1980s, and aiding U.S. and British military forces in their campaign against Afghanistan’s Taliban government in 2001. Earlier in the 20th century, the intelligence services of the Soviet Union assassinated exiled political figures such as Leon Trotsky (1879–1940) and supported Marxist-Leninist organizations throughout the world.
_____
Types of intelligence:
The types of intelligence a country may require are extremely varied. The country’s armed services need military intelligence, its space and Earth-satellite programs need scientific intelligence, its foreign offices need political and biographical intelligence, and its premier or president needs a combination of these types and many others. Consequently, intelligence has become a vast industry. At the beginning of the 21st century it was estimated that the U.S. government spent some $30 billion annually on intelligence-related activities, employing perhaps 200,000 people in the United States and many thousands more U.S. citizens overseas in both clandestine and overt capacities. The intelligence operations of the Soviet Union were likely of even greater dimensions prior to the dissolution of the country in 1991. All other major countries maintain large intelligence bureaucracies.
Political intelligence is at once the most sought-after and the least reliable of the various types of intelligence. Because no one can predict with absolute certainty the effects of the political forces in a foreign country, analysts are reduced to making forecasts of alternatives based on what is known about political trends and patterns. Concrete data that are helpful in this regard include voting trends, details of party organization and leadership, and information derived from analyses of political documents. A chief source of political intelligence has long been the reports of diplomats, who normally gather data from “open,” or legally accessible, sources in the country where they are stationed. Their work is supplemented by that of the professional intelligence apparatus.
Much military intelligence is gathered by military attachés, who have formal diplomatic status but are known to be mainly concerned with intelligence. Space satellites produce reliable information about the composition of military units and weapons and can track their movements; satellites are especially important for monitoring a country’s production of strategic ballistic missiles and weapons of mass destruction (i.e., biological, chemical, and nuclear weapons). The most valuable kinds of military intelligence concern military organization and equipment, procedures and formations, and the number of units and total personnel.
The state of a country’s economy is crucial to its military strength, its political development, and the conduct of its foreign policy. Consequently, intelligence organizations attach great importance to the collection of economic information, including data on trade, finance, natural resources, industrial capacity, and gross national product.
Because of continuous advances in technology, there has been a constant race between new methods of collecting intelligence and new techniques of protecting secret information. In order to guard against scientific or technological breakthroughs that may give other countries a decisive advantage, intelligence organizations keep abreast of foreign advances in nuclear technology, in the electronic, chemical, and computer sciences, and in many other scientific fields.
In order to make accurate predictions of a foreign country’s future behaviour, intelligence systems obviously require detailed information about the personal characteristics of the country’s leaders. The need for biographical information has expanded with the proliferation of international organizations, whose officers must be briefed about their foreign counterparts. Intelligence agencies also compile data on foreign populations, topographies, climates, and a wide range of ecological factors.
____
Sources of intelligence:
Despite the public image of intelligence operatives as cloak-and-dagger secret agents, the largest amount of intelligence work is an undramatic search of open sources, such as radio broadcasts and publications of all kinds. Much of this work, which also includes sifting reports from diplomats, businessmen, accredited military attachés, and other observers, is performed by university-trained research analysts in quiet offices.
Covert sources of intelligence fall into three major categories: imagery intelligence, which includes aerial and space reconnaissance; signals intelligence, which includes electronic eavesdropping and code breaking; and human intelligence, which involves the secret agent working at the classic spy trade. Broadly speaking, the relative value of these sources is reflected in the order in which they are listed above. A photograph, for example, constitutes hard (i.e., reliable) intelligence, whereas the report of a secret agent may be speculative and difficult to prove.
Intelligence gathering, also known as intelligence collection, is the process of acquiring information about a target, whether it’s a person, organization, or entity, to understand their activities, intentions, and vulnerabilities. This information can be used for various purposes, including risk assessment, security planning, and making informed decisions in areas like security, business, or even resource mobilization.
_______
Intelligence cycle:
The intelligence cycle is a systematic process that intelligence agencies and organizations follow to gather, analyze, and disseminate intelligence information. It consists of several interconnected stages that form a continuous loop, enabling the gathering and utilization of intelligence for decision-making and action. The collection step in the intelligence cycle is a foundational phase where raw data is gathered from various sources to provide a basis for further analysis and intelligence production. It is a critical stage that sets the groundwork for the entire intelligence process. During this phase, intelligence professionals employ various methods and techniques to acquire information relevant to the organization’s intelligence requirements. Once information is collected, it undergoes further processing, analysis, and dissemination to transform raw data into valuable intelligence that informs decision-making and action. The success of the entire intelligence cycle relies on the quality, comprehensiveness, and accuracy of the data collected during this crucial phase. Intelligence is considered to be the product of the collection, processing, and analysis of raw information. As a product, intelligence is developed and made available using the intelligence cycle which, in its most standard model, is made up of 5 steps as seen in figure below:
-1. Planning and Direction (also known as Requirements)
-2. Collection
-3. Processing
-4. Analysis and Production
-5. Dissemination and Integration
________
Applications of Intelligence:
Gathering reliable information allows policymakers to make informed decisions. Intelligence collection also protects national security and mitigates threats. Here are some of the many ways organizations use intelligence.
Threat Assessment:
Intelligence can indicate potential threats, allowing national security and law enforcement organizations to prevent harm before it occurs. While much threat assessment intelligence remains classified, the Office of the Director of National Intelligence (ODNI) releases an annual report that provides an assessment of national security threats. These threats include terrorism, cyberattacks, weapons of mass destruction, and environmental threats.
Criminal Intelligence:
Law enforcement and criminal justice organizations rely on intelligence to battle organized crime and complete criminal investigations. Information gathered from informants, intercepted electronic communication, and other intelligence can prove vital during an investigation. Accurate and timely information can help police apprehend suspects, protect targets, and reduce crime.
Counterintelligence:
Data theft, foreign espionage, and financial crimes are all significant challenges for the intelligence community. Counterintelligence protects sensitive information and assets by identifying and blocking attempts to access information. Gathering tactical intelligence on rivals and their intelligence operations plays an important role in counterintelligence.
Resource Allocation:
Policymakers have limited resources, and intelligence collection provides important information on where to allocate those resources. At the local level, law enforcement uses intelligence collection to decide where to station patrol officers and units. Internationally, intelligence identifies emerging threats that require response strategies.
Disseminating Information:
While several forms of intelligence are highly classified, disseminating information to the public is a key goal of other areas of intelligence collection. For example, journalists and the media collect information to inform the public, while emergency management organizations warn the public about public health and environmental risks.
______
Traditional Forms of Intelligence Gathering:
Within the sphere of information and intelligence gathering, some techniques have remained unchanged. Simply stated, there was no need to fix what was not broken. Techniques and methodologies of this sort have transcended time, space, culture, and borders. The who, what, where, when, how, and whys are all as important today as they were 7000 years ago although the targets and information may have changed as has the reasoning behind the activity in general. Regardless of this, the underlying theme for this type of activity is the need to know, versus the desire to know. At its core, this is rooted in the ability to manage and control the balance of power within a given contextual model. This is a human issue, which can only be addressed by humans. As a result, field craft, or the tools and methodology of the trade, have been developed to guard against the probing activities of unauthorized parties, or perform these activities without being detected. Failure or success is often predicated on two factors being mastered with respect to this space: deception and subversion. Why are these concepts so important to these activities? For many reasons, however, depending on the context in which one finds oneself, they may mean the difference between life and death. Being able to extract or remove oneself and/or team with the target of interest in hand and without incurring notice is key in all intelligence operations, electronic or otherwise. To be caught in the act is a typically unacceptable option in most cases. Equally, valuable to the success or failure of these activities was the ability to remain silent under the most inhospitable of circumstances as well as in hospitable ones.
_______
Intelligence Gathering Methods:
Intelligence professionals utilize a wide range of collection methods to gather information from identified sources.
These methods may include:
Open Source Intelligence (OSINT): Gathering information from publicly accessible sources such as websites, social media platforms, news articles, and online databases.
Human Intelligence (HUMINT): Obtaining information through direct interaction with human sources, including interviews, debriefings, and elicitation techniques.
Signals Intelligence (SIGINT): Intercepting and analyzing electronic signals, communications, and other electronic data to gather intelligence.
Geospatial Intelligence (GEOSINT): Collecting, analyzing, and interpreting geospatial data and imagery to understand physical features and activities on the Earth’s surface.
Measurement and Signature Intelligence (MASINT): Collecting and analyzing unique physical characteristics or attributes to gain intelligence insights.
Cyber Intelligence (CYBINT): Collecting and analyzing information from digital sources and cyber activities. This could include web scraping, data mining, social media monitoring, or manual searching.
Each method has distinct advantages and limitations, so you can carefully select each source to optimize your efforts.
______
Understanding Intelligence Gathering Techniques:
Intelligence gathering techniques encompass methods employed to acquire, analyze, and interpret information crucial for strategic decision-making. This foundational pillar enables military entities to anticipate threats, assess vulnerabilities, and formulate effective countermeasures. Understanding these techniques is paramount in the realm of military intelligence, as it forms the cornerstone of proactive defense strategies and operational planning.
With a blend of human expertise and technology, intelligence gathering techniques span a diverse spectrum, ranging from human intelligence (HUMINT) derived through espionage and interrogation methods to signals intelligence (SIGINT) extracted from intercepted communications. Leveraging imagery intelligence (IMINT) enhances situational awareness through aerial or satellite imagery, complemented by open-source intelligence (OSINT) sourced from publicly available data.
Furthermore, the evolution of cyber intelligence delves into intricacies of hacking, digital espionage, and data mining techniques, enabling comprehensive information extraction in the digital domain. Covert surveillance operations provide real-time insights, while meticulous analysis and interpretation of gathered intelligence facilitate informed decision-making. Upholding legal and ethical standards is imperative, ensuring adherence to privacy laws and codes of conduct within intelligence operations.
In the realm of military operations, the art of gathering vital information, known as Intelligence Gathering Techniques, plays a crucial role in shaping strategic decisions and outcomes. Understanding the intricacies of Human Intelligence (HUMINT), Signals Intelligence (SIGINT), Imagery Intelligence (IMINT), and other facets is indispensable for effective military intelligence operations.
______
______
Human Intelligence (HUMINT):
HUMINT is derived from human sources. The public perception of this discipline is usually related to clandestine activities – think undercover missions and spies. Yet, the reality is that most of the sources used these days are less exciting and much more overt in nature. In fact, most of the raw information used to produce this intelligence is collected through interviews conducted with witnesses, suspects, and Persons of Interest in an investigation, for example. Interestingly, HUMINT is one of the oldest forms of data collection. It remained the primary intelligence source for governments until the technological revolution of the late 20th century. Human Intelligence (HUMINT) is a cornerstone of intelligence gathering in military operations.
_
Role of Spies and Informants:
Spies and informants play pivotal roles in gathering valuable intelligence in military operations. Spies are individuals who clandestinely collect information from targeted entities, often operating under deep cover to avoid detection. These operatives infiltrate enemy organizations to provide critical insights, such as troop movements or strategic plans, enabling decision-makers to make informed choices based on actionable intelligence.
Informants, on the other hand, are individuals who willingly cooperate with intelligence agencies by sharing insider knowledge. They may include defectors, local civilians, or individuals motivated by various factors such as ideology, money, or coercion. Informants offer a unique perspective on internal activities, providing a nuanced understanding of the enemy’s intentions, capabilities, and vulnerabilities.
The collaboration between spies and informants enhances the breadth and depth of gathered intelligence, enabling analysts to construct a comprehensive operational picture. By leveraging human intelligence (HUMINT) gathered from these sources, military planners can anticipate and counter potential threats effectively, gaining a strategic advantage in complex and dynamic environments. The successful integration of spies and informants within intelligence operations is crucial for achieving mission objectives and safeguarding national security interests.
_
Interrogation Methods:
Interrogation methods in intelligence gathering play a vital role in extracting information from individuals who may possess valuable insights. Various techniques are employed during interrogations to elicit reliable and actionable intelligence. These methods are structured approaches designed to uncover critical details without relying solely on brute force or coercion. Effective interrogation methods require a combination of psychological tactics, communication skills, and strategic questioning.
Key elements of interrogation methods include establishing rapport with the subject, creating a conducive environment for dialogue, and actively listening to verbal and nonverbal cues. By utilizing a mix of open-ended questions, follow-up inquiries, and observation techniques, interrogators can gauge the veracity of the information provided and discern potential leads for further investigation. Additionally, the use of cognitive interviewing techniques can aid in memory retrieval and enhance the accuracy of the intelligence gathered.
Interrogation methods encompass both traditional face-to-face interactions and innovative technological tools such as voice stress analysis and computerized algorithms for deception detection. By adapting to the evolving landscape of intelligence gathering, interrogators can refine their techniques to overcome challenges posed by sophisticated adversaries. Continuous training and adherence to ethical standards are essential to ensure that interrogation methods are conducted in a lawful and professional manner, upholding the integrity of intelligence operations.
_
The process of intelligence gathering from people (abbreviated HUMINT) is achieved through interpersonal contacts. NATO defines HUMINT as “a category of intelligence derived from information collected and provided by human sources.” (NATO 2018) Typical HUMINT activities consist of queries and conversations with people who have access to information. The way HUMINT operations are conducted is dictated by both the official protocol and the nature of the information source. Sources may be neutral, friendly or hostile and may or may not be aware of their involvement in intelligence gathering. A well-known technique is the manipulation of human agents to obtain information. The process, known as “the development of controlled sources,” may involve extensive use of psychological manipulation, blackmail, and financial rewards. (Godfrey 1978) Intelligence gathering applying these techniques work in hostile environments. But intelligence, Sherman Kent argued, could be likened to familiar means of seeking the truth. (Kent 1966) Intelligence, unlike any other profession, does not work according to known moral or ethical standards. Some of these standards tend to be, at best, cosmetic. The argument is that anything vital to national survival is acceptable in any situation, even when the method provokes everything that is democratic. Clandestine operations remain unclear in international law and there is very little scientific research to cover the subject.
_
The Scharff Technique: On How to Effectively Elicit Intelligence from Human Sources:
One of the most common forms of HUMINT collection operations conducted during an armed conflict is interrogation. In World War II, each of the parties to this conflict aggressively pursued the intelligence potential that could be derived from a systematic interrogation effort involving the collection of information from captured prisoners-of-war (POWs). In support of the German war effort, the Luftwaffe interrogation camp, Dulag Luft, proved to be an irreplaceable source of intelligence on Allied air operations.
History has documented the exceptional performance of one Dulag Luft interrogator, Hanns Scharff, who artfully elicited detailed, high-value intelligence from Allied aircrews. His accomplishments would be remarkable if only for the exhaustive volume of intelligence he was able to gather. Equally noteworthy, however, were his methods. Rather than compelling his prisoners to reveal classified data through the employment of coercive methods, his success was the result of carefully orchestrated, outwardly friendly exchanges with his prisoners. The overarching philosophical construct that informed this approach was, according to Scharff, both simple and profound: he behaved ‘‘exactly opposite to the way [Army Air Corps airmen] were taught to expect. Instead of torture or degradation, we offered captured airmen the utmost in courtesy and consideration…[w]e took them to cinema shows as we could manage to put on, and invited them to share our tea and coffee when we could get it.’’
His success appears to have bred a degree of confidence in his ability to effectively elicit information from POWs, even those who had been trained to resist interrogation, as were most of the Allied POWs he encountered at Dulag Luft. This was illustrated after the war as he reflected upon his experiences in the challenging art of interrogation and the timeless value of interrogation as a form of intelligence collection:
As long as wars have been waged on this earth, captors have taken the right to question captives. As long as POWs are interrogated, they will talk. No patriotism, no self-control, no logic gives any man enough strength to repel relentlessly pressed attacks utilizing accumulated combinations of facts and circumstantial evidence.
Scharff received no formal training in how to interrogate prisoners. Instead, he carefully observed his fellow interrogators and how they interacted with their prisoners. By imagining himself in the prisoners’ position, he uncovered how they resisted conventional interview techniques. With that knowledge, he then formed his own tactics to counter the prisoners’ strategies.
Scharff’s approach bears strong similarities to the psychological concept of perspective taking: the cognitive capacity to consider the world from another’s viewpoint, which facilitates the anticipation of other people’s behavior and reactions. The ability to take the perspective of others is predictive of success in negotiations, and, due to their inherent similarities, likely to be of importance also for interrogators. Research has notably shown that people typically use themselves as the point of reference when describing and thinking about others, a mode of thinking that can prove counterproductive in the interrogation context.
Scharff used perspective taking to plan for, and profitably respond to, the counter-interrogation strategies adopted by his prisoners.
CONCEPTUALIZING THE SCHARFF TECHNIQUE:
The first conceptualization of the Scharff technique was presented by Pa¨r Anders Granhag during a seminar organized by the Federal Bureau of Investigation’s (FBI) High-Value Detainee Interrogation Group (HIG). This conceptualization draws on a set of five interrelated tactics:
-1. To employ a friendly approach. Create an atmosphere in which the source feels relaxed and comfortable by, for example, displaying acceptance and adopting adaptive interpersonal behaviors.
-2. Do not press for information. Instead of being asked explicit questions, the source is offered opportunities to add information and confirm=disconfirm claims. For this tactic, acknowledging the source’s autonomy and intrinsic motivation is important.
-3. The illusion of knowing-it-all. The interaction begins with the interviewer presenting previously known information to the source, thereby demonstrating a fair amount of reliable knowledge on the topic. The aim is twofold: First, to be perceived even as minimally cooperative the source must provide information beyond what was revealed by the interviewer. Second, the source might assume that the interviewer holds information beyond what was told. In brief, if the source (a) misperceives the amount of information held by the interviewer, and (b) strives to provide only already known information (a common counter-interrogation strategy), the source might reveal information that is in fact new to the interviewer.
-4. The use of confirmations=disconfirmations. Rather than asking direct questions, the interviewer presents claims that the source must confirm or disconfirm. This tactic draws on the assumption that the source will perceive responding to claims as a less active form of complicity as compared to answering explicit questions.
-5. Ignore new information. When provided with previously unknown critical information, the interviewer downplays it as unimportant or already known, hiding the fact that the information provided is of interest.
_
Sources of HUMINT:
Typically, sources of HUMINT generally include:
- Advisors or foreign internal defense personnel working with host nation forces or populations
- Diplomatic reporting by accredited diplomats
- Espionage clandestine reporting, access agents, couriers, cutouts
- Military attachés
- Non-governmental organizations
- Prisoners of war or detainees
- Refugees
- Routine patrolling (military police, patrols, etc.)
- Special reconnaissance
- Traveler debriefing
The first steps for recruiting HUMINT sources is spotting and assessing a target. Surveillance of targets (e.g., military or other establishments, open source or compromised reference documents) sometimes reveals people with potential access to information, but no clear means of approaching them. With this group, a secondary survey is in order. Headquarters may be able to suggest an approach, perhaps through a third party or through resources not known to the field station.
_
HUMINT activities can be divided into several categories as seen in the figure below:
- Overt Information Gathering: Includes open activities by intelligence operatives and law enforcement, such as questioning, observation, and discussions.
- Clandestine Activity: Involves secretive intelligence gathering, mainly through informants.
- Interrogation: The systematic questioning of relevant individuals to obtain crucial information.
- Sourcing: The recruitment and utilization of proxies, assets, and informants to gather intelligence.
_
HUMINT Challenges:
Conducting quality HUMINT is a complex business that throws several obstacles to successful inquiries. These include:
- Language barriers
- Data corroboration (cross-validation)
- Vetting operatives, informants, and other source handlers
- Carrying out constant exposure monitoring (exposure risk mitigation)
- Implementing appropriate counterintelligence measures
- Making sense of large volumes of collected data
- Accurate, logical, and clear data management
- Multiple source integration
- Adoption of new technologies (technical barriers)
- Detecting and filtering our disinformation
_
Solutions: Employing Intelligence Tools:
Human intelligence is usually considered distinct from more technology-driven forms of data gathering such as OSINT, SIGINT, IMINT, etc. But, in fact, HUMINT professionals can benefit hugely by employing advanced digital technologies in their work—the right platform can optimize workflows, mitigate operational threats, reduce routine tasks, and streamline the whole process of data management, fusion, and analysis.
Human intelligence is often crucial in providing information that can’t be gained in any other way. However, to get the most out of the data gathered, enhancement through digital means is absolutely indispensable. While intelligence tools are not necessarily designed specifically for HUMINT purposes, such solutions are still profoundly relevant because HUMINT is still an integral aspect of the intelligence cycle.
Digital platforms allow a range of processes that can elevate human intelligence work in many ways, leading to more effective results. These include:
- Cross-source validation of gathered data
- Using sock puppet accounts for virtual communication
- Automated, ML-powered translation of text, audio, and video
- ML-powered text summarization
- Integration of multiple forms of intelligence (IMINT, GEOINT, SIGINT, etc.) within a single case
- Identity verification through digital footprinting
- Real-time information exchange between team members
- Using data from the Deep and Dark Web as a supplementary source for intelligence enrichment
_
Many HUMINT challenges have a digital solution as depicted in figure below:
_
Top HUMINT Tools, 2024:
Let’s look at best solutions on the market today that can help you streamline and elevate human intelligence processes:
- SL Crimewall
- Palantir Gotham
- Babel
- Recorded Future
- Cellebrite
- Maltego
- i2
- Siren
- Pimeyes
- Spokeo
______
______
Open-Source Intelligence (OSINT):
In today’s information-driven world, knowledge is power. Gathering intelligence has traditionally been the domain of government agencies and large corporations. However, with the rise of the internet and the abundance of publicly available data, a new field of intelligence has emerged: Open Source Intelligence (OSINT). OSINT involves collecting and analyzing information from publicly accessible sources to obtain valuable insights. Obtaining the information doesn’t require clandestine effort; it is retrieved legally and meets copyright requirements. The raw data and information are then collected and analyzed to help understand something more clearly. The OSINT framework supports decision-making, assesses public perceptions, forecasts changes, and more.
OSINT is produced from publicly available information that is acquired through legal means such as official requests, observation, and acquisition. Even though OSINT has gained popularity with the advent of internet and digital media, it can be produced from information found in a wide range of formats and sources including the internet, commercial or public databases, newspapers, radio, television, etc.
While it is an industry term developed to fuel further product segmentation, Social Media Intelligence (SOCMINT) can be considered as a sub-discipline of OSINT. SOCMINT allows the monitoring of social media platforms, such as Facebook and Instagram. This includes the monitoring of content, messages, and other relevant data.
_
Open-source data and information are available in various places and are most accessible online. Examples include:
- Public records databases like BeenVerified, Spokeo, and Intelius.
- Government websites, reports, and documents
- The Internet
- Mass media (e.g., newspapers, TV, radio, magazines, and websites)
- Social networks, social media sites, user account profiles, posts, and tags
- Maps and commercial imagery
- Photos, images, videos
- The dark web, also known as the deep web or DarkNet
_
The Benefits of OSINT:
-1. Cost-effective: OSINT leverages free and publicly available information, making it a cost-effective approach compared to traditional intelligence-gathering methods that often require substantial resources and specialized expertise.
-2. Timeliness: OSINT allows for near real-time information gathering. With the proliferation of social media and online news platforms, OSINT analysts can quickly monitor and analyze unfolding events as they happen.
-3. Broad Perspective: OSINT uses diverse sources to provide a wider perspective on a given subject. It enables analysts to access viewpoints, opinions, and data from various individuals and organizations, leading to a more comprehensive understanding of the topic.
-4. Enhancing Decision-making: OSINT supports evidence-based decision-making by providing timely and relevant information. It enables individuals and organizations to make informed choices, mitigate risks, and identify opportunities based on a comprehensive understanding of the situation.
_
Within the context of cybersecurity, OSINT plays a pivotal role in amassing intelligence about potential vulnerabilities, weaknesses, and the strategies, methods, and procedures employed by adversaries. For example, OSINT played a role in the 23 & Me breach as a large number of users were using the same login credentials from other accounts – which had been leaked in a previous data breach. This led the attackers to gain unauthorized access to the accounts using OSINT.
OSINT’s adaptability is one of its most significant assets. It can be employed to detect immediate threats, support strategic planning, shape security policy development, and facilitate comprehensive risk assessments. For penetration testers, OSINT functions as an essential initial phase or recon phase in emulating attacks on systems, exposing how a malicious actor might collect information to exploit vulnerabilities.
______
______
Signals Intelligence (SIGINT):
Signals Intelligence (SIGINT) is a critical intelligence gathering technique employed in military operations. It involves intercepting and analyzing communication signals to gather information. SIGINT plays a pivotal role in gathering intelligence on enemy activities, such as troop movements, plans, and potential threats. This technique utilizes advanced technology to intercept a wide range of signals, including radio, radar, and digital communications.
In the realm of SIGINT, advanced surveillance technologies are utilized to monitor and intercept communications across various channels. This may include intercepting radio communications, tracking satellite signals, and decrypting encrypted messages. The gathered data is then analyzed to extract valuable intelligence insights. SIGINT operations require highly skilled personnel trained in deciphering complex signals and patterns to extract actionable intelligence.
The information obtained through SIGINT is often classified and used to support strategic decision-making processes within the military. By analyzing intercepted signals, intelligence analysts can provide critical insights into enemy capabilities, intentions, and potential threats. SIGINT remains a cornerstone of modern intelligence gathering, leveraging cutting-edge technology to stay ahead in the ever-evolving landscape of military operations.
SIGINT is comprised of three sub-disciplines:
- Communications Intelligence (COMINT), which targets voice or text messages in their different formats, as well as teleprinter and Morse code traffic. In other words, it intercepts communication transmissions using cryptographic methods and device-to-device transmissions.
- Electronic Intelligence (ELINT), which intercepts and analyzes non-communication transmissions made by radars and other electromagnetic radiation. The instruments used are almost exclusively property of specific governments, making them highly classified and protected sources.
- Foreign Instrumentation Signals Intelligence (FISINT), which can intercept the telemetry of a weapons system or space vehicles. The intelligence produced allows the end user to determine the performance of said systems and vehicles.
ELINT is a form of intelligence that focuses on the interception of noncommunication signals transmitted over electromagnetic waves with the exception being those identified as originating from atomic or nuclear detonations. ELINT saw its birth during World War II in which Allied forces monitored Axis air defense radar systems in order to neutralize them during a bombing raid via direct strikes or electronic countermeasures as seen in figure below.
Over time, this practice has continued in other conflicts, in which the United States has been involved, involving the Union of Soviet Socialist Republics (USSR), and the People’s Republic of China during the Cold War, the Democratic Republic of Vietnam (also known as North Vietnam) during the war in Southeast Asia, and in conflicts the world over involving Libya, Iran, and more current conflicts in the middle east. Although it is easy to mistake ELINT for RADINT (Radar Intelligence), RADINT does not involve the interception of radar signals but rather focuses on flight path intelligence and other data specifics derived from the reflection of enemy radar signals. RADINT by virtue of categorical relation is a subset of MASINT.
______
Imagery Intelligence (IMINT):
Imagery Intelligence (IMINT) plays a vital role in military intelligence by utilizing visual images for analysis and interpretation. This technique involves gathering information from satellite imagery, aerial photography, and other visual sources to assess enemy activities, locations, and capabilities. By scrutinizing these images, analysts can derive valuable insights to support strategic decision-making and operational planning.
IMINT enables military commanders to gain a comprehensive understanding of enemy movements and infrastructure without direct physical presence. It provides a high-resolution view of terrain, facilities, and potential threats, aiding in reconnaissance and target identification. By combining IMINT with other intelligence gathering techniques, such as Signals Intelligence (SIGINT) and Human Intelligence (HUMINT), a more accurate and comprehensive intelligence picture can be constructed for effective mission execution.
Analysts trained in IMINT use advanced tools and technologies to enhance image resolution, conduct feature extraction, and conduct geospatial analysis. They apply sophisticated image processing algorithms to detect patterns, anomalies, and changes within the imagery, facilitating the identification of potential threats or opportunities. The integration of IMINT data with real-time intelligence feeds and historical imagery archives enhances situational awareness and enables timely decision-making in dynamic operational environments.
_____
Geospatial Intelligence (GEOINT):
GEOINT is produced through a combination of imagery intelligence and geospatial information. In other words, it is information acquired through the analysis of images and data associated with a specific location. It can be used, not only for military purposes, but also for non-security use cases that track geographic changes and features (soil erosion, agricultural land usage, etc.).
While the Office of the Director of National Intelligence identifies Imagery Intelligence (IMINT) as a discipline, it is more often considered as a subdiscipline of GEOINT. IMINT can be derived from sources such as visual photography, infrared, radar sensors, lasers, and electro-optics, as well as imagery gathered via satellite. Nowadays, more nations have access to IMINT due to the surge in space-based imagery systems. However, quality is a prevalent issue that can only be addressed with the use of highly sophisticated technology to combat the effects that natural phenomena such as adverse weather and light conditions may have on imagery products.
_____
Measurement and Signature Intelligence (MASINT):
MASINT, which stands for Measurement and Signature Intelligence, is a technical intelligence discipline focused on detecting, tracking, identifying, or characterizing objects or activities by analyzing their unique signatures or distinctive characteristics. These signatures can be derived from various sources, including electromagnetic radiation, nuclear phenomena, acoustics, materials, and even geophysical phenomena. MASINT is crucial for providing insights that might not be available through other intelligence disciplines like SIGINT or IMINT. MASINT is produced by analyzing equipment emanations occurring within the electromagnetic spectrum. MASINT is used to detect information patterns not yet exploited by other systems and is comprised of five sub-disciplines or sources:
- RADINT, or Radar Intelligence
- IRINT, or Infrared Intelligence
- TELINT, or Telemetry Intelligence
- ACOUSTINT, or Acoustic Intelligence
- NUCINT, or Nuclear Intelligence
______
Cyber Intelligence:
Cyber Intelligence plays a critical role in modern military intelligence operations, encompassing various techniques such as hacking, digital espionage, data mining, and analysis. These methods involve the collection and analysis of information from digital sources, including monitoring communication networks and infiltrating secure systems to gather valuable intelligence.
In the realm of Cyber Intelligence, hackers and digital operatives are often employed to breach encrypted data, access sensitive information, and disrupt enemy networks. By utilizing advanced technologies and sophisticated tools, intelligence agencies can gather valuable insights into the activities, plans, and capabilities of adversaries, enabling strategic decision-making and operational success.
Data mining techniques play a crucial role in Cyber Intelligence, allowing analysts to sift through vast amounts of information and identify patterns, trends, and potential threats. Through robust data analysis, intelligence professionals can uncover hidden connections, predict future actions, and provide actionable intelligence to decision-makers, enhancing national security and defense capabilities.
Overall, Cyber Intelligence represents a dynamic and evolving field within military intelligence, where advancements in technology drive innovation and shape the landscape of modern warfare. By leveraging cyber capabilities effectively, intelligence agencies can stay ahead of threats, anticipate risks, and protect critical assets, ensuring a proactive approach to national security in an increasingly digital world.
Cyber espionage and cyber intelligence are related but distinct concepts. Cyber espionage is the act of gathering sensitive information, often for strategic advantage, through cyber means. Cyber intelligence, on the other hand, is the process of gathering, analyzing, and disseminating information about cyber threats to improve an organization’s security posture. In essence, cyber espionage is a specific type of malicious activity, while cyber intelligence is a broader field focused on security and defense.
_____
Covert Surveillance:
Covert Surveillance involves discreetly monitoring individuals, groups, or locations to gather information without their knowledge. It plays a critical role in intelligence operations by providing valuable insights into the activities of potential threats or targets. Covert surveillance methods are designed to be clandestine, ensuring that the subjects are unaware of being observed.
Types of Covert Surveillance Techniques:
-1. Electronic Surveillance: Utilizing devices such as hidden cameras, microphones, and GPS trackers to collect audio and visual data.
-2. Physical Surveillance: Involves trained agents following targets on foot or by vehicle to track their movements and interactions discreetly.
-3. Technical Surveillance: Employing sophisticated technology to intercept communication signals or data transmissions covertly.
-4. Cyber Surveillance: Monitoring digital activities, such as tracking online behavior or hacking into systems to gather intelligence.
Covert Surveillance is subject to legal and ethical constraints to safeguard individual rights and privacy. Intelligence agencies must adhere to strict guidelines and protocols to ensure that surveillance activities are conducted within the bounds of the law. Proper oversight and accountability mechanisms are essential to prevent misuse or abuse of covert surveillance techniques in military intelligence operations.
_______
_______
Knowledge Engineering in Intelligence Gathering:
Intelligence gathering is an essential function for governments, intelligence agencies, and organizations worldwide. It involves the collection, analysis, and dissemination of information critical to decision-making, security, and strategic planning. In this age of information abundance, the field of intelligence gathering has evolved, with knowledge engineering playing a pivotal role in ensuring efficient and effective information management and analysis.
Knowledge engineering was defined by Edward Feigenbaum, and Pamela McCorduck as follows: (Feigenbaum and McCorduck 1984)
“Knowledge engineering is an engineering discipline that involves integrating knowledge into computer systems in order to solve complex problems normally requiring a high level of human expertise.”
Currently, knowledge engineering refers to building, maintaining and developing knowledge-based systems. Knowledge engineering is related to mathematical logic, and heavily involved in cognitive sciences and socio-cognitive engineering where knowledge is produced by socio-cognitive aggregates (especially human) and is structured according to our understanding of how human rationality and logic work.
In knowledge engineering, intelligence gathering consists in finding information from structured and unstructured sources in a way that must represent knowledge in a way that facilitates inference. The result of the extraction goes beyond establishing structured information or transforming it into a relational scheme, requiring either reuse of existing formal knowledge (identifiers or ontologies) or generating a system based on source data. (Sfetcu 2016)
The role of knowledge engineering in intelligence gathering:
- Data Collection and Integration: Knowledge engineering involves designing systems that can gather, integrate, and organize data from various sources, including open-source information, classified documents, social media, and human intelligence. Automated tools and algorithms assist in extracting relevant information from unstructured data, helping intelligence analysts access a comprehensive set of data to work with.
- Knowledge Representation: Intelligence agencies need to structure and represent knowledge in a format that is easily understandable and searchable. Knowledge engineering helps create knowledge graphs and ontologies that organize data, relationships, and entities. This structured information allows analysts to navigate and connect pieces of information effectively, uncovering patterns and trends.
- Pattern Recognition and Analysis: Knowledge engineering supports the development of machine learning and AI algorithms for pattern recognition. These algorithms can sift through vast datasets to detect anomalies, predict future events, and identify potential threats. This is especially crucial in counterterrorism, cybersecurity, and law enforcement operations.
- Decision Support: Intelligence professionals rely on knowledge engineering systems for decision support. These systems provide recommendations, based on historical data and real-time information, to assist analysts and decision-makers in making informed choices.
_____
_____
Issues with intelligence:
-1. Too Much Information:
In this age of digitalization and technology, intelligence agencies across the globe process massive amounts of information about individuals, sub-state actors, and governments every day. Intelligence experts and military leaders often assume that the goal of intelligence work is to gather as much information as possible in order to formulate a more comprehensive picture of the world. The United States, in particular, has become a global epicenter of intelligence work—4.2 million US citizens, more than 10% of the country’s population, have some form of security clearance. However, this aggressive intelligence gathering does not make for better-informed government agencies or higher quality security policy. Instead, excessive information collection leads to information overload on both the individual and institutional levels, impairing the US intelligence community’s ability to do its job. What’s more, US government agencies do not use this information effectively, due to overclassification problems. These inefficiencies in intelligence ultimately propagate instability in the international system and increase the likelihood of conflict between states.
_
-2. Too Much Secrecy:
The US intelligence community does a poor job while sharing information internally, between agencies and between analysts, because vast portions of that information are overclassified. Overclassification occurs either when information is classified but should not be, or when information that is classified should be classified at a lower level. This is by no means a new problem. Almost six decades ago, a Department of Defense report argued that overclassification had “reached serious proportions.” More recently, public figures from John Kerry to Donald Rumsfeld have expressed strong concerns about how many documents are classified in the United States. Excessive classification has persisted because it arises from a fundamentally perverse incentive structure facing decision makers. Officials who decide whether to classify documents and how strictly to limit their circulation face virtually no consequences if they classify a document whose contents did not warrant such a designation. On the other hand, those officials are punished severely for failures to classify sensitive information. This leads decision makers to err on the side of caution, choosing to classify documents at higher levels in uncertain cases. The result is massive overclassification and institutional failure to make information available where and when it is needed.
Overclassification has become an obstacle to intelligence sharing across agencies, potentially leaving analysts in the CIA without easy access to necessary information gathered by the NSA (or other agencies), and therefore, with diminished ability to formulate an accurate picture of the world around us. The lack of transparency that necessarily results from such large-scale classification also decreases accountability, thereby reducing the incentive for analysts to carry out accurate intelligence reporting. Analysts cannot easily be reprimanded or commended for their work unless their superiors can gauge the accuracy of the information they produce and use. Excessive secrecy also precludes open discussion of security policy questions, fueling public ignorance on issues of national security and eliminating the government’s ability to take into account the voice of the people. Essentially, the US intelligence community has limited itself by placing too much emphasis on secrecy and not enough on efficiency.
_
-3. Intelligence failure:
Observers often claim that successful intelligence operations remain secret, while those that go awry become public knowledge. That argument suggests the world hears far more about instances when spies and other operatives get it wrong than when they get it right. That was certainly the case after the terrorist attacks of September 11, 2001, when the IC missed opportunities to pool and analyze information across agencies leading up to the attacks. Intelligence failures also clouded the decision to invade Iraq. In 2005, a government report found the IC was “dead wrong in almost all of its pre-war judgments about Iraq’s weapons of mass destruction.”
That said, headline-making failures sometimes overshadow intelligence wins that have shaped history. For example, a successful code-breaking operation by Allied forces in World War II likely shortened the conflict by several years. According to then U.K. Prime Minister Winston Churchill, this intelligence success ultimately “won the war.”
_
The failures of US intelligence do more than just erode US security. Given that the United States shares intelligence with many of its allies and coordinates with militaries across the globe, especially since 9/11, lapses in judgment and inconsistencies in intelligence on the part of US analysts cause ripple effects throughout the military and intelligence communities across the world. Since 1946, the United States has upheld a signals intelligence sharing agreement—often called “Five Eyes”—with the United Kingdom, Canada, Australia, and New Zealand. Washington also cooperates closely with newer allies in the Middle East and South Asia, including Israel, Saudi Arabia, Yemen, and Pakistan. US intelligence agencies have even reached out to governments that have traditionally not been their greatest partners—nations such as China and, before the Arab Spring, Libya and Syria.
This means that any failures of US intelligence are multiplied and spread across the international community. These shortcomings in US intelligence collection have serious security implications for the world as a whole. States make decisions about entering, exiting, and preparing for war based on their perceptions of the international system, their views of how power is distributed, and their understandings of what capabilities other states have. All of these assessments are shaped by the United States’ and other nations’ abilities to collect accurate, relevant information and distribute that intelligence to allies.
Furthermore, less effective intelligence work heightens the chance of war between states. One classic problem in political science deals with why war occurs: conflict is costly for both winners and losers, which seems to suggest that it is irrational for two states to wage war. One prominent explanation for the existence of war, then, is that states act rationally but make mistakes due to imperfect information. That is, if the world were in fact exactly the way a state perceived it, then that state would be acting rationally. But, because the world differs in some significant way from that state’s view of it, the state makes irrational choices. Specifically, governments make miscalculations surrounding relative military capabilities, strategies, the intentions of allies to provide support, or the resolve of military and civilian leadership to pursue a drawn out conflict. A state’s misunderstanding of one or more of these factors could lead it to overestimate its ability to win wars, leading it to enter more conflicts.
_
Historically, there have been many wars founded on misinformation or incomplete intelligence—conflicts which could have been avoided by better intelligence work. Overclassification prevented US intelligence analysts from making the right connections in the months and days leading up to the terrorist attacks of September 11th, 2001; the 9/11 Commission later blamed those intelligence gaps on “overclassification and excessive compartmentalization of information among agencies.” Moreover, the US war in Iraq from 2003 to 2011 began because of a widely held belief that Iraqi President Saddam Hussein possessed and was perhaps willing to use weapons of mass destruction. This claim proved false, but the war nonetheless claimed more than 50,000 US and Iraqi lives, left more than 100,000 people wounded, and condemned Iraq to years of instability. With better intelligence work, the US intelligence community could have seen this miscalculation before it was too late.
_
Today, faulty intelligence gathering still poses a threat to peace. For example, without accurate information about Iran’s nuclear capabilities and intelligence about the nature and locations of its nuclear plants, a risk-averse Israel could overestimate the need to take drastic, pre-emptive measures against Iran. Israeli Prime Minister Benjamin Netanyahu has already called for international action to stop Iranian development of functional nuclear weapons, calling that prospect… the main [problem] facing not only myself and Israel, but the entire world.” Israel’s decision to strike or not to strike Iran depends in large part on the Israeli government and military’s perceptions about Iran’s strength, capabilities, and intentions. If faulty intelligence leads Israel to believe that Iran is putting the finishing touches on a nuclear arsenal or that Iran intends to use a nuclear weapon against Israel, Israel will likely carry out an airstrike on suspected Iranian nuclear facilities. Such action may be acceptable if Iran is indeed in possession of a nuclear weapon, but if that intelligence turns out to be false, an Israeli strike would destabilize the region without achieving much. Inadequate information therefore continues to have the potential to create unnecessary conflict. The US intelligence community assessed in the 2024 Worldwide Threat Assessment that Iran has not resumed key nuclear weapons-related activities but its nuclear advances are at better position it to develop nuclear weapons if the decision is made to do so. Iran has accumulated enough uranium enriched to 60 percent to build nuclear weapons. According to the IAEA, Iran’s total inventory of enriched uranium as of May 17 was approximately 9,250 kilograms. The IAEA also estimates that over 400 kilograms of the uranium hexafluoride gas have already been enriched to 60 percent—a level considered highly enriched, but not yet weapons grade. This material sits outside of international oversight. It’s enough for about 10 nuclear weapons. Mined uranium naturally is made of less than 1 percent fissile uranium 235. Going from a concentration of less than 1 percent uranium 235 to 60 percent uranium 235 takes much longer than further purifying 60-percent uranium 235 to a 90-percent concentration, the level considered “weapons grade.” Experts estimate that it could take as little as five to six days for Iran to complete this step and enrich enough uranium for one nuclear weapon. Just hours after the International Atomic Energy Agency’s board of governors censured Iran—for the first time in two decades—because of its failure to comply with nuclear commitments, the predictable occurred. On June 12, Israel carried out a series of airstrikes in Iran targeting the country’s nuclear sites. Interestingly Israel is estimated to have 90 nuclear warheads, with fissile material stockpiles for about 200 weapons but neither America nor IAEA mentions it. So, intelligence or intelligence failure is selective to say the least.
_______
_______
Military intelligence:
Intelligence gathering in modern warfare encompasses the collection, analysis, and dissemination of information regarding enemy forces, capabilities, and intentions. This practice serves as a cornerstone of strategic military planning, reducing uncertainties and enhancing operational effectiveness.
Military intelligence is a military discipline that uses information collection and analysis approaches to provide guidance and direction to assist commanders in their decisions. This aim is achieved by providing an assessment of data from a range of sources, directed towards the commanders’ mission requirements or responding to questions as part of operational or campaign planning. To provide an analysis, the commander’s information requirements are first identified, which are then incorporated into intelligence collection, analysis, and dissemination.
Technological advancements have significantly transformed intelligence operations. Drones, satellites, and cyber warfare tools provide real-time data, allowing military leaders to make informed decisions swiftly. The integration of artificial intelligence further enhances analysis, offering insights into complex scenarios that humans alone may not discern. In addition to technological tools, human intelligence remains vital. Special operations forces are often deployed to gather on-ground intelligence, ensuring a clearer understanding of local dynamics. This multi-faceted approach underscores the critical role of intelligence gathering in modern military engagements. Consequently, effective intelligence operations can decisively influence the outcomes of conflicts, often determining the success or failure of military strategies. The historical lessons learned, such as those from the Battle of Gettysburg, continue to resonate in contemporary military doctrines.
Importance of real-time intelligence:
Real-time intelligence refers to the prompt acquisition and dissemination of information crucial for immediate tactical decisions during warfare. The reliance on outdated or incomplete information adversely affected their operational decisions.
Key factors underlining the importance of real-time intelligence include:
- Enhanced situational awareness
- Increased responsiveness to enemy actions
- Improved decision-making capabilities
- Coordination among various military units
_
Throughout its history, the United States has maintained an intelligence capability principally to meet the needs of its military. These needs have been, and are today, wide-ranging and substantial. They include information on the size, capabilities, location, disposition, and plans of foreign military forces, as well as information about foreign countries and events in foreign countries required to plan for and carry out military operations.
A variety of intelligence organizations help to meet these needs. Producing military intelligence analysis is chiefly the responsibility of the Defense Intelligence Agency (DIA), the intelligence elements of the military services and the Unified Commands, and tactical intelligence units organic to the fighting forces. Other intelligence organizations (e.g., the National Security Agency, the Central Imagery Office, and the Central Intelligence Agency) also make significant contributions by providing support to current operations.
Together these organizations provide a broad range of support. They advise defense policymakers on political-military matters, major acquisitions, and force planning. They provide threat projections that guide the military services in how best to “organize, train, and equip” their forces, and warn of potential crises. Finally, they support the employment of the armed forces across a broad continuum of operations, from disaster relief, to peacekeeping, to combat operations. The principal consumers of such information are U.S. combat forces, the military departments, the Secretary of Defense, and the President, but those responsible for foreign policymaking often have need for such information as well.
______
______
Jehadi intelligence:
Intelligence itself is based on information, while information is the arrangement of structures around data. What intelligence can mean to a government is not much different from what it means to Jihādi groups. However, Jihādi intelligence may not necessarily serve a (self-proclaimed) government like the Islamic State or a group exercising certain territorial control, but rather may in fact benefit a much more decentralised and non-territorial cell structure. When Jihādi groups gather intelligence, they usually prefer human sources (HUMINT). Such HUMINT is obtained from information that comes from humans. It is a fairly inexpensive method of gathering information and also the oldest in human history. Jihādi groups also make considerable use of open-source information, as many intelligence requests can be answered using this discipline. In addition to this collection of open-source intelligence, Jihādi groups have conducted clandestine HUMINT activities (i.e. recruitment of assets) as well as Signals Intelligence (SIGINT), Imagery Intelligence (IMINT) via balloons or other affordable devices and vehicles, and especially the Islamic State has used Unmanned Aerial Vehicles (UAVs) for surveillance purposes and offensive attacks much like this would be done by some governmental institutions.
_
Jihādi groups usually set up their own counterintelligence departments and doctrines and train their members in counterintelligence-related skills. Although the modus operandi of groups such as al-Qaida or IS can be compared to state intelligence services, ideological and religious aspects of this phenomenon must also be taken into account. The recruitment of informants by al-Qaida or IS’ establishment of a surveillance state has not only practical, military, strategic or tactical reasons; it also has a religious and ideological level.
Jihādi agents often have to use false documents to disguise their identity and nationality. This common intelligence practise applies to Jihādi groups as well as state agencies. In both cases, individuals involved in intelligence gathering or covert operations may require false or forged passports. The element of safe travel is also significant and important for Jihādi groups and the planning of their operations, while ISIS in particular has managed to use forgeries in the area of propaganda as well.
_
There are different ways in which contemporary terrorists use the Internet, ranging from psychological warfare and propaganda to highly instrumental uses such as fundraising, recruitment, data mining, and coordination of actions. The information technologies of the twenty-first century have exposed new vulnerabilities that can be exploited by jihādi groups. Cyber-attacks, cyber-espionage and cyber-propaganda can be linked to the distorted interpretations of Islam which allows jihādi groups to remain operative and organised on the decentralised battleground of cyberspace despite the loss of leadership figures, controlled territory or manpower.
_______
Counterterrorism intelligence:
Intelligence gathering in counter-terrorism involves the systematic collection and analysis of information to prevent, deter, and respond to terrorist threats. This process is essential for identifying potential threats and understanding the motivations and methods employed by terrorist organizations.
The landscape of counter-terrorism intelligence is complex, necessitating collaboration between various agencies and international partners. Effective intelligence gathering requires not only the identification of threats but also the interpretation of data in a timely manner to inform decision-makers.
Challenges in intelligence gathering include dealing with political constraints and legal limitations that can hinder operations. Additionally, interagency cooperation issues can create barriers to sharing crucial intelligence, ultimately impacting the effectiveness of counter-terrorism efforts.
Understanding the nuances of intelligence gathering in counter-terrorism is vital to adapt to evolving threats. This entails not only technological advancements but also recognizing the importance of human factors and public trust, all of which significantly influence the success of intelligence operations.
Throughout the course of history, many wars have been fought depending heavily on various forms of intelligence. During most recent actions in the War on Terror, intelligence analysis has played a critical role in both offensive and defensive operations in Iraq and Afghanistan.
_
All police departments have the same potential—they rely on daily, personal interaction within their assigned sector of patrol to perform their duties. While the information they “collect” is for the purpose of protecting the populace, enforcing laws and preventing crime, some information can be useful to analysts tracking the potential terrorist threats within our borders. Almost every illegal activity can be given away by indicators. It’s the observation of these indicators and the proper analysis of their significance that could directly lead to the defeat of future terrorist acts. Various stages of terrorist operations can be determined by the smallest of indicators provided during that particular operational maneuver. You won’t necessarily recognize these indicators for what they are, but to an analyst who has studied a particular terrorist group or individual that indicator can speak volumes.
_
The Role of Technology in counter-terrorism intelligence gathering:
Technology significantly enhances intelligence gathering in counter-terrorism by improving data collection, analysis, and communication capabilities. It supports the myriad processes involved in monitoring potential threats, detecting terrorist activities, and coordinating responses among government agencies.
Key technological advancements include:
- Surveillance Systems: High-resolution cameras and drones enable real-time monitoring of suspicious activities.
- Data Analytics Tools: Big data analytics facilitate the identification of patterns and trends from vast amounts of information.
- Cryptography and Cybersecurity Measures: These technologies protect sensitive data from exploitation, ensuring that intelligence remains secure.
While technology mitigates certain challenges in intelligence gathering, it also presents new hurdles. The rapid pace of technological evolution may outstrip the capacity for effective regulation and oversight, potentially leading to misuse or overreach in surveillance practices. Hence, striking a balance between effective intelligence operations and protecting civil liberties remains vital.
_
Bin laden in Abbottabad: intelligence failure or connivance:
Osama bin Laden, the founder and leader of al-Qaeda and the September 11, 2001 mastermind, is believed to have lived in the Abbottabad compound, where he was killed, for at least five years. Participating in a discussion on Piers Morgan Uncensored show, Shehzad Ghias Shaikh said, “The bin Laden papers were not released by Pakistan. They were released by the American intelligence. 470,000 papers clearly state that Osama bin Laden was trying to hide from the Pakistani intelligence,” Shaikh said. Morgan, who stopped Shaikh mid-sentence, said he had made an “utterly ludicrous” statement. “Sorry, with the best will in the world, what you just said is utterly ludicrous. Osama bin Laden was found literally living in a house, a few hundred yards from Pakistan’s main military bases. If your intelligence did not know that he was there, it would be the world’s worst intelligence in the world. That’s why this is a ludicrous statement,” Morgan said. Bin Laden was killed by US Seals in a big, fenced house he had been living in the garrison town of Abbottabad on May 2, 2011. The proximity of the compound to a major military facility led western intelligence agencies to question Pakistan’s claim of not knowing here the man who plotted 9/11 was. After years of intelligence gathering, the CIA traced a trusted courier to a compound in Abbottabad. The compound was heavily secured and unusually large, raising suspicions that a high-value target was residing there.
_
Cyber espionage is a viable tool to combat terrorist groups:
Terrorists use the web for a variety of tasks such as: propaganda, recruitment, training, fundraising, communication and targeting. The main reason terrorists now use the web instead of close net social groups is because they are no longer confined to geographical boundaries. Further, the web is a powerful tool to reach a wider, global, audience. It has been found that “nearly all terrorist groups have a web presence.” As of January 2008, it was found that al-Qaeda had an estimated 5,600 websites and increases at a rate of approximately 900 per year. Al-Qaeda and its affiliates use multiple websites in different languages and targeted to different audiences. By using cyber espionage, intelligence can be gathered stealthily from primary sources by compromising websites that terrorists use to collaborate and train. Using the websites as a staging point, the personal devices of the terrorists can be compromised enabling an in-depth social networking analysis to be conducted. Being able to track a terrorist by GPS 24/7 on their smartphone could provide tremendous intelligence. Using their phone as a bugging device by turning on the microphone could provide even more intelligence. Encrypted communications can be intercepted before encryption ever takes place. The use of cyber espionage can open up many possibilities.
_____
_____
Test your intelligence about intelligence:
Can you tell true or false to these statements about what the NSA does?
Amy Zegart posed this question on a national survey.
What activities does the NSA do?
-1. Break other countries’ secret codes
-2. Intercept foreign telephone and email communications
-3. Analyze information
-4. Build spy satellites
-5. Interrogate detainees
-6. Conduct operations to capture or kill foreign terrorists
Answers: Statements 1 through 3 are true and statements 4 through 6 are false.
In a national poll Zegart conducted with YouGov, Zegart found most Americans couldn’t distinguish between fact and fiction: 78 percent of Americans wrongly believed statement 4 was true, as did 77 percent on statement 5, and 71 percent on statement 6. Various surveys show how little Americans know about what the National Security Agency and other agencies in the intelligence community do.
_____
_____
Intelligence failure or policy failure?
Is intelligence intelligent? How intelligent is intelligence agencies? Well. exactly as smart as we are. Intelligence failure refers to the inability of intelligence agencies to accurately predict or prevent significant events, often leading to strategic surprises or crises. These failures can stem from various factors, including organizational issues, analytical shortcomings, communication breakdowns, and inadequate political leadership. The consequences of intelligence failures can be severe, ranging from political embarrassment to loss of life and national security threats.
_
Michael Rubin of the American Enterprise Institute wrote about the withdrawal from Afghanistan, which he calls an intelligence failure. Not only did the Central Intelligence Agency and other U.S. intelligence agencies wildly underestimate the speed of the Taliban advance, they appeared to have been blind to the political dealings of the Taliban and the military prepositioning the Taliban had achieved. Afghanistan was an intelligence failure. There’s an old saying in intelligence business that there are never policy failures, there are only intelligence failures. But Afghanistan was really was a colossal policy failure. And in fact, if you take a closer look at different intelligence agencies and what they said, the CIA was always more pessimistic about the ability of the government in Afghanistan to sustain itself than the military was. The reason that withdrawal was so devastatingly unsuccessful had less to do with intelligence agencies, and much more to do with the Biden Administration’s policies.
_
Meeting in the White House in 2002, CIA director George Tenet tells President Bush, the evidence that Iraq possesses weapons of mass destruction amounts to a slam dunk case. And of course, America invades the next year, and WMDs aren’t there. After the war, the Robb-Silberman Commission investigates what happened. They investigate the intelligence, particularly. And the central finding, which judge Larry Silberman discussed is this, Saddam Hussein had persuaded everyone in Iraq, his generals, his family, that he did have weapons of mass destruction. And if everybody believed something that’s untrue, whether it’s untrue or not, it’s very, very hard for intelligence to pick that up.
_
Good intelligence really requires two things. You have to collect the right information and then you have to assess what it means. And information is often ambiguous, so you have to have both things. And in the case of Iraq and WMD, we really didn’t have people on the ground after weapons inspectors were kicked out of the country. And so our information coming out of Iraq was really frozen in time. And so what that then led to was a series of analytic errors. In the absence of new intelligence, our intelligence agencies assumed Saddam was doing what he had done before. When in fact he wasn’t. And so that commission and other commissions that investigated the WMD failure really found a number of different analytic problems. Group think being one of them. Nobody really took dissenting views seriously, for example. There were dissenting views, but they were buried in that national intelligence estimate. Well, we also know that there was sort of mirror imaging. We imagine that Saddam would behave, as we would behave, in that situation. And that turned out not to be true, too. So as political scientists like to say, the failure in Iraq was overdetermined. There were so many variables that went wrong. Lots of factors that went into this mistake. But it was clearly an intelligence failure.
_
Here’s another case study and that’s the search for Osama bin Laden. Very briefly the hunt for bin Laden took a decade. And for most of those years intelligence officers told us that bin Laden was most likely in very difficult, mountainous terrain in Afghanistan. And when we found him, nothing of the sort. He was living in a comfortable compound, less than a mile from the Pakistani military academy. He wasn’t in the mountains. He was in a perfectly inhabited part of Pakistan. How do we assess this? On the one hand, we found him, and we got him. On the other hand, it took a decade. And who knows how many tens of millions of dollars to find a man who was, well, not exactly hiding in plain sight, but he certainly wasn’t up in the inaccessible mountains. Osama bin Laden’s location was discovered through a combination of intelligence gathering and tracking a key courier. After years of investigation, U.S. intelligence agencies identified a courier known as Abu Ahmed al-Kuwaiti, who was a close associate of Khalid Sheikh Mohammed. By tracking al-Kuwaiti, they eventually traced him to a compound in Abbottabad, Pakistan, in 2010. Further analysis of satellite imagery and intelligence reports led them to conclude that the compound was likely a hiding place for someone of significance, and they surmised that it was bin Laden’s residence.
_
The history of espionage is a lesson in paradox: the better your intelligence, the dumber your conduct; the more you know, the less you anticipate. During the First World War, the British decrypting center known as Room 40 had useful information about the movement of German ships during the Battle of Jutland, off the coast of Denmark, but the officers of the British fleet, disliking the cut of the analyst’s intellectual jib, contemptuously ignored what they were told, and managed only to draw a battle they could have won. Richard Sorge, a Russian spy in Germany’s Embassy in Japan, gained detailed knowledge about the approaching German invasion of Russia in 1941, and passed it on. Stalin not only ignored information about the coming invasion but threatened anyone who took it seriously, since he knew that his ally Hitler wouldn’t betray him. The delayed reaction cost hundreds of thousands of lives, perhaps millions, and very nearly handed Hitler victory. The invasion was launched, and Stalin soon retreated to his dacha in shock. When a delegation of apparatchiks came to see him, he took it for granted that they were coming to depose him, since that’s what he would have done in their place, and was startled when they begged him to step forward and lead, being themselves dependent on the cult of the great leader.
_
The rule that having more intelligence doesn’t lead to smarter decisions persists, it seems, for two basic reasons. First, if you have any secret information at all, you often have too much to know what matters. Second, having found a way to collect intelligence yourself, you become convinced that the other side must be doing the same to you, and is therefore feeding you fake information in order to guide you to the wrong decisions. The universal law of unintended consequences rules with a special ferocity in espionage and covert action, because pervasive secrecy rules out the small, mid-course corrections that are possible in normal social pursuits. When you have to prevent people from finding out what you’re doing and telling you if you’re doing it well, you don’t find out that you didn’t do it well until you realize just how badly you did it. (The simple term of art for this effect, “blowback,” originated within the C.I.A.) Good and bad intelligence circle round and round, until both go down the drain of sense.
______
______
Section-5
Introduction to cyber espionage:
According to Burton (2015), cyber threats can be classified into four main categories: Cybercrime, cyber espionage, cyberterrorism, and cyber warfare.
Cybercrime is crime enabled by or that targets computers. Criminal activities can be carried out by individuals or groups who have diverse goals such as financial gain, identity theft, and damaging property. Usually, cybercrime is financially motivated.
Cyber espionage activities are conducted by state-sponsored cyber attackers “for the purpose of providing knowledge to the states to obtain political, commercial, and military gain” (Burton, 2015).
According to Denning, cyberterrorism is “the convergence of cyberspace and terrorism” that covers politically motivated hacking and operations intended to cause grave harm such as loss of life or severe economic damage.
Cyber Warfare involves the use of computers and systems to target an enemy’s information systems. The use of cyber power in military operations is an important force multiplier. Since the armed forces are highly dependent on information technologies and computer networks, disruption of these systems would provide great advantages. Cyberspace is regarded as the fifth domain of warfare after land, sea, air, and space.
_
Cyber Espionage is the act of using digital tools and techniques to unlawfully obtain sensitive, classified, or proprietary information from an individual, organization, or government. The information targeted typically holds strategic, economic, or political value, and its unauthorized access can lead to significant damage to the entity from which it was stolen.
While the term ‘espionage’ has been traditionally associated with spy activities in the physical world, the advent of the internet and digital technologies has given rise to a new form of espionage that operates in the cyber realm. Cyber Espionage can be conducted remotely, often without the knowledge of the victim, making it a particularly insidious form of information theft. Cyber espionage is difficult to detect, the perpetrators can hardly be successfully prosecuted, as the purported country of origin does of course not help to elucidate the affair and determination by the means of intelligence of the origins of the cyber-attack (attribution) can simply be denied based on the lack of provability.
With an estimated 50 billion devices that may collect data on their users by 2030, 127 new devices per second being connected to the internet, and 4.66 billion people using the internet as of 2021, technology use is growing at a monstrous rate-and so is the ability to spy on people using these devices. Devices can track what you do on them, from what you watched on YouTube a few minutes ago down to the second you searched for a photo a week ago. As a result, there is a common saying: once something is on the internet, it can never be erased.
_
Cyber espionage, cyber spying, or cyber-collection is the act or practice of obtaining secrets and information without the permission and knowledge of the holder of the information using methods on the Internet, networks or individual computers through the use of proxy servers, cracking techniques and malicious software including Trojan horses and spyware. Cyber espionage can be used to target various actors – individuals, competitors, rivals, groups, governments, and others – in order to obtain personal, economic, political or military advantages. It may wholly be perpetrated online from computer desks of professionals on bases in faraway countries or may involve infiltration at home by computer trained conventional spies and moles or in other cases may be the criminal handiwork of amateur malicious hackers and software programmers. Cyber spying started as far back as 1996, when widespread deployment of Internet connectivity to government and corporate systems gained momentum. Since that time, there have been numerous cases of such activities.
_
Major Historical Events:
Cyber espionage has significantly shaped national security dynamics, with key historical events underscoring its profound implications. For instance, the 2007 cyber-attack on Estonia exemplifies how coordinated cyber operations can disrupt critical infrastructure, signaling a new era in state-sponsored aggression.
Another notable incident is the 2010 Stuxnet worm attack, which targeted Iran’s nuclear enrichment facilities. This sophisticated cyber operation marked a pivotal moment, revealing the potential of cyber espionage to influence geopolitical outcomes without conventional warfare.
The Edward Snowden revelations in 2013 brought to light extensive surveillance programs conducted by the National Security Agency (NSA). These disclosures ignited global debates about privacy, state power, and the boundaries of cyber espionage, emphasizing its impact on international relations.
The 2020 SolarWinds attack illustrated the evolving nature of cyber threats. This event, attributed to Russian operatives, infiltrated government and corporate networks, highlighting vulnerabilities in national security and prompting nations to reevaluate their defense strategies against cyber espionage.
_
Difference between Cyber Espionage and Cyber Warfare:
Cyber espionage and cyber warfare are terms often used interchangeably, but they refer to distinct activities in the realm of digital conflict.
-1. Cyber Espionage: Cyber espionage is primarily focused on intelligence gathering. It involves infiltrating the computer systems of other nations to access sensitive information, steal technological secrets, or gather intelligence for political or military advantages. The goal is to remain covert and gather information without causing significant damage.
-2. Cyber Warfare: Cyber warfare, on the other hand, goes beyond intelligence gathering and involves the use of cyber attacks to cause harm or disruption. This can include disrupting critical infrastructure, disabling military systems, or even causing economic damage. Unlike espionage, cyber warfare is more overt and aims to achieve strategic objectives through the use of force in the digital realm. It can take numerous forms, yet all of them comprise the destruction of critical systems as the ultimate goal is to incapacitate the target country by compromising its core systems.
The distinction between cyber espionage and more aggressive cyber operations is critical under international law. Espionage has been considered unregulated under the international legal system – meaning cyber activities that constitute espionage are neither lawful nor unlawful under international law. As a result, States freely engage in espionage and generally accept it from other States, with results limited to punishing spies under domestic law and the expulsion of diplomats. This is in stark contrast to the treatment of aggressive activity, which might constitute an illegal use of force under the U.N. Charter.
Occupying the space between cyber espionage and cyber aggression is Operational Preparation of the Environment (OPE). The Department of Defense defines OPE as “the conduct of activities in likely or potential areas of operations to prepare and shape the operational environment.” OPE could include cyber operations to penetrate systems, introduce malware or undertake other actions in preparation for offensive action. These activities occur in the absence of armed conflict, although conflict may be anticipated.
Pre-positioning cyber capabilities on networks or computer systems, by itself, does not constitute cyber aggression, and is not quite espionage, because it is not collecting intelligence. This activity is rather some unique category falling between espionage and attack. Although capabilities are prepositioned in the kinetic world as well, the legal issues are easier to deal with in the physical world. For example, there is little doubt that concealing a weapons cache in another State’s territory is preparation for armed attack. On the other hand, obtaining access to a system often fails to signal what kind of follow-on action is anticipated. This ambiguity is one thing that makes cyber operations uniquely challenging.
Similarly, many pre-positioned capabilities provide the ability to engage in either espionage or aggressive activity, and so acting to emplace these capabilities may be mistaken for either of the other two. For example, malware that allows its controller to log on a system with administrator privileges would provide the opportunity to view or copy information on a network, as well as delete information and take other actions that could physically damage the system, i.e., constitute an attack. Obtaining and maintaining this kind of prepositioned capability could be seen as the equivalent of planting explosives to be used at a future point.
_______
Types of Cyber Espionage:
There are different types of cyber espionage. State-sponsored cyber espionage, corporate cyber espionage, political cyber espionage, economic cyber espionage, military cyber espionage, and cyber espionage by non-state actors are some of the well-defined cyber espionage types. These types of cyber spying are going to be explained in the following paragraphs.
-1. Nation-state cyber espionage:
Governments engaging in cyber espionage have sophisticated capabilities and vast resources at their disposal. These nation-state actors can be motivated by a variety of reasons, including national security, economic competition, or geopolitical influence. Countries may target each other to gain insights into military strategies, technological advancements, or political decision-making processes. Nation-states engage in cyber espionage primarily as a means to gather intelligence, monitor threats, and bolster national security. These entities leverage advanced technological capabilities to infiltrate foreign networks, obtaining sensitive data that can influence political or military strategies.
Prominent nation-states involved in cyber espionage include the United States, China, Russia, and North Korea. Each of these countries employs sophisticated tactics, ranging from phishing attacks to advanced persistent threats (APTs), to achieve their espionage objectives. Their motivations vary, including the pursuit of economic advantage, political leverage, and military supremacy.
States can hire hackers directly by using their armed forces and other government agencies. They could potentially raise money in another way. This makes it simpler to refute the state’s involvement if the attack is discovered. This may lessen the diplomatic effects that these strikes may have. Moreover, it obfuscates the distinction between government and criminal organizations. The state-sponsored organizations then focus on their funders’ enemies for a variety of reasons. State-sponsored cyber attacks may, for instance, involve espionage, the dissemination of false information, testing the fitness or capabilities of adversaries, or, more recently, the collection of information in preparation for an attack on important infrastructure and businesses.
It can be summed up as finding corporate secrets, technologies, and secret political information; harming the defender and significantly reducing their defensive capabilities; upsetting political opinion within a state; influencing elections; sowing resentment against governments or people; or boosting public opinion of particular parties. However, sometimes the main objective is to acquire data, assess the attacker’s potential, and assess the readiness of the opposition. State-sponsored attacks are difficult to identify since they are heavily funded, outfitted, and trained. It can be exceedingly challenging to prove that a state was behind a cyberattack. Because of this, states now have an efficient and largely risk-free option for conducting cyber spying.
-2. Economic Cyber Espionage:
Industrial or corporate espionage typically takes place between firms, whereas economic espionage is conducted by governments and has a global scale. Economic espionage is the theft of a trade secret or proprietary information, or the appropriation, taking, carrying away, or concealment of a trade secret or private information, or the obtaining of a trade secret or private information through fraud, artifice, or deception without the owner’s consent. Other examples include copying, duplicating, downloading, uploading, destroying, transmitting, delivering, sending, communicating, or conveying trade secret or proprietary information. Economic espionage is frequently used by foreign governments, particularly in nations where many enterprises are state-owned and where there is a significant emphasis on economic development. Other governments consequently became involved in it as well. There are two types of economic and industrial espionage. One is the purchase of intellectual property, which includes things like production methods, plant locations, confidential or operational knowledge about customers, pricing, sales, R&D, and policies, as well as potential bids, plans, and marketing strategies. The second is the theft of trade secrets, as well as corruption, extortion, or technological spying using spyware of various kinds.
-3. Industrial/corporate cyber espionage:
The unlawful and unethical theft of firm trade secrets for use by a rival to gain a competitive edge is called industrial espionage. This is a clandestine procedure frequently carried out by an insider or an employee hired with the specific intent of spying on and stealing sensitive information for a rival. With the aid of the internet and insufficient cybersecurity procedures, industrial espionage has increased. Innovations and cutting-edge technologies in computer hardware and software, biotechnology, aerospace, telecommunications, any type of machine and automobile technologies, and energy and material science are the main targets of industrial espionage.
The most typical method of industrial espionage actively looks to learn information about a business or organization. Intellectual property, such as manufacturing procedures, chemical formulas, recipes, skills, or ideas, is stolen. The concealment or restriction of access to vital information about pricing, bidding, planning, research, and other topics constitutes industrial espionage. Such a strategy aims to give the party with the information a competitive benefit.
-4. Political Cyber Espionage:
Political cyberespionage aims to improve national security by obtaining private political and military data that is held by other state and non-state players in the international system. Actors who engage in political cyber-espionage target political groups or people to learn more about political activities or to sabotage political processes. The upkeep of global peace and security is threatened by political cyberespionage.
-5. Military Cyber Espionage:
Governments and armed forces throughout the world are becoming more concerned about national security due to the rising significance of cyberspace in contemporary society and its growing usage as a forum for conflict.
In military cyber espionage, actors who want to obtain private information about military secrets and/or technology or obstruct military activities target military organizations. Military cyber espionage can also be the reason or a result of cyber espionage in support of geopolitical interests.
-6. Cyber Espionage by Non-State Actors:
Cyberspace has unique qualities that make it appealing to nation-states and non-state actors in cyber conflict, including its asymmetrical nature, lack of attribution, low barrier to entry, and role as an effective medium for protest, crime, espionage, and military aggression.
Non-state actors in cyber espionage refer to entities that operate independently of government control but still engage in espionage activities, impacting national security. These actors can range from organized criminal groups to politically motivated hacktivists and private corporations.
Organized crime syndicates have increasingly leveraged cyber espionage to achieve financial gain, often targeting sensitive information from corporations and government entities. Their activities can undermine national security by compromising critical infrastructure and national data.
Hacktivist groups, such as Anonymous, utilize cyber espionage to promote social and political agendas. Their operations often aim to expose perceived injustices or government misconduct, drawing attention to their causes while threatening the security of sensitive information.
Additionally, private corporations sometimes engage in corporate espionage, where they infiltrate competitors’ networks to gain access to trade secrets. This form of cyber espionage not only harms individual businesses but can also destabilize entire industries, ultimately posing risks to national security.
The actions of nation-states and various non-state actors coexist in cyberspace. Numerous countries are presently working to develop their cyberwarfare capabilities, frequently using criminal gangs and irregular armies. It has also been demonstrated that using non-state actors in state-on-state cyberspace operations, such as hacker groups, nationalist hackers, and cyber militia can be a useful strategy for launching cyber attacks. The hacker groups are capable of launching several attacks against private companies, vital infrastructure, and governmental institutions. The majority of the attacks were intended to undermine state propaganda, including the hacking of radio stations, and to infiltrate private companies to expose sensitive data and disrupt their operations.
________
General process of cyber espionage:
Cyber espionage process is executed in most cases to fulfill the goals of the attackers, where the typical attack vector and main tool used for espionage is malware, but also social engineering techniques may be the starting point of a cyber espionage attack. Figure below shows an approach that encompasses the most common phases of the process used to carry out cyber espionage.
Reconnaissance:
In the first phase of this process, the attacker conducts a thorough investigation of the target to gather useful information for later use in espionage. This information can include email addresses, IP addresses, employee names, in general, any information that can help to deploy the attack. Due to the nature of this information, social engineering and more sophisticated techniques can be used to detect the technical vulnerabilities of the target. This phase requires effort and individuals with computer security skills, even though some activities to perform reconnaissance are automated.
Preparation:
Depending on the objective, it can have two attack vectors based on different techniques. First, social engineering, its success relies on the preparation of the attack which requires a considerable amount of resources, time, knowledge of human psychology, language, culture, among others. Second, computer exploitation, the success of it, depends on the sophistication of the malware used and the technical knowledge of the attackers to exploit possible vulnerabilities previously detected over the targeted computer systems.
Attack:
Once the attacker has analyzed vulnerabilities of target, selected the attack vector and the techniques with the highest success factor, the attack is carried out. Next, the attacker will attempt to obtain access credentials to the target’s systems. Whether through malware, backdoor or APT, the attacker could wait for some time to continue with the next phase or start with this one immediately, the latter can occur when the attacker believes he can be discovered. Once the attack has succeeded, internal reconnaissance is performed to escalate privileges. Most commonly, the intruder will try to get users and passwords that allow access to more resources by cracking common password hashes or performing brute force attacks. During the infiltration, the intruder tries to collect information from the systems, similar to footprinting but performed locally, to learn about the victim’s environment. There are even several tools typically used in ethical hacking that can facilitate this task (e.g., nmap, dnsenum, dimitry).
This phase is quite delicate; a mistake could cause the intruder to be detected. As the final part of this step, once the attackers have the necessary permissions they could install keyloggers or other specific malware that suits the attacker’s needs, such as installing new backdoors on multiple systems, creating a VPN connection using legitimate credentials, authenticating on web portals. All these, in order to maintain their presence inside the systems silently.
Information gathering:
Once the attacker knows the environment he is spying on, he must know what type of information he is looking for, such as images, text documents, email files, databases. It is important to know the language of the victim to facilitate the identification of files and directories of the systems. A specific type of malware to help in this task are advanced keyloggers. They have functionalities that allow capturing the activities executed by the user, such as VoIP conversations, screen captures, typing any character, among others.
Maintenance:
If the espionage will be conducted over a long period, the attackers have to adapt to the changing environment. If one or more implemented backdoors are detected or compromised, attackers will identify and analyze the cause to prevent this from occurring with other backdoors distributed in the systems. Once they implement the appropriate measures such as creating new attacks to maintain their permanence in the attacked systems, they will check if they can perform more attacks or adapt their current infiltration to continue with the gathering information. Therefore, this is a continuous phase meanwhile the espionage lasts.
Information leakage:
This phase occurs simultaneously with the previous one, or it takes place after collecting all the information needed. The attacker usually compresses the information using formats such as RAR or 7z, protects them with a password or applies encryption algorithms. To extract information, the attacker could transmit using proxy networks, such as the Tor network (also known as deep web), to hide his identity. In other cases, information is transmitted using the backdoors implemented in previous phases or even uploading information on servers that are compromised for later download.
Information sale:
Espionage is also offered as Espionage-as-a-Service (EaaS). In this case, customers of the stolen information or technologies often try to manage their own R&D costs through this type of technology transfer, since the acquisition cost will be lower than their own R&D. Consequently, attackers use the stolen information as a bargaining chip with the interested party, to encourage future purchases and thus take advantage of the espionage processes they have in place.
_______
Methods Employed in Cyber Espionage:
-1. Hacking: Hackers often exploit vulnerabilities in software, hardware, or network configurations to infiltrate a target’s systems. This can include techniques such as exploiting zero-day vulnerabilities or conducting spear-phishing campaigns to trick users into revealing their login credentials.
-2. Malware: The use of malicious software, such as spyware, Trojans, and keyloggers, is a common method in cyber espionage. These tools can infect a target’s devices or network and silently record data, including keystrokes, communications, and files.
-3. Advanced Persistent Threats (APTs): APTs are long-term, highly sophisticated cyberattacks orchestrated by well-funded and organized actors, often state-sponsored. These attacks involve multiple stages, including initial compromise, data exfiltration, and maintaining persistent access to a victim’s network.
-4. Social Engineering: Cyber espionage actors may manipulate individuals within the target organization through techniques like phishing emails, pretexting, or baiting, exploiting human psychology to gain access to sensitive information.
-5. Zero-Day Exploits: These are vulnerabilities in software or hardware that are unknown to the vendor or have not yet been patched. Cyber spies may leverage zero-day exploits to gain a foothold in a target’s systems.
______
Cyber Espionage Targets:
Cyber threat is a potential malicious act that can harm computer systems, networks, or data, often involving unauthorized access, disruption, or data breaches.
_
Large enterprises, government agencies, academic institutions, think tanks, and other organizations that have significant intellectual property and technical data that can give another organization or government a competitive edge are the most frequent targets of cyber espionage. Targeted campaigns can be launched against specific people, including well-known politicians, high-ranking government officials, business leaders, and even celebrities. Cyber spies carefully choose their targets, focusing on organizations and sectors with valuable data. Key targets include:
- Large corporations: These are prime targets due to their wealth of intellectual property, financial information, strategic plans, and research & development data. Competitors or foreign governments may seek this information to gain a competitive edge or disrupt business operations.
- Government agencies: Due to their pivotal role in national security and policy-making, government agencies possess sensitive information that can be valuable for other nations. Such data includes military secrets, diplomatic communications, and internal strategies.
- Academic institutions: Universities conducting cutting-edge research are attractive for cyber spies looking to acquire new scientific knowledge or technological innovations without investing in costly R&D.
- Think tanks: These organizations influence public policy through research and advocacy. In turn, accessing their insights on geopolitical trends or defense strategies can be beneficial for adversaries aiming to shape favorable global narratives.
- High-ranking government officials: Individuals in positions of power within governments hold confidential knowledge about state affairs, making them attractive targets for those seeking insight into governmental decisions that inform future moves.
- Business executives: Corporate leaders possess comprehensive knowledge of their company’s most guarded secrets, from product blueprints and marketing strategies to plans for mergers and acquisitions. Accessing the communications of these executives could yield competitive intelligence that might provide a significant edge in the marketplace.
- Celebrities: At first glance, public figures and entertainers might not seem like typical targets for cyber espionage. However, personal scandals or sensitive information obtained by invading their privacy can be used to manipulate media coverage or potentially harm reputations.
Each of these targets offers a unique value proposition to attackers. Whether it’s about stealing groundbreaking technology, influencing political outcomes, or understanding market dynamics, the underlying motive remains consistent: gaining an advantage through means otherwise unattainable.
Threat actors using cyber espionage frequently target internal corporate information. This refers to private, sensitive information that a company keeps for its own internal use. Data for operations and research and development are just two examples. Cyber espionage is used to target information about secret projects, trade secrets, corporate plans, and other private information pertaining to ongoing initiatives and emerging goods. That simply means whatever information the attacker might be able to offer or sell for a profit. In these sectors, the impact of a successful cyber espionage attack can result in massive financial losses and long-term damage to reputation and operations.
_
Targeted Technologies:
Although many aspects of economic activity and technology are of potential interest to foreign intelligence collectors, the highest interest is in the following areas:
|
Industry |
Priority Sectors / Technologies |
|
|
Energy / Alternative Energy |
• Advanced pressurized water reactor and high-temperature, gas-cooled nuclear power stations • Biofuels • Energy-efficient industries |
• Oil, gas, and coalbed methane development, including fracking • Smart grids • Solar energy technology • Wind turbines |
|
Biotechnology |
• Advanced medical devices • Biomanufacturing and chemical manufacturing • Biomaterials |
• Biopharmaceuticals • Genetically modified organisms • Infectious disease treatment • New vaccines and drugs |
|
Defense Technology |
• Aerospace & Aeronautic Systems • Armaments |
• Marine Systems • Radar • Optics |
|
Environmental Protection |
• Batteries • Energy-efficient appliances • Green building materials |
• Hybrid and electric cars • Waste management • Water/air pollution control |
|
High-End Manufacturing |
• 3D printing • Advanced robotics • Aircraft engines • Aviation maintenance and service sectors • Civilian aircraft • Electric motors • Foundational manufacturing equipment |
• High-end computer numerically controlled machines • High-performance composite materials • High-performance sealing materials • Integrated circuit manufacturing equipment and assembly technology • Space infrastructure and exploration technology • Synthetic rubber |
|
Information and Communications Technology |
• Artificial intelligence • Big data analysis • Core electronics industries • E-commerce services • Foundational software products • High-end computer chips • Internet of Things |
• Network equipment • Next-generation broadband wireless communications networks • Quantum computing and communications • Rare-earth materials |
_____
Usual Motives for Cyber Espionage Campaigns:
-1. Economic Gain: The aim to obtain a competitive advantage in the market by stealing trade secrets, intellectual property, or other confidential information from competitors is the driving force behind many cyber espionage operations.
-2. Political Advantage: Cyber espionage is a tactic used by governments to monitor the actions of their enemies, gather critical political intelligence, and sway foreign policy decisions.
-3. Military Intelligence: In order to obtain an advantage in potential conflicts or negotiations, cyber espionage is widely employed to obtain sensitive military information, including defence tactics, weapon capabilities, and troop movements.
-4. Strategic Advantage: Cyber espionage is carried out by nation-states and other organisations to further their strategic objectives, which include finding weaknesses in vital infrastructure or interfering with the activities of adversarial states.
-5. Espionage for Hire: Certain individuals or groups engage in cyber espionage by offering their services to interested parties, such as governments, corporations, or criminal organisations, in exchange for cash payments or other benefits.
_
Key Motivations and Objectives behind Cyber Espionage are depicted in table below:
|
Motive |
Objective |
Examples |
|
Financial Gain |
Steal intellectual property or trade secrets to gain a competitive economic advantage. |
A company steals a competitor’s technology to save on research and development costs. |
|
Political & Strategic Intelligence |
Gather intelligence on foreign governments, including military strategies and diplomatic plans. |
A government monitors diplomatic communications to gain leverage in international negotiations. |
|
Military Superiority |
Uncover details about adversaries’ weapons, defense systems, and troop movements. |
Cyber spies gather information on an enemy nation’s defense systems for strategic planning. |
|
Sabotage |
Disrupt critical infrastructure such as power grids or communication networks, causing chaos. |
A cyberattack on a country’s energy infrastructure leads to massive blackouts, threatening national security. |
Whether for economic advantage, political intelligence, military insights, or direct sabotage, cyber espionage poses a serious and evolving threat across multiple industries and sectors. Sabotage caused by cyber espionage makes it cyber warfare.
_____
Broader Implications of Cyber Espionage:
Cyber espionage carries significant implications for individuals, businesses, and nations:
-1. Economic Impact: Stolen intellectual property and trade secrets can lead to significant financial losses for businesses, as competitors gain an unfair advantage. Nations may suffer economic consequences if their critical infrastructure or defense capabilities are compromised.
-2. National Security: State-sponsored cyber espionage poses a threat to a country’s national security. Access to classified information or critical infrastructure vulnerabilities can be leveraged for strategic advantage or used in future cyberattacks.
-3. Privacy Concerns: Individuals’ personal information and communications can be compromised in cyber espionage operations, leading to privacy breaches and potential identity theft.
-4. Geopolitical Tensions: Cyber espionage can escalate tensions between nations, leading to diplomatic disputes or even conflict. Accusations of state-sponsored hacking can strain international relations.
-5. Technological Arms Race: As nations invest in cyber capabilities, a global arms race in cyber warfare is underway. The development and deployment of cyber weapons have the potential to disrupt the global balance of power.
______
Cyber espionage is a global threat:
Just like the stories of Robert Ludlum or Tom Clancy highlight traditional espionage extending beyond a select few countries, the reality at hand indicates that the global nature of cyber espionage is just as evident. This global scale of cyber espionage is evidenced by events like the 2020 SolarWinds attack. In this case, a nation-state, likely Russia’s APT29 (Cozy Bear), took advantage of a supply chain vulnerability, impacting 18,000 customers — including a few major U.S. government agencies. Cozy Bear and Fancy Bear further demonstrate this international reach by expanding their targets to include Norwegian and Dutch ministries in instances of state-sponsored hacking. Moreover, North Korea heightens global cybersecurity concerns by allegedly engaging in cyber espionage attacks on countries like Japan, South Korea, and Vietnam. Notably, U.S. intelligence officials traced the 2014 Sony Pictures corporate espionage attack back to the North Korean government (although it has denied any responsibility). These instances, and many others, provide unequivocal proof of the widespread prevalence of cyber espionage.
The General Electric case:
Xiaoqing Zheng, an American citizen of Chinese descent, was accused of spying against General Electric (GE). Mr. Zheng allegedly stole GE’s turbine technology secrets and delivered them to a Chinese business man who allegedly, delivered them to a Chinese official. Mr Zheng worked for GE between 2008 and 2018. The United Sates justice department accused the two men of stealing information to advance their own business interests in two turbine research and development companies – Liaoning Tianyi Aviation Technology Co Ltd and Nanjing Tianyi Avi Tech Co Ltd.
The modus operandi of this inside threat actor included:
-copying secrets into a USB drive until GE blocked the use of these devices;
-encrypting the secrets and use steganography to hide data files in the binary code of digital photo files;
-plugging an iPhone to the work desktop computer to copy the image;
-sending the files to his personal e-mail address.
_
Examples of Cyber Espionage:
Percentage of organizations compromised by at least one successful cyber espionage attack is depicted in figure below:
_
Table below summarizes relevant cyber espionage cases.
For each case or cyber espionage group, first it presents the year of publication of the case report. Then it shows the main attack vector, which in most cases is malware of various types, such as backdoor, trojan, remote access trojan (RAT), multi-featured malware, spyware. There are other cases that indicate social engineering techniques such as spear phishing, e-mail attachments, spam campaigns, among others.
|
Cyber Espionage Cases |
Year |
Main Attack Vector |
|
Mandiant’s APT1 |
2006 |
several malware families |
|
GhostNet |
2009 |
malware (RAT), phishing |
|
Stuxnet |
2010 |
malware (multi-feature) |
|
Flame |
2010 |
malware (RAT) |
|
BundesTrojaner |
2011 |
malware (trojan) |
|
Icefog |
2011 |
malware, social engineering |
|
Mahdi |
2012 |
malware, social engineering |
|
Shamoon |
2012 |
malware, social engineering |
|
Gauss |
2012 |
malware (RAT) |
|
Red October |
2013 |
malware, social engineering |
|
Hacking Team |
2013 |
malware (multi-feature) |
|
Careto |
2014 |
malware, social engineering |
|
Dragonfly-Energetic Bear |
2014 |
social engineering |
|
Regin |
2014 |
malware (spy) |
|
Fancy Bear-APT28 |
2014 |
malware (spy) |
|
OceanLotus-APT32 |
2017 |
malware, social engineering |
|
Sowbug |
2017 |
malware (backdoor, trojan) |
|
Slingshot |
2018 |
router vulnerability |
|
Chafer-APT39 |
2018 |
malware (backdoor) |
|
Double dragon-APT41 |
2019 |
malware |
_
Several significant cyber espionage incidents have taken place over time. Well-known examples of cyber espionage are explained below:
- Titan Rain:
Titan Rain was a concerted series of cyber attacks on US computer systems that began in 2003 and were known to have persisted for at least three years. It is thought that the action is connected to a state-sponsored, advanced persistent threat from China. Titan Rain was the designation, according to the US federal government. In order to steal sensitive data, the Titan Rain hackers acquired access to the computer networks of numerous US defense contractors, including Lockheed Martin, Sandia National Laboratories, Redstone Arsenal, and NASA. Both the US Defense Intelligence Agency and the UK Ministry of Defence were targeted by these hackers. In 2006, a section of the UK House of Commons computer system was shut down by an organized Chinese hacking team. The Chinese authorities denied being in charge. The U.S. administration said that the 2004 attacks were carried out by people with a military-like degree of discipline and blamed the Chinese government for them. According to reports, Titan Rain attacked a number of institutions, including NASA and the FBI. Despite no reports of classified information being obtained, the hackers were able to obtain unclassified data that might show the US’s fitness. Titan Rain caused some trust issues between a few countries and China.
- GhostNet:
The GhostNet network, which hacked computer systems in Tibet, Taiwan, and several other nations, is another well-known instance of Chinese cyber espionage activity. Cyber specialists gave an update on the enormous eavesdropping network GhostNet in 2009. Around 1000 computers in over 100 nations were compromised by the Ghostnet, including those at the German, Thai, Iranian, South Korean, and Pakistani embassies. An extensive operation that, in less than two years, has compromised more than a thousand computers in more than a hundred nations, including many that are located in embassies, foreign ministries, and other government institutions, including those in India, Brussels, London, and New York,
- Night Dragon:
In 2006, the cyberespionage operation known as ” Night Dragon” targeted persons and executives in Kazakhstan, Taiwan, Greece, and the United States, as well as oil, energy, and petrochemical businesses. The unidentified threat actors obtained data from systems and looked for information on financials, oil and gas field production systems, and SCADA systems. Security researchers concluded that the campaign was carried out by a threat organization based in China based on the methodologies, tools, and network activity that were seen.
There were numerous components employed in the attacks, and no one piece or family of malware was in charge. The target network was penetrated as part of the attack’s initial phase. It has reportedly been done using spear-phishing and SQL injection on Web servers that are accessible to the general public. Once inside, the attackers upload open-source hacking software onto the compromised servers to obtain access to the internal network. The internal network was then breached using standard techniques, such as getting access to Active Directory account information or breaking user passwords, to infect networked computers with remote administration trojans. Given that a government carried out this operation, the hackers had access to a lot of hardware, software, and other capabilities.
- Operation Pawn Storm – 2014 onwards:
Attacks on military, embassy, and defense contractor workers from the United States and its allies are typically the focus of Operation Pawn Storm, which is a group of threat actors. The national security division of a U.S. ally as well as opposing factions and dissidents of the Russian government were targeted. Three attack channels were employed by the threat actors: spear phishing emails with malware attachments, a sophisticated network of phishing websites, and exploits inserted into reliable Polish websites. The attackers sent emails to personnel in the military, embassies, and defense contractors, among other possible victims.
- Operation GhostSecret – 2018:
Operation GhostSecret, a global cyberattack campaign, was thought to have been orchestrated by North Korea. The global cyber campaign reportedly involved more than fifteen nations, including the US, the UK, Germany, Japan, and Russia. The goal was to gather data on vital infrastructure, telecommunications, entertainment, healthcare, and other industries. According to experts, hackers created and employed a variety of cyber tools and quickly expand their international activities. Investigations show that the perpetrators employed several malware implants, including one that was not publicly disclosed.
- Operation Sharpshooter – 2018:
Operation Sharpshooter used an in-memory implant to download and retrieve a second-stage implant for further exploitation, which was called Rising Sun. According to the investigation, the Rising Sun infection infiltrates these important businesses, using a novel framework that incorporates source code from the Lazarus Group’s 2015 backdoor Trojan Duuzer. The Lazarus group employed the Duuzer backdoor, which is comparable to the Rising Sun, in the now-famous 2014 Sony breach. The attack was attributed by American authorities to North Korean hackers.
The Rising Sun implant first surfaced in 87 organizations across more than 20 nations in October and November 2018, mostly in the United States. The defense, communications, energy, and finance sectors of many government agencies and numerous private businesses were impacted. The operation’s primary goal appeared to be intelligence gathering. The majority of the impacted organizations speak English. In order to learn more about specific individuals of interest or businesses that handle data pertaining to the industries of interest, this actor has utilized recruiting as bait. Moreover, the operation reportedly began on October 25 with a series of phishing emails that were sent to multiple targets and were disguised to look like recruitment emails. The word attachments from various companies were all filled with what appeared to be real job descriptions.
- APT10 Group and Operation Cloud Hopper – 2018:
A group known as “APT10” had a widespread cyber espionage campaign, according to security specialists. The organization exploited managed IT service providers as middlemen in its attacks to obtain access to the business assets and trade secrets of their target. APT10 is a Chinese state-sponsored cyberespionage organization that has been active since 2006. The firm was accused of spying on and stealing technologies and trade secrets from more than ten nations in 2018. The organization has been tracked by several security companies under various identities, including MenuPass by FireEye, Stone Panda by Crowstrike, APT10 by Mandiant, and POTASSIUM by Microsoft.
The campaign has impacted organizations in North America, Europe, South America, and Asia and most recently, managed service providers (MSPs) in many western countries. The MSPs, which oversaw the infrastructure of the victims’ applications, networks, and systems, were penetrated in order to get access to the networks of their real targets, like the MSPs’ customers. Engineering, industrial production, retail, energy, the pharmaceutical industry, telecommunications, and government organizations are among the sectors impacted. This group was seen in June 2022 utilizing ransomware attacks as a cover to hide its malicious actions, which is an unusual strategy for an APT group to employ.
- SolarWinds Hack – 2020:
In the SolarWinds hack, the hackers inserted malicious code into the Orion framework using a supply chain attack. In the Orion hack, a backdoor was made that the hackers could exploit to pretend to be users and accounts of the targeted companies. Using this backdoor, the hackers were able to access system files while blending in with everyday activities and disguising the malicious code from antivirus software. For this kind of supply chain attack, SolarWinds was a potentially lucrative target. Because so many large corporations and governmental organizations depend on their Orion software, all the hackers had to do was embed the trojan onto a fresh set of updates that SolarWinds would release.
The Sunburst upgrade had already infected millions of PCs globally when it was first discovered in late 2020. The update had been installed by more than 18,000 SolarWinds users, which gave the remote trojan access to all of their users’ computers and networks. Among the notable victims of this attack were the US departments of treasury, state, and health.
A few other examples of cyber espionage are the Microsoft Internet Explorer event, in 2010, The Sony Pictures Entertainment event, in 2014, and the UK energy sector event, in 2015. Between 2009 and 2010, Chinese hacker groups took advantage of a security flaw in Microsoft Internet Explorer to spy on at least 20 foreign media and tech companies. In the months before SPE released a movie that depicts the killing of the head of the nation-state, a North Korean hacker group known as the “Guardians of Peace” conducted cyber espionage against the corporation.
_____
_____
China’s Cyber Espionage surges 150%, Says CrowdStrike in February, 2025
CrowdStrike’s 2025 Global Threat Report finds a rapid rise in China-nexus cyber activity, as well as growing Gen AI use and cloud infrastructure attacks. There’s a clear message to business leaders in CrowdStrike’s comprehensive 2025 Global Threat Report: underestimate your adversaries at your own risk. They are becoming more efficient, focused and business-like in their approach to instigating malicious attacks by harnessing advanced technologies like AI and machine learning – which are being commercialised for cybercriminals as much as they are for the organisations they attack. In the case of Gen AI, for example, highly effective adversaries from all major categories (nation-state, eCrime and hacktivist) have become avid adopters, exploiting the impact of commonly used enterprise tools like chatbots.
Among nation-states in particular, China–nexus activity has surged by 150% overall, says CrowdStrike – one of many rapidly growing threats that businesses must work hard to stay ahead of by reinforcing and fortifying their cybersecurity postures as we move through 2025.
CrowdStrike exposes the growing aggression of China’s cyber operations. While China-nexus adversaries escalated state-sponsored attacks by 150%, the report finds that targeted attacks in financial services, media, manufacturing and the industrial sectors rose up to 300%. The company’s research identified seven new advanced persistent threat (APT) groups linked to China in 2024, five of which were unique in their specialisation and sophistication.
______
______
Social media spying:
In a recent interview to a publication recently, Julian Assange, Wikileaks editor-in-chief and main spokesperson, said that US intelligence and law-enforcement agencies have access to all information on all major social networks and many Internet-based companies. Facebook in particular is the most appalling spying machine that has ever been invented. Here we have the world’s most comprehensive database about people, their relationships, their names, their addresses, their locations and the communications with each other, their relatives, all sitting within the United States, all accessible to US intelligence. Facebook, Google, Yahoo – all these major US organizations have built-in interfaces for US intelligence. Now, is it the case that Facebook is actually run by US intelligence? No, it’s not like that. It’s simply that US intelligence is able to bring to bear legal and political pressure on them. And it’s costly for them to hand out records one by one, so they have automated the process. Everyone should understand that when they add their friends to Facebook, they are doing free work for United States intelligence agencies in building this database for them.
_
Facebook Fakes:
In January 2017 the Israeli Defense Forces published a blog on their website describing an attack on their soldiers and it’s all about the influence tactic known as liking. The attackers (reportedly Hamas operatives) created fake Facebook profiles of attractive young women. The goal of these Facebook fakes was to entices Israeli Defense Forces (IDF) soldiers to befriend them. The Facebook fakes built trust and rapport through messaging and photo sharing. Then the operative (spies) would inquire if the soldier would like to video chat. To do so, requires installing an app that is actually a virus. Once installed the soldiers’ mobile device becomes an open book. Contacts, location, apps, pictures, and files are all now accessible to Hamas operatives.
______
______
Apps spying:
Smartphone spyware apps that allow people to spy on each other are not only hard to notice and detect, they also will easily leak the sensitive personal information they collect. While publicly marketed as tools to monitor underage children and employees using their employer’s equipment, spyware apps are also frequently used by abusers to covertly spy on a spouse or a partner. These apps require little to no technical expertise from the abusers; offer detailed installation instructions; and only need temporary access to a victim’s device. After installation, they covertly record the victim’s device activities — including any text messages, emails, photos, or voice calls — and allow abusers to remotely review this information through a web portal.
Spyware has become an increasingly serious problem. In one recent study from Norton Labs, the number of devices with spyware apps in the United States increased by 63 percent between September 2020 and May 2021. A similar report from Avast in the United Kingdom recorded a stunning 93 percent increase in the use of spyware apps over a similar period.
If you want to know if your device has been infected by one of these apps, you should check your privacy dashboard and the listing of all apps in settings.
While Google does not permit the sale of such apps on its Google Play app store, Android phones commonly allow such invasive apps to be downloaded separately via the Web. The iPhone, in comparison, does not allow such “side loading” and thus consumer spyware apps on this platform tend to be far more limited and less invasive in capabilities.
Spyware apps surreptitiously run on a device, most often without the device owner’s awareness. They collect a range of sensitive information such as location, texts and calls, as well as audio and video. Some apps can even stream live audio and video. All this information is delivered to an abuser via an online spyware portal.
Spyware apps are marketed directly to the general public and are relatively cheap — typically between $30 and $100 per month. They are easy to install on a smartphone and require no specialized knowledge to deploy or operate. But users need to have temporary physical access to their target’s device and the ability to install apps that are not in the pre-approved app stores.
______
Is TikTok really spying:
Officials, politicians and security staff in many Western countries have been banned from installing TikTok on work phones. Critics argue TikTok is a “Trojan horse” – although it looks harmless, it could prove to be a powerful weapon during times of conflict.
-1. TikTok collects an ‘excessive’ amount of data:
TikTok says the app’s data collection is “in line with industry practices”.
A test carried out by Citizen Lab concluded “in comparison to other popular social media platforms, TikTok collects similar types of data to track user behaviour”. Similarly, a report by the Georgia Institute of Technology stated: “The key fact here is that most other social media and mobile apps do the same things.”
-2. TikTok could be used by the Chinese government to spy on users:
TikTok says the company is fully independent and “has not provided user data to the Chinese government, nor would we if asked”.
The issue that critics have with TikTok is that it is owned by Beijing-based tech giant ByteDance, making it unique as a non-American mainstream app. Facebook, Instagram, Snapchat and YouTube, for example, all collect similar amounts of data but are all US-founded companies. For years, US lawmakers, along with most of the rest of the world, have assumed a level of trust: that the data collected by these platforms will not be used for nefarious reasons which might put national security at risk.
Article seven of China’s National Intelligence Law states that all Chinese organisations and citizens should “support, assist and co-operate” with the country’s intelligence efforts. This sentence is often cited by people suspicious not just of TikTok, but all Chinese companies.
However, researchers from the Georgia Institute of Technology argue this sentence is taken out of context, and note that the law also includes caveats protecting the rights of users and private companies.
In 2022, ByteDance admitted that several of its Beijing-based employees did access the data of at least two journalists in the US and UK to track their locations and check whether they were meeting TikTok employees suspected of leaking information to the media. TikTok’s spokeswoman says the employees who accessed the data were dismissed.
The firm insists user data has never been stored in China and is building data centres in Texas for US user data, and at sites in Europe for data from its citizens. In the EU the company has also gone much further than any other social network and enlisted an independent cyber-security company to oversee all use of data at its European sites. TikTok says “data of our European users is safeguarded in a specially designed protective environment, and can only be accessed by approved employees subject to strict independent oversight and verification.”
-3. TikTok could be used as a ‘brainwashing’ tool:
TikTok argues that its community guidelines “prohibit misinformation that could cause harm to community or the larger public, which includes engaging in co-ordinated inauthentic behaviour”.
In November 2022, Christopher Wray, director of the Federal Bureau of Investigation, told US lawmakers: “The Chinese government could… control the recommendation algorithm, which could be used for influence operations.” The claim has been repeated many times.
Those concerns are further inflamed by the fact that TikTok’s sister app, Douyin – which is only available in China – is heavily censored and reportedly engineered to encourage educational and wholesome material to go viral for its young user base. All social networks are heavily censored in China, with an army of internet police deleting content which criticises the government or excites political unrest.
At the start of TikTok’s ascendancy, there were high-profile cases of censorship on the app: a user in the US had her account suspended for discussing Beijing’s treatment of Muslims in Xinjiang. After a fierce public backlash, TikTok apologised and reinstated the account. Since then there have been few cases of censorship, other than the sort of controversial moderation decisions with which all platforms have to deal.
Researchers at Citizen Lab carried out a comparison of TikTok and Douyin. They concluded that TikTok does not employ the same political censorship. “The platform does not enforce obvious post censorship,” researchers said in 2021.
Georgia Institute of Technology analysts also searched for topics such as the independence of Taiwan or jokes about Chinese President Xi Jinping, and concluded: “Videos in all of these categories can easily be found on TikTok. Many are popular and widely shared.”
In conclusion, while there’s no concrete evidence of widespread spying, TikTok’s data collection practices and ByteDance’s ties to China have raised legitimate concerns about privacy and security. Users should be aware of these concerns and take steps to protect their personal information.
______
______
Prevent Cyber Espionage:
One of the most challenging tasks for those tasked with protecting desirable targets like government agencies, military contractors, and research organizations is routing out cyber spies. Attacks for cyber espionage are frequently well-funded, highly technical, and remarkably undetectable online. According to reports, there are numerous instances of cyberespionage that compromised their targets quickly, sometimes in a matter of seconds. It can take months or years for victim organizations to learn about the attack. Although some general cyber health procedures are beneficial, there are several specialized considerations that go into reducing the danger of cyber espionage:
- Strong passwords and multi-factor authentication: Make sure to change the passwords for your online accounts every week or month. Establish a company policy to ensure that the staff members adhere to these digital security habits. Every employee in a company or government agency must promote a culture of electronic data security. Password sharing, using work email for personal purposes, leaving laptops unlocked, or pausing device security updates are all prohibited for employees. Use multi-factor authentication (MFA) procedures for all system and facility accesses across the enterprise. This aids in identifying issues and the point of the breach of security.
- Regular software and security updates: Software updates bring new and improved capabilities while eliminating bugs and crash-related issues. Antivirus companies frequently upgrade their solutions to make them better in order to protect you from new viruses and malware. The prevention of cyber espionage is aided by reviewing software source code. Get a software engineer to examine the source code from top to bottom before installing any program. This will prevent a business adversary from sabotaging any software deliveries to harm your company’s equipment or workstations.
- Network segmentation and firewalls: Network segmentation is a method for dividing a network into a number of segments or subnets, each of which operates as a separate independent network. The flow of network traffic between subnets can then be managed by network administrators using detailed policies. Give as few people access to your business data as you can. Use highly developed cloud storage services to grant immediate access to necessary company data and withdraw access after the work is complete.
- Encryption for sensitive data: Data is converted into another form, or code, via data encryption so that only those with a secret key (officially referred to as a decryption key) or password may decode it. While encrypted data is commonly called ciphertext, unencrypted data is known as “plaintext”. Encryption safeguards sensitive data, private information, and the security of communication between client apps and servers. In essence, if your data is encrypted, it won’t be readable even if someone or something has access to it without your consent.
- Regular backups and disaster recovery plan: It takes effort, planning, and automation to create a thorough disaster recovery plan. Integrity, usability, security, and documentation are the main subjects to consider. Doing nightly backups is significantly simpler than creating a thorough backup strategy. There are many possible situations to take into account, and considering them all may be unrealistic given the current status of your firm. Knowing what you cover, what your risks are, and making sure all decision-makers are at ease with those risks are crucial components of a strong backup and disaster recovery plan.
Understanding the fundamentals of backup and disaster recovery helps you create successful plans that reduce downtime. To determine which deployment option is best for your firm, compare several cloud and on-premises choices. Choose the technologies that will help you achieve your backup and disaster recovery objectives.
You may create efficient strategies for preventing the effects of downtime by distinguishing backup from disaster recovery, defining keywords, and analyzing alternative deployment options and technologies.
- User education and awareness training: Inform yourself and your staff. There must be ongoing cybersecurity training for you and your employees. Because the IT industry is always changing, it’s important to be informed about the most recent methods of cyber espionage.
- Implement a “zero-trust” philosophy within your company: Establish a “zero-trust” policy for all business data across the firm. Every internal and external piece of equipment connected to the organization must be assumed to have been compromised in this situation by the cyber security team. The burden of proof should fall on the employee to demonstrate that the device is free of malware, spyware, Trojans, and other threats.
- Stop utilizing illegal software at your company: The source codes in pirated software have been tampered with, therefore installation does not require any code validation. As a result, these are the most convenient means of spreading malware, spyware, and trojans. Avoid using such apps both personally and professionally.
- Limiting network access for third-party vendors: A crucial first step in reducing the risk to your confidential and sensitive information is having visibility into where data moves and who has access to these data. Make a list of the vendors in your network and map their access to data. Companies should inquire with their vendors about their procedures and security measures for controlling access to sensitive information. To make sure that only authorized staff can view sensitive client information, this could include multi-factor authentication, two-step verification, encrypting data while in transit, or other security procedures.
- Vulnerability scanning and penetration testing: An automated, high-level test called a vulnerability scan searches for and notifies potential vulnerabilities. A penetration test is a thorough, hands-on inspection conducted by a real person with the goal of finding and exploiting vulnerabilities in your system. With vulnerability scanners, businesses are made aware of the existence and location of flaws in their code. During penetration tests, faults that could endanger the program are sought out in an effort to discover whether unauthorized access or other harmful behavior is feasible.
- Monitoring for unusual network activity: Today, software that can track employee activities, including access to particular data repositories, apps, and edge or portable devices, is available on almost every network, hardware, and software platform. Tools for detecting malicious traffic continuously scan network traffic for indications of questionable files, links, or behaviors. The tools evaluate whether the suspicious item is originating from a problematic URL or other channels in order to spot fraudulent internet activity. Your personnel will be informed of potentially malicious activities in your network via an Intrusion Detection System (IDS). Nevertheless, this tool does not take any steps to prevent or correct an attack; it merely identifies it and tells your IT department about it. If there is unlawful access or if access is taking place in a region of the nation or the world where it shouldn’t be, this security monitoring program can send out an alert. This enables IT to look into the problem right away.
- Incident response and threat intelligence sharing: An organization foresees possible dangers by using well-planned incident response and threat intelligence services. An efficient threat intelligence program and a strong incident response framework are the first steps in being able to recognize and address issues as soon as possible. The phases of the incident response cycle should include threat intelligence techniques like preparation, containment, and mitigation.
_______
_______
Section-6
The psychology of spying:
Espionage has been an integral part of human history, stretching back to ancient civilizations that relied on secret intelligence to safeguard their territories and gain strategic advantages. From the biblical accounts of spies surveying the Promised Land to the advanced intelligence networks of today, espionage has grown into a vital tool for ensuring national security and shaping global strategies. However, beyond its tactical importance lies a deeply human story— one marked by psychological intricacies, ethical challenges, and the influence of diverse cultural perspectives.
_
Spies navigate a complicated world of duplicity and danger, where personal identities and emotional stability are often the price of serving a greater cause. The psychological toll of espionage reaches far beyond the agents themselves, spreading ripples of betrayal, paranoia, and mistrust to the individuals and organizations they target. To grasp the psychological complexities of espionage, we must delve into the motivations that drive people to become operatives, the mental strain of leading double lives, and the profound consequences of deception on both spies and their unsuspecting victims.
_
Espionage has shifted from traditional methods to digital operations, bringing new psychological challenges. Cyber espionage and modern surveillance tools allow spies to remain physically distant from their targets, but this detachment creates ethical concerns. The use of technology can make it easier for operatives to justify questionable actions while increasing the vulnerability of their targets (Singer & Friedman, 2014). Historically, espionage has also been shaped by cultural nuances. What is considered an acceptable intelligence gathering tactic in one region may be deemed unethical or illegal in another. Cultural frameworks influence both the methods used and the psychological resilience of operatives working in foreign environments. For instance, Cold War espionage often hinged on ideological convictions, whereas modern intelligence gathering is frequently driven by economic and technological competition. (Andrew, 1999).
_
The psychology of spying encompasses the study of how spies think, behave, and are motivated, as well as the psychological strategies they employ to gather information and achieve their objectives. It involves understanding human behavior, deception, manipulation, and the resilience needed to withstand the pressures of espionage. Spies often leverage trust, empathy, and vulnerability to build relationships and gain access to secrets. The world of espionage is not just about physical prowess and high-tech gadgets; it’s equally about the mental and psychological aspects. Understanding the psychology behind espionage can offer fascinating insights into what drives spies and how they operate under extreme conditions.
-1. The Mindset of a Spy
Being a spy requires a particular mindset. Traits like adaptability, resilience, and the ability to think quickly under pressure are paramount. Spies often need to make split-second decisions that can have far-reaching consequences, which requires a high level of mental agility and emotional control.
-2. The Art of Deception
Deception is a key element of espionage. Spies must be skilled in lying and manipulating situations to their advantage. This requires not only a natural talent for deceit but also an understanding of human psychology to predict and influence others’ behavior.
-3. Coping with Stress and Isolation
Spies often work in stressful and isolating conditions. The ability to manage stress and maintain mental well-being is crucial. This includes coping with the loneliness that comes from being cut off from family and friends and the constant fear of discovery.
-4. Training and Mental Preparation
Intelligence agencies invest significantly in training their agents to handle the psychological aspects of espionage. This training includes everything from learning interrogation resistance techniques to developing emotional intelligence skills.
-5. Moral and Ethical Considerations
Spies often face moral and ethical dilemmas that can cause internal conflict. Balancing national security interests with personal ethics can be challenging, and spies must often navigate complex situations where the lines between right and wrong are blurred.
______
______
Psychological challenges faced by spies:
Spies operate in one of the most psychologically demanding professions in existence. Their work requires a unique combination of mental fortitude, adaptability, and an unwavering ability to maintain composure under constant pressure. While their actions are often seen as patriotic or strategic, the psychological demands of espionage frequently blur the lines between duty, morality, and personal identity.
_
Cognitive Dissonance:
One of the most persistent psychological challenges faced by spies is cognitive dissonance, a mental state of discomfort arising from holding conflicting beliefs or engaging in actions that contradict one’s values. Many operatives enter the field motivated by ideals of patriotism or loyalty, only to find that their work involves betrayal, deception, and the manipulation of others. (Festinger, 1957).
For instance, a spy might need to exploit personal relationships to gain access to classified information, causing internal conflict between their professional goals and their personal morality. The tension between serving the greater good and committing acts of betrayal can create a psychological strain that may not surface immediately but builds over time.
Studies in psychology, such as those by Leon Festinger (1957), highlight how individuals attempt to resolve cognitive dissonance by rationalizing their actions. Spies may justify morally ambiguous decisions by emphasizing their contributions to national security or the belief that their actions prevent greater harm. However, unresolved dissonance can lead to long-term psychological issues, including guilt, anxiety, and depression. (Festinger, 1957).
_
Paranoia:
The nature of espionage ensures that spies live in a state of near-constant paranoia. Operatives are trained to anticipate threats, uncover deception, and identify potential surveillance, which fosters hyper-vigilance—a heightened awareness of their surroundings. While these skills are critical for survival in the field, they can also be psychologically draining.
Paranoia, although necessary to evade detection, often becomes pathological. Spies might begin to mistrust even their closest allies, fearing betrayal or exposure. This pervasive fear can lead to social isolation and difficulty reintegrating into normal life. Historical accounts from former agents, such as those detailed in memoirs by Cold War defectors, reveal how living under constant suspicion can erode trust in others and lead to severe mental health challenges. (Andrew, 1999).
_
Identity Crisis and the Double Life:
A spy’s ability to assume a false identity is one of their most critical tools. Yet, living under an alias for extended periods often comes at a psychological cost. The constant act of pretending to be someone else can create a profound sense of identity crisis. Operatives may struggle to reconcile their fabricated persona with their true self, leading to confusion about their own identity and purpose. (Erikson, 1968).
Erik Erikson’s (1968) theory of identity formation suggests that maintaining a coherent sense of self is vital for psychological well-being. For spies, however, this coherence is frequently compromised. They might adopt the habits, beliefs, and even emotional connections of their false identity, making it difficult to detach from their role once their mission concludes.
Moreover, living a double life often necessitates severing ties with friends and family, further contributing to a sense of isolation. Former CIA agents have reported that maintaining relationships with loved ones becomes nearly impossible when operating under the shadow of secrecy. The emotional detachment required to sustain their cover can lead to long-term damage in personal relationships and emotional health.
_
Emotional Resilience:
Espionage requires exceptional emotional resilience. Spies must remain calm in high-pressure situations, from navigating hostile environments to executing complex deceptions. Training programs for operatives often include psychological conditioning designed to enhance their ability to handle stress. Techniques such as compartmentalization—mentally separating personal emotions from professional tasks—are frequently employed to help spies remain focused on their objectives.
However, this resilience has its limits. Chronic stress, compounded by the ever-present threat of exposure, can lead to burnout and post-traumatic stress disorder (PTSD). Psychological studies on military personnel and covert operatives indicate that extended exposure to high-stress environments significantly increases the risk of PTSD, particularly in situations where operatives witness or participate in traumatic events.
_
Loyalty vs. Betrayal:
One of the most emotionally taxing aspects of espionage is the act of betrayal. Spies often form relationships of trust with their targets, only to exploit those bonds for intelligence. While some operatives view this as a necessary evil, others struggle with the guilt and emotional fallout of such actions.
Additionally, spies themselves are frequently at risk of betrayal. Double agents and informants have been integral to some of the most famous intelligence operations, leading operatives to question the loyalty of their own colleagues.
This cycle of betrayal fosters an environment of mistrust, further exacerbating the psychological toll.
_
Real-World Examples:
Historical accounts provide valuable insights into the psychological experiences of spies. For instance:
The Cambridge Five, a group of British double agents during the Cold War, struggled with ideological conflicts as they spied for the Soviet Union while holding positions of trust in Western intelligence. Their dual allegiances created significant moral dilemmas, and several members later expressed regret for their actions. (Andrew, 1999).
Aldrich Ames, a CIA officer turned Soviet spy, cited financial motivations and personal grievances as key factors in his betrayal. However, his later imprisonment revealed the profound psychological consequences of his actions, including isolation and estrangement from his family.
_
Psychological Support:
Given the immense psychological challenges faced by spies, many intelligence agencies now prioritize mental health support for their operatives. Counselling, decompression programs, and reintegration strategies are increasingly recognized as essential tools for helping spies cope with the demands of their work.
For example, post-mission debriefings often include psychological evaluations to assess the operative’s mental state. In some cases, retired spies receive ongoing support to address issues such as PTSD and difficulties reintegrating into civilian life.
______
______
Professor Adrian Furnham and John Taylor have written an authoritative book, “The Psychology of Spies and Spying” which describes in detail the real world of spies. It is rich in its insights and description of skills which are useful for people in business. Here are three.
-1. Assessing People
There are two kinds of spies – the professional intelligence officer (IO), usually employees of government agencies such as the CIA, SIS and DGSE. These people go through thorough selection and vetting procedures which are among the most rigorous assessment centres in the recruitment world.
Then there are the agents, the human sources. These people are recruited for one reason only – they have access to secret intelligence. Their work with the intelligence agency is illegal and if discovered they will go to prison for a long time and in many countries, they face execution. The job of the intelligence officer is to assess the personality and the motivation of the agent.
Agents are not given sophisticated personality questionnaires, demanding written and practical exercises nor a structured interview. The intelligence officer must make the assessment during a ‘cultivation’ involving social meetings and conversations in restaurants. If the IO is lucky there will be an online presence on Facebook, LinkedIn or other social media.
During a cultivation the IO will collect information on six dimensions of their ‘target’. Insights into their cultural background, their early years, intellect and personality all help to understand the individual.
Potential dark side behaviours and motivations are critical. Businesspeople, just as Intelligence Officers need to know if their recruits or potential business partners suffer serious personality disorders such as the toxic trio: narcissism, sociopathy or Machiavellian.
The presence of these or other personality disorders does not necessarily mean the recruitment will be dropped. Some of our greatest business leaders suffer all three. And it’s the same for some of the greatest intelligence agents. Intelligence officers learn how to identify these characteristics and to manage them.
Agent motivation is no less important or complex. Rarely does an agent work for one reason. Usually, it is a mix. Material motivation (money) is often present but on its own is difficult to manage. Ideology (caring about the company’s vision and mission), respect and liking for the intelligence officer (McClelland’s ‘affiliation’), excitement (stimulation) and a desire to change the world (achievement) are often significant parts of a motivation picture. There is another motivation which often drives agents – ‘disenchantment’ with their leaders.
-2. Influencing others
The task of an intelligence officer is formidable. Having assessed a potential agent, they then have to ‘recruit’ him or her. This is not putting a business proposal together with inputs and outputs, costs and revenue or the description of how a project might be managed. The IO has to persuade a foreign national to commit treason; if discovered they will go to prison for a long time, some will be executed.
IOs will use all the techniques familiar to businesspeople, for example the six influencers described by Cialdini in “Influence, The Psychology of Persuasion”. In “Influence, The Psychology of Persuasion,” Robert Cialdini identifies six key principles that influence how people make decisions and say “yes”: Reciprocity, Commitment and Consistency, Social Proof, Liking, Authority, and Scarcity. In addition, they have to establish trust and, in most cases, a significant degree of liking for the intelligence officer and subsequently the agency itself. Agent handlers often move jobs and posts, so they have to ‘handover’ the agent to a colleague. The initial respect and liking must be transferred to someone else in the same agency. George Smiley’s world is dominated by betrayals and suspicion. In the real world of espionage trust dominates the mindset.
-3. The Insider Threat
The role of disenchantment as a significant motivator for agents is mentioned earlier. An intelligence officer roaming the diplomatic cocktail circuits, international business meetings or even in these electronic days the Internet is looking for potential recruits. If they come across someone who extols the virtues of their country and the wisdom and excellence of their boss, they will not linger long with that individual. If however they come across someone who is likely to have intelligence and who is unhappy with their lot at work or with the actions of their leaders, the IO will explore and if promising, befriend the unhappy person. Disenchanted workers are the kindling for insider threats. The question is whether this is the result of bad apples or toxic bosses?
Furnham and Taylor have conducted research on this over many years and developed tools to measure disenchantment in organisations. This shows that there are people, with personality characteristics which are more likely to result in actions against their employer. The temptation is to select these people out at the recruitment stage. The problem with that approach is that many potential leaders and drivers in an organisation will also be selected out!
More interestingly Furnham and Taylor’s research shows that those who are disenchanted are often grouped together in departments or sections where the boss is toxic in one way or another.
Furnham identified five reasons for such disenchantment as seen in figure below:
- Corporate/Organisational Lying – belief that the way the company presents itself is hypocritical, saying it values one thing but never adheres to it.
- Perceived Inequity – belief that others in the organisation are treated differently; favouritism; that getting far is more about networking than working hard/showing loyalty.
- Respect – belief that colleagues are callous and bullies, putting others down and making it difficult to do your job.
- Broken Promises – the company has let you down; not giving the promotion/development opportunity/time off that was promised in exchange for hard work.
- Distrust – the company does not trust its employees to work without unnecessary scrutiny.
This is the stuff of what an intelligence officer is looking for. The world of espionage is full of insights and solutions. Here we have identified three aspects with direct relevance to the business world. There are many more described in Taylor and Furnham’s book ‘The Psychology of Spies and Spying’. Bond and Smiley may not be role-models for those in business, but they certainly entertain. The real spies may be secretive and hard to decode, but this book points the way and contains more insights into their world and how we can all benefit from their experience.
______
______
Section-7
Agents and Agencies:
In espionage jargon, an “agent” is the person who does the spying. They may be a citizen of a country recruited by that country to spy on another; a citizen of a country recruited by that country to carry out false flag assignments disrupting his own country; a citizen of one country who is recruited by a second country to spy on or work against his own country or a third country, and more. In popular usage, this term is sometimes confused with an intelligence officer, intelligence operative, or case officer who recruits and handles agents.
Agents and intelligence officers:
Spies working for states fall into two categories: intelligence officers and agents.
Intelligence officers:
Intelligence officers are members of intelligence services. They will be highly trained in espionage techniques and the use of agents. They may operate openly, declaring themselves as representatives of foreign intelligence services to their host nation, or covertly under the cover of other official positions such as diplomatic staff or trade delegates.
Some intelligence officers may operate under non-official cover to conceal the fact that they work for an intelligence service – posing as a business person, student or journalist for example. In some cases they may operate in “deep cover” under false names and nationalities. Such spies are dubbed “illegals” because they operate without any of the protections offered by diplomatic immunity.
Agents:
An agent is someone who secretly provides information to an intelligence officer. They will probably not be a professional “spy” but may have some basic instruction in espionage methods. An agent may be motivated by a wide variety of personal or ideological factors.
Confusion often arises between what is meant by an officer and an agent. Other countries use the same terminology in different ways. In the United States, for instance, an agent is a member of an intelligence or security agency such as the FBI or CIA. Such agencies call a covert human intelligence source an “informant” rather than an “agent.”
_
How intelligence officers and agents operate:
Intelligence officers seek to gather covert intelligence directly and to recruit agents to obtain intelligence on their behalf. The methods used by intelligence officers vary widely, and are often limited only by their ingenuity. They will often take advantage of the latest technology, using it to eavesdrop, tap telephone calls and communicate secretly. However, the human relationship between intelligence officers and their agents remains a key element of espionage.
Foreign intelligence services typically seek to establish networks of agents whom they can use over a sustained period of time, so that they can obtain a reliable flow of information. Agents operate by exploiting trusted relationships and positions to obtain sensitive information. They may also look for vulnerabilities among those handling secrets. They may be aware of flaws in their organisation’s security that they can exploit.
_
Agent Handlers:
The most important assets (agents) are those who provide secret intelligence. They betray their employer’s trust. The Handler must, therefore, manage the relationship with great care so the source’s employers do not discover what the source is doing. It is perhaps the greatest skill that a Handler has: agent recruitment and handling.
Handlers need to establish a high degree of trust with their agents. The Handler also needs strong powers of charm and persuasion. At the same time, the Handler must ensure that potentially hostile people or technical devices do not observe their meetings.
This latter process is known as tradecraft or street craft and involves the use of clandestine communication systems such as a brush contact or dead letter box. Source Handlers also must become experts in identifying hostile surveillance.
_
The assessment of intelligence officers:
The main skills and qualities which recruiters will look for in their assessment of potential intelligence officers are summarized below:
-1. Intellectual horsepower – Not everyone in an organization needs to be super clever; they do however need to be ‘bright enough’. There are different kinds of intellect that are required in an intelligence service:
• Intellectual and cognitive capacity (IQ): an individual’s efficiency at information processing and storage. It predicts how quickly and efficiently they learn. People can be taught skills but there is not much people can do to improve their intelligence.
- Analytical: the ability to identify relationships and patterns from information and data.
• Numeric or deductive ability: this relates to those posts which demand a strong mathematical or scientific approach to their work.
-2. Personality – is about preferred ways of doing things and seeing the world. Intelligence officers cannot change their personalities but they can learn to change their behaviors. Different roles require different personality traits. Recruiters will want to assess the following:
- Stability/resilience/composure – an ability to withstand stressful external stimuli without psychological hindrance. All roles involve pressure, some more than others. It is important that people do not buckle under pressure and make bad decisions.
- Openness/inquisitiveness – open to experience and embrace the new and the different. They are less fazed by unusual or different places, people, or ways of doing things. Inquisitiveness is about an individual’s ability to innovate and be curious when presented with intelligence from an existing source or a new source.
- Sociability/extraversion – value social interaction and a preference to work in groups and as part of a team. Introverts value independence, preferring to work alone, or in an insular manner.
-3. Risk-taking preferences – central to intelligence roles is the concept of risk. While all risks are thoroughly analyzed, understood, and (as much as possible) mitigated, intelligence roles require that people take risks.
• ‘Hot’ Risk – risk where decisions have immediate (and potentially dangerous) consequences. This represents a person’s willingness to engage in missions that are physically stimulating/frightening.
• ‘Cold’ Risk – risk where decisions have effects that are distant and in the future. This represents a person’s willingness to make strategic decisions based on intelligence or challenge existing intelligence in favor of a different strategy. It is calculated, planned, and strategic.
-4. Drive/conscientiousness/work ethic – this trait assesses the level of self-motivation, organization, and drive within an individual. A conscientious person is organized, reliable, and responsible.
-5. Integrity/honesty – an individual’s ‘moral compass’. It focuses on whether the individual is manipulative, callous, and devious or whether they have an ethical sense and moral backbone. This is one of the most important traits in the spying world, famous for its intrigues and falsehoods. It is vitally important that insiders can trust their colleagues.
-6. Skills – Skills can be taught – people can learn to do better. Inevitably an individual’s intellect and personality tend to dictate both what skills they initially have and how efficiently they learn further or higher skills.
- Interpersonal skills – the ability to cultivate and maintain relationships. Certain jobs specify a need for strong social skills, not only to gather information but also to operate with others.
- Observational skills – the ability to observe and follow targets. Certain roles have a need to be aware of their surroundings.
- Physical ability – some roles require more than average physical fitness.
- Leadership – leadership is relevant primarily for the Spymaster and for those who have to lead groups. It needs to encompass strategic ability, ambition, and a willingness to delegate. The desirable qualities of a leader are much debated.
______
______
Types of spies:
Spy agents, or intelligence operatives, come in various forms, each with unique roles and responsibilities. Some common types include field agents who gather information, intelligence officers who manage operations, and double agents who work for opposing sides. Additionally, there are agents of influence, sleepers, and those who act as informants or fabricators.
Here’s a more detailed breakdown:
- Field Agents:
These are the individuals on the ground, tasked with collecting intelligence through observation, infiltration, and gathering information.
- Intelligence Officers:
These are the professionals who manage operations, recruit agents, and provide support to the field agents.
- Asset:
An asset refers to a person, organization, or other resource that provides information or assistance to an intelligence agency. This could be a spy, a confidential informant, or even a piece of technology like a surveillance device.
- Double Agents:
These agents are spies who secretly work for an opposing intelligence agency, often providing misinformation or manipulating the enemy.
- Agents of Influence:
These agents are individuals who are used to subtly influence public opinion or policy in a target country or region.
- Sleeper Agents:
These agents are placed in a target area, but are not activated immediately. They are activated when needed, potentially causing disruption or providing valuable information.
- Informants:
These individuals provide information to intelligence agencies, often for a reward or other incentives.
- Fabricators:
These agents create false information or documents to deceive the enemy.
- Resident Spies:
These agents operate within a foreign country for extended periods of time, often establishing a “station” or “rezidentura” to coordinate their activities.
- Executive Agents:
These agents are tasked with carrying out missions that involve physical violence or sabotage, such as assassinations or damage to infrastructure.
- Recruiting Agents:
These agents are responsible for recruiting new spies.
- Local Spies:
Spies familiar with a specific area and its local contacts, often used for gathering information about specific events or locations.
- Inside Spies:
Spies who have a connection to an enemy group or country, allowing them access to sensitive information.
- Reverse Spies:
Spies who were formerly working for the enemy, now used to provide them with false information.
- Dead Spies:
Spies who are killed or allowed to die to provide false information to the enemy.
- Walk-in:
Shows up and offers his services and historically some of the best agents are walk-in e.g. Oleg Penkovsky (British/US agent), John Walker (Sov agent), Aldrich Ames (Sov agent), Jonathan Pollard (Israeli agent)
- Confusion agent:
Provides misleading information to an enemy intelligence service or attempts to discredit the operations of the target in an operation.
- Facilities agent:
Provides access to buildings, such as garages or offices used for staging operations, resupply, etc.
- Illegal agent:
Lives in another country under false credentials and does not report to a local station. A nonofficial cover operative can be dubbed an “illegal” when working in another country without diplomatic protection.
- Principal agent:
Functions as a handler for an established network of agents, usually considered “blue chip”.
- Agent provocateur:
Instigates trouble or provides information to gather as many people as possible into one location for an arrest.
- Intelligence agent:
Provides access to sensitive information through the use of special privileges. If used in corporate intelligence gathering, this may include gathering information of a corporate business venture or stock portfolio.
- Covert vs. Overt spies:
Covert spies work in secret and their actions are not acknowledged by the government they work for. Overt spies are open about their affiliation with a government and carry out their duties under official cover.
- Moles:
These spies work within an organization or government and gather information from within. For example, a mole within a foreign intelligence agency who provides information to another government.
- Access agents:
An access agent does not have significant access to material of intelligence value, but has contact with those who do.
_
Sun Tzu types of spies:
There are five kinds of spy: The local spy, the inside spy, the reverse spy, the dead spy, and the living spy. When the five kinds of spies are all active, no one knows their routes – this is called organizational genius, and is valuable to the leadership. Local spies are hired from among the people of a locality. Inside spies are hired from among enemy officials. Reverse spies are hired from among enemy spies. Dead spies transmit false intelligence to enemy spies. Living spies come back to report.
______
______
Agent recruitment:
Spies have to find, charm, befriend and motivate agents effectively to commit treason. Many of the best secrets come from people who are betraying their country or terrorist organisation. The spies’ job is to find people who have secrets they want (they call these people ‘agents’), assess their potential motivation to spy, understand their personality and motivation, recruit them as a secret source, and then manage them as they pass their secrets, often in very dangerous circumstances. This is a deeply complex and sophisticated task. It follows that agents are recruited not because they have the desirable skills and attributes necessary for such a demanding job, but for one reason alone – do they have access to secrets that the spies and their masters want. Spies, that is the professional intelligence officers, have therefore to have excellent judgement and influencing skills. It is a skilful business using a range of sophisticated psychological techniques. It is often said that they need the combined skills of an actor, salesman, counsellor and journalist.
_
Handlers receive a lot of training in how to meet, cultivate, recruit and run an agent. There are essentially seven steps as seen in figure below.
Potential agents need to be found. Usually, the next step is developing some sort of relationship with them. While this is occurring, there is a great deal of assessment essentially about two things: what they know, and what they are like. Then, and only then, are they formally recruited, so they know who they are dealing with and “the rules of the game”.
Often, the trickiest bit is what is called handling, which means developing the relationship to get the secret information that is wanted. The spy-agent relationship may continue for many years, which means a handler has to hand over the relationship to a colleague when he or she is posted to another assignment. Finally, when the task is done, the relationship is terminated.
_
Understanding Agents:
Spies have to assess their agents, as do selectors. They have to understand how they deal with stress, how they build relationships, how easily they learn and follow instructions, and where any potential danger points are.
Clearly, agents can’t be put through assessment centres with all the sophisticated techniques used by work psychologists (the CIA do ask their agents to go through a polygraph test). Spies, often working in a second (or third) language, may only have short, clandestine meetings with their agent to try and understand them. Many agents are difficult, disturbed and unattractive individuals; but all have to be cultivated and recruited. The question is how to achieve that end. There appear to be six things that one needs to know in order to understand an individual as seen in figure below.
The first is the cultural and sub-cultural background of the agent. This is essentially cross-cultural psychology and draws upon the work of people like Hofstede. It is about how the place and time a person grows up shape their world view. We know how influential the titanic fascism-communism clash of the 1930s was in shaping so many famous spies. Is the potential agent an Egyptian Coptic Christian, a white South African, or a Baltic Russian? How did the place and time of their upbringing shape their world view and ideology?
Second, what about their personal upbringing – their bio-data? Were their parents rich or poor, strict or liberal, cold or loving? Did they have any handicaps to overcome as a child? What was the predominant religion and belief system they were exposed to in their youth?
Third, are they bright enough to do the somewhat complex tasks required in the job? Is there evidence of their information-processing speed and retention that gives one confidence they could do the job?
Fourth, what about their personality, paying particular attention to two traits: neuroticism and conscientiousness, which we know are the two strongest determinants of any work performance? Neuroticism, or emotional stability, is relevant primarily because it relates to how the agent copes with stress, both acute and chronic, which is an inherent part of the job. It is vitally important to know how agents regulate their emotions, what things make them most stressed and how adaptive their coping strategies are.
Fifth, and more relevant, are the dark-side personality traits: the sub-clinical personality disorders. Of these, two are particularly relevant: anti-social (psychopath) and narcissistic personality disorder. The focus on what is now called the “dark triad” has always been fundamental. Are they fantasists or mercurial? Are they a bit of a loner, unable to establish relationships?
And finally, sixth, possibly the most difficult bit: what really, fundamentally motivates them? Differential psychologists usually attempt to measure three areas of an individual: ability, personality and motivation. It is usually agreed that it is the last of these that is most difficult to measure. For those in the spying business, one of the most important tasks is to try to understand the motives of the agent, which they themselves may not be able to articulate clearly.
An analysis of many successfully and unsuccessfully recruited and run agents suggests a short list of motives that can be crudely classified into three groups as seen in figure below:
There are “push” factors concerning deep unhappiness and bitterness about the way they have been treated by an organisation they worked for. This could be a commercial or a government organisation. There are also “pull” factors to the world of espionage, such as powerful and deep-seated ideological beliefs, material benefits (mainly money) as a reward, and the sheer excitement of the whole activity. Third, there is the reward of a friendship and relationship with the spy and his/her colleagues.
_
When Shawnee Delaney worked for the Defense Intelligence Agency she was tasked with gathering tactical information on America’s enemies in the Middle East. It fell to her to recruit a Mullah, a committed fundamentalist who had close ties to Osama bin Laden but who started having doubts about al-Qaeda after 9/11. The Mullah had not been formally recruited yet for a simple reason: he wouldn’t agree to take money, and money makes the spying world go around. How could Shawnee convince him to go on the DIA’s payroll? First she needed to understand the Mullah’s motivations for providing intelligence. Then, Shawnee needed another five months until she finally figured out how to close the deal.
_
Sexual entrapment as recruitment tool:
One former CIA officer said that while sexual entrapment was not generally a good tool to recruit a foreign official, it was sometimes employed successfully to solve short-term problems. Seduction is a classic technique; “swallow” was the KGB tradecraft term for women, and “raven” the term for men, trained to seduce intelligence targets.
During the Cold War, the KGB (and allied services, including the East German Stasi under Markus Wolf, and the Cuban Intelligence Directorate [formerly known as Dirección General de Inteligencia or DGI]) frequently sought to entrap CIA officers. The KGB believed that Americans were sex-obsessed materialists, and that U.S. spies could easily be entrapped by sexual lures. The best-known incident, however, was of Clayton Lonetree, a Marine guard supervisor at the Moscow embassy, who was seduced by a “swallow” who was a translator at the Embassy of the United States in Moscow. Once the seduction took place, she put him in touch with a KGB handler. The espionage continued after his transfer to Vienna, although he eventually turned himself in.
The Soviets used sex not only for direct recruitment, but as a contingency for a possible future need of kompromat of an American officer. The CIA itself made limited use of sexual recruitment against foreign intelligence services. “Coercive recruitment generally didn’t work. We found that offers of money and freedom worked better”. If the Agency found a Soviet intelligence officer had a girlfriend, they would try to recruit the girlfriend as an access agent. Once the CIA personnel had access to the Soviet officer, they might attempt to double him.
Examples of people trapped by sexual means include:
- Robert Osman, an American soldier stationed in Panama Canal Zone in 1933, was involved in a “honey trap” – Frema Karry, a young Russian girl in Robert Gordon Switz’s network. Osman provided war plans. He was arrested, represented by socialist lawyer Louis Waldman (later lawyer for Walter Krivitsky), and imprisoned for 25 years
- John Vassall, a British embassy official in Moscow, who was guided by the KGB into having sex with multiple male partners while drunk in 1954. The KGB then used photographs of this incident to blackmail Vassall into providing them with secret information.
- Sir Geoffrey Harrison, the British Ambassador to the Soviet Union, was recalled to London in 1968 after he admitted to the Foreign Office that he had been having an affair with a Russian chambermaid at the embassy, of which he had been shown compromising photographs by the KGB.
- Mordechai Vanunu, an Israeli nuclear whistleblower.
- Clayton J. Lonetree, a U.S. Marine Sergeant embassy guard in Moscow, was entrapped by a female Soviet officer in 1987. He was then blackmailed into handing over documents when he was assigned to Vienna. Lonetree was the first U.S. Marine to be convicted of spying against the United States.
- Irvin C. Scarbeck, a U.S. diplomat, was entrapped by a female Polish officer in 1961 and photographed in a compromising position. He was blackmailed into providing secrets.
- Sharon Scranage, a CIA employee described as a “shy, naive, country girl”, was allegedly seduced by Ghanaian intelligence agent Michael Soussoudis. She later gave him information on CIA operations in Ghana, which was later shared with Soviet-bloc countries.
- In 2006, the British Defence Attaché in Islamabad was recalled home when it emerged that he had been involved in a relationship with a Pakistani woman, who was an intelligence agent. While the British Government deny that secrets were lost, other sources say that several Western operatives and operations within Pakistan were compromised.
- In May 2007 a female officer serving in Sweden’s Kosovo force was suspected of having leaked classified information to her Serbian lover who turned out to be a spy.
- Won Jeong-hwa, who was arrested by South Korea in 2008 and charged with spying for North Korea, was accused of using this method to obtain information from an army officer.
______
______
Double agent:
In the field of counterintelligence, a double agent is an employee of a secret intelligence service for one country, whose primary purpose is to spy on a target organization of another country, but who is now spying on their own country’s organization for the target organization.
Double agentry may be practiced by spies of the target organization who infiltrate the controlling organization or may result from the turning (switching sides) of previously loyal agents of the controlling organization by the target. The threat of execution is the most common method of turning a captured agent (working for an intelligence service) into a double agent (working for a foreign intelligence service) or a double agent into a re-doubled agent. It is unlike a defector, who is not considered an agent as agents are in place to function for an intelligence service and defectors are not, but some consider that defectors in place are agents until they have defected.
Double agents are often used to transmit disinformation or to identify other agents as part of counter-espionage operations. They are often very trusted by the controlling organization since the target organization will give them true, but useless or even counterproductive, information to pass along.
Experience suggests that some people who take to the double agent role-perhaps a majority of willing ones, in fact have a number of traits in common with the con-man. Psychiatrists describe such persons as sociopaths.
From the point of view of the double agent operation, here are their key traits:
- They are unusually calm and stable under stress but cannot tolerate routine or boredom.
- They do not form lasting and adult emotional relationships with other people because their attitude toward others is exploitative.
- They have above-average intelligence. They are good verbalizers-sometimes in two or more languages.
- They are sceptical and even cynical about the motives and abilities of others but have exaggerated notions about their own competence.
- Their reliability as agents is largely determined by the extent to which the case officer’s instructions coincide with what they consider their own best interests.
- They are ambitious only in a short range sense: they want much and they want it now. They do not have the patience to plod toward a distant reward.
- They are naturally clandestine and enjoy secrecy and deception for its own sake.
_
Events in which double agents played an important role:
- Babington plot
- Battle of Lexington
- Battle of Normandy
- Camp Chapman attack
- Cold War
- Duquesne Spy Ring
- Gukurahundi
- Stormontgate
- Vietnam War
- War on Terrorism
- Yom Kippur War
_
Re-doubled agent:
A re-doubled agent is an agent who gets caught as a double agent and is forced to mislead the foreign intelligence service. F.M. Begoum describes the re-doubled agent as “one whose duplicity in doubling for another service has been detected by his original sponsor and who has been persuaded to reverse his affections again”.
_
Triple agent:
A triple agent is a spy who pretends to be a double agent for one side while they are truthfully a double agent for the other side. Unlike a re-doubled agent, who changes allegiance due to being compromised, a triple agent usually has always been loyal to their original side. It may also refer to a spy who works for three opposing sides, such that each side thinks the spy works for them alone.
Notable triple agents include:
- Michael Goleniewski
- Abdul Razak Hussein
- Ibrahim Ismail
- Humam Khalil
- Katrina Leung
______
Foreign agent:
A foreign agent is any person or entity actively carrying out the interests of a foreign principal while located in another host country, generally outside the protections offered to those working in their official capacity for a diplomatic mission. Foreign agents may be citizens of the host country. In contemporary English, the term has a generally pejorative connotation, reinforced by its use in the US laws aimed to curb the foreign influence. A covert foreign agent, also known as a secret agent of a foreign government, may in some countries be presumed to be engaging in espionage.
______
Mole:
In espionage jargon, a mole (also called a “penetration agent”, “deep cover agent”, “illegal” or “sleeper agent”) is a long-term spy (espionage agent) who is recruited before having access to secret intelligence, subsequently managing to get into the target organization. However, it is popularly used to mean any long-term clandestine spy or informant within an organization (government or private). In police work, a mole is an undercover law-enforcement agent who joins an organization in order to collect incriminating evidence about its operations and to eventually charge its members.
A mole may be recruited early in life, and take decades to get a job in government service and reach a position of access to secret information before becoming active as a spy. Perhaps the most famous examples of moles were the Cambridge Five, five upper-class British men recruited by the KGB as communist students at Cambridge University in the 1930s who later rose to high levels in various parts of the British government. By contrast, most espionage agents, such as CIA counterintelligence officer Aldrich Ames and FBI agent Robert Hanssen, who spied on the US government for the KGB, were either recruited or offered their services as spies after they were in place as members of the target organization.
Because their recruitment occurred in the remote past, moles are difficult for a nation’s security services to detect. The possibility that a top politician, corporate executive, government minister, or officer in an intelligence service could be a mole working for a foreign government is the worst nightmare of counterintelligence services. Moles have been featured in numerous espionage films, television shows, video games and novels.
Because the spy career of a mole is so long-term, sometimes occupying most of a lifetime, those who become moles must be highly motivated. One common motivation is ideology (political convictions). During the Cold War, a major source of moles in Western countries was so-called fellow travellers, Westerners who, in their youth during the 1920s to 1940s, became disaffected with their own governments and sympathetic to world communism without actually joining a communist party.
_______
Sleeper agent:
A sleeper agent is a spy or operative who is placed in a target country or organization, not to undertake an immediate mission, but instead to act as a potential asset on short notice if activated in the future. Even if not activated, the “sleeper agent” is still an asset and can still play an active role in sabotage, sedition, espionage, or possibly treason by virtue of agreeing to act if activated.
In espionage, a sleeper agent is one who has infiltrated the target country and has “gone to sleep”, sometimes for many years. The agent makes no attempt to communicate with the sponsor or any existing agents or to obtain information beyond what is public, and becomes active only upon receiving a pre-arranged signal or message from the sponsor or a fellow agent.
The agent acquires jobs and identities, ideally ones that will prove useful in the future, and attempts to blend into everyday life as a normal citizen. Counterespionage agencies in the target country cannot, in practice, closely watch all those who may possibly have been recruited some time before.
In a sense, the best sleeper agents are those who do not need to be paid by the sponsor, as they are able to earn enough money to finance themselves, averting any possibly traceable payments from abroad. In such cases, the sleeper agent may be successful enough to become what is sometimes termed an “agent of influence”.
Sleeper agents who have been discovered have often been natives of the target country who moved elsewhere in early life and were co-opted (perhaps for ideological or ethnic reasons) before returning to the target country. That is valuable to the sponsor, as the sleeper’s language and other skills can be those of a native, thus less likely to trigger domestic suspicion.
Choosing and inserting sleeper agents has often been difficult, as whether the target will be appropriate some years in the future is uncertain. If the sponsor government and its policies change after the sleeper has been inserted, the sleeper may be found to have been planted in the wrong target.
Examples:
- Jack Barsky was planted as a sleeper agent in the United States by the Soviet KGB. He was an active sleeper agent between 1978 and 1988. He was located by US authorities in 1994 and then arrested in 1997. Barsky quickly confessed after being arrested and became a useful source of information about spy techniques.
- The Illegals Program was a network of sleeper spies planted in the US by the Russian Foreign Intelligence Service. A multi-year investigation culminated in June 2010 with the filing of charges and the arrest of 10 suspects in the US and another one in Cyprus. The Russian General Directorate for special programs, or GUSP in Russian transliteration (Главное управление специальных программ, ГУСП), still recruits candidates among students and talented scientists to use them as sleeper agents or as legal employees in police and intelligence bodies in Russia.
______
Resident spy:
A resident spy in the world of espionage is an agent operating within a foreign country for extended periods of time. A base of operations within a foreign country with which a resident spy may liaise is known as a “station” in English and a rezidentura (резиденту́ра, ‘residency’) in Russian. What the U.S. would call a “station chief”, the head spy, is known as a rezident (резиде́нт) in Russian.
In the Soviet Union nomenclature, there are two types of resident spies: legal’nye rezidenty (легальные резиденты, legal resident spy) and nelegal’nye rezidenty (нелегальные резиденты, illegal resident spy). In U.S. parlance, the same distinction is between “official cover” and “non-official cover”.
A legal resident spy operates in a foreign country under official cover (such as from their country’s embassy). They are an official member of the consular staff, such as a commercial, cultural, or military attaché. They have diplomatic immunity from prosecution and cannot be arrested by the host country if suspected of espionage. The host country can expel such a person, requiring them to return to their home country as persona non grata.
An illegal resident spy operates under non-official cover. They cannot claim immunity from prosecution when arrested. They may operate under a false name and have documents purportedly establishing them as a national of the country, or from a different country than the one for which they are spying. Examples of two famous Soviet “illegals” are Rudolf Abel, who operated in the United States; and Gordon Lonsdale, who was born in Russia, claimed to be Canadian, and operated in Britain. Other famous Soviet and Russian “illegals” include Richard Sorge, Walter Krivitsky, Vasily Zarubin, Alexander Ulanovsky, and Anna Chapman, who was also known as a sleeper agent.
______
______
Agencies:
An intelligence agency is a government agency responsible for the collection, analysis, and exploitation of information in support of law enforcement, national security, military, public safety, and foreign policy objectives. Means of information gathering are both overt and covert and may include espionage, communication interception, cryptanalysis, cooperation with other institutions, and evaluation of public sources. The assembly and propagation of this information is known as intelligence analysis or intelligence assessment. These organizations use a variety of methods, including human intelligence, open-source intelligence, and signals intelligence, to gather data. Examples of intelligence gathering organizations include government agencies like the CIA, MI6, and MSS, as well as private companies that provide intelligence services to businesses and individuals.
Objectives:
Intelligence agencies can provide the following services for their national governments.
- Give early warning of impending crisis;
- Serve national and international crisis management by helping to discern the intentions of current or potential opponents;
- Inform national defense planning and military operations, known as military intelligence;
- Protect sensitive information secrets, both of their own sources and activities, and those of other state agencies;
- Covertly influence the outcome of events in favor of national interests, or influence international security; and
- Defense against the efforts of other national intelligence agencies, known as counterintelligence.
There is a distinction between “security intelligence” and “foreign intelligence”. Security intelligence pertains to domestic threats, including terrorism and espionage. Foreign intelligence involves information collection relating to the political, or economic activities of foreign states.
Some agencies have been involved in assassination, arms trafficking, coups d’état, and the placement of misinformation propaganda and other covert and clandestine operations to support their own or their governments’ interests.
_____
Types of Intelligence Gathering Organizations:
- Government Agencies:
These agencies are responsible for collecting intelligence to protect national security and foreign policy interests. Examples include the CIA (United States), MI6 (United Kingdom), and MSS (China).
- Law Enforcement Agencies:
Law enforcement agencies use intelligence gathering to combat crime and terrorism. Examples include the FBI (United States) and various national police forces.
- Military Intelligence:
Military intelligence agencies collect information to support military operations and defense planning. Examples include the Defense Intelligence Agency (DIA, United States).
- Private Intelligence Agencies:
These companies provide intelligence services to businesses and individuals, often focusing on security, risk assessment, and business intelligence.
- Counterintelligence:
Counterintelligence agencies are responsible for protecting their own country’s intelligence assets and preventing espionage.
______
______
Top Intelligence Agencies in the World:
Intelligence agencies form the backbone of national security systems worldwide, operating in the shadows to protect their nations’ interests. These organizations gather critical information, conduct covert operations, and serve as the first line of defense against threats both foreign and domestic. Their work has shaped history, determined the outcomes of wars, and influenced global politics in profound ways.
_
-1. Central Intelligence Agency (CIA)
Country: United States of America
Founded: 1947
Headquarters: Langley, Virginia
The CIA stands as the foremost intelligence agency globally, responsible for gathering and analyzing national security information from around the world. What sets the CIA apart is its extensive use of human intelligence (HUMINT) networks and advanced technological capabilities.
The agency maintains its own training university where recruits learn specialized skills, including methods to defeat polygraph tests. Their recruitment process is highly selective, sometimes identifying potential agents as early as high school.
Citizens who work for the CIA are officers — not agents or spies. All employees, from case officers, to analysts, to librarians and public affairs, are considered CIA officers.
CIA case officers recruit well-placed human assets with access to information. These spies are agents. They provide critical information about their country to help America. Case officers are CIA employees who spot, recruit, and handle foreign agents. They are experts in understanding human nature, emotions, intentions, and motivations. Foreign agents/spies are invaluable. The information they provide plays a critical role in developing and implementing US foreign and national security policy. Spies risk imprisonment, the loss of their job, reputation, or family and friends. Some are even at risk of execution if caught.
Notable Operations:
- Assassination of Osama bin Laden
- Extensive Cold War operations against the Soviet Union
- Intelligence operations during the Iraq and Afghanistan conflicts
- Recent involvement in the Syrian civil war
_
The public often confuses the Federal Bureau of Investigation’s (FBI) responsibilities with that of the CIA. The two agencies work closely together, but their roles in keeping America safe are very different. The CIA is not a law enforcement agency. The CIA’s responsibility is to collect intelligence and information overseas. When conducting mission overseas, CIA take steps to safeguard any information on Americans that could be incidentally collected. The FBI is the government agency that investigates crimes on American soil and against American citizens abroad. The FBI is also responsible for intelligence matters in the United States, especially those directed against US citizens. The vast majority of CIA officers do not carry weapons. Aside from officers in the Security Protective Service, or those serving in war zones, most CIA officers will never be issued a gun. FBI agents are authorized to carry firearms and typically do so while on duty.
_
-2. Secret Intelligence Service (MI6)
Country: United Kingdom
Founded: 1909
Headquarters: London, UK
Commonly known as MI6, the Secret Intelligence Service specializes in foreign espionage and counter-intelligence activities. Working alongside domestic counterparts like MI5 and GCHQ, MI6 has established itself as one of the most sophisticated intelligence operations in the world.
The agency’s long history has given it unparalleled experience and global reach, making it a crucial ally to many Western nations’ intelligence efforts.
Notable Operations:
- Critical intelligence gathering during World Wars I and II
- The breaking of the Enigma code, which helped turn the tide of WWII
- Extensive Cold War operations against the USSR
- Intelligence support during the 1991 August coup in the Soviet Union
- Operations during the Libyan civil war
_
-3. Federal Security Service (FSB)
Country: Russia
Founded: 1995
Headquarters: Moscow, Russia
In Russian, FSB is an acronym for Федеральная служба безопасности (Federal’naya sluzhba bezopasnosti), which translates to Federal Security Service in English. It’s the main domestic security agency of Russia and a successor to the Soviet-era KGB. As the main successor to the infamous KGB, Russia’s FSB has maintained its predecessor’s reputation while modernizing its approach. Under Putin’s government, the agency underwent significant reforms that refined its operational focus and structure.
The FSB primarily handles internal security matters, counter-intelligence, border security, and counter-terrorism within Russian territory. Its organizational structure includes specialized divisions for counter-espionage, constitutional defense, economic security, and border protection.
Notable Operations:
- Cold War intelligence operations (as the KGB)
- Security operations during the 1991 coup
- Involvement in the Lebanon crisis
- Intelligence gathering during the Syrian war
_
-4. Research and Analysis Wing (RAW)
Country: India
Founded: 1968
Headquarters: New Delhi, India
India’s RAW was established following intelligence failures during the Sino-Indian and Indo-Pakistani wars, creating a specialized agency dedicated solely to foreign intelligence gathering. Despite being relatively young compared to other agencies on this list, RAW has quickly established itself as one of the most effective intelligence organizations globally.
The agency recruits from civil services, the Indian Police Service, and armed forces, with training facilities complemented by field training from the Indian Army at the Indian Military Academy.
Notable Operations:
- Intelligence support leading to the creation of Bangladesh
- Operation Smiling Buddha (India’s first nuclear test)
- Operation Meghdoot
- Intelligence gathering during the Kargil War
- Covert operations in Balochistan
_
-5. Mossad
Country: Israel
Founded: 1949
Headquarters: Tel Aviv, Israel
Notable operations: From pager bombs to silent kills:
Formed in 1949, Israel’s national intelligence agency, Mossad, is one of the most secretive and formidable espionage organisations in the world. Operating well beyond Israel’s borders, Mossad is responsible for gathering foreign intelligence, conducting counterterrorism operations, and executing covert missions that influence global geopolitics.
Short for HaMossad leModiʿin uleTafkidim Meyuḥadim—“Institute for Intelligence and Special Operations”—the agency reports directly to the Israeli Prime Minister and functions independently from the country’s military apparatus. Over the decades, it has developed a reputation built on stealth, precision, and ruthlessness.
Mossad is known for its unconventional tactics: psychological manipulation, forged identities, honey traps, and deep-cover infiltration. Its global network of sayanim (voluntary Jewish helpers abroad) supports operatives who often work under non-official cover, making them nearly impossible to detect. Agents are extensively trained in surveillance, multiple languages, cyberwarfare, and close combat, blending classic tradecraft with modern technology.
From capturing Nazi fugitives in South America to launching cyberattacks inside Iranian nuclear facilities, Mossad’s missions often read like high-octane thrillers. It has been praised for its effectiveness and criticised for its secrecy and collateral damage. Whether through exploding walkie-talkies, doctored toothpaste, or remote hacks, Mossad’s tactics continue to evolve in a world of hybrid warfare.
Israel carried out a surprise attack on Iran recently, targeting high-level military and nuclear assets with extraordinary precision. Using a combination of human intelligence and advanced AI, Israeli forces smuggled drones and launched airstrikes that crippled Iran’s air defenses and eliminated key generals and scientists. While Israeli officials remained largely silent, former Mossad research chief Sima Shine confirmed the operation’s strategic depth, reinforcing its roots in long-term covert planning. Mossad’s reputation for executing daring, complex missions with strategic precision has earned it global recognition. Popular culture has further mythologised its operations, with films like ‘Munich’ and ‘The Angel’ portraying its storied past.
_
-6. Federal Intelligence Service (BND)
Country: Germany
Founded: 1956
Headquarters: Berlin, Germany
Germany’s Bundesnachrichtendienst (BND) serves as the country’s foreign intelligence agency, reporting directly to the Chancellor’s Office. The BND functions as an early warning system for threats to German interests abroad, relying heavily on electronic surveillance and wiretapping of international communications.
The agency’s responsibilities span areas including terrorism, weapons proliferation, organized crime, drug trafficking, money laundering, and information warfare.
Notable Operations:
- Intelligence gathering during the Munich Olympics incident
- Support during the Libyan bombings
- Intelligence operations during the Iraq invasion
- Kosovo war intelligence collection
_
-7. Ministry of State Security (MSS)
Country: China
Founded: 1983
Headquarters: Beijing, China
China’s Ministry of State Security handles both counterintelligence and foreign intelligence operations, functioning as the primary security and intelligence organization of the People’s Republic of China. The MSS operates with extreme secrecy, often infiltrating other nations to advance Chinese interests.
The agency has been compared to the former Soviet KGB in terms of its reach and methodologies. Its operations typically focus on political security and intelligence gathering that supports China’s strategic goals.
Notable Operations:
- Intelligence operations during the Korean War
- Operations related to Taiwan
- Extensive Cold War intelligence gathering
_
-8. Inter-Services Intelligence (ISI)
Country: Pakistan
Founded: 1948
Headquarters: Islamabad, Pakistan
Pakistan’s ISI is the largest of the country’s three intelligence services and primarily operates as a military intelligence agency. The ISI has earned recognition for its effectiveness in regional operations and has even been utilized by Western countries for intelligence on Taliban and other terrorist networks.
The agency recruits exclusively from Pakistan’s armed forces and maintains specialized divisions for covert action, counterintelligence, and political intelligence. Inter-Service Intelligence [ISI] plays an ambiguous role in the War on Terrorism. An important ally for Western intelligence with whom it has very close links, the ISI also has a long history of involvement in supporting and promoting terrorism in the name of Pakistan’s geostrategic interests. The ISI, has often been accused of playing a role in major terrorist attacks across India. The ISI is also accused of supporting Taliban forces and recruiting and training mujahideen to fight in Afghanistan and Kashmir.
Notable Operations:
- Extensive involvement in the Soviet-Afghan War
- Operations during the Indo-Pakistan War of 1971
- Intelligence activities during the 2001 Afghanistan War
- Support during the Kargil War
_
-9. Australian Secret Intelligence Service (ASIS)
Country: Australia
Founded: 1952
Headquarters: Canberra, Australia
Australia’s foreign intelligence agency focuses on overseas intelligence collection, counterintelligence, and coordination with partner intelligence agencies. Comparable to Britain’s MI6 and America’s CIA, ASIS plays a crucial role in maintaining Australia’s national security.
The agency’s operations and structure remain largely classified, but it serves as a key intelligence partner in the Five Eyes alliance (alongside the US, UK, Canada, and New Zealand).
_
-10. Directorate-General for External Security (DGSE)
Country: France
Founded: 1982
Headquarters: Paris, France
France’s DGSE functions as the nation’s external intelligence agency, operating under the direction of the French Ministry of Defense. Working alongside its domestic counterpart, the DGSI, the DGSE focuses on providing intelligence and conducting paramilitary and counterintelligence operations abroad.
The agency maintains specialized divisions for administration, strategy, intelligence gathering, and operations, including the Action Division responsible for clandestine activities.
Notable Operations:
- Intelligence gathering during the Soviet-Afghan War
- Operation Satanic
- Infiltration of al-Qaeda networks
_
Throughout history, these intelligence agencies have proven instrumental in shaping global events and safeguarding their respective nations. Their sophisticated operations, technological capabilities, and human intelligence networks continue to evolve, adapting to new threats in an increasingly complex world. While much of their work remains classified, their impact on international relations and national security is undeniable.
______
______
Section-8
Spycraft (spy tactics):
Spycraft refers to the skills, techniques, and methods used by spies and intelligence operatives. It encompasses a wide range of activities, from surveillance and covert communication to deception and infiltration, all aimed at gathering secret information or carrying out clandestine operations.
Spy Tactics can be defined as a set of strategic methods and techniques used by covert agents to gather intelligence, conduct surveillance, and carry out clandestine operations. These tactics involve a combination of skills, knowledge, and specialized tools to navigate complex situations and obtain critical information.
The origins of secret agent spy tactics can be traced back to ancient times when spies were used as a means of gaining an advantage in conflicts and securing sensitive information. Throughout history, various civilizations have employed espionage as a tool to gather intelligence and stay one step ahead of their adversaries.
Spy tactics play a crucial role in national security as they provide vital information about potential threats, enemy activities, and emerging geopolitical developments. By employing these tactics, intelligence agencies and covert operatives can assess risks, prevent attacks, and protect the interests of their respective nations.
While spy tactics may seem complex and mysterious, they can be broken down into more understandable terms. At its core, spy tactics involve skills such as disguise, source cultivation, secret communication, physical training, observation, analysis, counterintelligence, operational security, and technical proficiency. These skills collectively enable spies to blend into their surroundings, gather valuable intelligence, and carry out missions undetected.
_
Here are some Spy Techniques from History:
Imagine you have to send an important message to someone, but it absolutely cannot fall into the wrong hands. We’re talking top-secret, classified information. How would you make sure that only the right person reads it? Throughout history, people have come up with all sorts of inventive solutions to this conundrum.
-1. Hairy Situation
An ancient Greek ruler named Histiaeus had a unique method of keeping his messages secret. He shaved the head of a messenger, tattooed the message onto his scalp, and waited for his hair to grow back before sending him to the message’s intended recipient. There, the messenger would shave his head again to reveal the secret. No word on how the messenger got back home without everyone else seeing the secret message. Maybe he wore a hat.
-2. Eggshell Strategy
Elizabeth Van Lew was one of the most successful Union spies during the American Civil War. Like many other female spies, her strategy relied on being underestimated. If a local man kept visiting Union soldiers in prison, other people in Richmond would probably get suspicious. After all, Richmond was the heart of the Confederacy. But how could they stop a young woman from charitably supplying the Union soldiers with baskets of food and clothing and other supplies while in prison? In fact, the baskets of food were part of her secret spy method. She was known to smuggle hollow egg shells concealing messages in baskets of eggs. And that was only one of her tricks!
-3. Petticoats
During the American Revolution, a band of spies called the Culper Ring found inventive ways to communicate messages. Anna Strong’s method was the most creative of all– communicating via her laundry! When she hung out her laundry to dry on a clothesline, another spy watched with a telescope from across the bay. A black petticoat meant fellow spy Caleb Brewster was in town. The order of the rest of the laundry determined where they would meet that night.
-4. Ink on eggshell
It’s easy to think of invisible ink as a modern invention, but Renaissance-era scientist Giovanni della Porta combined invisible ink and hard-boiled eggs to send a truly unique form of secret message. He would write on the egg’s shells with invisible ink. Eggshells are porous enough to let ink leach through to the eggs underneath. Just peel the egg to read the secret message! The exact recipe and method is a little tricky to track down, and few have been able to replicate della Porta’s success.
-5. Knitting
Knitting has been used as a way to record or pass on coded messages throughout history and literature. In the Belgian Resistance during World War II, women who lived near railway yards would record the comings and goings of trains through their stitches, sometimes intentionally dropping a stitch to create a hole. An elderly woman colorfully called Molly “Old Mom” Rinker dropped messages hidden in yarn balls to soldiers during the Revolutionary War from her favorite knitting spot high atop a rock.
The most famous knitting spy was Phyllis Latour, a World War I era spy. She’d knit secret messages onto pieces of silk, which she could conceal in her hair tie. Latour walked around with secret messages in her hair! Although she was caught and examined by an enemy officer, they never thought to check the hair tie!
-6. Caesar’s Cipher!
Coded messages have always been one of the most important ways for spies to communicate. One of the most famous leaders in history used a code that was so simple, a child could learn it– but to the untrained eye, it’s just gibberish. The famous Caesar cipher consists of shifting every letter in a message down several places– for example, 3 letters. So
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z would become
D E F G H I J K L M N O P Q R S T U V W X Y Z A B C
_____
Espionage techniques encompass a wide range of methods used to gather information secretly. These include covert surveillance, eavesdropping, and the use of various technologies and strategies like steganography, dead drops, and cyber espionage. Deception and psychological manipulation are also employed, such as false flag operations and honey trapping.
Traditional Espionage Techniques:
- Surveillance:
Involves covertly observing individuals, locations, or activities to gather information.
- Disguise:
Spies often change appearance to throw off agents who may be watching them. Wigs, hats, false beards and moustaches are common tools.
- Eavesdropping:
Listening in on private conversations or using concealed listening devices to overhear confidential discussions. Modern surveillance technology allows agents to eavesdrop from a distance. Laser microphones pick up sound vibrations from objects, such as a picture frame inside a room, without entering the target’s space. The beam translates these vibrations into audio signals, providing insight into private conversations.
- Foldering:
Foldering is a clandestine way of electronically communicating. It involves communicating via messages saved to the “drafts” folder of an email or other messaging account that is accessible by multiple people. The messages are never actually sent, it’s a digital equivalent of a dead drop.
- Secret Writing:
Utilizing techniques like invisible ink or microdots to convey messages secretly.
- Dead Drops:
Establishing hidden locations to exchange information or objects without direct contact. In traditional espionage, a dead drop refers to a method of passing information which doesn’t require the two parties to ever meet, communicating only through secret locations.
Figure above shows hidden letter that Aldrich Ames left at a dead drop for his KGB contact.
CIA official Aldrich Ames began spying for the Soviets in the 1980s for a variety of reasons, but mainly because he was heavily in debt and needed money. Ames was a walk-in — he came up with a plan to sell the names of Soviets who were working for the CIA, and went to the Soviet embassy in New York City to do it. He reportedly demanded $50,000, and continued to spy for money for several years. At least three people were executed by the USSR as a result of Ames’ spying.
- False Flag Operations:
Deceptive actions designed to appear as though they were carried out by an opposing group. The term ‘false flag operations’ has its roots in naval warfare, wherein enemy ships would purposefully fly the flag of a friendly nation to trick a fleet into peacefully letting them on-board, and then… well, you know how war works. It has since come to define any espionage operation that seeks to meet a specific strategic objective by putting the blame on someone other than the party carrying it out.
- Chicken Feed:
Chicken feed refers to a technique used to gain the trust of a target by sharing small but seemingly valuable pieces of information. This builds credibility, but crucial information remains concealed. The leaked information is truthful but not harmful, helping establish a bond that could lead to deeper exchanges.
- Canary Traps:
Using decoys to test the security of a target or to expose potential spies. When you have a lot of suspected spies around you, it becomes difficult to catch all of them. A relatively foolproof technique that has worked against that through the ages has now come to be known as a canary trap. Basically, just give different false pieces of information to each of the suspected spies and see which one gets leaked.
- Double Agents:
Individuals who are secretly working for one side while appearing to be on the other side.
- Steganography:
Hiding messages within other media, like images or audio, to conceal their presence. Steganography refers to the umbrella craft of hiding information in a publicly accessible place.
- Biographic Leverage:
Exploiting a person’s personal relationships or background to gain information.
- Agent Provocateur:
A person who incites others to take action, often for malicious or deceptive purposes.
- Honey Trapping:
Enticing individuals to reveal confidential information by using seductive or manipulative tactics. Honey trapping involves seducing a target to extract valuable information. The target may be distracted or directly manipulated into providing sensitive data. This tactic has been employed effectively, although it is not sustainable for long-term operations.
- Disinformation Campaigns:
Spreading false or misleading information to deceive or undermine an opponent.
- Clandestine Cell Systems:
To prevent espionage organizations from being easily dismantled, agents often operate in small, compartmentalized cells, with members knowing little about their counterparts. This system ensures that if one member is caught, the larger network remains intact.
- Concealed weapons:
Espionage is, naturally, a dangerous business, and if spies get caught in the act, they can face interrogation and torture, followed by decades in prison, or even execution. So evading capture, even by the most extreme means imaginable, was something they needed to be equipped for. During the Cold War period, spies were equipped with all manner of secret weapons, including tiny pistols hidden in items such as torches, gloves, lipsticks, and pipes. Often the pistols could only fire one shot, so they needed a steady hand and a lot of luck. If they failed to shoot their way out, their final recourse was to take a suicide pill. Again, these needed to be hidden, as being found with such a pill would have been highly incriminating, and because they formed a vital, if harrowing, last resort. Cyanide capsules were hidden in the arms of glasses that the wearer could casually chew on, releasing the poison, or the collars of shirts, so they could be quickly retrieved and taken before the enemy realised.
_
Modern Espionage Techniques (Cyber Espionage):
- Phishing Attacks: Using deceptive emails or websites to trick individuals into revealing login credentials or other sensitive information.
- Malware and Spyware: Installing malicious software to track keystrokes, monitor browsing habits, or steal data.
- Advanced Persistent Threats (APTs): Long-term, stealthy cyberattacks that can remain undetected for extended periods.
- Hacking: Gaining unauthorized access to computer systems and networks.
_
Other Techniques:
- Cutouts: Third parties used to transmit messages or information to avoid direct contact between the sender and receiver. Cutouts act as intermediaries between spies, relaying information without revealing identities. They know only the source and destination of the intelligence but remain unaware of any other details, minimizing risk in case they are compromised.
- Number Stations: Radio broadcasts used to communicate coded messages.
- One-Time Pad: A secure encryption method using a unique key for each message.
- Agent Handling: The management and support of spies or agents.
- Elicitation: Subtly drawing out information from individuals through conversation and observation
_______
_______
Corporate Espionage Spy Techniques:
-1. Social engineering: Spies may use techniques to manipulate people into providing sensitive information or access to systems, such as phishing emails, pretexting, or impersonation.
-2. Physical access: Spies may try to gain physical access to a company’s premises to gather information through means such as tailgating, stealing badges, or planting listening devices.
-3. Dumpster diving: Spies may rummage through a company’s trash to find confidential information such as documents, reports, or electronic devices.
-4. Hacking: Spies may attempt to breach a company’s computer systems or networks to access sensitive data.
-5. Shoulder surfing: Spies may watch over the shoulder of an employee while they work on their computer or mobile device to observe confidential information.
-6. Wiretapping: Spies may intercept telephone conversations, voicemail messages, or other electronic communications to gather information.
-7. Covert surveillance: Spies may use cameras, bugs, or other surveillance techniques to monitor company activities or personnel.
-8. Blackmail: Spies may use threats or coercion to force employees to provide access to confidential information.
-9. Insider threats: Spies may target employees who have access to sensitive information and attempt to bribe or recruit them to share confidential information.
-10. Social media: Spies may use social media platforms to gather information about a company’s employees, operations, or business partners.
-11. Business travel: Spies may try to gather information by monitoring company travel itineraries, booking hotels near the target company, or impersonating business partners.
-12. Impersonation: Spies may impersonate a company employee or representative to gain access to sensitive information or assets.
-13. Third-party vendors: Spies may target third-party vendors who have access to a company’s systems or data.
-14. Physical surveillance: Spies may use physical surveillance techniques to gather information, such as following employees, observing meetings, or taking photos or videos.
-15. False job applications: Spies may submit false job applications to a company to gain access to sensitive information or to network with employees.
-16. Social events: Spies may attend company social events or conferences to gather information about employees or business partners.
-17. Eavesdropping: Spies may listen in on conversations between employees or business partners to gather information.
-18. Supply chain attacks: Spies may target a company’s suppliers or vendors to gain access to sensitive information or to introduce malware into a company’s systems.
-19. Remote access: Spies may attempt to gain remote access to a company’s systems or data through methods such as phishing or malware.
-20. Physical theft: Spies may steal physical assets such as laptops, mobile devices, or hard drives that contain sensitive information.
______
______
How spy works:
Methods of acquiring information are as varied as the information as itself. The most important element of a long term spying operation is the use of a cover and the creation of a legend. A cover is a secret identity, and a legend is the background story and documents that support the cover.
For example, a British agent whose cover identity is a Russian accountant would need to speak Russian and know a great deal about Russian financial laws. To make the cover seem more realistic, the legend must be very thorough. The agent will have a fake life history that he must memorize. Where did he go to school? Does he have a diploma to prove it? Where was he born? Who is his ex-wife? What are his hobbies? If the legend states that the agent enjoys fishing, he’d better have some fishing gear in his house. The failure or success of spies can hinge on such seemingly minor details.
Once the spy establishes a cover, he might spend years doing his job and establishing trust. Eventually, the spy will try to gain promotions or transfers to a position with access to vital information, or befriend someone with such access.
_
It is possible for a spy to memorize information and pass it on to his controller. However, it is much more reliable to photocopy papers and maps, often transferring the data to a tiny slip of microfilm or a microdot. Stealing original documents could blow the spy’s cover, so a wide assortment of miniature cameras hidden in innocuous objects are used.
There are numerous technological ways for countries to spy on each other without ever sending an actual spy to collect information. Satellites equipped with cameras have been tracking the positions of military units since the 1960s. At first, the satellite would drop a bucket with the film inside over the ocean. In 1970, digital film technology was first developed, allowing the satellites to transmit the photographic data by radio. Today’s spy satellites can take photographs with a high enough resolution to read the headline on a newspaper.
It was more difficult to get that kind of accuracy in the ’60s and ’70s — spy planes such as the U-2 had to fly directly over enemy territory, exposing the pilot to the risk of being shot down, and the spying nation to the risk of international embarrassment.
Other forms of Tech Int, or technological intelligence, include super-sensitive microphones, phone wire taps, seismic equipment to detect nuclear testing and underwater sensors to find enemy submarines. Spies also scan, record and analyze enemy radio frequencies and cell-phone traffic.
_
When secret information is passed to the spy’s controllers, it must be hidden so that the enemy doesn’t suspect anything. This could ruin the spy’s cover, or lead the enemy to deliberately supply misinformation. Until the early 20th century, spies resorted to invisible inks to hide messages between the lines or on the back of non-suspicious correspondence. Sugar solutions or lemon juice are invisible until heated. Other chemicals don’t appear until the paper is painted with a specific reagent.
One time-tested method for relaying information is the dead drop. A dead drop is a secret hiding place somewhere in public. It could be behind a loose brick in a wall at the city park, or in a plant at a certain street corner. When a spy has a message to send, he goes about his business, perhaps picking up some dry cleaning or seeing a movie. He passes by the dead drop and deposits the message casually, without arousing suspicion. The spy then has to leave a signal to let his handlers know there is a message to be retrieved. A chalk mark on a lamppost, a certain color of sheet on a clothes lines or even a cryptic message in the classified section of a newspaper are all possible signals. A spy may use several dead drops so he isn’t noticed repeatedly visiting the same loose brick.
_
Spy controllers can use one-way communication to issue instructions to spies. The mysterious numbers stations in operation around the world are almost certainly used for this purpose. A numbers station is a government operated radio station broadcasting intermittently on the short-band frequencies. A certain song or announcement will mark the beginning and end of each broadcast, which consists solely of a voice, possibly altered electronically, reciting a long series of numbers. The numbers are coded messages deciphered by the intended recipient using a virtually unbreakable cipher known as a one-time pad.
A great deal of espionage revolves around secret codes. Information transmitted between spies and controllers is usually coded, and a large proportion of government and military communications are encoded, particularly during wars. Many spy missions have the sole purpose of acquiring the keys needed to solve these codes, or obtaining the devices used to encode and decode messages.
_
The acquisition and transmission of secret information is meaningless if the information isn’t properly analyzed and acted upon. Russian leader Joseph Stalin was provided with information from several agents that Germany was going to break the German-Russian alliance and attack Russia during World War II, but he refused to believe it. Russian forces were not properly aligned or prepared when the German attack came.
Data analysts take information from numerous sources, not just spies, and develop an overall picture of enemy strategies and policies. This information is then written into briefings for political leaders. While information from a single source may be untrustworthy, additional sources can be used to corroborate the data. For example, U.S. code breakers had partially cracked the Japanese Purple code during World War II, and they were fairly certain that Japan was planning an attack at Midway Island. They weren’t completely sure if they were reading Japan’s code word for the island (AF) correctly, however, so they had troops positioned at Midway to issue a radio alert saying they were running short on fresh water. Shortly, Japanese communications were intercepted that reported that AF was low on fresh water, confirming the target of the coming attack.
_
Secret Codes During WWII:
During World War II, the German military used a device known as an Enigma machine to send coded messages. The machine functioned somewhat like a typewriter with a maze of complicated mechanical and electronic connections. Any message typed into the machine would be transposed into a code; another Enigma with the identical set-up of wires and rotors could reverse the code and reveal the original message.
Polish code breakers had cracked the Enigma code and built duplicate Enigma machines before World War II. They shared their knowledge with the British, who used it, along with several captured Enigmas, to decipher an enormous volume of coded Nazi messages, some from Hitler himself. This information, codenamed ULTRA, was kept under tight wraps so that the Germans would not suspect that their messages were being read.
_
Misinformation:
Spies spend as much time feeding false information to their enemies as they do gathering information. This keeps them guessing, forces them to miscalculate military capabilities and commit forces to the wrong area. A steady stream of misinformation can even damage the real information the enemy has, because they will begin to doubt the authenticity of their own intelligence gathering activities.
One method of spreading misinformation is the double agent. Imagine that a U.S. scientist is recruited by the Russians to supply American military technology. The United States becomes aware that this scientist is spying for the Russians. Instead of arresting him, they allow him to continue feeding information to the Russians. However, they make sure that the blueprints, technical readouts and other data he has access to are altered. The Russians are now getting technical information that is useless. They might spend millions of dollars on research into flawed technology. Thus, the scientist is an unwitting double agent.
Alternately, the United States could confront the scientist and threaten him with a long prison sentence (or even the death sentence, the penalty for treason). To avoid this, he agrees to intentionally turn double agent. Not only does he knowingly supply the Russians with false information, but he works to gain information from his Russian controller. He might provide the United States with the names of other Russian spies, or intelligence on the level of Russian scientific research.
There is always the potential for this same scientist/spy to turn triple agent. That is, he informs the Russians that the Americans caught him. Now, the Russians know to disregard the technical information that he provides, and in turn, they supply misinformation back to the Americans. If it seems confusing, imagine trying to keep it all straight when a mistake could cost you your life. Some agents have even gone beyond triple agent, playing the two sides against one another and creating such a tangled web that historians have no idea whose side the spy was really on.
_
Operation Fortitude was one of the grandest and most successful misinformation campaigns ever conducted. The goal of Fortitude was to fool the Germans into withholding their strongest military units or putting them in the wrong place when the Allies invaded Normandy in 1944. Wooden and cardboard airplanes, fake fuel depots and even dummy troops were massed in southern England to make the Germans think the attack would come from there, rather than at Normandy in the north. A completely fictional U.S. Army group was created: FUSAG (First U.S. Army Group), which even had General George Patton leading it. False radio traffic supplemented the deception. The most important element, however, was the misinformation provided to the Germans by double agents. Information supplied by a double agent code-named Garbo convinced Hitler that the attack would come from the south. To keep up the pretence and delay the arrival of German reinforcements in Normandy as long as possible, the day of the invasion even featured a fake landing force with loudspeakers playing the sounds of a giant fleet moving across the English Channel, with radar-reflecting balloons and metal strips dropped by planes creating the radar signature of a large invasion. Once the attack at Normandy was underway, Garbo told his German handlers that it was just a feint meant to draw German troops away from the “real” attack to the south.
_
Real spies are nothing like James Bond. Bond spent his time seducing and assassinating while real spies spend their time recruiting moles and gathering intelligence information. Real spies rarely pick up a gun, let alone kill other spies. One agent told the Los Angeles Times, “Your James Bond wouldn’t do for us at all because we don’t think he’d be any good at writing. All he’s good at is running around, leaping into cars and shooting from cars. He’s more like a superior policeman…but he would be a hopeless intelligence agent…Our kind of spy has to have higher education, be a beautiful writer, be well-read understand that you have to use both official and other sources to cover the country properly.” Some of the gadgets devised by James Bond movies like the dart-firing cigarettes and poison-tipped umbrellas, were reportedly studied by the KGB as potential weapons. A poison-tipped umbrellas was used to kill Bulgarian defector and writer Georgi Markov in London in 1978.
_______
_______
Spy Technology:
Concealment devices are clever items used to get materials across borders. Over the years these have included hollowed out glass eyes; a plastics dish that opens with a hidden switch triggered with a magnet; and a candlestick that is opened by applying an electric charge to a special spot in the base. Other devises have included tire spikes, igniters used for detonating explosives concealed in fountain pens, rectal concealment containers shaped like a cigarette lighter, lenses used for viewing microdots, lock-picking devices and shoe transmitters.
The CIA developed a realistic robot catfish named “Charlie” in 2000. The CIA would not reveal its mission but it is believed to be to used to collect water samples near nuclear plants. The fish was outfit with a pectoral fin that was larger than normal so it wouldn’t be eaten by predators.
The CIA developed a remote-controlled dragonfly that was developed to plant listening devises outside of windows. Powered by a small engine built by a watchmaker, it proved to be unreliable because it couldn’t fly straight in winds.
The latest spy technology includes advanced surveillance tools like high-resolution cameras, powerful GPS trackers, and sophisticated listening devices. These gadgets are increasingly integrated with features like AI for facial recognition, remote monitoring capabilities, and miniaturization for discreet placement. Furthermore, there’s a growing trend towards combining multiple functionalities into single devices, such as power bank GPS trackers with anti-theft alarms.
_
Spy Cameras:
Spy cameras have been developed that are small enough to fit in buttons and long enough to pear through walls. Ones that could be concealed in a person’s body—a vest camera with a lens in a buttonhole— were used as early 1885. In World War I, cameras were mounted on carrier pigeons. The CIA used cameras strapped to pigeons into the 1970s.
Spy cameras have been placed in cigarette lighters, walking sticks, matchboxes, cigarette boxes, eyeglass cases, cigarette packs, opera glasses, cravat pins, books, pocket watches, cloths hooks, black lace garters and fountain pens. The KGB developed a spy camera with a lens inside of a ring. A key-chain camera was capable of taking 44 photographs.
The first microdots (photographed documents reduced to the size of less than a millimeter) were used in 1852. They are produced by special cameras that take the pictures and were particularly popular in World War II. They were small and contained lots of information and could be hidden almost anywhere, even on the inside of an individual’s teeth.
_
In recent years, camera-enabled devices (surveillance camera, baby monitor, IP camera, etc.) have been widely deployed to facilitate a variety of protection functions ranging from personal security to public safety. For user convenience, most of these devices provide capabilities of streaming live videos from the camera to the cloud via wireless networks. On the other hand, there have been increasing incidents of streaming live videos of individuals’ activities in sensitive spaces like living rooms and hotels via wireless spy cameras that are easy to deploy (without requiring additional wiring) and provide Internet connection through pervasively available Wi-Fi access points (APs). These have created a serious privacy threat and become a social problem.
_
Spy Listening Devises:
Sophisticated listening devices were places in ashtrays, globes and phones. In 1945, the U.S. Ambassador in Moscow was given a gift: a seal of the United States outfit with an ingenious listening device that required no batteries or wires. The device, a half-dollar-size passive cavity resonator acted like an ear, allowing conversations in the room to be heard by bouncing radio waves off the resonator’s antenna, a brass rod imbedded behind the bald eagle on the seal. The device wasn’t discovered for seven years and American scientists couldn’t figure out how it worked.
The Soviets learned how to listen to conversations within a room by reflecting infrared waves off glass windows at precise points. They were able to listen to voices that caused slight vibrations on the windowpanes. The Soviets also attached vibro-acoustic sensors to iron bars embedded in reinforced concrete used in the load-bearing columns of buildings. The sensors in the columns acted like giant omnidirectional microphones. The Russians used the technology in the new American Embassy in Moscow.
A typical bug has a listening device and transmitter and wire that serves as an antenna. Over time listening devise and transmitter have gotten smaller and smaller. In the 1940s they were about the size small film canister. By the 1980s they were size of M&M. Modern ones are comprised of a millimeter square microchip with a two-inch attached wire.
The KGB outfit shoes with a transmitter, microphone and battery in the heel that was used to listen to diplomats. The shoes could be worn or activated by a valet or maid who would pull a tiny pin. The CIA developed listening devices placed by a submarine on a Soviet telephone cable. Sometimes agents climbed into overhead ducts to listen to conversations.
_
Spy Weapons:
The CIA developed a “High Standard” pistol that was so quiet that legendary CIA founder William “Wild Bill” Donovan fired off 10 rounds into a bag of sand in the Oval Office of the White House while U.S. President Franklin Roosevelt was on the phone without the President realizing anything had happened.
Single-shot pistols were disguised as lipstick case or pens. Describing their purpose, one former CIA agent told Reuters, “If you were captured, it would allow you to sneak up on a sentry and use that one round to kill the sentry and get the sentry’s weapon and that way you could fight your way out.”
U.S. Naval Intelligence developed a glove pistol that fired when the wearer punched somebody. “Liberator pistols (guns dropped to resistance fighters in World War I) were mass produced at a cost of $1.72 a piece.
Describing what he had been taught about violence in the KGB, Russian President Vladimir Putin said: “There is no need to meddle into anything without extreme necessity, but as it happened, you must proceed from the assumption that there is no way back, and must fight until the end.” “Another simple rule they taught me in the KGB was that you don’t pull your weapon unless you are ready to use it. Don’t try to scare anyone.”
_
Spy Satellites:
A reconnaissance satellite or intelligence satellite (commonly, although unofficially, referred to as a spy satellite) is an Earth observation satellite or communications satellite deployed for military or intelligence applications.
The first-generation type (i.e., Corona and Zenit) took photographs, then ejected canisters of photographic film which would descend back down into Earth’s atmosphere. Corona capsules were retrieved in mid-air as they floated down on parachutes. Later, satellite had digital imaging systems and downloaded the images via encrypted radio links.
Spy satellites have traditionally been very important to the United States. They are outfit with a variety of cameras—some with incredibly high resolution—and various listening devices that can pick up military signals and telephone and computer transmissions. Cameras in spy satellites have to be able to survive the intense vibrations of a launch, the freezing temperatures in space and deliver photographs of license plates 80 kilometers up in space.
There were 1,419 active satellites in orbit around the Earth as of August 2015, according to a database compiled by the Union of Concerned Scientists, a nonprofit advocacy group of scientists and engineers. While a large number of these spacecraft are operated by commercial users like DirecTV, XM Satellite Radio and others for communications purposes, another large portion are used for military or government purposes.
_
There are several major types of reconnaissance satellite.
-1. Missile early warning
Provides warning of an attack by detecting ballistic missile launches. Earliest known are Missile Defense Alarm System.
-2. Nuclear explosion detection
Detects nuclear detonation from space. Vela is the earliest known.
-3. Electronic reconnaissance
Signals intelligence, intercepts stray radio waves. SOLRAD is the earliest known.
-4. Optical imaging surveillance
Earth imaging satellites. Satellite images can be a survey or close-look telephoto. Corona is the earliest known. Spectral imaging is commonplace.
-5. Radar imaging surveillance
Most space-based radars use synthetic-aperture radar. Can be used at night or through cloud cover. Earliest known are the Soviet US-A series.
_
Missions:
Examples of reconnaissance satellite missions:
- High resolution photography (IMINT)
- Measurement and Signature Intelligence (MASINT)
- Communications eavesdropping (SIGINT)
- Covert communications
- Monitoring of nuclear test ban compliance
- Detection of missile launches
The 560 acre complex of satellite dishes on Menwith Hill, England may be the largest surveillance station in the world. Run by the National Security Agency, it is believed to be widely involved in intercepting telephone and computer transmissions from around the world. Using a computer program called Echelo, supercomputers at the facility can reportedly scan billions of phone calls and e-mails an hour.
_
Spy Aircraft:
Before spy satellites there were U-2 planes. First flown over the Soviet Union in July 1956, they were built like a glider and could soar above 70,000 feet, beyond the range of missiles that could shoot them down. They took clear pictures of air strips, secret cites and missile sites on 24 flights over four years until Gary Power was shot out of the sky, abruptly ending the program.
More sophisticated than the U-2 was the D-21 “Tagboard” unmanned jet, which was kept secret until the late 1970s. It was launched from the back of the ultra-fast SR-71 aircraft and cruised at a speed of 2,200 mph at an altitude of 17 miles.
The development of advanced aircraft began after World War II when the U.S. military became concerned that for all intents and purposes it didn’t have a clue about the size and capability of the Soviet armed forces: how many aircraft, submarines and rockets they had, and what they were planning to do with them. Memories of Pearl Harbor were still fresh; and concerns about a surprise attack were on the minds of military strategists.
Early renaissance was in the form of planes—first modified World War II bombers and later low-flying jets that flew along the Soviet border in the Baltic and the Pacific. The Russians were not pleased as the United States would have been if Soviet planes regularly flew along its border. Several American planes were shot down by the Soviets.
Air reconnaissance was invaluable but dangerous. From 1950 to 1970 at least 252 crew members of spy flights—most directed at the Soviet Union—were involved in crashes. Only 90 of them survived.
_
Drones and Surveillance Tools:
Drones and surveillance tools have transformed espionage tactics and techniques significantly. These devices enable intelligence agencies to gather vital information without exposing agents to direct danger. The use of drones allows for the observation of sensitive areas from a safe distance, enhancing data collection.
Drones equipped with high-resolution cameras can capture detailed imagery from various altitudes, making them indispensable in reconnaissance missions. Their ability to hover in place provides a unique advantage for monitoring large areas or specific targets for extended periods. Surveillance tools, including motion sensors and thermal imaging systems, further enhance their capabilities.
These technologies have drastically reduced the need for traditional human intelligence (HUMINT) operations in certain environments. However, the efficiency of drones can raise ethical considerations regarding privacy and the potential for misuse. Balancing their benefits with responsible usage is essential in the evolving landscape of espionage.
As the role of drones continues to expand, their integration with artificial intelligence is also on the rise. This development is poised to improve threat detection and analysis, leading to more sophisticated espionage tactics and techniques in the future.
_
Advanced Encryption Techniques:
Advanced encryption techniques are methods used to secure information by converting it into a format that is unreadable without the correct decryption key. A key aspect of modern espionage tactics and techniques, these methods ensure that sensitive communications remain confidential, even in the face of potential interception.
One prevalent approach is asymmetric encryption, often exemplified by the RSA algorithm. This technique utilizes two keys—a public key for encryption and a private key for decryption—providing a robust security framework that is crucial for protecting classified data in espionage operations.
Symmetric encryption, on the other hand, employs a single key for both encryption and decryption. Algorithms like AES (Advanced Encryption Standard) are commonly used for their speed and efficiency, making them suitable for securing vast amounts of intelligence in real-time scenarios.
In espionage, the integration of advanced encryption with secure communication channels enhances operational security. As adversaries continually evolve their hacking techniques, the ongoing development of encryption technologies remains imperative for safeguarding national interests in an increasingly interconnected world.
_
Fusion technology:
Technological advancements have significantly transformed espionage tactics and techniques, allowing for more sophisticated methods of information gathering and covert operations. Modern technology enables intelligence agencies to enhance their capabilities, making traditional espionage increasingly reliant on digital tools.
Security cameras. License plate readers. Smartphone trackers. Drones. We’re being watched 24/7. Fusion technology means all these data streams are fused into one. Fusion architectures are central to the Chinese government’s campaign against dissidents and minority citizens, particularly the Uighur Muslim group. One such system, the Integrated Joint Operations Platform, fuses together facial recognition scans from CCTV cameras; financial, medical, and criminal records; hardware identifiers from smartphones and computers; even mandatory questionnaires that ask residents, among other things, how many times they pray each day. According to reporting by The New York Times, a cloud computing center in Xinjiang, powered in part by chips from Nvidia, can comb through hundreds of millions of photos and reports from the area’s many checkpoints while applying real-time analytics to up to 1,000 CCTV cameras simultaneously. Authorities use the life histories generated by these systems to determine who is “trustworthy.” Those who aren’t often risk being sent to prison or a re-education camp.
_
ESP and Psychic Experiments:
Both the Soviets and the Americans did research in extrasensory perception (ESP) and other psychic phenomena. For 10 years a small group in the technical Services Division of the CIA studied hypnosis and telepathy but concluded that these methods were too unreliable to have practical applications and the programs should be axed. The person who pushed most of its continuance was future CIA director Richard Helms. In a memo he argued that the that the Soviet pursuit of “cybernetics, telepathy, hypnosis and related subjected” needed to addressed and “recent reported advances…may indicate more potential than were believed existed.”
The CIA-run Operation Stargate used clairvoyants and psychics to “visualize” the identities of KGB agents and designs of Soviet weapons. Used primarily in the 1970s and 80s at Fort Meade, Maryland, the psychics reportedly drew clear diagrams of secret Soviet submarine and helped locate a kidnaped American general in Italy. The budget was $20 million a year for 16 psychics involved in 250 projects involving thousands of missions.
In the early 1970s Stanford Research Institute was give $50,000 to investigate “remote viewing.” One psychic was given the geographical coordinates for Semipalatinsk, a secret site in Kazakhstan. The psychic designed a cluster of buildings and an underground storage site for missiles and drew of picture of “damned big crane.” Satellite photography later backed up his descriptions. The pictures of the crane he drew was remarkably similar to a crane that was photographed at the site.
The CIA also developed an ESP teaching machine and gave employees an ESP test along with a standard personality test. The U.S. military looked for “talent,” by checking out people with “certain odd proclivities, like a creative pursuit in music or art, an interest or aptitude in foreign languages. They were also looking for people who didn’t report any ESP experiences.”
The CIA and KGB also experiment with various kinds of drugs. The CIA gave LSD and other hallucinogenic to unwitting human guinea pigs.
_______
_______
Spy equipment:
Spies use a variety of equipment; some are available to purchase on the commercial market, while the restricted professional equipment is available to law enforcement and governments, including:
Communication devices: These can include encrypted smartphones, radios, laptops, and tablets with secure messaging software.
Surveillance equipment: Spies may use hidden cameras in the form of Wi-Fi, GSM, UHF and, in some cases, electricity carrier-type cameras, GPS tracking devices, and RF (radio frequency) bug detectors to monitor their targets.
Disguise tools: Wigs, makeup, and props can alter a person’s appearance and help them blend in with their surroundings. It’s not uncommon for professionals to take advantage of realistic artificial prosthetics to change the tones and shapes of their faces.
Self-defence weapons: Small, easily concealable weapons may be used when cornered in a situation where flight is not an option. Pepper spray and stun guns can be used for self-protection.
Technical spy gadgets: Spies have access to handheld devices such as code-breaking machines, lock-picking tools, and biometric devices to access secure locations.
Concealed devices: Spies may use pens, key fobs, a coffee cup spy camera, buttons, and smartphones to conceal tiny cameras, microphones, or memory cards.
Night vision monocular: These can be used to see in low-light and pitch-dark conditions and conduct observational surveillance at night.
_____
_____
Social engineering in espionage:
In the context of information security, social engineering is the use of psychological influence of people into performing actions or divulging confidential information. This differs from psychological manipulation in that it doesn’t need to be controlling, negative or a one-way transaction. Manipulation involves a zero-sum game where one party wins and the other loses while social engineering can be win-win for both parties. A type of confidence trick for the purpose of information gathering, fraud, or system access, it differs from a traditional “con” in the sense that it is often one of the many steps in a more complex fraud scheme. It has also been defined as “any act that influences a person to take an action that may or may not be in their best interests.”
All social engineering techniques are based on exploitable weaknesses in human decision-making known as cognitive biases.
One example of social engineering is an individual who walks into a building and posts an official-looking announcement to the company bulletin that says the number for the help desk has changed. So, when employees call for help the individual asks them for their passwords and IDs thereby gaining the ability to access the company’s private information. Another example of social engineering would be that the hacker contacts the target on a social networking site and starts a conversation with the target. Gradually the hacker gains the trust of the target and then uses that trust to get access to sensitive information like password or bank account details.
Pretexting:
Pretexting (adj. pretextual), also known in the UK as blagging, is the act of creating and using an invented scenario (the pretext) to engage a targeted victim in a manner that increases the chance the victim will divulge information or perform actions that would be unlikely in ordinary circumstances. An elaborate lie, it most often involves some prior research or setup and the use of this information for impersonation (e.g., date of birth, Social Security number, last bill amount) to establish legitimacy in the mind of the target.
Water holing:
Water holing is a targeted social engineering strategy that capitalizes on the trust users have in websites they regularly visit. The victim feels safe to do things they would not do in a different situation. A wary person might, for example, purposefully avoid clicking a link in an unsolicited email, but the same person would not hesitate to follow a link on a website they often visit. So, the attacker prepares a trap for the unwary prey at a favored watering hole. This strategy has been successfully used to gain access to some (supposedly) very secure systems.
Baiting:
Baiting is like the real-world Trojan horse that uses physical media and relies on the curiosity or greed of the victim. In this attack, attackers leave malware-infected floppy disks, CD-ROMs, or USB flash drives in locations people will find them (bathrooms, elevators, sidewalks, parking lots, etc.), give them legitimate and curiosity-piquing labels, and wait for victims.
Unless computer controls block infections, insertion compromises PCs “auto-running” media. Hostile devices can also be used. For instance, a “lucky winner” is sent a free digital audio player compromising any computer it is plugged to. A “road apple” (the colloquial term for horse manure, suggesting the device’s undesirable nature) is any removable media with malicious software left in opportunistic or conspicuous places. It may be a CD, DVD, or USB flash drive, among other media. Curious people take it and plug it into a computer, infecting the host and any attached networks. Again, hackers may give them enticing labels, such as “Employee Salaries” or “Confidential”.
One study published in 2016 had researchers drop 297 USB drives around the campus of the University of Illinois. The drives contained files on them that linked to webpages owned by the researchers. The researchers were able to see how many of the drives had files on them opened, but not how many were inserted into a computer without having a file opened. Of the 297 drives that were dropped, 290 (98%) of them were picked up and 135 (45%) of them “called home”.
Quid Pro Quo:
An attacker offers to provide sensitive information (e.g. login credentials) or pay some amount of money in exchange for a favor. The attacker may pose as an expert offering free IT help, whereby they need login credentials from the user.
Scareware:
The victim is bombarded with multiple messages about fake threats and alerts, making them think that the system is infected with malware. Thus, attackers force them to install remote login software or other malicious software. Or directly extort a ransom, such as offering to send a certain amount of money in cryptocurrency in exchange for the safety of confidential videos that the criminal has, as he claims.
Tailgating (piggybacking):
An attacker pretends to be a company employee or other person with access rights in order to enter an office or other restricted area. Deception and social engineering tools are actively used. For example, the intruder pretends to be a courier or loader carrying something in his hands and asks an employee who is walking outside to hold the door, gaining access to the building.
_
2016 United States Elections leaks:
During the 2016 United States Elections, hackers associated with Russian Military Intelligence (GRU) sent phishing emails directed to members of Hillary Clinton’s campaign, disguised as a Google alert. Many members, including the chairman of the campaign, John Podesta, had entered their passwords thinking it would be reset, causing their personal information, and thousands of private emails and documents to be leaked. With this information, they hacked into other computers in the Democratic Congressional Campaign Committee, implanting malware in them, which caused their computer activities to be monitored and leaked.
_______
Sex espionage (sexpionage):
Sexpionage is such a potent spying tool. What explains rampant use of sexpionage and honeytraps is the psychology of human vulnerability. Intelligence agencies know that love can often conquer patriotism. Humans are wired for attachment. Emotional bonds, once formed, can override logic and ethical considerations. A target who believes he or she is in love or deeply romantically connected to someone is less likely to question that person’s motives. This emotional fog dulls suspicion and sharpens loyalty — even to the enemy nation’s cause.
Illicit sexual encounters can carry with them a burden of secrecy, fear or shame. Spies exploit this by recording liaisons or extracting compromising information during moments of vulnerability. The resulting “kompromat” (compromising material) can be used for blackmail or coercion.
Many high-value targets are in positions of power and may overestimate their ability to control situations including secret relationships. Narcissistic personalities, in particular, are susceptible to flattery and romantic attention, making them ideal prey. Narcissism and sexual risk-taking are said to be common traits among compromised agents.
The use of romance and sex in spying isn’t always about seduction. Sometimes it’s about cultivating long-term relationships under false pretences. These can last for months or years, with the operative posing as a spouse or lover. This is especially effective because trust deepens over time, increasing the quality and quantity of information the target shares. Cover stories are more believable — a long-term romantic partner often has access to secure devices, travel and conversations. In such operations, targets are more willing to make sacrifices for someone they perceive as a partner or soulmate.
_
KGB Sex Espionage:
A research paper ‘Sex-espionage as a method of intelligence and security agencies’ written in 2014 by Prof. Saša Mijalković of the Academy of Criminalistic and Police Studies, Belgrade, detailed how Soviet spy agency KGB trained its spies for sexpionage: Thus KGB, in addition to all classic and modern technical methods, used the techniques of sex-espionage. It even developed specialist courses of instruction for such purposes. The KGB was fond of using the “Romeo method,” in which handsome Soviet men were sent to the West with false papers to seduce female secretaries with access to information the Communists wanted. The KGB also tried to seducing enemy males with female, and even male agents for information gathering or blackmail purposes. This method was called the “honey trap.” Brothels known as “raspberries” were set up to entrap Westerners.
It was the USSR that established one of the most sophisticated special services in the world, which trained female spies to seduce men. There has been a book put out recently about sex spying. A girl named Vera narrated the story about KGB and how they recruited pretty girls, promising them that they would have all kinds of welfare imaginable, if they would agree to fulfil their civil duty and become sex agents. They were trying to deliver them from any shyness or shame, teaching them sex techniques, showing perverted pornographic videos. Girls were supposed to be able to execute any task.
However, surprised happened sometimes too, like it was with the notorious case for seducing Indonesian President Ahmed Sukarno. He was known for his sexual passion. That is why KGB sent a group of young girls to him during his visit to Moscow. Those girls got acquainted with Ahmed Sukarno in a plane, under the disguise of air hostesses, then he invited them to his hotel room in Moscow and arranged a grand orgy. The orgy was filmed by two candid cameras that were fixed behind mirrors. It seemed that the operation was just perfect. Before starting the blackmail, KGB invited Sukarno in a small private movie theatre and showed him the pornographic video, in which he was playing the main part. KGB agents were expecting him to get really frightened, that he would agree to cooperate with them at once, but everything happened vice versa: Sukarno fondly decided that it was a gift from the Soviet government, so he asked for more copies to take them back to Indonesia and show them in movie theatres. Sukarno said to flabbergasted agents that the people of Indonesia would be very proud of him, if they could see him doing the nasty with Russian girls.
______
______
Animal use for espionage:
The death of a spy is rarely newsworthy, due to the secrecy surrounding it. But when a white beluga whale suspected of spying for Moscow was found dead in Norwegian waters, the animal soon became a minor celebrity. Hvaldimir (a play on the Norwegian word for whale, hval, and the first name of Russian president) was even given an official autopsy by the Norwegian Directorate of Fisheries. The whale had been uncovered as a spy in 2019, and is one in a long line of animals which have been used by the intelligence services. The US ran similar experiments with animals, some dating back to the 1960s. One of the CIA’s more unusual attempts to use animals as spies was Operation Acoustic Kitty. The idea was to implant a microphone and antenna into the cat and use it to eavesdrop on potentially interesting conversations. The test of the “prototype” went horribly wrong when the cat wandered off and was run over by a taxi, leading to the programme being quickly abandoned.
A more successful example was the use of spy pigeons. Equipped with tiny cameras, pigeons could easily access otherwise restricted areas and “take photos” without arousing suspicion before safely returning to home base using their extraordinary homing ability.
Over time, technology created opportunities to exploit the stealthiness of animals while eliminating their unpredictability. Project Aquiline aimed to create a bird-like drone fully equipped in the style of more traditional spy planes, but smaller and more versatile so it could get closer to its targets.
Another, even more miniature version was the insectothopter that the CIA developed in the 1970s. Although neither the aquiline or insectothopter designs ever became fully operational, they are acknowledged as forerunners of today’s drones.
Fast-forward to the 1990s, and the CIA’s robotic catfish Charlie emerges as one in a longer line of successfully operationalised underwater drones that are more effective and less vulnerable than the hapless Hvaldimir.
_______
_______
AI and espionage:
Artificial Intelligence (AI) involves the use of machine learning algorithms and predictive models to process and analyze large datasets. Intelligence gathering, a critical component of national security and defense systems, refers to the collection and analysis of information to identify potential threats. Recently, AI has taken on a bigger role in intelligence systems, automating data collection and analysis processes that used to be completed manually.
Artificial intelligence is revolutionizing intelligence gathering in modern conflicts by enhancing data analysis and decision-making processes. Its ability to sift through vast amounts of information rapidly allows military analysts to identify trends and potential threats with unprecedented precision.
In the realm of signals intelligence, AI algorithms can analyze communications and electronic signals more efficiently than human operators. This capability enables armed forces to intercept and decode vital enemy communications, improving situational awareness and operational readiness during conflicts.
Another significant application is in predictive analytics, where AI models forecast enemy movements and intentions based on historical data. By utilizing machine learning algorithms, forces can anticipate actions before they occur, allowing for proactive strategic planning and resource allocation.
AI also enhances image recognition technologies, allowing for better surveillance and reconnaissance. Drones equipped with AI can autonomously identify targets and assess battlefield conditions, providing critical intelligence that significantly influences military operations and strategies in modern warfare.
_
The strategic competition between the United States and China has elevated AI as a critical factor in national security and defense intelligence capabilities. Both nations are heavily investing in AI, aiming to outpace each other in developing technologies that could offer a decisive advantage in intelligence gathering. At the same time, AI’s role in geospatial intelligence is particularly evident in the ongoing Russo-Ukrainian conflict. AI has become an essential asset for analyzing data from various sensors, systems, and personnel in the field. It gathers data from combat scenarios in real-time and provides actionable intelligence to military operators.
Proponents of AI’s increasing role in intelligence and defense cite two key reasons for their support:
- Enhanced Data Analysis: Proponents of AI in intelligence gathering highlight AI’s ability to process vast amounts of data quickly and with precision. For example, Scylla AI software, designed for security and defense applications, demonstrated threat detection accuracy exceeding 96% and significantly reduced false alarm rates when tested by the U.S Department of Defense. By integrating computer vision and machine learning algorithms, Scylla improved response times in critical defense and security environments. Additionally, supporters cite projects like the U.S. Defense Intelligence Agency’s SABLE SPEAR which successfully employed AI to identify illicit activities that traditional methods overlooked.
- Complementary Capabilities: Supporters contend that by automating repetitive tasks and providing recommendations based on historical data, AI not only reduces human error, but can serve to complement human decision-making. They argue that AI systems are not completely replacing military operators’ autonomy to make decisions, but rather serving as a partner in decision making that can increase accuracy and decrease collateral damage in military operations.
_
How are artificial intelligence and the fire hose of incoming data upending the traditional business of intelligence gathering and analysis?
Five ‘more’ things that are changing the intelligence business in dramatic ways.
-1. The first is more threats, more types of nefarious actors who can threaten across vast geographic distances in cyberspace. From the dawn of history until the invention of the internet in the 1960s, two things provided security: power and geography. That’s no longer true. In cyberspace, anyone can threaten across borders without firing a shot because good and bad neighborhoods are all connected online. There are no oceans or mountain ranges protecting us. At the same time, power isn’t what it used to be. The U.S. is the most powerful actor in cyberspace and also the most vulnerable actor in cyberspace because we are so digitally connected. The result is that American intelligence officials have to understand and anticipate a wide array of threats from weak countries and non-state actors, not just powerful countries like Russia and China.
-2. The second “more” is data. Thanks to new technologies, the amount of data on Earth is doubling every 24 months. It’s an astounding amount, and much of it is from open sources that are publicly available. It used to be that intelligence agencies had to hunt for secrets, but now they’re drowning in data.
Traditionally, intelligence reports started with clandestine material and then sprinkled open-source information on top. It should now be the opposite: Start with the open-source intelligence and then see how it fits with what comes from clandestine sources. And the key to using open-source intelligence is AI.
-3. The third “more” is more speed: Information is traveling at greater speeds, decision-making is at greater speeds, and we need intelligence insights much faster. During the Cuban missile crisis of 1962, President Kennedy had 13 days to deliberate in secret about what he would do after U-2 spy planes discovered Soviet missiles in Cuba. On 9/11, President George W. Bush had just 13 hours to weigh intelligence about who was responsible for that horrific attack and how the U.S. would respond. Today, decision time could be 13 minutes or less.
-4. The fourth “more” is the expanding number of decision makers who need intelligence. Who counts as a decision maker today? It’s not just people with security clearances. It’s tech company leaders. It’s Twitter and Facebook and other companies that exercise more global influence than most governments. It’s voters getting public service announcements about foreign election interference. So the intelligence community needs to think about how it produces analysis for all these other decision makers outside of the U.S. government.
-5. The fifth “more” is more competition, more competitors in the collection and analysis of intelligence. Intelligence is anybody’s business now. One example, the raid on Osama Bin Laden. The Pakistani military didn’t see U.S. forces coming, but a local guy heard the helicopters and was live-tweeting the whole time it was happening. Anybody can be an intelligence collector or analyst today whether realizing it or not. One challenge for intelligence agencies is figuring out how to harness the insights from this open-source world.
_
Is traditional human intelligence gathering — using spies and clandestine operations to pry loose secrets — becoming irrelevant?
Human intelligence will always be important, but machine learning can free up humans for tasks that they’re better at. Satellites and AI algorithms are good at counting the number of trucks on a bridge, but they can’t tell you what those trucks mean. You need humans to figure out the wishes, intentions, and desires of others. The less time that human analysts spend counting trucks on a bridge, the more time they will have to figure out what those trucks are doing and why.
There is a vast amount of open-source data, but you need artificial intelligence to sift through it. So imagine a new intelligence cycle where you begin by using open-source information to surface key issues, and then get human sources to dig deeper into them.
A lot of human analytical work right now is on mundane tasks that could be automated by artificial intelligence. Think about how much time it takes for human analysts to locate Chinese surface-to-air missiles over its huge territory. An algorithm for analyzing satellite images can reduce the number of suspect sites, which frees up bandwidth for humans to do higher-level analytical thinking.
One of the most intriguing ideas is to have AI “red cells,” or teams that use open-source information and AI and compete against human analysts. The idea is that red cells would help scrub human assumptions and sharpen thinking by surfacing alternative pieces of information or hypotheses. That is what the Russians are doing.
_
AI enabled enhanced spying:
In an editorial for Slate, renowned security researcher Bruce Schneier warned that AI models may enable a new era of mass spying, allowing companies and governments to automate the process of analyzing and summarizing large volumes of conversation data, fundamentally lowering barriers to spying activities that currently require human labor.
In the piece, Schneier notes that the existing landscape of electronic surveillance has already transformed the modern era, becoming the business model of the Internet, where our digital footprints are constantly tracked and analyzed for commercial reasons. Spying, by contrast, can take that kind of economically inspired monitoring to a completely new level:
“Spying and surveillance are different but related things,” Schneier writes. “If I hired a private detective to spy on you, that detective could hide a bug in your home or car, tap your phone, and listen to what you said. At the end, I would get a report of all the conversations you had and the contents of those conversations. If I hired that same private detective to put you under surveillance, I would get a different report: where you went, whom you talked to, what you purchased, what you did.”
Schneier says that current spying methods, like phone tapping or physical surveillance, are labor-intensive, but the advent of AI significantly reduces this constraint. Generative AI systems are increasingly adept at summarizing lengthy conversations and sifting through massive datasets to organize and extract relevant information. This capability, he argues, will not only make spying more accessible but also more comprehensive.
“This spying is not limited to conversations on our phones or computers,” Schneier writes. “Just as cameras everywhere fueled mass surveillance, microphones everywhere will fuel mass spying. Siri and Alexa and ‘Hey, Google’ are already always listening; the conversations just aren’t being saved yet.”
What’s especially pernicious about AI-powered spying is that deep-learning systems introduce the ability to analyze the intent and context of interactions through techniques like sentiment analysis. It signifies a shift from observing actions with traditional digital surveillance to interpreting thoughts and discussions, potentially impacting everything from personal privacy to corporate and governmental strategies in information gathering and social control.
In his editorial, Schneier raises concerns about the chilling effect that mass spying could have on society, cautioning that the knowledge of being under constant surveillance may lead individuals to alter their behavior, engage in self-censorship, and conform to perceived norms, ultimately stifling free expression and personal privacy.
_
The Growing Threat of AI-Enhanced Hacking and Cyber Espionage:
Figure below shows limitations of cybersecurity:
The rise of Artificial Intelligence (AI) in cyber warfare has ushered in a new era of state-sponsored espionage, posing unprecedented global security risks. North Korea’s notorious hacking campaigns, aimed at stealing classified military information and fueling its banned nuclear program, exemplify how AI enhances state-sponsored cyber espionage. A specific North Korean hacking group, APT45, also known as Anadriel, has been linked to various cyberattacks, targeting defense manufacturers and engineering firms in the United States and South Korea. North Korea’s cyber operations have targeted critical sectors globally. In one case, Rim Jong Hyok, a military intelligence operative, was indicted for hacking into U.S. hospitals, NASA, and military bases, installing ransomware that disrupted healthcare services and encrypted sensitive data. The ransom was demanded in Bitcoin, which was laundered through a Chinese bank to fund further cyberattacks. North Korean operatives have also exploited the rise of remote work by posing as IT workers using falsified identities. For example, “Kyle,” a North Korean agent, secured a remote job in the U.S. and had company laptops shipped to North Korea, giving him direct access to corporate networks. These activities highlight the use of AI-driven malware, which evolves rapidly, making traditional defense systems like firewalls and antivirus software ineffective against the adaptive nature of these threats.
North Korea’s cyber espionage is not unique, but its sophistication is amplified by AI’s ability to automate complex attacks. According to the United Nations Security Council’s March 2024 report, North Korea has stolen approximately three billion dollars’ worth of cryptocurrency between 2017 and 2023 to fund its nuclear weapons program. AI technologies, such as OpenAI’s large language models, have been used by North Korean hackers to automate phishing campaigns and identify targets more efficiently, further complicating cybersecurity efforts and making state-sponsored espionage harder to counter. By employing AI in the reconnaissance phase, hackers can analyze massive datasets to identify network vulnerabilities more efficiently than ever. This automation enables them to breach systems undetected and steal sensitive data, as seen in the high-profile theft of cryptocurrency to fund North Korea’s nuclear weapons program.
The AI-enhanced malware used in these campaigns can self-evolve, bypassing conventional defenses, thus underscoring the limitations of traditional cybersecurity strategies in the face of AI-driven threats. Cybersecurity strategies must evolve, requiring continuous monitoring and updates to include AI-specific defenses. Failing to do so risks opening security gaps, as current control systems may become outdated or incomplete without proper adjustments.
In response, some nations have recognized the growing necessity of integrating AI into their own cybersecurity strategies. South Korea, for example, revised its National Cybersecurity Strategy to incorporate AI-driven tools to detect and respond to cyber threats in real-time. Such adaptive measures allow for faster detection of anomalies and enable predictive threat intelligence, reducing the reaction time to cyber intrusions. Yet, as AI empowers state-sponsored espionage, it also raises significant ethical concerns. The line between effective cybersecurity and potential violations of privacy and civil liberties becomes increasingly blurred when vast amounts of data are processed by AI to detect threats.
AI has also enabled new forms of social engineering, making cyberattacks more targeted and persuasive. Cybercriminals can now craft more realistic phishing emails and deepfake videos that are nearly indistinguishable from legitimate communications. These attacks exploit human trust and can be difficult to detect without advanced AI-based defenses. The FBI has raised alarms about the increasing use of AI in phishing and social engineering, noting that AI can enhance the scale and accuracy of such attacks, leading to more successful intrusions. As technology continues to evolve, so do cybercriminals’ tactics. Attackers are leveraging AI to craft highly convincing voice or video messages and emails to enable fraud schemes against individuals and businesses alike. These sophisticated tactics can result in devastating financial losses, reputational damage, and compromise of sensitive data. For instance, AI-powered voice and video cloning scams have tricked victims into divulging sensitive information by mimicking trusted individuals.
Despite the threats posed by AI-enhanced hacking, the technology itself offers some solutions. AI-powered cybersecurity tools are being developed to counter these evolving threats. By analyzing vast amounts of data in real-time, AI can detect and respond to malicious activity more effectively than traditional security measures. For example, AI’s ability to learn from patterns allows it to anticipate cyberattacks and react faster than human-operated systems. The use of AI in cybersecurity is already showing promising results, with organizations reporting significant reductions in the cost of data breaches thanks to AI-driven threat detection.
However, this arms race between cybercriminals and defenders presents a paradox: while AI offers powerful tools for defense, it simultaneously lowers the barrier for novice hackers. AI’s accessibility means that even less skilled individuals can carry out sophisticated cyberattacks. In the near future, AI will almost certainly escalate the frequency and intensity of cyberattacks. The UK’s National Cyber Security Centre predicts that by 2025, AI will significantly enhance existing hacking tactics, allowing both state and non-state actors to conduct more sophisticated operations with greater ease. This democratization of hacking capabilities exacerbates the cybersecurity threat landscape, as AI can be used to automate everything from reconnaissance to executing complex attacks, as seen in AI-enhanced ransomware campaigns.
_
AI’s growing role in intelligence and defense has drawn criticism for many reasons:
- The “Black Box” Problem: Critics argue that AI’s lack of transparency in decision-making, often referred to as the “black box effect,” presents a significant challenge. AI systems may behave unpredictably, especially when trained on biased data. Since it is very difficult for operators to discern how and why AI systems reach certain decisions, it is difficult to redirect AI systems after making decisions that are harmful.
- Human Rights Consequences: Opponents say the “Black Box” problem can lead to errors in critical applications, rendering AI-driven decisions dangerous in combat. A notable example is the U.S. military’s AI-driven drone strike in Kabul on August 29, 2021. The AI system incorrectly identified a civilian vehicle as a threat, resulting in a tragic strike that killed 10 civilians, including 7 children. AI’s reliance on input data quality means that biased or flawed data can produce inaccurate and potentially deadly conclusions. In the context of military operations, these flaws could lead to increased civilian casualties or misidentification of combatants, violating international norms like the Geneva Convention.
- Security Vulnerabilities: Centralized data analysis systems also increase the risk of cyberattacks. Critics point out that advanced AI systems could be exploited by malicious actors, raising concerns over the security of sensitive information used in intelligence operations.
- Infrastructure and Cultural Resistance: Finally, critics hold that integrating AI into government systems requires significant resources and organizational overhaul. Transitioning to AI-based intelligence systems requires updates to infrastructure and organizational culture, and may result in layoffs of employees. The U.S. Department of Defense has faced difficulties in standardizing and integrating its vast array of data sources, hindering AI deployment across military branches. Additionally, resistance from personnel concerned about job displacement and AI’s role in decision-making has slowed the integration process.
_
In a nutshell, the integration of AI into intelligence operations offers the potential for increased efficiency, enhanced data analysis, and improved threat detection. However, it also introduces serious concerns about accessible and comprehensive mass spying, enhances state-sponsored cyber espionage, enhanced scale and accuracy of cyber-attacks, threat to data security, threat to job security, and the human rights risks of unpredictable combat outcomes.
______
______
Section-9
Government spying on people:
_
Surveillance:
Surveillance is the monitoring of behavior, many activities, or information for the purpose of information gathering, influencing, managing, or directing. This can include observation from a distance by means of electronic equipment, such as closed-circuit television (CCTV), or interception of electronically transmitted information like Internet traffic. Increasingly, governments may also obtain consumer data through the purchase of online information, effectively expanding surveillance capabilities through commercially available digital records. It can also include simple technical methods, such as human intelligence gathering and postal interception.
Surveillance is used by citizens, for instance for protecting their neighborhoods. It is widely used by governments for intelligence gathering, including espionage, prevention of crime, the protection of a process, person, group or object, or the investigation of crime. It is also used by criminal organizations to plan and commit crimes, and by businesses to gather intelligence on criminals, their competitors, suppliers or customers. Religious organizations charged with detecting heresy and heterodoxy may also carry out surveillance. Auditors carry out a form of surveillance.
Surveillance can unjustifiably violate people’s privacy and is often criticized by civil liberties activists. Democracies may have laws that seek to restrict governmental and private use of surveillance, whereas authoritarian governments seldom have any domestic restrictions.
Espionage is by definition covert and typically illegal according to the rules of the observed party, whereas most types of surveillance are overt and are considered legal or legitimate by state authorities.
_
Government Surveillance:
Government surveillance refers to the monitoring of individuals or groups by government agencies, often justified by national security concerns. In the United States, this practice has evolved significantly, particularly since the 9/11 attacks, leading to increased powers for agencies like the NSA, FBI, and CIA to conduct surveillance activities such as wiretapping and data collection. The balance between ensuring national security and protecting individual privacy rights remains a contentious issue, with various laws like the USA PATRIOT Act and the Foreign Intelligence Surveillance Act (FISA) shaping the legal framework governing these practices.
Critics argue that government surveillance, particularly mass wiretapping, infringes on civil liberties and violates the First Amendment rights of individuals, raising concerns about the potential misuse of collected data. Historical controversies, such as the NSA’s warrantless wiretapping program and the use of surveillance against marginalized groups, highlight the complex dynamics at play. The emergence of whistleblowers like Edward Snowden has further intensified the debate over transparency and accountability in government surveillance practices. As legal challenges and reforms continue to evolve, understanding the implications of government surveillance is essential for informed public discourse on privacy and security in a democratic society.
_
Also known as government surveillance, government spying refers to the observation of an individual or group by a government to collect information. The surveillance is typically carried out for an extended period.
Governments can spy on individuals and groups using surveillance technologies and by observing the following:
-1. Wiretaps and listening devices: Authorized by court orders, these can be used to intercept phone calls and text messages.
-2. CCTV and facial recognition technology: AI tools used by governments can take the pictures you’ve shared on social media and enter them into a facial recognition database. Once they have that, they can pair it with CCTV cameras that can pinpoint your location and monitor your comings and goings.
-3. Metadata analysis: Even if the content of communications is not intercepted, agencies can collect metadata—data about data—such as the time and duration of phone calls, email addresses of senders and recipients, and the locations of the communicating parties.
-4. Data collection programs: These programs can collect vast amounts of data from internet service providers and tech companies, including emails, chat messages, web searches, and more, especially when you sign into accounts that identify and track you.
-5. Backdoor access to devices and software: Governments can pressure or collaborate with technology companies to gain backdoor access to devices and software, allowing them to bypass encryption and directly access data and communications.
-6. Social media monitoring: Government agencies monitor social media platforms to gather intelligence
_
Why does the government spy on us?
There are multiple reasons why the government spies on citizens:
- Fighting terrorism. The government may spy on citizens to identify and combat terrorism. To that end, it may collect citizens’ data from telecommunications services and Internet Service Providers (ISPs). Typically, the government collects this information in bulk and it often contains metadata. This may help police investigate, prevent, and prosecute terrorists.
- Preventing and combating crime. To unearth organised crime, including smuggling, poaching, the drug, cigarette and weapons trade, and human trafficking. The government can spy on individuals to help fight crime and to make the country safer. The FBI can secretly place a wiretap on a person’s device as part of a criminal investigation. However, it doesn’t have to prove probable cause or have reasonable suspicion that a crime has been committed.
- Protecting national security. When there is threat to critical national infrastructure (such as the electricity supply, major ports of entry, and mobile network infrastructure). The NSA monitors, collects, and processes information to aid in foreign intelligence, domestic intelligence, and counterintelligence activities. It may do so without a warrant.
- Law enforcement investigations. Law enforcement now has more resources available to help fight crime than undercover cops and agents. The advancement of technology means that crime suspects can be monitored remotely with the use of technology.
- Political intelligence. The government may monitor citizens to counter the threat of espionage. For example, the UK government’s MI5 Security Service has a branch dedicated to tackling espionage to foil the plans of anyone passing on sensitive information and equipment to other countries.
Note:
You don’t have to be on the FBI’s most wanted list, a known terrorist, or an enemy of the state to be monitored by the government. The government collects information about regular citizens, too. That’s why it’s important to be proactive about protecting your privacy.
_
Is it legal for the government to watch people?
It is illegal for the government to watch people without their permission, as it infringes upon their right to privacy. However, certain laws permit government agencies to monitor US citizens. For example, according to the American Civil Liberties Union (ACLU), the Patriot Act allows the FBI to secretly wiretap or physically search US citizens to obtain evidence in a criminal case. In fact, they can do so without proving probable cause, as required by the Fourth Amendment.
Federal agencies that can spy on American citizen include:
- National Security Agency (NSA)
- Federal Bureau of Investigation (FBI)
- Department of Homeland Security (DHS)
- Homeland Security Investigations (HSI)
- US Customs and Border Protection (CBP)
- Immigration and Customs Enforcement (ICE).
_
Here’s how the NSA can monitor you:
- Obtaining your data from Big Tech. PRISM is an NSA program that collects customers’ data related to internet communications. The NSA’s PRISM program requires Big Tech companies to hand over this data, which includes documents, emails, and messages. These companies include Google, Microsoft, Apple, Facebook, Yahoo!, YouTube, Skype, and more.
- Accessing your phone records. The NSA has accessed the phone records of US citizens in the past, so this could happen to you. According to the New York Times, the NSA claimed it discovered in 2018 that it had unknowingly and illegally obtained the phone and text records of 600 million people. It blamed the situation on an unnamed telecommunications provider.
- Hacking your tech devices. The NSA’s Tailored Access Operations is a hacking unit focused on exploiting security vulnerabilities in consumer devices. It also hacks into vulnerable IT systems.
- Using backdoors on your devices. The NSA can intercept your device through backdoors. It works with manufacturers to build backdoors, which are vulnerabilities that give you access to a device. But that’s not all; the NSA also intercepts device shipments to add backdoors to phones and computers. This is all done to make it easier for the government department to spy on citizens.
_
Below are the various reasons why the US government may use social media to collect information about you:
- Monitoring situations. Government departments monitor social media platforms to get first-hand information and updates about current events. This allows those officials to come up with official responses based on the information gathered. To that end, they track keywords related to current events and breaking news on social media apps and platforms.
- Identifying threats. Similar to monitoring situations, the government monitors social media to track specific individuals or identify threats related to public safety and more. If the user being monitored has their social media accounts set to public, the government can easily and frequently watch them there. The difference between monitoring situations and identifying threats is that the former focuses on threats on a broader scale, while the latter focuses on tracking individuals who pose a threat.
- Screening and vetting travellers and immigrants. The US places importance on managing threats coming into the country. So the government may screen incoming travellers and immigrants to ensure they pose no threat to the country and verify their information upon entering it. The government can also track travellers while they’re in the country.
- Investigating cases. Investigating criminals and civil cases is a lot of work and much of it entails traveling, on-the-ground work, and working with documents. Social media, however, makes it so much easier. Government officials can spy on suspects or anyone involved in a case on social media from behind a desk. The FBI is an example of a government department that uses social media for investigative work. They don’t have to hack the targets’ accounts, either; they can collect information from their posts, especially if they’re active social media users.
______
How would you know if the federal government had been electronically spying on you?
Short answer: You probably wouldn’t.
When the government invades your privacy — whether by searching your home, your car, your emails, or anything else — it should give you notice of that intrusion unless it has a compelling reason for delay. You see it on television all the time: When the police search a house, they show a warrant or leave one behind at the scene. The individual whose privacy is at stake knows there was a search and what was taken.
If the government never told you that it had spied on you, you’d never be able to challenge the search or stop it from happening again. You’d be stuck essentially having to trust that if the government searched your emails or other belongings, it had good reason to and was acting lawfully.
It’s worth noting, however, that the federal government has a long history of abusing its surveillance powers. And as the amount of digital data has expanded, the amount of surveillance has exploded, too. So has the secrecy and the absence of accountability surrounding electronic searches. These searches are conducted under various laws, but they have one thing in common: Individuals rarely find out that their private emails, internet chats, or documents stored in the cloud have been searched. (Some companies strive to inform their customers when the government demands private data, but very often the companies that receive these demands are gagged from saying anything.)
______
______
ECHELON:
In 1988 an article titled “Somebody’s listening” by Duncan Campbell in the New Statesman described the signals-intelligence gathering activities of a program code-named “ECHELON”. The program was engaged by English-speaking World War II Allied countries – Australia, Canada, New Zealand, the United Kingdom and the United States (collectively known as AUSCANNZUKUS). It was created by the five countries to monitor the military and diplomatic communications of the Soviet Union and of its Eastern Bloc allies during the Cold War in the early 1960s.
By the 1990s the ECHELON system could intercept satellite transmissions, public switched telephone network (PSTN) communications (including most Internet traffic), and transmissions carried by microwave. The New Zealand journalist Nicky Hager provided a detailed description of ECHELON in his 1996 book Secret Power. While some member governments denied the existence of ECHELON, a report by a committee of the European Parliament in 2001 confirmed the program’s use and warned Europeans about its reach and effects. The European Parliament stated in its report that the term “ECHELON” occurred in a number of contexts, but that the evidence presented indicated it was a signals-intelligence collection system capable of interception and content-inspection of telephone calls, fax, e-mail and other data-traffic globally.
James Bamford further described the capabilities of ECHELON in Body of Secrets (2002) about the National Security Agency. Intelligence monitoring of citizens, and their communications, in the area covered by the AUSCANNZUKUS security agreement have, over the years, caused considerable public concern.
______
______
Post 9/11 mass surveillance:
The events of 9/11 have been used to dramatically expand the government’s mass surveillance authorities (figure below) and weaken Constitutional protections.
This post-9/11 expansion has built on a much longer history of slavery, colonial occupation, and longstanding racism, as well as wartime spying and the War on Drugs. Yet it is also markedly different from what existed before, in both its technological capacities and its scale and breadth. The pervasive fear, Islamophobia and xenophobia, weakened civil liberties protections, and exponentially increased funding of the post-9/11 era enabled the unprecedented breadth and scale of surveillance reigning across the United States today.
_
While “mass surveillance” is often used to refer to government spying, today it involves a complex grouping of federal agencies, local police, private companies, and even members of the public. Mass surveillance programs allow the U.S. government to warrantlessly and “incidentally” vacuum up Americans’ communications, metadata and content, and store their information in data centers and repositories such as the database authorized by Section 702. Federal agencies also increasingly obtain data from private companies and track Americans using facial recognition, social media geomapping, and other technologies.
_
Mass surveillance has intensified the criminalization of marginalized and racialized groups, from Muslims and Arabs to Latinx immigrant communities to Black and Indigenous organizers, and has increasingly targeted protest movements such as Black Lives Matter and the movement to stop the Dakota Access Pipeline. With the rise of what the U.S. government portrays as competition with China, Asian Americans have also been increasingly targeted. Mass surveillance has also facilitated the tracking, incarceration, and deportation of thousands of migrants, most of whom were guilty only of the civil offense of crossing a border without government permission. The post-9/11 state’s focus on racialized groups may have ill-prepared it to address rising white supremacist violence.
_
In a nutshell, in post 9/11 mass surveillance:
- The U.S. used post-9/11 terrorist fears to expand its monitoring of U.S. citizens who have nothing to do with terrorism.
- Mass surveillance has intensified the criminalization of marginalized and racialized groups, particularly Muslims, immigrants, and protesters for racial and labor justice.
- Mass surveillance has cost untold dollars, normalized an erosion of privacy and freedom, and entrenched an expanding surveillance infrastructure that grows ever more difficult to control.
_____
_____
NSA Spying:
NSA spying refers to the surveillance activities conducted by the National Security Agency (NSA), primarily revealed to the public in 2013 through the disclosures of whistleblower Edward Snowden. Snowden, a former NSA contractor, leaked classified documents that exposed extensive programs the NSA used to collect data on global citizens, including telephone metadata and internet communications. His revelations ignited widespread debate about privacy rights, government transparency, and the balance between national security and individual freedoms.
_
The origins of the NSA date back to World War I, evolving significantly after the September 11 attacks, which granted the agency enhanced surveillance powers under the USA PATRIOT Act. The subsequent public backlash prompted demands for investigations and reforms regarding the agency’s practices, especially concerning its compliance with the Fourth Amendment, which protects against unreasonable searches. Notably, Snowden’s actions led to various legal challenges and legislative measures aimed at curbing surveillance overreach. While some argue that NSA surveillance is vital for national security, others contend that such practices infringe on civil liberties. The ongoing discourse underscores a critical intersection of technology, privacy, and governance, reflecting diverse perspectives on the role of intelligence in a democratic society.
_
NSA Spying Today:
The NSA was forced to halt its program of phone spying by June 1, 2015, after the provisions of the Patriot Act that allowed for the program had expired and the Senate failed to extend them. The USA Freedom Act passed the next day reestablished some elements of the Patriot Act, but also imposed limits on the harvesting of telecommunications metadata by the NSA (and other intelligence agencies). However, critics of the agency’s data collection efforts argued that loopholes would allow the NSA to continue gathering the same type of information through other means. The agency’s operations in general have remained controversial, with ongoing debate over the balance between surveillance that benefits national security and that which potentially infringes on people’s rights. The domestic surveillance programs known as PRISM and Upstream (which focused on internet communications) drew particular opposition from human rights watchdog groups.
As for Snowden himself, he continued to live in Russia, with his asylum claim extended repeatedly. US officials continued to seek his return to the United States, where he would likely face prosecution for espionage and theft of government property. In January 2014, two Norwegian politicians nominated him for the Nobel Peace Prize. They stated that, while they did not condone all of his actions, Snowden’s whistle-blowing sparked public debate and policy changes that have “contributed to a more stable and peaceful world order.” Snowden’s appeals for clemency from the United States were unsuccessful, as was a widespread campaign to have him pardoned that was launched in 2016 by human rights organizations such as Amnesty International and the American Civil Liberties Union (ACLU). He faced further pressure from the administration of US president Donald Trump, who suggested Snowden should be executed. Snowden published the memoir Permanent Record in 2019, and in October 2020 Russia granted him permanent residency status.
_______
_______
Section-10
Nations spying on nations:
_
Espionage and Political Influence:
Espionage refers to the covert acquisition of confidential information for political, military, or economic advantage. This practice has a long history and remains an integral tool for nations seeking to exert political influence. Political influence, on the other hand, encompasses the capacity to affect decisions and actions of governmental entities, often through various means, including espionage.
The relationship between espionage and political influence is complex and deeply intertwined. Espionage can provide critical insights into an adversary’s capabilities and intentions, enabling a nation to formulate informed strategies. In this context, political influence may be wielded based on the intelligence obtained, altering diplomatic relations or internal policies.
Modern political landscapes increasingly involve non-traditional forms of espionage, such as cyber methods. The rise of technology has transformed how states gather intelligence and reshape political dynamics, emphasizing the need for understanding the mechanisms of espionage and political influence in today’s global environment.
_
Espionage is the practice of obtaining confidential information by clandestine means, primarily for political and military purposes. In essence, it serves as a tool for states to gain a strategic advantage in international relations. This delicate interplay between espionage and politics highlights their intrinsic connection; political agendas often dictate the scope and methods of espionage activities. The political context of espionage is shaped by the necessity of states to safeguard national interests while navigating complex global dynamics. Governments rely on espionage to uncover critical intelligence about adversaries, assess threats, and inform decision-making processes. Consequently, the intersection of espionage and politics impacts both diplomatic relationships and the formulation of foreign policies. Moreover, political motivations can also justify ethically ambiguous actions in espionage. States may prioritize national security concerns over moral considerations, leading to debates regarding the legitimacy of specific espionage operations. As such, the political implications of espionage extend beyond mere intelligence gathering, influencing international stability and the balance of power.
_
Espionage serves as a critical tool in shaping international relations by facilitating states’ understanding of each other’s intentions, capabilities, and vulnerabilities. The utilization of covert information collection directly influences diplomatic strategies and international negotiations, often determining the balance of power.
Espionage significantly impacts foreign policy, enabling nations to anticipate and mitigate threats. Historical examples, such as the CIA’s operations during the Cold War, reveal how intelligence activities were pivotal in forming alliances and countering perceived adversaries. Such maneuvers illustrate that espionage is not merely tactical but also strategically essential.
_
The intricate relationship between espionage and diplomatic tensions can be exemplified by incidents like the Snowden revelations. These disclosures highlighted the extent of surveillance among allies, leading to deteriorated trust and complications in cooperative agreements. Espionage activities can thus strain relationships and alter political landscapes. Overall, espionage profoundly influences international relations by shaping how countries interact, negotiate, and position themselves on the global stage. The ramifications of such activities extend beyond immediate political gains, establishing patterns of suspicion and rivalry that can persist over time.
_____
Espionage as a Tool of Foreign Policy:
Espionage is an integral tool in the realm of foreign policy, employed by nations to gather sensitive information about potential adversaries or allies. This clandestine activity allows governments to shape strategic decisions based on insights into military capabilities, political intentions, and economic stability. Historically, espionage has influenced diplomatic negotiations and military strategies. For instance, during the Cold War, the United States and the Soviet Union heavily relied on espionage to gauge each other’s nuclear capabilities, which informed their foreign policy decisions and arms control agreements. Today, espionage extends beyond traditional methods, incorporating cyber operations to gain intelligence efficiently. Nations exploit technological advancements to monitor economic trends, political developments, and social unrest, ensuring that foreign policy remains adaptive and informed by real-time data. In summary, espionage serves as an influential tool of foreign policy, enabling states to navigate complex international landscapes. As governments continue to leverage these tactics, the interplay between espionage and political influence will remain vital for maintaining national security and diplomatic relations.
_
Espionage and Diplomatic Tensions:
Espionage is the act of obtaining secret or confidential information, particularly in the political domain, which can heighten diplomatic tensions between nations. States often engage in espionage to bolster their strategic advantage, leading to mistrust and conflict.
Espionage can strain relations through several mechanisms:
-1. Discovery of clandestine operations can provoke outrage and retaliation.
-2. Tensions escalate when espionage is linked to violations of sovereignty.
-3. Political fallout occurs if targeted nations retaliate through sanctions or other diplomatic means.
-4. Espionage can damage diplomatic relations between countries and lead to mistrust and suspicion.
-5. The intelligence gathered through espionage can be used to fuel conflicts or even lead to wars.
-6. Some argue that espionage is unethical and that governments should rely on more transparent methods of communication and cooperation.
Historical instances, such as the revelations of the U.S. National Security Agency’s surveillance programs, demonstrate how espionage can lead to strained relationships with allies. Such incidents highlight the fine line governments tread between security interests and maintaining diplomatic ties.
The interplay of espionage and diplomatic tensions shapes international relations, often resulting in a cycle of distrust, defensive posturing, and counterintelligence efforts. Nations must continuously navigate this complex landscape to mitigate risks while pursuing their geopolitical goals.
_____
Espionage between governments:
Espionage among nations is an exceptionally old and extensive human endeavour. In times of war and peace, a generous slice of states’ resources is allocated to intelligence organizations. Governmental espionage, often called “espionage between governments,” refers to spying by one government on another, primarily for intelligence gathering purposes like national security, foreign policy, or military strategy. This practice involves gathering secret information about a target government’s plans, activities, and vulnerabilities.
Why Governments Spy on Each Other:
- National Security:
Governments spy on each other to gather information about potential threats, including military capabilities, political instability, and terrorist groups.
- Foreign Policy:
Espionage helps governments understand the foreign policy goals and actions of other countries, allowing them to make informed decisions about international relations.
- Military Strategy:
Spy activities can provide information about the enemy’s military strength, deployment strategies, and vulnerabilities, which is crucial for military planning.
- Economic Intelligence:
Governments may also gather economic information about other countries to assess their economic strength and influence, as well as identify opportunities for trade or investment.
_
Examples of Espionage among nations:
- The Cold War:
During the Cold War, the US and the Soviet Union engaged in extensive espionage, with both sides gathering information on each other’s military, political, and economic activities.
- Modern Espionage:
Today, countries still spy on each other, using various methods like human intelligence (using spies), signals intelligence (intercepting communications), and cyber intelligence (hacking computer systems).
_____
Spying on the United Nations:
Spying on the United Nations refers to acts of espionage committed by state against the United Nations. The UN claims that acts of espionage on it are illegal under a number of international treaties, including the 1946 Convention on the Privileges and Immunities of the United Nations, the 1947 agreement between the United Nations and the United States, and the 1961 Vienna Convention on Diplomatic Relations. In one notable incident, the US and other Western countries were found to be spying on the UN in March 2003, in the run-up to the Iraq War, and actual bugging devices were found inside the UN. In 2010, leaked diplomatic cables revealed that US diplomats had been spying on UN leaders. On 25 August 2013, Der Spiegel revealed US National Security Agency secretly monitored the U.N.’s internal video conferencing system via decryption in 2012.
_____
Is it against international law to spy on mobile phone conversations of foreign heads of government?
Wiretapping is not per se regulated by international law; there is no explicit rule that prohibits espionage. But that doesn’t mean it’s allowed. Likewise, just because all countries are spying, you cannot conclude that there is a rule of customary international law that allows them to do so. The states know that spying is problematic. That’s why they do it secretly.
These practices may infringe on general principles of international law, such as the principle of state sovereignty. One facet of state sovereignty provides for non-interference in internal affairs. The internal communication between politicians, public officials and state authorities is part of those internal affairs. If public officials can’t have a confidential phone conversation anymore, this aspect of the sovereignty principle in international law is being violated. Another principle that could be affected is the distribution of state authority. As a general rule, a state is bound to its territory when it comes to the exercise of public authority. State-initiated wiretapping is an act of public authority. In Switzerland, it is illegal if somebody exercises acts on Swiss territory that would normally be acts of public authority.
______
Technologies and tactics used by countries to spy on each other:
It’s no secret most countries around the world are watching each other. China gave a brazen reminder of this when one of its suspected spy balloons traversed US airspace — before being shot down recently. The balloon captivated public attention for being a seemingly peculiar vehicle for espionage.
Photo below shows a jet flies in the sky past the Chinese spy balloon off the coast of South Carolina.
The Chinese spy balloon that flew across the U.S. was able to gather intelligence from several sensitive American military sites. The intelligence China collected was mostly from electronic signals, which can be picked up from weapons systems or include communications from base personnel, rather than images. US has since said China has used such surveillance balloons to target more than 40 countries on five continents.
_
NATO chief Jens Stoltenberg warned there had been increased Chinese intelligence activities in Europe, citing the use of satellites and cyber threats. Meanwhile, an audit found that Chinese government-linked equipment was found in hundreds of Australian Commonwealth buildings, including defence and foreign affairs offices. It prompted urgent calls for a plan to “rip” the hundreds of devices out of government sites. But in the vast and ever-evolving world of espionage, intelligence experts say China’s tactics aren’t particularly advanced. The Pentagon has also insisted the spy balloon did not give China an intelligence collection capability above what it already has via satellites and other means.
_
Information collection comes in various forms, whether it’s through “good old-fashioned” spies on the ground, signals, imagery, or cyber intelligence. But Kristian Gustafson, from Brunel University London’s Centre for Intelligence and Security Studies, said open source was where countries like the UK, US and Australia were increasingly honing their efforts. “We focus on the major, big things like a spy balloon, Earth observation satellites, or various types of space-based intelligence collection,” he says. “But variously, 70 to 90 per cent of usable intelligence for any state is based on open source material.” Open source isn’t necessarily hacked information, it often comes directly from what is published. There are sophisticated ways of analysing open information to get a sense of what a country is developing in regards to artificial intelligence (AI), hypersonics, or space-based observation, Dr Gustafson said. “Weapons development is based on pure research. It’s pure research that then gets weaponised,” he said. “It’s so obvious it’s often overlooked. The power of open-source information has been on display in Ukraine. Smartphone geolocation and high-res civilian and commercial satellite images from Maxar and Google have dramatically increased the volume and accessibility of valuable intelligence. “Not only have we multiplied the amount of Earth observation, but we’ve made it accessible to a massive number of people,” Dr Gustafson said. For instance, in the lead-up to Moscow’s full-scale invasion, imagery from Maxar and collected social media posts portrayed a very public build-up of Russian forces.
Although they tried, it made it difficult for Russia to refute its intentions. “It makes traditional kinds of denial and deception — the normal practice of trying to hide what you’re doing from an adversary — much harder,” Dr Gustafson said.
________
Nation State Cyber Espionage [see section five above, introduction to cyber espionage]:
Espionage between nation-states is hardly a new phenomenon, but in the last few decades the world had moved into a whole new realm of spying: cyber espionage. This new form of espionage is affecting the economic and political relationships between nation-states as well as changing the shape of modern warfare. Therefore, in spite of the advantages brought about by modern technology, there is a whole new set of problems as well. Although many countries all over the world are committing cyber espionage, the United States, Russia, and
China are considered the most advanced and most prolific cyber spies.
Current Trends:
There are two major trends associated with modern nation-state cyber espionage that have shaped not only the landscape of cyberspace but also public perception of cyber espionage and warfare.
The first of these is that cyber espionage is becoming more advanced, effective, and professional. This is only natural, of course, as our world becomes increasingly dependent on computers, but it is no less disturbing to see that crime and espionage are migrating to the digital world as well. The level of advancement associated with recent cyber operations leaves little doubt that these operations could only have been carried out by large, powerful entities, namely a few specific governments with the power and resources to devote to developing such tools. An example of this trend and a major turning point in cyber espionage was the discovery of the Stuxnet virus in 2010.
This leads to the second trend in nation-state cyber espionage: cyber espionage is becoming an accepted, and even preferred means of warfare. That is not to say that cyber espionage will replace traditional means of warfare, but it is already affecting the nature of nation-state conflict. This shift began with the Cold War, when the United States and Russia focused their efforts on covert information gathering over outright warfare. Because all-out war between major world powers has become less acceptable in the modern world, it makes sense that a preference for more furtive strategies has continued into the 21st century. In the last few decades especially, as technology has become more advanced, cyber espionage tools have become indispensable to modern military operations.
_
Arguably the most famous cyberattack in recent years has been the Stuxnet virus, which was discovered in 2010. Stuxnet specifically targeted Iranian nuclear facilities and was designed to take over computer systems that control and monitor physical hardware in these facilities. Stuxnet was a surprise because it was highly sophisticated and because it was the first major cyberattack that could inflict damage on the physical world as well as the digital world. Three other major espionage tools have also been discovered that seem to link to Stuxnet. The first is Gauss, discovered in 2012, which steals passwords and other data. The second is Flame, which is able to take over drivers, screenshots, Skype, and Bluetooth functions, and can monitor a computer’s keyboard and network traffic. And the third is DuQu, the sneakiest of these four, which simply waits silently in the background, collecting data. Expert analysts believe because of the sophistication of these viruses and the similarities in their code, that these four viruses were created by the same world power, mainly the United States or Israel, though neither country has claimed responsibility for them.
_
The fact that cyber espionage is starting to play an increasingly important role in modern warfare can be seen in the way cyberattacks have been used by Russia in recent conflicts. In 2007, in response to Estonia removing a proSoviet Union statue, Russia launched a massive DDoS attack on Estonia that shut down service to major websites and disrupted communication across the country. Again in 2008, before Russia sent troops into Georgia, it first used DDoS attacks to shut down communication systems, effectively cutting off Georgia from the outside world. This was the first time that cyber espionage had been used in conjunction with traditional warfare. Even more recently, Russia again used this tactic in 2014, when it first disabled Ukraine’s mobile phone communications before employing traditional battlefield methods. Russia has also been using cyber espionage against the United States for many years. One example of this is the Moonlight Maze virus, discovered in late 1999. This virus had spent two years stealing confidential information from the Department of Defense, the Department of Energy, NASA, and military contractors [Schaap]. This may seem like ancient history, but another attack, the socalled “Red October” malware, was discovered in 2012. This malware exploited vulnerabilities in Microsoft Word and Excel to infiltrate computer systems of foreign nations and gather secure data. Most of the targets were former Soviet countries in Eastern Europe, but the Red October malware was discovered in dozens of countries all over the world. The most worrisome part of this attack, however, is that this malware lurked in these systems for as long as 5 years before finally being discovered. This latest example shows that although Russia may seem quiet on the cyber warfront, in reality it is more active than it appears.
_
Cyber espionage does not take place only in the realm of warfare. Nation-states are employing cyber tools against each other to steal economic and financial data as well. China seems more interested in using confidential information for economic gain, rather than political advantage. According to United States government reports, thus far the energy, finance, information technology, and automotive industries have experienced attacks originating from China. Commercial industries that have links to military technology and newspapers like The New York Times, The Wall Street Journal, and The Washington Post were also targeted. Most of these attacks are unsuccessful, though many companies do not disclose when they have been attacked, meaning China’s success rate could be higher than it appears.
_______
Chinese Espionage in the United States:
The Chinese government has a large, well-developed, and aggressive state intelligence system. The main Chinese government agencies devoted to state espionage are the Chinese Ministry of State Security (MSS) and the PLA. In addition, they have a large variety of programs that likely incentivize commercial espionage. Thus, the scale of Chinese intelligence operations is potentially much larger than the size or effectiveness of its government intelligence agencies would suggest. It should be noted that the incidents of Chinese espionage far outnumber those by any other country, even Russia. The long-term cost to the American economy and national security cannot be precisely measured, but estimates run into the billions of dollars for commercial and technological espionage. Chinese espionage also created immeasurable damage to national security with the theft of weapons technology, including nuclear weapons test data. In the last few years, China has added the theft of massive quantities of personal information, political coercion, and influence operations, to its espionage activities. It is worth noting that while nationality is a predictive factor for espionage, ethnicity is not. Chinese nationals who come to the US to work or study are a fertile ground for recruitment. Often they intend to return to China or have close family members resident in China, making them more susceptible to coercion. In contrast, Americans of Chinese descent are very unlikely to be recruited. The espionage problem is the result of the increasingly hostile policies of China’s ruling Communist Party. Hacking is China’s preferred mode of espionage.
_
Until recently, the United States probably lost between $20 billion and $30 billion annually from Chinese cyber espionage. This does not count the losses from traditional espionage (e.g., using agents). The cumulative cost may reach $600 billion, since this kind of espionage has been going on for more than two decades. Any estimate has to take into account that some stolen IP cannot be turned into products, making the loss in these instances zero. In other cases, however, the victim company suffers revenue losses for years to come. Chinese companies are getting an illegal “subsidy”; they can spend less on R&D, since they can access U.S. research. The range of Chinese economic espionage, from simple household goods like wooden furniture and house paint to the most advanced high-tech products, is part of the explanation for China’s rapid growth. Cyber espionage accounts for a majority (but not all) of IP theft. For some companies, the cost of Chinese IP theft can be fatal (when combined with other business problems). There is also an effect on employment. Research by the International Trade Administration and the European Union found that that $1 billion in exports created roughly 6,000 jobs. Chinese IP theft reduced U.S. exports, meaning the United States could have lost thousands of jobs annually. China has sought to acquire U.S. technology by any means, licit or illicit, since Deng Xiaoping opened China to the West. Espionage and theft were part of this, but so were forced technology transfers or mandatory joint ventures as a condition for doing business in China. China’s development in automotive, aircraft, information technology, high-speed trains, and defense industries all benefitted from espionage. Many U.S. companies yielded to these forced transfers, calculating that the immediate benefit of access to China’s market outweighs the eventual loss. After 30 years, those chickens have come home to roost. Companies also calculated that they could shield their most valuable technologies and that the technologies would have moved to a new generation by the time the Chinese were able to enter the market. These strategies were partially successful, but they worked better when China was less developed. Now that it is the second-largest economy in the world, what was tolerable before is no longer acceptable.
_______
Spying is Kremlin’s secret tool in its war against the West:
Russian illegal agents have often used Latin American countries such as Argentina, Peru, or Brazil to create their new identities, making deceased babies disappear from the registers to steal their names, bribing civil registry officials in remote provinces to obtain certificates, and taking advantage of the cultural mix of a varied and multicultural continent. The case of the couple who posed as Argentines and whose children did not know they were Russian before being exchanged in a prisoner swap shows the importance that Vladimir Putin places on deep-cover agents as seen in figure below.
When Anna Dultseva and Artem Dultsev spoke to reporters from one of Moscow’s biggest television stations to praise the authorities that had rescued them from a Slovenian prison, they did so in very rusty Russian. The married couple, spies in the service of the Kremlin and two of the protagonists of the largest prisoner exchange between Russia and the West since the Cold War, have spent so much time clinging to their false identity — that of an enterprising Argentine couple based in Slovenia — that their mother tongue has suffered. Their children, an 11-year-old girl and an 8-year-old boy, who have been raised at home in Spanish, don’t speak it at all. For spies in such deep cover, speaking Russian, thinking in Russian and even dreaming in Russian is strictly forbidden. And they train for years to perform their duties.
These are agents who work under a false identity — most of the time with foreign citizenship and with no ties to Russia — and without the diplomatic cover that legal spies — those linked to embassies and other governmental organizations who enjoy immunity if they are uncovered — are afforded.
A fundamental espionage tool in the era of the Soviet Union, illegal spies have never ceased to be part of Moscow’s playbook in its war against the West. Kremlinologists believe that Russian President Vladimir Putin, who was a spy in the Soviet KGB and later head of its successor agency, the FSB, revitalized the program and has always held special respect for such operatives. The training and education of a good illegal spy, recounted Soviet spy master Yuri Drozdov, can take up to a decade. One of the most famous was Rudolf Abel, arrested in New York in 1957 and exchanged with the USSR for American pilot Gary Powers on a Berlin bridge in 1962, an episode that would inspire the movie Bridge of Spies.
Note:
Spy swaps are example of surveillance diplomacy and nonformal modes of enforcement. The U.S. and the Russians (and the Soviets before them) have engaged for years in spy swaps. What are these swaps? They represent a complete departure from the criminal process. After all, the spy is convicted and sentenced, and yet their prison sentence is sweetened to advance broader political and diplomatic goals—in bringing back our spies.
______
______
Section-11
Industrial/corporate and economic espionage:
_
Corporate espionage:
Industrial espionage, also known as corporate espionage, is a form of espionage conducted for commercial purposes instead of purely national security. While political espionage is conducted or orchestrated by governments and is international in scope, industrial or corporate espionage is more often national and occurs between companies or corporations. It may include the acquisition of intellectual property, such as information on industrial manufacture, ideas, techniques and processes, recipes and formulas. Or it could include sequestration of proprietary or operational information, such as that on customer datasets, pricing, sales, marketing, research and development, policies, prospective bids, planning or marketing strategies or the changing compositions and locations of production. It may describe activities such as theft of trade secrets, bribery, blackmail and technological surveillance. As well as orchestrating espionage on commercial organizations, governments can also be targets – for example, to determine the terms of a tender for a government contract. Reportedly Canada is losing $12 billion and German companies are estimated to be losing about €50 billion ($87 billion) and 30,000 jobs to industrial espionage every year. Corporate espionage techniques are delineated above in section eight (spy tactics).
_
Corporate espionage is stealing proprietary information, trade secrets, or intellectual property from a business and giving or selling it to another. The primary intent behind corporate espionage is to use the acquired information to gain a competitive advantage. Competitive intelligence differs from corporate espionage because it does not involve acquiring information using unethical or illegal methods. Corporate espionage is not legal. Such activities are based on unlawful methods. Whereas gathering non-confidential information by attending industry events or via open-source research is legal, stealing confidential information from competitors is not. Depending on the severity of the offense and the laws violated, individuals involved in industrial espionage might face criminal charges such as theft, fraud, or economic espionage. Penalties could include imprisonment, fines, or both. Laws and penalties for corporate espionage vary across different countries. As an example, the Economic Espionage Act of 1996 in the US criminalizes the theft or misappropriation of trade secrets for economic benefit. Penalties can include up to 15 years in prison and fines up to $500,000. Similarly, the Trade Secrets Directive (2016/943/EU) standardizes the legal protection of trade secrets throughout the European Union. Unfortunately, detecting and proving industrial espionage and holding perpetrators accountable can be challenging, especially when it involves intangible information like trade secrets.
_
Industrial/corporate versus economic espionage:
To clarify what we are talking about here, definitions of industrial espionage and economic espionage are in order. Industrial espionage is defined as an individual or private business entity sponsorship or coordination of intelligence activity conducted for the purpose of enhancing a competitor’s advantage in the marketplace.
According to the FBI, economic espionage is defined as “government-directed, sponsored, or coordinated intelligence activity, which may or may not constitute violations of law, conducted for the purpose of enhancing that country’s or another country’s economic competitiveness.” In other words, industrial/corporate espionage is between industries/corporations while economic espionage is between nations and state sponsored.
_
The larger umbrella of corporate espionage comprises several different forms of action. The two most common types include:
- Intellectual property acquisition – Intellectual property (IP) acquisition – also known as IP theft – is the act of stealing unique inventions, ideas or information from other parties for profit, financial or otherwise. Today’s hyper-innovative, globally-competitive market demands fresh ideas, novel information and new processes, which makes IP acquisition a very dangerous threat. Thieves loot another party’s IP to gain a competitive edge, monetize a product or steal the “secret sauce” that drives a certain company’s success. Organizations must keep IP theft at bay to avoid productivity issues, revenue loss and other long-term damage to their brand and viability.
- Trade secret theft – A trade secret is considered any type of information that’s not public that holds potential economic value to the organization to which it belongs. Employees create, move and share trade secrets at a regular cadence, which makes them especially hard to protect. Emails, text messages, browser histories, personal drives and more can all contain trade secrets that malicious actors want to steal. Since it’s difficult to tell when and where trade secrets move, exposure can happen without a trace.
_
Industries commonly affected by Corporate Espionage:
Technically, any business in any industry can fall victim to corporate espionage. However, there are a few that are more commonly affected than others:
- Computer software – Businesses that design and publish computer software develop novel and valuable products, which makes them greater targets of corporate espionage.
- Manufacturing – Attackers often attempt to steal information from companies that design and build technology products about how they craft their hardware.
- Biotechnology – Foreign attackers use both corporate and economic espionage to steal sensitive information and data around advanced manufacturing, robotics and chemicals.
- Aerospace – Avionics and aircraft designs are among two of the most common trade secrets exposed and stolen in aerospace espionage acts.
- Chemical – Industrial spies target chemical companies for their customer details, marketing plans and product trade secrets for a significant advantage over competitors.
- Financial – In the financial sector, data is even more valuable than cash, especially since data can be moved anonymously.
- Retail – The highly competitive retail industry and companies within it lack adequate cybersecurity — thus making it a frequent target for espionage attacks. Within the retail space customer details, financial information, marketing plans are all often at risk.
_
Business harms due to corporate espionage:
Unauthorized access to trade secrets, intellectual property, and other sensitive information can have a profound and far-reaching impact on your business. Potential negative consequences include:
- Loss of competitive advantage. Losing confidential information can cripple your company’s competitive edge. Competitors with access to stolen secrets can develop similar products or marketing strategies, making it difficult for your business to compete.
- Reputational damage. A successful business espionage attack can damage your organization’s reputation for innovation and security. This can erode customer trust and make it harder to attract investors and partners.
- Legal implications. Depending on the nature of the stolen information, you may face legal ramifications. These could include lawsuits from investors or partners who also suffered from the espionage attack on your organization.
- National security risks. In some cases, industrial espionage can have national security implications. Stolen information related to defense technologies or sensitive government projects could pose a threat to national security.
- Financial loss. The most common consequence of industrial espionage is the loss of intellectual property, which can lead to significant financial losses. Other consequences such as reputational damage and legal issues may also erode market shares and reduce profits.
The severity of the consequences depends on the type of information stolen and how it’s used. Ultimately, industrial espionage can harm any business, causing financial losses, hindering competitiveness, and damaging reputation.
_
High-Profile Corporate Espionage Cases:
It doesn’t matter how mature or well-recognized a company is – an organization of any size can experience a corporate espionage attack. That being said, there are several well-known corporate espionage cases that you may remember after seeing these big names in the news headlines:
- Google – Back in 2010, Google’s China operation was attacked by hackers who accessed the Gmail account information of Chinese human rights activists and managed to steal IP. This was a shocking incident, as it proved the tech giant wasn’t impervious to malicious actors.
- Oracle – In 2000, Oracle was caught (and admitted to) spying on Microsoft to uncover if their independent advocacy groups were, in reality, shell organizations financed by Microsoft. Oracle stole Microsoft’s garbage to access their trade secrets.
- Amazon – Amazon fell victim to corporate espionage by way of insider theft in 2020, when an employee exposed customer email addresses to a third party.
- Coca-Cola – Another incident of insider theft occurred in 2021, when a Coca-Cola employee was convicted for selling trade secrets regarding bisphenol-A (BPA). She photographed sensitive company information with her cell phone to circumvent the company’s security measures.
- Gillette – After being demoted to a lower position in 1997, a disgruntled Gillette subcontractor sent trade secrets to several rivals.
______
______
Economic Espionage:
Economic espionage refers to the act of stealing trade secrets, proprietary information, intellectual property (IP), or confidential business strategies from companies, governments, or institutions to use it to gain a competitive advantage, often for the benefit of another country and it is state sponsored. This form of espionage is focused on economic, rather than national security interests and can involve a wide range of activities, including cyber hacking, surveillance, bribery, and infiltration by corporate spies.
- Targets and Tactics: The primary targets are trade secrets, confidential business plans, innovative technologies, manufacturing processes, and other forms of intellectual property. Tactics can range from cyber hacking and insider threats to surveillance and the exploitation of business relationships.
- Legal Framework: Various countries have enacted laws specifically aimed at combating economic espionage. For example, the United States has the Economic Espionage Act of 1996, which makes the theft or misappropriation of a trade secret a federal crime if the act benefits a foreign government, foreign instrumentality, or foreign agent.
- Impact on Businesses and National Security: The impact of economic espionage can be profound, affecting not just the competitive edge and financial standing of companies but also national security. In sectors like defense, energy, and telecommunications, the theft of proprietary technology can compromise a country’s technological superiority and infrastructure resilience.
- International Relations and Trade: Economic espionage often strains relations between countries, leading to diplomatic conflicts and affecting international trade. Actions taken by governments against suspected espionage, such as sanctions, trade restrictions, or legal action, can have wide-ranging implications for global commerce and diplomacy.
- Cyber Espionage: With the proliferation of digital technology, cyber espionage has become a predominant method for conducting economic espionage. Hackers can infiltrate company networks to steal data, often with sophisticated malware or through social engineering tactics. These cyber activities are increasingly linked to state actors, complicating the international cybersecurity landscape.
- Countermeasures: Companies and governments invest heavily in countermeasures to protect sensitive information. These include cybersecurity defenses, counterintelligence operations, and legal actions. There is also a growing emphasis on awareness and training to mitigate insider threats and safeguard against social engineering tactics.
_
Foreign economic espionage against the United States continues to represent a significant threat to America’s prosperity, security, and competitive advantage. Cyberspace remains a preferred operational domain for a wide range of industrial espionage threat actors, from adversarial nation-states, to commercial enterprises operating under state influence, to sponsored activities conducted by proxy hacker groups. Next-generation technologies, such as Artificial Intelligence (AI) and the Internet-of-Things (IoT) will introduce new vulnerabilities to U.S. networks for which the cybersecurity community remains largely unprepared. Building an effective response will require understanding economic espionage as a worldwide, multi-vector threat to the integrity of the U.S. economy and global trade. China, Russia, and Iran stand out as three of the most capable and active cyber actors tied to economic espionage and the potential theft of U.S. trade secrets and proprietary information. Countries with closer ties to the United States also have conducted cyber espionage to obtain U.S. technology. Despite advances in cybersecurity, cyber espionage continues to offer threat actors a relatively low-cost, high-yield avenue of approach to a wide spectrum of intellectual property.
_
China is considered to be the Most Active Perpetrator of Economic Espionage:
The U.S. Department of Justice reports that China is involved in more than 80% of economic espionage cases prosecuted by the Department of Justice as of 2021. Over the years, the Chinese government has advanced its economy with Western technology and resources. It is believed that Chinese economic espionage is fueled by China’s desire to be the economic and technological leader of the world, displacing the United States.
China has expansive efforts in place to acquire U.S. technology to include sensitive trade secrets and proprietary information. It continues to use cyber espionage to support its strategic development goals—science and technology advancement, military modernization, and economic policy objectives. China’s cyberspace operations are part of a complex, multipronged technology development strategy that uses licit and illicit methods to achieve its goals. Chinese companies and individuals often acquire U.S. technology for commercial and scientific purposes. At the same time, the Chinese government seeks to enhance its collection of U.S. technology by enlisting the support of a broad range of actors spread throughout its government and industrial base.
China’s Strategic Goals are depicted in figure below:
The Intelligence Community and private sector security experts continue to identify ongoing Chinese cyber activity. Most Chinese cyber operations against U.S. private industry that have been detected are focused on cleared defense contractors or IT and communications firms whose products and services support government and private sector networks worldwide. Examples of identified ongoing Chinese cyber activity include the following:
-1. According to several cyber intelligence companies, in 2017 the China-associated cyber espionage group APT10 continued widespread operations to target engineering, telecommunications, and aerospace industries. APT10 targeted companies across the globe, including the United States, using its exploitation of managed IT service providers as a means to conduct such operations. Cybersecurity researchers have found links between Chinese cyber actors and a back door in the popular CCleaner application that allowed the actors to target U.S. companies, including Google, Microsoft, Intel, and VMware.
-2. In November 2017, PricewaterhouseCoopers (PWC) reported that the China-based APT, known as KeyBoy, was shifting its focus to target Western organizations. According to PWC, the targeting likely was for corporate espionage purposes. KeyBoy previously focused on Asian targets, according to commercial cybersecurity reporting.
-3. According to FireEye, in 2017 TEMP.Periscope continued targeting the maritime industry as well as engineering-focused entities including research institutes, academic organizations, and private firms in the United States. FireEye has detected sharp increases in targeting in early 2018 as well.
_______
_______
Section-12
Academic and nuclear espionage:
The term academic espionage can be defined as violating core principles of integrity by the practice of obtaining, using, or distributing the information, data, or methods that are used in the university’s research enterprise through unethical, dishonest, or illegal means to unauthorized individuals, companies, or nation states. Academic espionage poses threats to the university community through risks associated with the integrity of the research enterprise (violations of responsible and ethical conduct of research; actions that undermine peer review and grant award processes), risks to economic security (hidden diversions of research and/or resources that weaken the innovative base and threaten economic competitiveness) and risks to host national security. In the shadowy world of espionage, the battlefield is no longer confined to dimly lit alleys or distant war zones — it’s unfolding on university campuses. Amid the vibrant hum of academia, foreign intelligence operatives have found fertile ground for covert operations. The blend of cutting-edge research, access to sensitive information, and ambitious scholars makes universities prime targets for espionage.
______
China infiltrated US universities:
Rather than resort to high-stakes spy games, China’s approach is slow, methodical, and often entirely legal — or at least, operating in legal gray zones. American research labs and university departments, funded by billions in taxpayer dollars through agencies like the National Institutes of Health (NIH), National Science Foundation (NSF), and Department of Defense (DoD), have become fertile ground for technology theft by China. Chinese nationals working at these institutions have repeatedly been caught transferring sensitive data, proprietary algorithms, and advanced research back to China. In some cases, professors themselves — either of Chinese descent or with lucrative ties to Chinese institutions — have been co-opted into talent recruitment programs in China which incentivizes scientists to share or replicate American breakthroughs on Chinese soil.
_
One of the key instruments of infiltration by the Chinese state in American universities has been the Chinese Scholarship Council (CSC), which funds thousands of Chinese students to study abroad. Many of these scholarships come with ideological and political strings attached. Recipients are often required to report back to Chinese embassies, sign loyalty pledges, and in some cases, participate in intelligence-gathering efforts. These arrangements are rarely disclosed to US universities. Programs such as the “Thousand Talents Plan” and “Ten Thousand Talents Program” were launched by China to lure Chinese scientists and engineers working abroad back to China, often while they remained employed at US institutions. Launched in 2008, the Thousand Talents Plan was one of the CCP’s most audacious projects, offering grants, lab access, and prestige to researchers who agreed to funnel intellectual property back to China. While framed as a way to reverse brain drain and attract overseas Chinese talent, the program quickly became a vehicle for tech transfer—drawing scrutiny from U.S. intelligence agencies and university administrators alike. In several high-profile cases, American academics failed to disclose their affiliations with the program while simultaneously receiving U.S. federal research grants—a clear conflict of interest and, in some cases, fraud.
Perhaps the most insidious method has involved Chinese military-affiliated researchers entering US universities under civilian pretences. A 2020 report by the Australian Strategic Policy Institute estimated that hundreds of PLA scientists conducted research at American institutions. Some deliberately concealed their ties to military organizations, gaining access to sensitive technologies in fields like quantum computing, artificial intelligence and biotechnology.
Many American universities, especially elite research institutions, have often turned a blind eye to these activities, driven by their own incentives: foreign student tuition, international partnerships, and access to global talent. Many institutions welcomed funding from Chinese universities and institutions, even those known to be affiliated with the Chinese military. Some administrators ignored red flags to preserve relationships or out of fear of appearing xenophobic.
_
The CCP’s Strategy:
According to Stanford experts on Chinese intelligence-gathering efforts who wished to remain anonymous, the Chinese Communist Party (CCP) has employed a ‘crowdsourced approach’ to gathering information at Stanford. Dubbed ‘non-traditional collection,’ the Chinese Ministry for State Security (MSS) uses civilians unaffiliated with the intelligence community to acquire and report sensitive information. The aim of non-traditional collectors isn’t necessarily to steal classified documents but rather to quietly extract the know-how behind American innovation.
A China expert, familiar with Stanford, who wished to remain anonymous, confirmed that of the approximately 1,129 Chinese International students on campus, a select number are actively reporting to the Chinese Communist Party (CCP). China’s 2017 National Intelligence Law mandates that all Chinese citizens support and cooperate with state intelligence work regardless of location. Article 7 of this law enforces compliance: “Any organization or citizen shall support, assist, and cooperate with state intelligence work in accordance with the law, and keep the secrets of the national intelligence work from becoming known to the public.” These laws leave Chinese students no option but to accept the demands of the CCP. Students engaged in sensitive scientific research, especially in fields like AI and robotics, are those most often targeted.
Many Chinese [nationals] have handlers; they [CCP] want to know everything that’s going on at Stanford. This is a very normal thing. They just relay the information they have. The Chinese government spends a lot of time collecting data on its overseas students; it has a pretty good understanding of who is doing what and if someone is working in an area of interest [frontier technology]. If students have access to things the government would like access to, it is relatively easy to reach out to an individual. They use carrots and sticks. If you turn over information, you may get a reward; if you don’t, there is a punishment. Chinese nationals with family members in China are coerced into sharing sensitive information with the most harrowing of punishments on their families if they refuse to do so. They are often told that it is in the best interest of both them and their families to provide research data that would not typically be disclosed.
_
Prominent cases of Chinese students and researchers working as spies:
Many Chinese students and researchers were found stealing technology for China. The decision to revoke visas of Chinese students with PLA/CCP ties comes in the wake of a large number of cases where students and researchers were found to be stealing technology for China or working on the behalf of China. Below are some of such cases compiled from various sources:
-1. While not Chinese himself, Charles Lieber, a prominent nanotechnology scientist and former chair of Harvard’s Chemistry Department, was deeply entangled in China’s academic espionage apparatus, along with two Chinese nationals, Yanqing Ye and Zaosong Zheng. In 2021, he was convicted of lying to federal authorities about his financial ties to China’s Thousand Talents Plan and receiving $50,000 per month from Wuhan University of Technology. Lieber’s case exposed how even elite institutions can become complicit in technological transfer, wittingly or not.
-2. Yanqing Ye, a lieutenant in the People’s Liberation Army, entered the United States on a student visa and studied at Boston University’s Department of Biomedical Engineering. According to the FBI, she maintained active military status while conducting research and was tasked with gathering intelligence on U.S. military sites. She fled to China before facing prosecution. Her case highlighted the difficulty in vetting student identities and affiliations.
-3. Wang Xin, a researcher in the medical sciences at the University of California, was discovered in 2020 to be an active PLA technician. He attempted to smuggle biological samples back to China and misrepresented his military status on visa applications. According to court documents, his mission included gathering information on American lab design and medical innovations. After being apprehended at the airport, he confessed his military assignment and was deported.
-4. Song Guo Zheng, a professor of internal medicine at Ohio State University and Pennsylvania State University, pled guilty in 2020 to making false statements to federal authorities as part of a scheme to use over $4 million in grants from the NIH to develop China’s expertise in rheumatology and immunology through his undisclosed partnership with a Chinese university controlled by the Chinese government.
-5. Saw-Teong Ang, a University of Arkansas professor, was indicted in 2020 for wire fraud for his acceptance of U.S contracting funds related to NASA and the Air Force while being employed by Chinese entities.
-6. Zhengdong Cheng, a professor at Texas A&M, was charged in 2020 with wire fraud for concealing his affiliation with Chinese universities and enterprises while accepting a NASA grant. His position allowed him access to sensitive NASA projects. He was a participant of the Thousand Talents Plan.
-7. Guan Lei, a researcher at the University of California at Los Angeles, was charged in 2020 with destruction of evidence during an FBI investigation. Guan is being investigated for transferring sensitive software and other technical data to the PLA and China’s National University of Defense Technology.
-8. Former University of Florida professor Lin Yang was indicted in 2021 on charges of committing wire fraud and making false statements regarding a $1.75 million grant from the National Institutes of Health (NIH). The indictment alleges Yang concealed a business he established in China promoting a product he created using the NIH grant and applying to join China’s Thousand Talent Program.
-9. Visiting Stanford researcher Chen Song was indicted in 2021 for obstruction, alteration of records, visa fraud charges and false statements regarding her status as a member of the PRC military forces while conducting brain disease research in the United States.
-10. University of Arkansas Professor, Simon Saw-Teong Ang, pleaded guilty in 2022 to making a materially false and fictitious statement and representation to an FBI Special Agent for failing to disclose his 24 Chinese patents to the university and to the FBI, when interviewed.
______
______
CIA secretly recruits academics:
In order to tempt nuclear scientists from countries such as Iran or North Korea to defect, US spy agencies routinely send agents to academic conferences – or even host their own fake ones. In perhaps its most audacious and elaborate incursion into academia, the CIA has secretly spent millions of dollars staging scientific conferences around the world. Its purpose was to lure Iranian nuclear scientists out of their homeland and into an accessible setting, where its intelligence officers could approach them individually and press them to defect. In other words, the agency sought to delay Iran’s development of nuclear weapons by exploiting academia’s internationalism, and pulling off a mass deception on the institutions that hosted the conferences and the professors who attended and spoke at them. The people attending the conference had no idea they were acting in a drama that simulated reality but was stage-managed from afar. Whether the national security mission justified this manipulation of the professoriate can be debated, but there’s little doubt that most academics would have balked at being dupes in a CIA scheme.
_
The importance of a conference may be measured not just by the number of Nobel prize-winners or Oxford dons it attracts, but by the number of spies. US and foreign intelligence officers flock to conferences for the same reason that army recruiters concentrate on low-income neighbourhoods: they make the best hunting grounds. While a university campus might have only one or two professors of interest to an intelligence service, the right conference – on drone technology– could have dozens. Every intelligence service in the world works conferences, sponsors conferences, and looks for ways to get people to conferences. Intelligence from academic conferences can shape policy. It helped persuade the George W Bush administration –mistakenly, as it turned out – that Saddam Hussein was still developing weapons of mass destruction in Iraq. “What our spies and informants were noticing, of course, was that Iraqi scientists specialising in chemistry, biology and, to a lesser extent, nuclear power kept showing up at international symposia,” former CIA counterterrorism officer John Kiriakou wrote in a 2009 memoir. “They presented papers, listened to the presentation of others, took copious notes, and returned to Jordan, where they could transmit overland back to Iraq.” Some of those spies may have drawn the wrong conclusions because they lacked advanced degrees in chemistry, biology or nuclear power. Without expertise, agents might misunderstand the subject matter, or be exposed as frauds.
______
______
Nuclear espionage:
Nuclear espionage is the purposeful giving of state secrets regarding nuclear weapons to other states without authorization (espionage). There have been many cases of known nuclear espionage throughout the history of nuclear weapons and many cases of suspected or alleged espionage. Because nuclear weapons are generally considered one of the most important of state secrets, all nations with nuclear weapons have strict restrictions against the giving of information relating to nuclear weapon design, stockpiles, delivery systems, and deployment. States are also limited in their ability to make public the information regarding nuclear weapons by non-proliferation agreements.
_
The Manhattan Project was an unprecedented, top-secret World War II government program in which the United States rushed to develop and deploy the world’s first atomic weapons before Nazi Germany. Espionage was one of General Groves’ main concerns during the Manhattan Project. For all of the attention paid to secrecy and counter-intelligence, spies were still able to penetrate the project and steal information about the atomic bomb. The Manhattan Project was infiltrated not by its enemies Germany and Japan, but by the Soviet Union. Soviet spies occupied positions of trust and importance in the Manhattan Project, and passed on valuable information about the bomb and its design. During the Manhattan Project, the joint effort during World War II by the United States, the United Kingdom, and Canada to create the first nuclear weapons, there were many instances of nuclear espionage in which project scientists or technicians channeled information about bomb development and design to the Soviet Union. These people are often referred to as the Atomic Spies, and their work continued into the early Cold War. Because most of these cases became well known in the context of the anti-Communist 1950s, there has been long-standing dispute over the exact details of these cases, though some of this was settled with the making public of the Venona project transcripts, which were intercepted and decrypted messages between Soviet agents and the Soviet government. Some issues remain unsettled, however.
The most prominent of these included:
- Klaus Fuchs – German refugee theoretical physicist who worked with the British delegation at Los Alamos during the Manhattan Project. He was eventually discovered, confessed, and sentenced to jail in Britain. He was later released, and he emigrated to East Germany. Because of his close connection to many aspects of project activities, and his extensive technical knowledge, he is considered to have been the most valuable of the “Atomic Spies” in terms of the information he gave to the Soviet Union about the American fission bomb program. He also gave early information about the American hydrogen bomb program but since he was not present at the time that the successful Teller-Ulam design was discovered, his information on this is not thought to have been of much value.
- Theodore Hall – a young American physicist at Los Alamos, whose identity as a spy was not revealed until very late in the 20th century. He gave implosion bomb details to a Soviet official at a U.S. Communist party meeting in New York. From then, he continued to give information about the hydrogen bomb to his Soviet contacts. He was never arrested in connection to his espionage work, though seems to have admitted to it in later years to reporters and to his family. Near the end of his life, he admitted that he abhorred the idea of the United States holding overwhelming power over the world’s nuclear stockpile and believed all nations should have the same amount of atomic knowledge.
- David Greenglass – an American machinist at Los Alamos during the Manhattan Project. Greenglass confessed that he gave crude schematics of lab experiments to the Russians during World War II. Some aspects of his testimony against his sister and brother-in-law (the Rosenbergs, see below) are now thought to have been fabricated in an effort to keep his own wife from prosecution. Greenglass confessed to his espionage and was given a long prison term.
- George Koval – The American-born son of a Belarusian emigrant family that returned to the Soviet Union where he was inducted into the Red Army and recruited into the GRU intelligence service. He infiltrated the US Army and became a radiation health officer in the Special Engineering Detachment. Acting under the code name DELMAR he obtained information from Oak Ridge and the Dayton Project about the Urchin (detonator) used on the Fat Man plutonium bomb. His work was not known to the west until he was posthumously recognized as a hero of the Russian Federation by Vladimir Putin in 2007.
- Ethel and Julius Rosenberg – Americans who were supposedly involved in coordinating and recruiting an espionage network which included David Greenglass. While most scholars believe that Julius was likely involved in some sort of network, whether or not Ethel was involved or cognizant of the activities remains a matter of dispute. Julius and Ethel refused to confess to any charges, and were convicted and executed at Sing Sing Prison.
- Harry Gold – American, confessed to acting as a courier for Greenglass and Fuchs.
_
While the spies mentioned previously have become infamous for their actions, more Los Alamos spies have been identified in recent years due in part to the FBI releasing previously classified documents. Other spies have become more known after being overlooked by historians. Most Soviet spies were properly convicted, but several evaded indictment due to a lack of evidence. In the case of Arthur Adams, he was watched by the FBI for many years before his escape to the Soviet Union. The FBI had probable cause Adams was engaging in espionage, but critically lacked evidence to proceed against him. The same goes for his associate Clarence Hiskey who was able to live the rest of his life out in the United States even though he was questioned by the FBI several times. Oscar Seborer was the most prevalent case of this, with his involvement not being discovered until decades after his spy work. Documents will continue to be found and more information about these spies and other potential saboteurs will become public knowledge.
______
Nuclear espionage gave Pakistan atom bomb:
Pakistan nuclear scientist Abdul Qadeer Khan was revered as a hero in his country, but he was one of the most notorious nuclear smugglers in the world. He is considered responsible for nuclear proliferation as he smuggled technology to states like North Korea, Iran and Libya. In 1972, he began working at Physical Dynamic Research Laboratory (FDO), a subcontractor of Ultra Centrifuge Nederland (UCN). Soon after starting work at FDO, Khan paid unauthorised visits to the advanced UCN enrichment facility in Almelo, Netherlands, In I975, Khan abruptly left for Pakistan with copied blueprints for centrifuges and other components and contact information for nearly 100 companies. Khan was later convicted, in absentia, in Dutch court for conducting nuclear espionage and sentenced to four years in prison. In the 1980s, Khan acquired blueprints for the Chinese bomb that was tested in China’s nuclear explosion in 1966. In 1998, India detonated a total of five devices in nuclear tests on May 11 and 13. Pakistan responded with six nuclear tests. In the years following the multiple nuclear tests in the Indian subcontinent, a massive global nuclear proliferation scandal came to light. Pakistan leadership came under massive pressure from the international community. Then Army chief and President Pervez Musharraf accused Khan of running a rogue proliferation network for nuclear material. Khan confessed in 2004 to have helped supply materials necessary for making nuclear weapons to North Korea and Libya. According to New York Times, Khan insisted that he alone was guilty, however, it is widely believed that Pakistan’s powerful military was complicit in this exceeding trade. Khan was pardoned and put under house arrest in 2004. But Pakistan was unable to hold to even that mild punishment. Pakistan Prime Minister Imran Khan said Dr Khan was loved by the nation because of his critical contribution to making Pakistan a nuclear weapon state.
_____
_____
Section-13
Spousal spying:
Spousal spying can take many forms. It may involve glancing over your spouse’s shoulder while they are sending a text message or putting hidden cameras in your home. Whether you are spying or being spied on, there are several things you should know about spousal spying, particularly in the context of a divorce case. Alarmingly, 40% of the divorce cases now include instances of one spouse spying on the other. A spouse may just be curious about who you’re talking to, how you are spending your money, or other private details of your life. Spousal spying can also have a more direct motive—such as gathering evidence that could be used against you in a divorce. For example, evidence that you’ve had an affair could have serious consequences in a divorce case, especially when it comes to an alimony award. Your spouse may also want to find out if you have secret bank accounts or if you are using marital funds for expenses that your partner doesn’t know about.
_
Emails, texts, and Facebook posts are being called on as evidence in an increasing number of divorce proceedings. But when it comes to collecting this kind of “cyber evidence” — what’s fair game, and what crosses the line? Spouses attempting to build a case for divorce can unknowingly expose themselves to criminal and civil liability in pursuit of the proverbial “smoking gun”. It almost goes without saying that uncovering evidence that a spouse or partner is having an affair or engaging in other lurid and/or improper behavior is often enough to precipitate the decision to file for divorce or dissolution of a civil union. Whether or not damaging emails, photos, and texts can be admitted as evidence in divorce or dissolution litigation, however, largely depends on how the information is collected. In today’s technology-driven world, the kind of spying taking place may involve any number of stealth “snooping” technologies, from computer spyware as a way to gain access to email or Facebook passwords to GPS-tracking smartphone apps. Spyware can be secretly installed on smartphones, tablets, and computers, allowing the controlling partner to read emails, text messages, and listen to phone calls. Software can also record keystrokes, giving the spouse access to passwords and other private information. Many spyware apps also have GPS tracking, allowing spouse to monitor their partner’s location in real-time, increasing their control.
_
Recognising the signs of a spying partner can be challenging, often leaving the victim in doubt, but there are some subtle indicators. These include:
- Unusual battery drain: Spyware often runs constantly in the background, leading to faster battery depletion.
- Increased data usage: Monitoring and data transmission by spyware can cause a significant spike in data usage.
- Strange device behaviour: Phones or computers may act erratically, including random reboots or slowdowns.
- Unexplained changes in settings: Partner might alter device settings to facilitate easier monitoring.
- Unexpected app installations: You discover unfamiliar apps or software installed on your device that you didn’t download or recognise.
- Problems with your device: Your device frequently crashes, shuts down unexpectedly, or exhibits other technical issues.
- Increased suspicion from your partner: Your partner seems unusually interested in your digital activities or devices, asking questions that seem intrusive.
_
Activities that may be illegal or constitute a violation of privacy include the following: (note that differences may occur by jurisdiction and State laws)
- Hacking password-protected accounts.
- Snooping on a spouse’s computer or phone that is owned by his or her place of work.
- Intercepting and/or recording cellular or cordless telephone calls between your spouse and another party that do not include you.
When it’s a matter of a stranger spying on you, the rules for what constitutes an invasion of privacy are pretty clear, but in cases of “inter-spousal” spying there can be significant gray areas. Even in a failing marriage, married couples often know a lot about each other’s business. You may share a computer. Some couples share online accounts, such as on social media. But the line between legal and illegal is drawn where one spouse has a reasonable expectation of privacy. A surreptitious intrusion into an area of someone’s life that they have intentionally kept separate and beyond your knowledge is spying. It could be illegal. For example, accessing a spouse’s password-protected account without permission would likely be considered illegal spying. The fact that the spouse took steps – the password – to ensure others could not access the account indicates that they had an expectation of privacy.
_
The misuse of technology to spy on a spouse is a form of coercive control that disregards people’s right to privacy. Recognising the signs of spyware, understanding the profound impact it can have, and taking strategic steps to be vigilant are unfortunately vital in the digital age. If you are going through a divorce and have suspicions about your spouse, speak to your divorce lawyer. Legal professionals and support networks can play an essential role in helping victims reclaim their privacy and autonomy, ensuring that technology serves as a tool for empowerment rather than oppression.
_____
_____
Section-14
Legality of Spying:
In the old world, there was an absolutist way of thinking about spying. Spying was either always legal, always illegal, or neither legal nor illegal, a.k.a., extra-legal.
For permissivists, spying was always legal. Chinese military strategist Sun Tzu said, “Spy, spy, and spy again.” English philosopher Thomas Hobbes believed spying was like “rays of light onto the human spirit.” He reasoned that a leader who chooses not to spy commits a dereliction of duty; they’re not protecting the polity from surprise attacks in a world where there’s growing uncertainty around safety and security. So any spying, no matter what the means or targets are, is always lawful.
A second approach was a prohibitionist approach—spying is always illegal. Philosopher Immanuel Kant promoted a perpetual peace and believed the way to achieve it was by building trust among nations. The thing that hurts that trust, he believed, were the lies, cheating, and deceiving that come with espionage. Kant thus called spying a diabolical act. So for Kant and those who took Kantian positions, the idea is that spying, no matter the reason, the means, or the targets, will always be illegal.
The third camp are those who’ve claimed that espionage and international law just start from opposite positions. International law is about the peaceful resolution of conflict. Spying is about lying, cheating, and deceiving. International law is about justice where justice was once trampled. Espionage is about circumvention of justice. Spying is also filled with dualities that make it hard to regulate. We tell our spies to violate the laws of other countries but to comply with ours. We treat spies as heroes at home but traitors abroad. All these dualities seem to suggest that there’s just something queer about this practice. Everyone’s doing it, but everyone’s saying it’s illegal under their own domestic legislation. So extra-legalist scholars suggest that spying is neither legal nor illegal; it’s outside the bounds of law.
_______
Under international law, the act of spying, or espionage, describes an act of information gathering that is clandestine or takes place under false pretences (API Art. 46). Spying, or espionage, is generally illegal under international law and the domestic laws of most countries. Espionage against a nation is a crime under the legal code of many world states. However, intelligence agencies like the CIA operate under a different framework that often involves a complex interplay of legality, national security, and international relations. Here are some key points to understand this situation:
National Sovereignty:
Each country has the right to protect its own national interests, which includes gathering intelligence. Countries often accept that espionage is a reality of international relations, even if it’s technically illegal.
Legal Framework:
The CIA operates under U.S. law, which provides it with the authority to conduct intelligence activities abroad. These activities are often justified under national security interests and are subject to oversight by the executive branch and Congress.
Reciprocity and Tolerance:
Many countries engage in espionage, and there is a tacit understanding that while spying is illegal, it is a common practice. Countries may turn a blind eye to espionage activities conducted by other nations, recognizing that they also engage in similar actions.
Geopolitical Context:
In a world where intelligence can provide significant advantages in diplomacy, military operations, and economic competition, countries often prioritize national security over strict adherence to laws against spying.
_
The United States in World War I passed the Espionage Act of 1917. Over the years, many spies, such as the Soble spy ring, Robert Lee Johnson, the Rosenberg ring, Aldrich Hazen Ames, Robert Philip Hanssen, Jonathan Pollard, John Anthony Walker, James Hall III, and others have been prosecuted under this law. In modern times, many people convicted of espionage have been given penal sentences rather than execution. For example, Aldrich Hazen Ames is an American CIA analyst, turned KGB mole, who was convicted of espionage in 1994; he is serving a life sentence without the possibility of parole in the high-security Allenwood U.S. Penitentiary. Ames was formerly a 31-year CIA counterintelligence officer and analyst who committed espionage against his country by spying for the Soviet Union and Russia. So far as it is known, Ames compromised the second-largest number of CIA agents, second only to Robert Hanssen, who also served a prison sentence until his death in 2023.
_____
In general, indiscriminate spying on individuals is considered a crime in India. The Supreme Court of India has ruled that such surveillance infringes upon the right to privacy. However, there are exceptions, such as when surveillance is necessary for protecting national security or interest and is proportional. Espionage is a crime under the legal code of many nations. The risks of espionage vary. A spy breaking the host country’s laws may be deported, imprisoned, or even executed. A spy breaking his/her own country’s laws can be imprisoned for espionage or/and treason (which can only occur if he or she take up arms or aiding the enemy against his or her own country during wartime), or even executed, as the Rosenbergs were. For example, when Aldrich Ames handed a stack of dossiers of CIA agents in the Eastern Bloc to his KGB-officer “handler”, the KGB “rolled up” several networks, and at least ten people were secretly shot. When Ames was arrested by the FBI, he faced life in prison; his contact, who had diplomatic immunity, was declared persona non grata and taken to the airport. Ames’s wife was threatened with life imprisonment if her husband did not cooperate; he did, and she was given a five-year sentence. Hugh Francis Redmond, a CIA officer in China, spent nineteen years in a Chinese prison for espionage—and died there—as he was operating without diplomatic cover and immunity. In United States law, treason and espionage are separate crimes.
_
Yes, espionage, which is the act of spying, is generally considered illegal, particularly in wartime and when directed against a nation or government. However, the legality of espionage in peacetime is less clear and can be more complex, especially in the context of cyber espionage.
The Practical Guide to Humanitarian Law defines espionage as clandestine information gathering or gathering information under false pretences.
Elaboration:
- Wartime Espionage:
During armed conflicts, espionage is a violation of international law, and individuals caught engaging in such activities may not have the right to prisoner-of-war status.
- Peacetime Espionage:
While some argue that peacetime espionage is also illegal, its legal status is not as clear-cut. The legality of peacetime espionage can be tricky to determine, especially when it comes to cyber espionage.
- Industrial Espionage:
The theft of trade secrets or other confidential business information for a competitor’s benefit is also considered illegal and unethical.
- Legal Protections:
Many nations have laws that criminalize espionage, and the penalties for being caught can be severe.
- Diplomacy:
Diplomatic and consular missions are protected by international law, and receiving states cannot engage in espionage against them.
_
Yes, there can be situations where the espionage campaign would be lawful, but particular choices around means and methods might not be. For example, in the leadup to catching Osama bin Laden, the CIA ran a sham hepatitis B vaccination program for children in Abbottabad, Pakistan. The idea was that somehow through the collection of DNA and blood samples, they’d be able to spot where bin Laden and his family were hiding.
The operation always had very little chance of success. Indeed, it didn’t succeed in finding bin Laden. Yet the operation caused a huge amount of collateral damage. When Pakistani families learned of the incident, they refused to vaccinate their children, with the Taliban even issuing a fatwa against vaccination programs and teams. To this day, local leaders in the region mischaracterize polio vaccination as a Western spying program. Imposing such a grave risk with such limited likelihood of success or high likelihood of harm should be prohibited.
_
Is cyber espionage legal?
The internet and lax cybersecurity practices have made cyber espionage easier, further complicating its legal status. During times of war, espionage against a nation is a crime under the legal code of many nations as well as under international law, and cyber espionage is no different. During peacetime, however, it can be a lot trickier to figure out when espionage crosses the line into illegality—all the more so for cyber spying. If cyber espionage does not cause any real-world physical damage, does it violate a nation’s territorial sovereignty? Where, in fact, does territorial sovereignty begin and end in cyberspace? These are just some of the questions being debated in international law regarding cyber espionage.
______
Legality of Electronic surveillance:
Electronic surveillance is a broad term that is used to describe monitoring another person’s actions or conversations without his/her knowledge or consent by using one or more electronic devices or platforms. Electronic surveillance can be done by misusing cameras, social media, or other tech. It can also involve stalkerware, also known as spyware, which can be installed on a computer, tablet, or smartphone. This allows someone to secretly monitor the activity on the device without the user’s knowledge. It can allow the spy person access to everything on the phone.
Whether electronic surveillance is legal or not may depend on whether the person doing the recording is part of the activity or conversation and your specific state’s laws on this issue.
If the person is part of the activity or conversation:
Many states allow someone to record a phone call, conversation, or activity as long as one person involved consents. This could be the person recording it who “gives consent.” Other states require that everyone who is part of the conversation or activity consents.
If the person is not part of the activity or conversation:
Depending on the state, there might be one or more laws that address:
- listening in on a private conversation;
- electronically recording a person’s conversation; and
- videotaping a person’s activities.
The names of these laws vary across countries, but they often include wiretap, voyeurism, interception, and other recording laws. Deciding which law(s) may apply to your situation can be tricky. It often depends on the circumstances of the surveillance and whether you had a “reasonable expectation of privacy” while the spy recorded or observed you. Legally, a reasonable expectation of privacy exists when you are in a situation where an average person would expect to not be seen or spied on. For example, a person in public places, such as in a football stadium or on a main street, may not reasonably expect privacy. A person in his/her bedroom or in a public restroom stall generally would.
Where is it legal to use spy cameras?
The use, sale and purchase of spy cameras are legal when they are used legally. One can use it for security purposes at home or in offices, to keep an eye on infants at home, record lawful entertainment like pranks, to collect evidence if the next person is corrupt or doing any illegal activity. While using at offices, stickers and disclaimers should be made visible that people are under surveillance.
______
Drone Spying Laws:
Drone spying involves using a drone to spy on someone or something without their knowledge. You can use your drone for commercial purposes, such as real estate photography or aerial photography for advertising purposes. Private citizens who want to take pictures of their property for personal use or security reasons can also use them. Drones are a great way to get a bird’s-eye view of the world, but you must follow specific rules when you fly them. Drone spying laws vary from state to state, so you must know the laws before attempting any drone spying operation.
-1. It’s illegal to fly drones over certain areas such as government buildings, airports, or anywhere else where you could interfere with air traffic.
-2. It’s illegal to fly a drone within a certain distance of an airport runway or helipad (typically about 5 km).
-3. It’s illegal to fly drones at night because other aircraft can’t see them and might crash into them.
-4. There are also some laws against flying drones near public events like concerts or sporting events, where many people may be watching from below.
The Federal Aviation Administration (FAA) has strict laws about how high drones can fly and how far away from airports they can be. Moreover, check with your town or city to make sure you’re following their rules.
Ensure you are familiar with the following laws to avoid getting fined or arrested for flying your drone illegally.
_____
Why DIY Spying is a Risky Move:
When emotions run high, it’s easy to act impulsively. But attempting to monitor someone on your own can lead to:
– Legal trouble. Recording or following someone without permission can violate privacy laws.
– Inadmissible evidence. If you gather evidence improperly, it won’t hold up in court.
– Escalated conflict. Personal surveillance often backfires, worsening an already tense situation.
_______
Privacy and civil liberties:
Regardless of the intelligence-gathering technique, the FBI follows all laws, policies, and procedures designed to protect the privacy of the American people.
Intelligence collection is governed by:
-The attorney general’s guidelines
-Procedures for national security investigations and foreign intelligence collection
-The U.S. Constitution
-Federal law
-Established criminal procedures
-Authorities controlled by U.S. court
______
Legality of Espionage during War versus Peace:
A person is considered a spy when, acting clandestinely or on false pretences, he obtains or endeavours to obtain military information in enemy-controlled territory. International law treats spying that occurs during wartime and peacetime differently. The rules on wartime spying focus on whether the information gathering is carried out through false pretences. In peacetime, the analysis centers on whether the methods of spying violate a State’s sovereignty.
_
In January 2023, the United States shot down a 200-foot balloon that had hovered for days over U.S. territory. The “spy balloon” incident heightened tensions between Washington and Beijing, prompting U.S. Sec. of State Antony Blinken to criticize China’s actions as “a clear violation of our sovereignty, a clear violation of international law, and clearly unacceptable.” A White House press statement similarly claimed the spy balloon violated U.S. sovereignty and international law. There is considerable debate about whether the spy balloon (and the U.S. shootdown of it) violated international law. But the incident also raises deeper questions about the legality and morality of espionage more broadly – questions policymakers must address as States rely on more subtle and pervasive forms of spying through artificial intelligence, mass surveillance, and cyber operations.
If you are applying the Chicago Convention, there are obvious restrictions against downing spy balloon. The U.S. is prohibited from resorting to the use of weapons against a civilian aircraft that poses no immediate threat.
So if the balloon was a civilian weather research aircraft, targeting it would be prohibited. Similarly, if the balloon was a military spy aircraft, as the U.S. contended, shooting it down would equally be prohibited because it’s entitled to sovereign immunity. But such a formalist and sterile analysis seems to be detached from reality. It avoids, for example, the need to ask more complex questions about what the Chinese were doing in Montana in the first place. So instead we might ask the more concrete questions of: What was the intention of the operation? What were the methods employed in this spying? Were they necessary, proportionate, efficacious?
_
Espionage During an International Armed Conflict:
Under customary international law and international humanitarian law (IHL) (codified in Additional Protocol (I) to the Geneva Conventions, Art. 46) espionage that occurs during an international armed conflict is carefully defined, though the precise methods of information gathering are not identified or prohibited. As the International Committee of the Red Cross notes, “espionage” is the “gathering or attempting to gather information in territory controlled by an adverse party through an act undertaken on false pretences or deliberately in a clandestine manner.”
During an armed conflict, an individual who engages in espionage is considered a spy and loses his/her right to prisoner of war status, including the protections around accommodation and access to food, clothing, hygiene and medical care. By contrast, members of the armed forces who wear their own uniforms (as opposed to those who wear civilian attire or the uniform of the adversary) may gather information in the territory of the adverse party without losing prisoner of war status. Similarly, a spy who rejoins his/her armed forces but who is then captured must be treated as a prisoner of war and incurs no responsibility for previous acts of espionage. If captured, a spy may not face summary execution and is guaranteed the right to a fair trial.
_
Espionage during Peacetime:
During peacetime, the position of espionage is more ambiguous. No treaty exists regulating the use of covert agents for the purposes of gathering intelligence. It is even difficult to determine the proper scope of what constitutes ‘espionage’ for the purposes of international law – for instance, whether espionage covers also diplomats that attempt to uncover sensitive information of the receiving State to disclose it, or even journalists that clandestinely leak information to a foreign State. The legality of espionage must be measured against general international law and existing instruments.
_
Diplomat or Spy: Diplomatic Law:
The main purpose of espionage is to collect information of the host State and communicate it to the sending State. This purpose is not unheard of in international law. Diplomatic law states it as one of the tasks entrusted on diplomatic missions. Spies and diplomats are different in four respects. First, spies do not disclose their status to the receiving State, as their operation is covert. Second, unlike diplomats, spies do not only seek to ascertain ‘conditions and developments’ in the receiving State, but also to uncover confidential and highly sensitive information that the receiving State does not make readily available (for instance, national security information). Third, unlike diplomats, spies do not necessarily employ lawful means in that endeavour. Finally, diplomats have multiple functions aside from information collection: the 1961 Vienna Convention on Diplomatic Relations (VCDR) states that the other functions of diplomats are to represent their sending State, to protect its interests and its nationals abroad, to negotiate and to promote friendly relations (see Article 3(1)). The similarity of the roles creates a significant risk of overlap, which has led States to expel diplomats on accusations of espionage. Some authors consider that sending spies under the guise of diplomats is an abuse of diplomatic immunity and privileges. For example, pursuant to the Vienna Convention, if an ambassador is found spying, the country that caught him can’t arrest him. It can’t bring him to criminal justice because the convention protects the diplomat’s immunity from the criminal jurisdiction of the receiving state. The only response available to the receiving state is to declare that ambassador a persona non grata and let him go back to his home country.
The VCDR does not regulate the scenario of sending covert agents to collect sensitive information or influence internal affairs. Something that can be pointed out is that one of the purposes of the VCDR is to facilitate friendly relations between States; whether espionage is conducive to friendly inter-State relations appears to be a matter of situational analysis. However, interpreting the legality of espionage from the VCDR’s silence would be repugnant to the object and purpose of that treaty. As clarified by the preamble of the VCDR, non-regulated issues should continue to be regulated by international custom.
_
Domestic Law:
Although international law allows for at least some forms of spying in diplomatic relations, individual States often create stricter domestic legislation to protect their national interests. For example, many countries punish corporate espionage such as the stealing of trade secrets or information gathering through cyber hacking. U.S. federal law criminalizes leaks of classified government information in the Espionage Act, and authorizes the government to collect surveillance information against foreign State adversaries and their agents. For instance, Yanjun Xu, a Chinese intelligence officer was given a 20-year sentence for economic espionage and theft of U.S. trade secrets and a National Security Agency employee was indicted for attempting to transmit classified information to a foreign government.
_
Enforcement issue:
Enforcement is always a challenge for international lawyers. The problem with the traditional generalist approach is that there’s a mismatch between what countries do and what generalists claim the law to be.
Right now, we say it’s illegal to spy in the territory of another state without its consent, but everyone does that. Right now, we say it’s illegal to spy from embassies, but every country spies from embassies. And so on.
There’s a mismatch between how the law is presented and reality. This is highly problematic for the legitimacy of the law. If the prescriptive rule doesn’t match what we’re seeing in the world, there’s a real concern. People start doubting if the rule is even a rule since it’s never enforced.
______
______
Legal spying:
At any stage of life, you realize the need to spy on someone, you should be aware of what activities you are allowed to perform, and which activities come into the category of prohibited activities. There are several incidents in our life when we need to spy on someone to reveal the truth. Nowadays, there have been several reasons, and lots of options to spy on your friends, colleagues, relatives, or neighbors.
-1. Placing hidden cams on your premises
If you want to know what the person does in your absence, you can install a spy cam. Setting up a hidden camera in your home to spy on some relative (e.g., a spouse) is an area of law that is still evolving. You are open to set-up a camera to monitor others’ activity if you are the owner of the property, and no audio is recorded.
-2. Location tracking through GPS
Technology has been playing a smart role in helping investigators and spies to accomplish their tasks with much clarity. GPS tracker is one of the best technology that plays a very important role in spying through location tracking. In terms of tracking the location of someone through GPS devices, the law is not defined clearly. If you’re placing a GPS tracker in your own vehicle, it is somehow legal. If you want someone to track where the person using your vehicle goes, positioning a GPS tracker to keep track of location is a great way. Positioning GPS device on other vehicles isn’t a good idea, as it can be illegal.
-3. Hire a private investigator
Private detectives have been on their duty for a long ago. If you find it hard to investigate others on your own, or you don’t want to do an investigation by yourself, you can let someone else do this task for you. Hiring a private investigator can be a great option for this. Persons in the profession have experience with surveillance, they are also competent enough to take care of privacy laws and other legal issues related to the investigation.
-Make it clear that the investigator you hire doesn’t use any illegal method to spy on someone. If somehow the investigator uses illegal means to spy on someone for you, you can be punished by law.
-Give clear instructions to your investigator and take his acceptance in writing.
-As it is about hiring a third person, be clear with all your instructions and permissions you give your private investigator.
-4. Collect information on the public identification
In this world of the internet and social media, every second person has social media account. You can identify habits, behaviors, interests, friend circle, future plans, social status, and a lot more about a person by searching them on the internet. Also, public information like criminal background, credit reports, and property records can be an intelligent way to spy on a person.
-5. Observing publicly
A person in a public place is very easy to spy on and observe as there is no expectation of privacy in this case.
_
Understand what is illegal:
-1. Don’t misuse the camera, use it to protect personal property
In various cases, spying on people through a hidden camera is not legal for a citizen. Yes! A private individual isn’t authorized to record the behavior of any other person, however, government agencies or a law-enforcement officer might have this right.
-If it is your private property you are allowed to install a camera to monitor what is going on in your house to secure your property from theft and damage. Placing cameras isn’t considered spying. If you make observations and collect information stealthily then it comes under spy.
-2. Installing a spy camera, or software on another’s PC is illegal
Using spyware on someone else’s pc or mobile without their consent is illegal.
-State law restricts unauthorized and international usage of private information stored on phones or computers.
-If you accidentally access such information, or the person whom you’re spying on has accepted to accessing their private communications, the activity can be considered legal.
-Usage of improperly obtained passwords is also not legal. Even guessing someone’s right password and getting into their device is also against the law.
-3. Pretexting is illegal
Do not pretend to be someone else to get information about that person. You can’t call a cell phone company, bank, or credit card company pretending to be someone other than yourself.
_
What is the punishment for spying on someone?
The punishment for spying on someone varies depending on the jurisdiction and the specific circumstances of the case. In general, the following outcomes are possible:
Criminal charges: Spying on someone can be considered a criminal offense, such as invasion of privacy or unauthorized access to computer systems. Penalties can include fines, imprisonment, or both.
Civil lawsuits: The victim of spying may also have the option to file a civil lawsuit against the person who spied on them, seeking monetary damages or an injunction to stop the behavior.
Administrative penalties: Depending on the nature of the spying, the person responsible may face administrative penalties, such as losing their job or professional license.
Restraining orders: In some cases, the victim may obtain a restraining order to prevent the person from continuing to spy on them.
The specific punishment for spying will depend on the laws of the jurisdiction, the severity of the offense, and the specific circumstances of the case.
______
______
Section-15
Risks and dangers of spying:
Espionage, unlike other harmful foreign policies such as war and economic sanctions, is not regulated in international law. In fact, it is hard to imagine how espionage ever can be so regulated. For law to be effective, parties must either trust each other to abide by the law or be able to verify each other’s compliance. Given that either alternative is unlikely in the case of espionage, the prospects for future international regulation seem dim. Moreover, the ethics of espionage has not received anywhere near the same attention from contemporary moral or legal philosophers as the morality of war and sanctions. Cécile Fabre’s book Spying Through a Glass Darkly: The Ethics of Espionage and Counter-Intelligence is a welcome contribution to fill this normative lacuna. Fabre notes that a common way of framing the ethics of espionage is by appeal to just war theory. Fabre explicitly rejects this approach, pointing out that espionage harms people in “less obvious and more complex ways” than war does.
_
In today’s world, information is a highly valuable asset. Spying and leaking classified information, however, pose major risks—not only to national security but also to global stability. Unauthorized sharing of sensitive data, whether intentional or accidental, can have serious and far-reaching consequences. These actions can undermine trust in government institutions, endanger lives, and spark international conflicts. Understanding the dangers of spying and the leaking of classified information, as well as knowing the steps organizations can take to prevent such breaches, the importance of thorough employee vetting, and the risks posed by individuals misusing their access to sensitive information, is essential for safeguarding your office or company.
_
Espionage poses significant threats to national security, political stability, and public trust. The unauthorized acquisition of sensitive information can undermine governmental functions and decision-making processes. This state of affairs can lead to the breakdown of diplomatic relations and heighten tensions between nations. Moreover, espionage can compromise personal privacy and civil liberties. Surveillance practices inherent in intelligence-gathering activities often infringe upon the rights of individuals, creating an environment of fear and distrust. Such scenarios can exacerbate societal divisions, fostering resentment toward authorities and government institutions.
Economic security also faces serious risks from espionage. Industrial espionage can lead to the theft of proprietary technologies or trade secrets, weakening competitive advantages for businesses and entire economies. This theft can drive companies into financial distress, ultimately affecting job stability and economic growth.
Lastly, the psychological impacts of espionage cannot be overlooked. Citizens may experience feelings of vulnerability and insecurity, knowing that their government is spying on them. This erosion of public confidence can diminish support for political institutions, exacerbating crises in governance and societal cohesion.
_________
_________
The harms of surveillance to privacy, expression and association:
On 5 June 2013, the Washington Post and the Guardian simultaneously published documents that would rock the world. The documents, leaked by ex-National Security Agency (NSA) contractor Edward Snowden, were not the first disclosures about the United States’ vast surveillance complex, but have arguably had the most impact.
The knowledge, or even the perception, of being surveilled can have a chilling effect. A 2012 industry study conducted by the World Economic Forum found that in high internet penetration countries, a majority of respondents (50.2%) believe that “the government monitors what people do on the Internet.” At the same time, only 50% believe that the internet is a safe place for expressing their opinions, while 60.7% agreed that “people who go online put their privacy at risk.”
A member survey conducted by writers’ organisation PEN American Center in December 2013 discovered that, since the publication of the first NSA leaks, 28% of respondents have “curtailed or avoided social media activities,” while another 24% have “deliberately avoided certain topics in phone or email conversations.” Perhaps even more worryingly, a full 16% have avoided writing or speaking on certain topics.
Surveillance affects us in myriad ways. It infringes on our personal freedoms, submits us to state control, and prevents us from progressing as a society.
_
When we talk about surveillance, it often follows that we speak of the importance of privacy, of being free from observation or disturbance, from public attention. In the US, privacy is a fundamental right, enshrined in the Fourth Amendment to the Constitution.
Of course, this is no coincidence – under King George II, the American colonisers found themselves at the mercy of writs of assistance, court-issued orders that allowed the King’s agents to carry out wide-ranging searches of anyone, anytime; a precursor to the modern surveillance state. Once issued, an individual writ would be valid for the King’s entire reign, and even up to six months past his death.
It was only after the death of King George II that a legal challenge was mounted. When a customs officer in Boston attempted to secure new writs of assistance, a group of Boston merchants, represented by attorney James Otis, opposed the move. Otis argued that the writs placed “the liberty of every man in the hands of every petty officer,” an argument that founding father John Adams later claimed “breathed into this nation the breath of life.” It was from this societal shift that the Fourth Amendment was born.
The opposition to surveillance, however, is not borne only out of a desire for privacy. In the United States, the First Amendment – that which prohibits the creation of law “respecting an establishment of religion, or prohibiting the free exercise thereof; or abridging the freedom of speech, or of the press; or the right of the people peaceably to assemble, and to petition the Government for a redress of grievances” – is often debated, but rarely restricted. It is a set of rights that is paramount in US culture; as Supreme Court Justice Hugo L. Black once stated:
First in the catalogue of human liberties essential to the life and growth of a government of, for, and by the people are those liberties written into the First Amendment of our Constitution. They are the pillars upon which popular government rests and without which a government of free men cannot survive.
Article 19 of the Universal Declaration of Human Rights similarly provides for the right to freedom of opinion and expression, to “seek, receive and impart information and ideas through any media and regardless of frontiers.”
Documents leaked by Edward Snowden in 2013 have demonstrated the extraordinary breadth of the US’s and other governments’ mass surveillance programmes, programmes which constitute an intrusion into the private lives of individuals all over the world.
The violation of privacy is apparent: indiscriminate, mass surveillance goes against the basic, fundamental right to privacy that our predecessors fought for. The negative effects of surveillance on the fundamental freedoms of expression and association may be less evident in an era of ubiquitous digital connection, but are no less important.
In a 2013 report, Frank La Rue, Special Rapporteur to the United Nations on the promotion and protection of the right to freedom of opinion and expression, discussed the ways in which mass surveillance can harm expression. He wrote:
Undue interference with individuals’ privacy can both directly and indirectly limit the free development and exchange of ideas. Restrictions of anonymity in communication, for example, have an evident chilling effect on victims of all forms of violence and abuse, who may be reluctant to report for fear of double victimization.
The harmful effects of surveillance on expression and association are undeniably linked – the right to organise is imperative for political expression and the advancement of ideas. In the US, although the two rights are linked in the First Amendment, historically, they have sometimes been treated separately.
_
There has been bipartisan recognition that the post-9/11 surveillance regime undermines privacy rights. The human toll of government surveillance is undeniable. It can have far-reaching consequences for people’s lives — particularly for communities of color, who are wrongly and disproportionately subject to surveillance. The people who feel the impact the most are Muslims, Black and Brown people, people of Asian descent, and others who have long been subject to wrongful profiling and discrimination in the name of national security. Routine surveillance is corrosive, making us feel like we are always being watched, and it chills the very kind of speech and association on which democracy depends. This spying is especially harmful because it often feeds into a national security apparatus that puts people on watchlists, subjects them to unwarranted scrutiny by law enforcement, and allows the government to upend lives on the basis of vague, secret claims.
_______
_______
Spying and Relationship scandal:
Around the end of 2010 and during 2011, it was disclosed in UK media that a number of undercover police officers had, as part of their ‘false persona’, entered into intimate relationships with members of targeted groups and in some cases proposed marriage or fathered children with protesters who were unaware their partner was a police officer in a role as part of their official duties. Various legal actions followed, including eight women who took action against the Metropolitan Police and the Association of Chief Police Officers (ACPO), stating they were deceived into long-term intimate relationships by five officers, including Mark Kennedy, the first officer to be identified as such, who was publicly identified on 21 October 2010 as infiltrating social and environmental justice campaigns, and Mark Kennedy himself who claimed in turn that he had been incompetently handled by his superiors and denied psychological counselling. According to The Guardian, Kennedy sued the police for ruining his life and failing to “protect” him from falling in love with one of the environmental activists whose movement he infiltrated.
Although the units had been previously disbanded, other cases continued to emerge. In 2015 the public Undercover Policing Inquiry under a senior judge was announced. In November 2015 the Metropolitan Police published an unreserved apology in which it exonerated and apologised to those women who had been deceived and stated the methodology had constituted abuse and a “gross violation” with severely harmful effects, as part of a settlement of their cases. In 2016 new cases continued to come to light.
_______
_______
Spy whose cover is blown up:
If a spy is caught, the outcome depends on the country, the severity of the espionage activities, and the relationship between the spy’s home country and the country where they were caught. In some cases, the spy may face legal consequences, such as criminal charges, imprisonment, or fines. In other cases, they may be expelled or deported from the country.
In situations where the spy is caught in a foreign country and working for their own government, diplomatic efforts may be made to secure their release. The handling of caught spies is often complex and politically sensitive, involving negotiations between governments and intelligence agencies. The consequences of being caught can be severe and long-lasting, and can impact not only the individual spy but also their country and international relations.
Some spies are just too important to be left by their handlers to rot in a foreign jail after they’ve been captured, and they are traded in a spy swap. Other times spy catchers are reluctant to consider a trade because the betrayal has been so great a long jail sentence seems deserving.
And then there are the expendables — so low-ranking their handlers don’t care what happens to them once they’re blown and too insignificant to consider for a spy swap.
Not everyone gets arrested. The two Russian men suspected of carrying out the 2018 Salisbury poisonings appeared on Russian state-funded television after being identified as suspects. They famously claimed to be visiting the “wonderful” English city as tourists to see its cathedral. The BBC said in a report in 2021 that they had not been seen since.
_
Life of glamor:
For Anna Vasilyevna Kushchenko (aka Anna Chapman), the former Russian sleeper agent, whose flame-colored hair captivated the American and British tabloid press, life after spying has been lucrative and a whirl of fashion shows, television and business opportunities. Chapman, who took her surname from a Briton she briefly married, was feted on her return home after being traded more than a decade ago in the biggest spy swap since the end of the Cold War. The United States released 10 Russians, including Chapman, and the Kremlin handed over Sergei Skripal, a Russian intelligence officer convicted of spying for Britain, plus three other people. She and her fellow sleeper agents met with Vladimir Putin on their arrival and reportedly sang patriotic songs together. Many of them were then given well-paid advisory jobs in state companies but Chapman hit the motherlode with the Kremlin keen to promote her as a poster “Bond girl” for Putin. She was appointed initially as an adviser to the CEO of a Russian bank. But since then, she has been a catwalk model, a fashion designer, a television presenter, and an entrepreneur.
Andrei Bezrukov, known in the U.S. as Donald Heathfield, who also returned in the same swap, has reinvented himself as an academic at the University of International Affairs in Moscow.
_
Left rotting in jail:
The CIA’s Aldrich Ames and the FBI’s Robert Hanssen were arrested in the 1990s. Hanssen spied for the Soviet and Russian intelligence services from 1979 to 2001 and his betrayal was described by prosecutors as “possibly the worst intelligence disaster in U.S. history.” He sold thousands of top-secret documents on U.S. nuclear strategies, developments in military weapons technologies, and American counter-intelligence programs.
Ames supplied the names of KGB agents working secretly for Washington who were executed on their unmasking. There was some talk of them being included in a spy swap, but the Russians have not held any spies of equal calibre to swap — in addition, their treachery was so heinous as far as the U.S. agencies were concerned, they didn’t deserve to be traded. From 2002 until his death at the age of 79, Hanssen was jailed at a maximum-security prison in Colorado where he was held in solitary confinement 23 hours a day. Ames, now aged 82, is serving his life sentence in a medium-security prison in Indiana.
______
______
Section-16
Counterintelligence (CI):
Counterintelligence (counter-intelligence) or counterespionage (counter-espionage) is any activity aimed at protecting an agency’s intelligence program from an opposition’s intelligence service. It includes gathering information and conducting activities to prevent espionage, sabotage, assassinations or other intelligence activities conducted by, for, or on behalf of foreign powers, organizations or persons.
Counterintelligence can also be defined as the collective of measures undertaken to identify, deter, exploit, degrade, neutralise, and protect against adversarial intelligence activities deemed as detrimental or potentially detrimental to one’s own interests (Duvenage 2010). The term ‘counterintelligence’ is thus an abbreviated form for the countering of hostile intelligence activities. Adversaries engaging in hostile intelligence actions include nation states, corporate entities, criminals, activists, individuals, and any combination of these.
Many countries will have multiple organizations focusing on a different aspect of counterintelligence, such as domestic, international, and counter-terrorism. Some states will formalize it as part of the police structure, such as the United States’ Federal Bureau of Investigation (FBI). Others will establish independent bodies, such as the United Kingdom’s MI5, others have both intelligence and counterintelligence grouped under the same agency, like the Canadian Security Intelligence Service (CSIS).
“Counterintelligence” (CI) is a term with multiple meanings—its definitions vary, even when applied to a single nation. Yet it can be understood by identifying the common CI functions in a source. These include: handling double agents, defectors, deception operations, and covert communications; handling and detecting moles or penetrations; and dealing with security threats in general. Antecedent elements of what is today called counterintelligence may be found in various histories of intelligence and warfare. Counterintelligence has been practised and described for millennia. The existence of security services can be traced back to ancient Egypt, Assyria, Persia, Greece, Rome, China, and Muscovy, among others. With the rise of the nation-state, rulers began creating secret political police organizations to safeguard their existence. In the case of the United States, it was not until the Civil War that there was anything like a domestic counterintelligence agency, and even then, it was not a statutory organization. After World War I, however, former intelligence officers, agents, defectors, and journalists began publishing accounts of counterintelligence and domestic security operations. The term in its contemporary connotations entered the English lexicon in the mid-1930s (Dictionary.com 2014). For some, counterintelligence is all about spies outgunning adversarial spies. For others, it invokes mundane security measures such as computer passwords, restrictions on the use of computing equipment, security guards, access control, and the like. Counterintelligence is all of these things, and so much more (Duvenage & von Solms 2013).
_
Let’s review the doctrinal definitions for the key concepts:
- Counterintelligence: Information gathered and activities conducted to protect against espionage, other intelligence activities, sabotage, or assassinations conducted by or on behalf of foreign governments or elements thereof, foreign organizations, or foreign persons, or international terrorist activities.
- Cyber Counterintelligence: Measures to identify, penetrate, or neutralize foreign operations that use cyber means as the primary tradecraft methodology, as well as foreign intelligence service collection efforts that use traditional methods to gauge cyber capabilities and intentions.
- Counterespionage: That aspect of counterintelligence designed to detect, destroy, neutralize, exploit, or prevent espionage activities through identification, penetration, manipulation, deception, and repression of individuals, groups, or organizations conducting or suspected of conducting espionage activities.
- Counterterrorism: Actions taken directly against terrorist networks and indirectly to influence and render global and regional environments inhospitable to terrorist networks.
_
According to Prunckun (2014), the objectives of counterintelligence are (1) detection of threats and threat sources; (2) deterrence of threats from adversaries; (3) threat neutralization, which blocks intelligence gathering or causes loss of interest, enthusiasm, or confidence in carrying out threat operations; and (4) deception, in which an adversary is misled about certain aspects of the target’s operations. The four objectives can be grouped into (1) detecting threats and their sources and (2) controlling the threats via measures pertaining to deterrence, neutralization, and deception.
_
9/11 as a turning point:
The 9/11 attacks were a turning point in the manner that states relate to the value of counterintelligence. Two American investigative committees published their conclusions on the attack, one in 2002, the other in 2004.These committees were in agreement about the intelligence failure to prevent the attack, and were surprised to discover embarrassing details about the low effectiveness of US counterintelligence operations. The conclusions were not different from those of commissions of inquiry that dealt with strategic surprise attacks. US intelligence had no shortage of information from open sources, and also from highly confidential sources, about Bin Laden’s intentions to attack the US. It would have been possible to prevent the attack, based on the gathered intelligence. The 9/11 inquiry commissions severely criticized the lack of inter-branch cooperation, asserting that the terror attack could have been prevented.
_
Adversarial intelligence activities include espionage, deception (disinformation), influencing, and some other forms of covert action that can have disruptive and destructive outcomes. Of these different intelligence activities, espionage is the most central. Espionage to obtain protected information in order to gain a competitive advantage can be an end in itself; or such information can be used to further other malicious ends such as data manipulation, disinformation, and disruption. Sophisticated adversaries execute their intelligence actions through the exploitation of humans (HUMINT) and technical means (TECHINT). The latter, in turn, comprise Signal Intelligence (SIGINT), Imagery Intelligence (IMINT), Measurement and Signature Intelligence (MASINT), and Cyber Intelligence (CYBINT). These conduits and their relation to adversarial intelligence ends are graphically depicted in figure below:
Figure above shows Adversarial Intelligence: Conduits and Ends.
Before moving away from the conceptual aspects of counterintelligence, it is beneficial to briefly mention its function as a sort of counterpart to “positive intelligence”, for lack of a better term. What this means is that each discipline of intelligence – HUMINT, SIGNIT, OSINT, etc – has a counterintelligence function on its opposite end. This is important, as each collection method has its own set of counterintelligence practices. In addition, different agencies, organisations, governments, companies, etc., will have their own specific tactics, techniques, and procedures as well.
_
Spies vs. Shields: Intelligence vs. Counterintelligence:
Spies gather secrets — intelligence seeks enemy plans via hacks or moles. Shields block them — counterintelligence hunts spies, fortifies defense. Intelligence vs counterintelligence is the eternal tug-of-war of secrets—spies gather, shields guard, in a chess match that never ends. Intelligence, the art of espionage, seeks to uncover state, corporate, or military secrets, using moles, intercepted signals, or cyber hacks to peer into enemy plans. Counterintelligence, its relentless counterweight, protects those plans, hunting moles, fortifying defences, and planting disinformation to mislead foes. Together, they form a shadowy ballet, driving modern espionage and cybersecurity into a relentless duel that captivates us with its depth.
Intelligence vs counterintelligence traces its roots to ancient shadows—Sun Tzu’s spies in ancient China, weaving secrets into war plans, and Roman scouts outwitting barbarian tribes with cunning traps. By the Renaissance, France’s Cardinal Richelieu ran moles against Spain, while Britain’s MI6 outfoxed Napoleon’s agents with whispered deceits. The Cold War cemented their stakes—think of a British mole like Kim Philby, slipping secrets to the Soviets, only for MI6’s counterintelligence to unravel the betrayal years later, a mole hunt that defined the era’s tension.
Imagine a CIA operative in a Berlin café, decades ago, slipping microfilm from a defecting East German—intelligence at its peak, a whisper of triumph. Now, picture a hacker in Moscow breaching NATO servers, stealing troop data in a blink—intelligence strikes anew. But an NSA analyst in a Maryland bunker spots the breach, deploys traps, and flips the script—counterintelligence fights back with equal ferocity. Intelligence vs counterintelligence explained is simple yet profound: one seeks, the other shields, and their clash pulses through today’s digital shadows, keeping us on edge with its endless intrigue.
_
Today, espionage and counterintelligence stretch beyond alleys into cyberspace—imagine a Russian operative planting false X posts to sway elections, intelligence at work, while a U.S. counter intel team crafts disinformation to sow doubt, shielding secrets with digital sleight of hand. From quill pens to quantum hacks, this timeless war evolves, its history a tapestry of wits that thrills us—intelligence vs counterintelligence explained through centuries reveals a game of minds that never fades, only deepens with each new tool.
|
Aspect |
Intelligence |
Counterintelligence |
|
Objective |
Collect information on adversaries. |
Protect against espionage and infiltration. |
|
Focus |
Offensive—seeking knowledge. |
Defensive—preventing leaks and sabotage. |
|
Tactics |
Spying, surveillance, and data analysis. |
Deception, detection, and neutralization. |
|
Outcome |
Informs policy decisions and military strategies. |
Safeguards assets and maintains operational security. |
_
Counterintelligence Measures:
Counterintelligence measures are strategic actions taken by nations to protect their intelligence operations and capabilities from being compromised by adversaries. They aim to thwart efforts by enemy states or groups seeking to monitor or disrupt intelligence activities. In modern conflicts, effective counterintelligence is vital for safeguarding sensitive information and preserving operational integrity. The implementation of counterintelligence measures can include a variety of techniques. These can be categorized as follows:
- Surveillance and Monitoring: Observing potential threats to detect unauthorized activities.
- Deception Operations: Manipulating information to mislead adversaries about intentions or capabilities.
- Security Enhancements: Strengthening physical and cyber protections around intelligence assets.
- Personnel Vetting: Ensuring that individuals involved in intelligence gather operations are trustworthy and pose minimal risk.
The effectiveness of counterintelligence measures relies on continuous assessment of potential threats and adapting strategies accordingly. As conflict dynamics evolve, so too must the approaches to counteracting espionage, ensuring that intelligence gathering in modern conflicts remains resilient and effective.
_
Counterintelligence process:
Similar to the intelligence cycle, we can break counterintelligence down into a process. Scholar Gašper Hribar breaks this process into four steps as seen in figure below.
-1. Planning: defining goals and establishing intelligence priorities.
-2. Data collection: collecting information through all-source disciplines.
-3. Analysis: data evaluation, analytical methods.
-4. Production & dissemination: report drafting, briefing and dissemination to customers.
Similarities with the intelligence cycle aside, the fundamental difference is within the direction and final product, which can cause counterintelligence actions, directed at implementing defensive solutions or offensive actions – defensive counterintelligence or offensive counterespionage.
_
Operational security (OPSEC)
In essence, OPSEC is a proactive approach to counterintelligence, focusing on preventing the compromise of critical information by anticipating and mitigating potential vulnerabilities before they can be exploited by an adversary. The U.S. government defines OPSEC as a “Systematic and proven process by which potential adversaries can be denied information about capabilities and intentions by identifying, controlling, and protecting generally unclassified evidence of the planning and execution of sensitive activities.” That process is five steps:
-1. Identification of critical information
-2. Analysis of threats
-3. Analysis of vulnerabilities
-4. Assessment of risks
-5. Applications of countermeasures
This process is not strictly for government employees or members of the intelligence community. It is just as important in the private sector as well, especially when there are trade secrets on the line, or the risk of economic or industrial espionage from a competitor or hostile threat actor.
_
Tradecraft of counterintelligence:
- Double/penetration agents: this includes detecting and deterring adversary agents (defensive) and cultivating or handling your own, as a way of neutralising or lessening your adversary’s intelligence collection capabilities.
- Covert surveillance: covert observation and tracking of “people, objects, facilities, or anything else deemed of value by the (intelligence) service.”
- Technical surveillance: surveillance aligned with technical collection methods (i.e. SIGINT, COMINT). This includes through the utilisation of electronics, communication equipment, and video surveillance.
- Counter surveillance: deterring, preventing, and exploiting an adversaries’ attempts at surveillance.
_
Common mistakes in counterintelligence:
- Poor OPSEC: poor OPSEC leads to fractures in security and opens an entity up to the intelligence actions of an adversary.
- Improper education: this includes personnel not having adequate training in OPSEC, organisational procedures, and safe handling of sensitive materials.
- Failure to report: specifically, failure to report individuals who have a noticeable shift in behaviour or signal red flags.
- Weak vetting: improper background checks and poor vetting procedures is a significant risk to organisational security.
- Complacency: complacency can mean many things for counterintelligence. One example is having a narrow view of what makes a threat, i.e. directing efforts to protect an organisation from external penetration when there is an equal internal risk.
_
Why is counterintelligence important?
Conducting intelligence without having a strong counterintelligence program puts an agency, organisation, or nation at a great disadvantage over their adversaries. As advantage is a component of intelligence operations and strategy, counterintelligence helps gain or preserve that, when done correctly. In addition, CI drives the mechanisms that protect national secrets, which in return protects national security. In the private sector, counterintelligence helps preserve sensitive information that can give a competitor an advantage, or open your organisation up for attack.
Intelligence vs counterintelligence matters more than ever—state secrets, election hacks, and corporate espionage shape a world where cyber threats cost trillions and threaten stability. For example, Russia swaying votes with false social posts, intelligence winning a quiet victory; China stealing U.S. chip designs threatening tech dominance. A NATO leak could spark war—intelligence triumphs, but counterintelligence’s lapse risks catastrophe.
______
Cyber counterintelligence:
Cyber counterintelligence (CCI) is a quickly evolving sub-element of the counterintelligence discipline, like how cyber operations are becoming increasingly enmeshed with intelligence. Practically, CCI is a way for actors to secure (defence) and advance (offense) their cyber interests. Although CCI is growing in scholarship and awareness, it is still a rather niche field that does not receive as much attention as other CI practices.
Scholars Petrus Duvenage and Sebastian von Solms have developed a useful matrix with CCI practitioners in mind. It covers both defensive and offensive modes.
-1. Passive-defence mode: physical and cyber security systems that deny opposition access.
-2. Active-defence mode: active collection, surveillance, human intelligence, prior opposition practice.
-3. Passive-offensive mode: Honey-pots, selective information exposure.
-4. Active-offensive mode: disinformation campaigns, covert action, offensive cyber-operations.
And, like normal intelligence, each axis on this matrix is broken into three levels: strategic, operational, and tactical-technical.
Note:
A honeypot is a deliberately created digital trap that simulates a legitimate system or resource to attract cyber attackers. By engaging with this isolated environment, attackers reveal their techniques, tools, and motivations, providing valuable insights for cybersecurity teams.
_
Four-Sector Counterintelligence Matrix, depicted in table below, is somewhat of an over-simplification, but is nonetheless useful in conveying the nuanced nature of the offensive-defensive interplay as well as the importance of collection:
|
Defensive Mode Denies adversaries access to and generates information about adversaries |
|
|
Passive Defence Denies the adversary access to information through physical security measures and security systems. |
Active Defence The active collection of information on the adversary to determine its sponsor, modus operandi, network, and targets. Methods include physical and electronic surveillance, dangles, double agents, moles, and electronic tapping. |
|
Offensive Mode Aims to manipulate, degrade, control, and neutralise adversaries |
|
|
Passive Offensive Reveals to the adversary what you want them to see. This could range from selective exposure of actual information to decoys and dummies. The adversary is thus left to draw its own inferences and interpretations. |
Active Offensive The adversary is fed with disinformation and its interpretation thereof manipulated. Disinformation can be channelled through, for example, double agents and ‘moles’. Active-offensive CI could include some forms of covert action. Covert action, in its use here, denotes the targeting of an adversary through the influencing of events, conditions, individuals, groups, or institutions to the benefit of a sponsor in a manner not attributable to the sponsor or by offering plausible deniability. Influencing is achieved through measures that vary from paramilitary and political actions to propaganda and intelligence assistance. |
______
Covert action:
When it comes to the intersection of counterintelligence and covert action, Roy Godson says it best: “As with counterintelligence, history is replete with examples of the advantages that accrue to states that blend an effective covert action capability into their overall policies, and of the problems besetting those that do not.” By and large, covert action and counterintelligence are both essential tools wielded in the protection of national security.
As it relates to counterintelligence, covert action operations are generally concerned with espionage, sabotage, and subversion (ESS). In part, protecting one’s own organisation or agency from ESS is itself a defensive CI function. However, the offensive side would fall under covert action. Further, ESS can be conducted in different ways depending on the INT – HUMINT driven ESS will look different than a cyber-operation, yet they share the same foundation.
______
Counterintelligence case studies:
Aldrich Ames:
Aldrich Ames is one of the most prolific examples of a counterintelligence failure in U.S. history. From 1985 to 1994, Ames lived a double life as a CIA counterintelligence officer and a Soviet agent. Coincidentally, Ames was a specialist on Soviet affairs, and spent his early career targeting KGB officers for recruitment. In 1985, Ames volunteered to be a KGB asset for substantial payments. There were a few indicators in his personal life, that he was vulnerable to recruitment, such as alcoholism and extramarital affairs. In May 1993, the FBI opened a case after receiving information regarding Ames’ unexplainable wealth gains. An almost year long investigation resulted in his arrest and further guilty plea in April 1994. Ames was sentenced to life in prison without the possibility of parole. His time as a Soviet agent resulted in the executions of multiple U.S. citizens overseas.
Ana Montes:
Ana Montes is another U.S. double agent who was recently released from incarceration. Montes was once the Defense Intelligence Agencies Top Cuban analyst, yet harboured sympathy for their cause. Her personal ideological leanings drove her to become a Cuban agent, which was ideal given her prime access to some of the nation’s most sensitive defence intelligence. Contrary to Ames, money was not a driver. Montes is an example of the power of ideology, and how it can result in some of the most steadfast agents. She was eventually caught and prosecuted, pleading guilty in 2002 and receiving a 25 year prison sentence.
Byzantine Hades:
Byzantine Hades is an example of a CCI operation – both a counterintelligence failure and success for the U.S. in the early to mid-2000s. In essence, Byzantine Hades is the codename for an array of Chinese advanced persistent threats that over the course of a few years, hacked into numerous Department of Defense systems through spearfishing attacks. As a result, the Chinese threat actors stole massive quantities of sensitive information, including schematics for the F-35 fighter jet, which was used to help their own next generation fighter jet program. This economic espionage resulted in millions of dollars in damage to DoD systems, and thousands of compromised accounts. It was kept private until the WikiLeaks scandal and further leaks from NSA whistleblower Edward Snowden.
______
______
Section-17
Know that you are being spied on and protect yourself from spying:
_
Be aware of what’s going on when you go in a restroom:
Mini-video cams get installed behind walls looking through holes so tiny you won’t notice them, so don’t expect privacy in the modern world, even look inside the toilet bowl, what looks like one of the bowl rinsing water inlet wash holes have been found to have fiber optic video system cables installed running to a remote video cam.
Figure above shows Women fight back against Spy Cams in Public Bathrooms. Some 70,000 women gathered in central Seoul, holding signs saying, “My life is not your porn.” It was the fourth protest in 2018 condemning the prevalence of hidden-camera crimes. The fear of digital peeping Toms has led women to stuff tiny balls of toilet paper into holes they find in public bathroom stalls or cover the holes with tape.
_
How do I find out if someone is a spy?
Identifying a spy can be extremely difficult, as spies are experts at hiding and blending in. However, there are some signs and behaviors that might suggest that someone might be involved in espionage:
- Frequent changes in appearance or routine: Spies often change their appearance and routine to avoid detection.
- Reserved or secretive behavior: Spies are often very cautious about the information they share and can be evasive about their personal or professional lives.
- Frequent and/or unexplained travel: If someone travels frequently, especially to conflict zones or to countries with hostile governments, it could be a sign that they are involved in espionage.
- Use of counterespionage: This can include things like repeatedly looking over your shoulder, changing your route home or to work, or appearing concerned about being followed.
It is important to note that these signs are only possible indicators, and many people who exhibit these behaviors are not involved in espionage. Also, a professional spy probably won’t show any of these signs. If you really suspect someone may be a spy, it’s best to report your suspicions to the proper authorities rather than try to investigate on your own.
_____
Common Physical Signs of Spying on you in Your Home or Office:
There are infinite ways by which anyone can be spied on at any time or place without being noticed. It also includes the equipment, methods, techniques, and tools. Physical spying and tracking others is the least common method used these days for spying because of technological advancements and the internet. A person sitting thousands of kilometers away from you can spy on you with a laptop or device. Spy cameras and microphones are relatively inexpensive, accessible, and smaller than ever. Thus, they are also easily installed and hidden. However, while installing may be simple, people may be in a hurry and leave behind traces of their work. Perhaps you’ve already noticed a few things that don’t seem quite right.
-1. Electrical fixture wall plates are slightly out of place. Look for signs of disturbance. Specifically, light switches, electrical outlets, and smoke alarms are popular places for eavesdropping devices because most of the time, we don’t pay much attention to them. For example, look for debris on the floor beneath a fixture, or subtle color differences in the wall plate color. Similarly, look for gaps or poor alignment that may result from hurried installation.
-2. Check your vinyl baseboard – where the floor and wall meet. Another common sign of surveillance is changes in your vinyl baseboards. Frequently, spy devices require wiring for power or data transmission. Thus, the suspect must hide wires. A favourite spot is behind the vinyl baseboard. So, look for a ridge, bump, or discolouring, and then check further for hidden microphone or wiring.
-3. Look for discoloration on ceilings and walls. It may be very small, but a circular spot, no larger than a coin, is a signal that you are being spied on. In particular, small devices such as pinhole microphones or video cameras, rest on the other side of a ceiling or wall and may leave an impression.
-4. A familiar item or sign in your home or office simply looks off. Eavesdroppers try to hide devices in the least obvious place. For this reason, fixtures like lamps and clock radios that you hardly pay attention to are popular choices. A sudden change in these familiar items may be a sign of surveillance. Remember, when someone is installing a surveillance device, they are usually in a hurry and nervous. This means any item that has been affected is rarely left in the same way. Thus, look to see if any are a little crooked, or showing a strange semi-reflective surface, or even have a tiny hole.
-5. You notice white debris close to a wall. It stands to reason that to install a small microphone or video camera inside the wall, you must bore a hole into them. This will generally leave white dust on the ground. Someone that is nervous or in a hurry may neglect to clean up the dust. Whenever you spot white powder-like dust, you should look at that wall or ceiling for any recent disturbances. Also, moveable ceiling tiles are ideal for hiding microphones and cameras. But, they are easily damaged when moved. Always take a closer if you see small pieces on the floor, or gouges, chips, cracks, or sagging in the tiles.
-6. The locks on your doors become easily stuck, or just don’t feel right. It may just need to be oiled, but when your lock suddenly becomes stiff, sticky, or even fails, it’s a strong indication that you’re being spied on. The chances are that someone picked or otherwise manipulated it to get inside and install spy devices.
-7. Your files or belongings appear to have been disturbed or rummaged through, but there doesn’t seem to be anything missing. Eavesdroppers often mistakenly think that items left out of sight are easily forgotten. So, when rummaging through filing cabinets, desk drawers, or dresser drawers, they are less concerned about leaving everything back the way it was. If things feel a little off and aren’t exactly as you remember them then there is every reason to be suspicious.
-8. A clear sign you’re being spied on – new items in your home or office appear from nowhere. Beware of new items at home or in your office. If you notice anything new, like a wall clock, phone, lamp, or even a picture frame, ask where it came from. If no one knows, it may have been planted there with a surveillance device inside it.
-9. Your home or office has been broken into, but nothing was stolen. Logically, burglars do not break into a home and take nothing, unless they were there for another reason, like installing eavesdropping devices. They may break in several times over a prolonged period, so repeat theft-free burglaries are a clue. Notably, physical evidence may be as subtle as slightly moved furniture and table-top items. So, check for exposed imprints on rugs or carpets, or dust-rings under lamps or telephones.
-10. Beware vendors or suppliers bearing electronic gifts. A popular tactic is to give you an alarm clock, radio, desk lamp, or almost any other type of electronic. The gift-giver may have hidden a microphone or camera, but because you know them, you don’t suspect it is bugged. Unfortunately, it is not limited to electronic gifts. Notably, desktop items like pens, calculators, and even Post-It dispensers, can house spying devices.
-11. You receive a written or recorded copy of a private conversation you’ve had. This is solid proof you have been under surveillance. Sometimes eavesdroppers send copies of private conversations to let you know they have something on you. This is an easy way to blackmail, intimidate, or otherwise psychologically undermine the target. This tactic is frequently used in divorce cases, civil suits, custody battles, criminal cases, to seek an advantage over the other.
-12. Unauthorized people seem to know information about your business that should have been confidential. The clear indication that you are being spied on is where one of your business competitors appears to have knowledge of some aspect of your company that is proprietary or sensitive. For example, your competitor might consistently out-bid you for contracts, or a third party refers to the contents of confidential company documents. They may have gained access to this information by bugging your office, telephone, or computer.
-13. Utility company workers or servicers show up without anyone calling for them. The oldest trick eavesdroppers pull is to pretend to be a plumber, air-con repairman, or utility company worker coming to fix a problem. Most people never question service providers, but it allows eavesdroppers to gain access to a building or office to install surveillance devices.
-14. You notice utility or cable company vehicles parked near your home or office but with no visible occupants, or frequently carrying out “repair work” in your area. Eavesdroppers often use service vans as surveillance posts to listen in on your activity. Of course, sometimes this their presence is perfectly innocent. However, an indication you’re under surveillance is if you notice the same track or van more than three times over a short time. You can contact the specific utility company to see if work is being required on your street.
-15. Your TV starts to experience unusual interference. As with your radio, spying devices emit signals and can interfere with your TV’s reception, particularly on UHF channels (usually channels 2, 7, 13, 14, 50-60, and 66-68). If you notice interference, this is a sign of surveillance.
-16. Your AM/FM radio starts to experience unusual interference. In the movies, we often blame UFOs for radio interference. But in the real world, sudden interference is more likely because someone tampered with your antennae. Interference happens when more than one electronic device shares a frequency. Since many listening devices use frequencies just inside the FM radio band, when they’re located in the same room with a radio, the radio will squeal. In this way, the radio is a bug detector because the closer it is to the device, the louder the squeal.
-17. When your phone is hung up, you hear a tone on your phone line. If you can hear a faint but continuous dull tone, it suggests that someone hooked up a “slave” eavesdropping device to your phone line. In this case, the chance you are being spied upon is high.
-18. When your phone is on the hook, you hear noises coming from the handset. A Hook Switch Bypass turns your phone’s receiver into a microphone. When installed, they create noises when your phone is on the hook. Additionally, this creates a double dilemma because it is effective within a radius of 20 feet from the phone. So, even when you’re not talking on the phone, an eavesdropper can monitor what is being said.
-19. Your house may be spying on you. The seemingly benign digital devices we have in our homes may actually threaten our well-being. The average U.S. household now has more than 17 connected devices – and that number continues to grow. To put everything in perspective, 500 billion devices are expected to be connected to the internet by 2030. Yet all these new “smart devices,” including fitness equipment, digital personal assistants, gaming consoles, thermostats and security cameras, etc., can potentially endanger not only our privacy and physical safety, but our finances as well. US Senator Ted Cruz revealed that common household appliances could have cameras and microphones that violate your privacy. This includes appliances you would least expect to spy on you, like air fryers, washers, and refrigerators.
-20. You notice drones overhead. The ease of use and fast advancing technology makes spying-by-drone commonplace.
We have discussed many ways in which you can be spied on. These are the ways that most people use. If there is a divorce case, your ex-wife/ex-husband knows everything about you. This information can be used against you. If you own a business, your opponent can de-track your plans or learn certain trade secrets. All of the above is how you must identify if you are being spied on.
_______
Signs that Your Phone is being Spied on:
There are millions of reasons anyone can spy on your phone and cause monetary, physical, or psychological damage. Multiple apps can spy on your phone by just clicking, and most of the most important thing is that they are free of cost and effortlessly available. Most of the time, these apps are installed physically in a targeted phone with some app’s permission, but if this option is not available, you are still not safe because hackers can enter your phone. They can use malicious attacks via emails, text messages, or packages sent on a phone; clicking them or opening them permits them to enter your phone. Our phone is highly vulnerable because of the internet; the internet is the easiest and the most effective mode of transmitting any bug or virus in a phone that can cause severe damage to your privacy. Spying phones are usually used for location tracking, call tracking, contact access, text messages, your search history, or sometimes access to your pictures and videos. Some signs that can tell us that your phone is being spied on are as follows:
-1. Phone Battery behaving abnormally:
The most common indication is that your phone battery starts behaving abnormally because the apps and the software used for spying consume the battery constantly by working in the background. If you are not using your phone and the battery is still dying continuously or started behaving weirdly, it can indicate that your phone is being spied on. Other than software or applications, attackers may access your camera and microphone. This hardware also drains the battery when not in use. To know that your phone is being spied on, you must look out for the software if installed without your knowledge. Access to a camera or microphone can also pose a risk to your phone. Some applications demand access. You should decline the request if these applications don’t need them.
-2. Unusual Sounds in a Telephone:
When your microphone is hacked, and your calls are being tapped, there are chances that it starts behaving abnormally. There can be sounds and sharp noises in phone calls, which might be echoes or beeps. If there is a faint or dull tone, then there might be a chance that your phone is being tracked. And your calls are being listened to. The chance of surveillance is high if you listen to a continuous beep on your phone. Someone might be hooked up to your device signal with a spying device. In that case, you have to look for unusual mobile phone sounds. The same is the case with the telephone. When someone connects two conductors to form a phone tap, they create a capacitive discharge. This wiretap can be a form of spying. Someone can use wires to bug your conversations. If there is a capacitive discharge, the noise will tell you that the phone is bugged.
-3. Data Usage more than usual:
Spyware used in spying and hacking sends data back to the hacker, and this process can eat a large amount of the internet. Suppose your data graph isn’t typical or used more than average. In that case, there is a sign that your phone might have some malicious app or spyware, or malware operating in the device that is consuming data continuously. Consider you are using a package of internet and mobile data, and it is consuming very fast. There are applications on mobile which uses the data more than usual. Look out for data usage.
-4. Spam Email or Text Message:
Special characters in the message can be a symptom of malware; these messages aren’t from the authentic or known service provider. Their number will be weird and will not be understandable. It can be a spam email or a Text message. If you get an unknown message continuously and click on it and choose to reply to it, then you might be giving access to the phone to other people. If you think you are being spied on, look in the email account’s spam folder.
-5. Unusual Popups:
There might be a popup on the screen while using the phone, and that popup will be weird because you haven’t seen that before; it might be a permission popup asking for permission to access the phone. If you have a business phone and think someone is spying on you, then look out for any popups on the mobile. There might be spyware or malware in them. It is a straightforward method to spy on someone. Mostly, people are curious about anything that comes to their phones. This curious nature will make the work of burglars very easy. They need any loophole at the other end of the server, which the suspect himself is providing by clicking on the popups. If there are unusual popups, then it is dangerous. But this is not a sign if there are popups like random on mobile from WhatsApp or Instagram, Facebook, etc.
-6. Performance Declining:
The phone’s performance might reduce weirdly without any changes made by you. Background apps use CPU performance even when not in use; they might eat most of the RAM because apps work in the background. The eavesdropper may use any application to access the mobile. These apps will use the battery of the phone to decline. The RAM will be less than usual. The memory problem will indicate that the background apps are running. These background apps can be a source for burglars to track the use of the phone. It is very easy to spy on someone by gaining access to the phone. With the help of this action, you can get to know whom they are talking to and where you are going. You must check the phone if you think you are being spied on.
-7. Rebooting of Phone:
Sometimes your phone can reboot itself; it can symbolize that someone is controlling your phone, and if they have the power to do that, they can access it a lot. In some scenarios, it becomes difficult to shut down the phone after giving the command. The phone might be suspicious if it is not responding to your commands. Rebooting means updating new terms and conditions without your permission. You can be easily spied on. Consider that if someone can access the settings, he might have access to anything. Private messages, calls, documents, and the company’s confidential data can be accessed. So, check the changes regularly.
-8. Excessive Heating:
If you are not using your phone at extreme levels, like gaming or some bulky software, and even after that, it is heating from the back side, it can be a symbol that someone is trying to access your phone when not in use. This is the least effective sign because if the phone is heating, there might be an issue with the software or hardware. It is only sometimes that someone is spying on you. But for precautions, you must know that excessive heating will weaken the phone, which can pave the way for eavesdropping.
-9. Extra Blinking of Phone:
Abnormal behavior can arise with the display, and your phone can blink, or the screen can turn on and off while you are not using it. This can be an indication that someone is trying to penetrate the device. If you are using essential data on your phone and your phone starts blinking, then look out for any deep things. Someone trying to penetrate your device will have the attention of using it against you. Spying is an act that is always negative. Even for a positive purpose, it is a hostile act.
_______
How to detect cyber espionage:
Due to the clandestine nature of cyber espionage, detecting unauthorized intrusion into your system is a challenging task. Nevertheless, being vigilant and employing robust cybersecurity measures may allow you to catch cyber-spies in the act.
- Monitoring systems. Sophisticated cyberattacks like advanced persistent threats are often executed in phases — the attackers must first get a foothold in the target system, install the required tools, and sniff out valuable data. Noticing aberrant behavior during this time lets you deploy cybersecurity tools against the attack.
- Monitoring networks. To cyber-spies, infiltrated networks are like vast, unexplored labyrinths — they must carefully make their way from system to system until they find the data they seek. Wary administrators may notice unusual movement or access requests in their network, alerting them to the possibility of a cyberattack.
- Using intrusion detection systems (IDS). As the name suggests, IDS tools are designed to detect and respond to unauthorized access attempts. IDS uses multiple techniques to identify intrusion, including detailed analysis of network packets, log files, and system events.
- Implementing security incident and event management (SIEM). SIEM systems continuously monitor security events and detect threats as they occur. They consolidate log and event data from multiple sources (including firewalls, antivirus software, and intrusion detection systems) and immediately alert security professionals to suspicious activities.
- Counter-espionage. Just like in real life, the best warning against cyber espionage attempts comes from your own cyber-spies embedded in the attacker’s organization. These operatives may reveal planned attack dates and vectors, or inform cybersecurity professionals about attacks already in progress.
- Changes to computer settings. If you notice that your computer settings have been changed, such as your default homepage or search engine, it may indicate that spyware has been installed on your device.
- Unexplained pop-ups or notifications. If you see pop-ups or notifications on your device that you were not expecting or that ask for personal information, it may indicate that your device has been compromised.
- Slow or unresponsive device. If your device is running slow or becomes unresponsive, it may indicate that there is malware or spyware running in the background.
- Unusual access attempts. If you notice unusual access attempts to your accounts or online services, such as failed login attempts or unauthorized password resets, it may indicate that someone is attempting to gain access to your accounts.
- Suspicious emails or messages. If you receive suspicious emails or messages that ask for personal information or contain links or attachments that you were not expecting, it may indicate that you are being targeted by phishing or other types of cyber-attacks.
______
______
How do you protect yourself from spying:
_
How do you find Hidden Spying Devices?
The following steps can help you to detect hidden spy devices:
-1. Use a bug detector: An RF detector can detect low-frequency and high-frequency radio signals from hidden cameras and other wireless devices. These devices vary in price depending on factors, including the material the detector is made from, the frequency range and the level of detail shown on the LCD.
-2. Conduct a physical search: You can look for hidden cameras and microphones by physically searching for tiny holes or suspicious wires. You can also use a flashlight or the camera flash on your phone to look for lenses reflecting light. While technology helps aid the success in finding such devices, 99% of bugs can be found through a physical search.
-3. Check your network: If you suspect that someone has installed spyware on your computer, you can check your network using a variety of off-the-shelf tools to see if there is any suspicious activity. It would help if you also considered installing anti-malware software to scan your computer for spyware.
-4. Look for unusual behaviour in electronic devices: If you suspect that your smartphone has been tampered with, look for signs such as the device turning on or off by itself, the battery running down faster than usual, or the device behaving in unexpected ways. Perform a factory reset if suspicious.
_____
Solutions For Mobile Phone Spying:
If the problems are increasing these days, there are also many solutions available regarding everything. Mobile phones can be made safe with a thorough check after some time and giving full attention to every minor behavior. Here are some solutions that can be made to avoid any unnecessary events.
- Always keep your mobile phone with you so no one can target your phone physically because that’s the most common and the easiest method used in spying. If you ever forget your phone in any public place or with any suspicious person, always check your phone thoroughly and analyze its behavior.
- Keep your phone updated with every security minor or significant update given by the company. They should be addressed because these updates can help your device stand against these attacks, and its security improves with every software update.
- Try to use your Internet connection or data bundle to avoid malicious attacks, but if you have to use public Wi-Fi or any personal hotspot, you should use a VPN.
- Check your phone settings to see if they are on default mode or have customized themselves; if so, disable the unknown apps installation, microphone, or camera access to the different apps.
- When using browsers, surf in authentic, recommended browsers and in incognito mode so your search history and passwords are safe.
- Try not to keep any personal information in your phone, like passwords, pin codes, or any series of numbers that are sensitive to share with others. It is better to memorize them or write them in any personal diary or file, which is not easily accessible to everyone.
- Do not install local and underrated applications on your phone which ask you for camera and microphone access. Avoid using apps with bad reviews and bad ratings to protect your phone from attackers.
- Do not try to open every mail or link to check what’s inside or what it can do; they are the best source of malicious and harmful viruses that can even damage your phone.
- Most malicious and spying attacks happen with the help of the internet, so when not in use, turn them off. When your phone is idle, disconnect it from Wi-Fi and Bluetooth.
- Check your device folders and delete every unnecessary file or document with no use or affiliation with your device. Clean your phone weekly or monthly to remove these kinds of junk files.
- You can use trusted and paid antivirus software for your phone to protect you against any harmful or malicious things. Some highly effective anti-malware and anti-spyware are also available on the google play store, which can help you a lot against all these odds.
- If your phone is not behaving well, then factory reset your phone, which can make your phone back to the default factory settings.
- Do not try to jailbreak or root your devices because it can make them vulnerable and less protective against attacks.
_____
How to protect yourself from government surveillance:
Protection from surveillance comes in two forms: top-down legal and policy limits on data collection, and bottom-up technological protections in the hands of the targets of that surveillance. Tech companies will very likely bend to the will of government. That may leave the technology you choose to use as a last line of defense. So, people should have the best tools in their hands and their pockets to maintain their privacy. Government spying is real, but there are ways to protect yourself against it. Here are some methods you can implement to protect yourself from government spying:
-1. Educate yourself about the law
-2. Use best practices
-3. Use a VPN service
-4. Use an app that encrypts your messages, like WhatsApp. Securing your data starts with securing your communications, and securing your communications means using end-to-end encryption.
-5. Encrypted Devices. Just as important as encrypting your conversations is strongly encrypting your devices themselves. On modern iOS and Android smartphones, that’s relatively easy. They’re designed to use full disk encryption by default: All the data is encrypted when they’re locked.
-6. Online Anonymity. The strongest tool available to obscure your trail online is the Tor Browser; or the private browsing feature in the Brave browser, which uses a stripped-down version of Tor’s anonymous routing by default.
-7. Turn off location access for as many apps as possible and regularly review and delete apps you don’t use anymore. You can also take similar precautions on desktop. And make sure that overarching accounts like your Google or Apple ID/iCloud accounts haven’t logged trusted places like a “home” for you.
-8. Financial surveillance is among the most powerful tracking tools in the government’s arsenal. Credit card payments or other transactions linked to your bank account are essentially transparent to any law enforcement agency that demands them. That “follow the money” form of surveillance also has a relatively simple analog defense: use cash.
-9. People should “compartmentalize” and control their data by having a second phone that separates some activities, like work versus personal life. This way, you don’t accidentally end up with photos of your family in your work’s cloud storage, say, or with confidential information from work on your personal device.
-10. Go private on social media
_____
Here are some of the steps for battling cyber espionage:
- Understand where the threats are coming from. When cybercrime first hit the scene, there initially were stand-alone criminals working toward their own, personal agendas. Those days are over and nation-states have wised up to the potential benefits of digital warfare and cyber espionage.
- Discover the motive. Understanding the source can provide a much better chance of discovering the motive. The reason a state actor is attacking might be entirely different from someone operating on their own accord. These reasons can range from trying to gain a competitive advantage, to disrupting a system or location. The motive of an attack can often tell a lot about the method, and vice-versa. Hence, if the motive is known, there can be a greater understanding of the target, which leads to a better grasp of the method most likely to be used to infiltrate it.
- Think like a hacker. When looking for the motive, thinking like a hacker could help a company catch a hacker faster. Catching criminals doesn’t happen by accident, and when thinking like a hacker, a clearer picture of what their movements may be can emerge more quickly. Putting this into practice is imperative, not only in the aftermath of a breach, but in protecting a company from one in the first place. If a security team can get into the mind-set of a hacker, it can actively seek out its own vulnerabilities, understand what tactics might be used to gain entry, and what data can be accessed using those methods.
- Identify the hacker’s techniques. Having knowledge of the potential techniques that a hacker might use can provide an invaluable weapon when fighting back against cybercriminals. A near-constant gathering of information is the key to success here. Having as many external sensors as possible, as well as participation in a vocal community that is sharing information.
- Take a proactive approach. Developing a proactive approach to security is often the most effective way of protection. The sentiment “the best defense is having a good offense” really does ring true here. By taking the fight to attackers, they can be stopped in their tracks and companies can prevent breaches at the source. With more sophisticated methods being used, and a greater volume of attacks, having a strong force is mission critical.
______
______
Moral of the story:
_
-1. We are living in age where control and protection of information define power, sovereignty, and security; and information itself has become both a target and a weapon.
_
-2. Spying is the act of gathering information about someone or something without their knowledge or consent. Spying is an ancient art, born from the need to obtain information, and has become a fundamental pillar of national security and business strategy in the modern society. At its core, spying deals with the acquisition of secret information and its use or protection. However, more than that, it is a delicate and dangerous dance that requires cunning, wits and courage. Techniques and methodologies of spycraft have transcended time, space, culture, and borders. The who, what, where, when, how, and whys are all as important today as they were 7000 years ago. In ancient times spies were used as a means of gaining an advantage in conflicts and securing sensitive information. Throughout history, various civilizations have employed espionage as a tool to gather intelligence and stay one step ahead of their adversaries.
_
-3. Espionage or spying is information gathering clandestinely under false pretences for a tangible benefit. Espionage has existed for a long time. In fact, it is often referred to as the “world’s second oldest profession.” In this article, the terms espionage and spying are used synonymously although there are subtle differences. Espionage is typically associated with government or national security matters, while spying can refer to a broader range of activities, including corporate or personal matters. Espionage usually involves the use of trained agents or operatives, while spying can involve anyone who gathers information without authorization. Espionage can be legal or illegal depending on the circumstances and jurisdiction, while spying is generally considered illegal and unethical. All espionage is spying but all spying is not espionage; for example, spying on spouse is not espionage.
_
-4. Espionage can also be defined as a tool for the execution of policy as well as a tool to inform policy. This definition adequately splits espionage into its two categories: covert operations (a tool for the execution of policy) and intelligence (a tool to inform policy). The first category, covert operations, consists of active operations and cyber operations, which are actions a state takes to influence or affect a foreign sovereign that lack public endorsement by the state and usually remain classified. The second category of espionage, covert intelligence, can also be divided into two strands: collection of information and analysis of that information.
_
-5. Civilisations have engaged in espionage since biblical times as states need information on what their enemies are thinking. Espionage is the practice of obtaining confidential information by clandestine means, primarily for political, economic and military purposes. Espionage serves as a critical tool in shaping international relations by facilitating states’ understanding of each other’s intentions, capabilities, and vulnerabilities. States often engage in espionage to bolster their strategic advantage, leading to mistrust and conflict. Unauthorized sharing of sensitive data, whether intentional or accidental, can have serious and far-reaching consequences. These actions can undermine trust in government institutions, endanger lives, and spark international conflicts.
_
-6. A spy is a person employed to seek out secret information from a source secretly. He may be called agent, operative or asset. The information a spy can obtain can change the course of a war, decide the fate of a company, or even alter the direction of history. Spies may also be used to spread disinformation in the organization in which they are planted, such as giving false reports about their country’s military movements, or about a competing company’s ability to bring a product to market. Spies may be given other roles that also require infiltration, such as sabotage.
_
-7. Spies working for states fall into two categories: intelligence officers and agents. The word “spy” is used to describe both intelligence officers and those they recruit but the intelligence officer and the recruited spy are not the same. Perhaps the most crucial difference is that an intelligence officer has chosen a career. Intelligence officers have been selected on the basis of their talents and then trained to hone their skills. Recruited spies, on the other hand, are selected solely on the basis of what kind of information they have access to and are willing to hand over. Thus, recruited spies are typically expected to betray their own countries. Also called agent or asset, a recruited spy is not a professional intelligence officer, and doesn’t usually receive formal training (though may be taught basic tradecraft). An agent is someone who secretly provides information to an intelligence officer. Intelligence officers have to find, charm, befriend and motivate agents effectively to commit espionage. Agents may be recruited through money, ideology, coercion, greed, or for another reason, such as love. They trust their handler (a professional intelligence officer) to protect them.
_
-8. A double agent is an employee of a secret intelligence service for one country, whose primary purpose is to spy on a target organization of another country, but who is now spying on their own country’s organization for the target organization. They are often very trusted by the controlling organization since the target organization will give them true, but useless or even counterproductive, information to pass along. Double agents are often used to transmit disinformation or to identify other agents as part of counter-espionage operations.
_
-9. A mole is a long-term spy (espionage agent) who is recruited before having access to secret intelligence, subsequently managing to get into the target organization. Moles are double agents whose identity is so secret and his access and position are so deep that the analogy is made to an underground-living mole.
_
-10. A sleeper agent is a spy or operative who is placed in a target country or organization, not to undertake an immediate mission, but instead to act as a potential asset on short notice if activated in the future. Even if not activated, the “sleeper agent” is still an asset and can still play an active role in sabotage, sedition, espionage, or possibly treason by virtue of agreeing to act if activated.
_
-11. The targets of espionage are many including military capability, economic strength, popular sentiments, natural resources, counterintelligence, large corporations, government agencies, academic institutions, think tanks, high-ranking government officials, business executives, celebrities etc.
_
-12. The terms “espionage” and “intelligence” are often used interchangeably, sometimes even synonymously. While they are intimately connected, they are not identical. Intelligence is the collection of information that have military, political, or economic value about foreign countries or nonstate actors that are usually, though not always, enemies or opponents. The purpose of intelligence is to help policymakers make their decisions. At its core, intelligence is the lawful and structured process of collecting, evaluating, and analyzing information that is relevant to decision-making.
Espionage, by contrast, is the covert and unauthorized acquisition of protected or restricted information—most often for the benefit of a foreign entity, competing interest, or adversarial actor. It is inherently clandestine, typically illegal, and often conducted in violation of trust, law, or institutional security policies. To gain access to secret information, governments use espionage, a blend of subterfuge, deception, technology and data analysis to obtain political and military information.
All espionage produces intelligence, but not all intelligence arises from espionage. Lawful intelligence gathering can rely entirely on legal sources—open-source intelligence (OSINT), public satellite imagery (IMINT), or communications metadata within the scope of lawful SIGINT programs. Espionage, however, involves crossing a threshold: violating permissions, breaching systems, deceiving individuals, or circumventing security controls.
While espionage between states is almost universally practiced, it is also nearly always denied. In contrast, intelligence collection through OSINT or interagency cooperation may be conducted openly and with legal legitimacy. However, distinction between espionage and intelligence is often blurred.
_
-13. Intelligence is a type of information. It is data or facts regarding current, past, or future events or associations. It’s important to note that information does not equal intelligence. It is only once this information is looked at from a critical thinking mindset and analyzed that it becomes intelligence. The largest amount of intelligence work is an undramatic search of open sources and not covert sources. About 70 to 90 per cent of usable intelligence for any state is based on open-source material. For instance, in the lead-up to Moscow’s full-scale invasion on Ukraine, imagery from Maxar and collected social media posts portrayed a very public build-up of Russian forces. Although they tried, it made it difficult for Russia to refute its intentions.
Actionable intelligence is information that is processed and analyzed to provide actionable insights, enabling individuals or organizations to make informed decisions and take specific actions. This valuable intelligence has the potential to change the course of battles and save lives.
Gathering reliable intelligence allows policymakers to make informed decisions. Policymakers have limited resources, and intelligence collection provides important information on where to allocate those resources. Intelligence collection also protects national security and mitigates threats including terrorism, cyberattacks, weapons of mass destruction, and environmental threats. Accurate and timely information can help police apprehend suspects, protect targets, and reduce crime.
At the beginning of the 21st century it was estimated that the U.S. government spent some $30 billion annually on intelligence-related activities, employing perhaps 200,000 people in the United States and many thousands more U.S. citizens overseas in both clandestine and overt capacities.
_
-14. HUMINT is a category of intelligence derived from information collected and provided by human sources. Typical HUMINT activities consist of queries and conversations with people who have access to information. The way HUMINT operations are conducted is dictated by both the official protocol and the nature of the information source. Sources may be neutral, friendly or hostile and may or may not be aware of their involvement in intelligence gathering. Digital platforms allow a range of processes that can elevate human intelligence work in many ways, leading to more effective results and overcome challenges to HUMINT.
OSINT involves collecting and analyzing information from publicly accessible sources to obtain valuable insights. Obtaining the information doesn’t require clandestine effort; it is retrieved legally and meets copyright requirements. The raw data and information are then collected and analyzed to help understand something more clearly. OSINT is cost-effective, having timeliness and broad perspective, and enhances decision-making.
_
-15. Military intelligence is a military discipline that uses information collection and analysis approaches to provide guidance and direction to assist commanders in their decisions. Technological advancements have significantly transformed intelligence operations. Drones, satellites, and cyber warfare tools provide real-time data, allowing military leaders to make informed decisions swiftly. The integration of artificial intelligence further enhances analysis, offering insights into complex scenarios that humans alone may not discern. Of course human intelligence remains vital for military intelligence.
_
-16. While both stalking and spying involve monitoring someone, the key differences between the two is intent. Stalking is a crime that is committed with the intent to cause fear or harm, while spying is typically done for a specific purpose, such as gathering information.
_
-17. Snooping and spying both involve gathering information secretly, but snooping is often more casual and less intentional than spying which is a deliberate and often more sophisticated effort to gather information.
_
-18. Spying and surveillance refer to different types of actions undertaken by individuals in order to gather information about someone. Spying usually involves spying on someone without their knowledge or consent which is an illegal activity, while surveillance is often done legally with the goal of protecting public safety. Surveillance serves an important role in investigations. It is a lawful activity and is considered as evidence in court. Yes, surveillance can potentially cross the line into spying, particularly when it involves covert or illegal activities, or when it infringes on privacy without a legitimate purpose.
_
-19. Monitoring means watching or keeping track of things to make sure they are safe and working well. People do this in different parts of life, like at home, at work, or in their daily routines. The key thing is that monitoring is often done with consent and trust. There is no watching someone secretly. Spying is when someone secretly monitors people without their consent. No matter the reason, spying is a serious invasion of individual privacy and can make people feel unsafe and untrustworthy. When monitoring turns into spying, it does more harm than good. So, instead of pushing employees to perform better, it pushes them away.
_
-20. A spy collects secret information, often with a motive, while a detective investigates crimes to uncover the truth and bring perpetrators to justice. Spies operate in the shadow of intelligence agencies, while detectives work within the legal framework of law enforcement. Spies prioritize secrecy and may betray trust for their own or their organization’s gain, whereas detectives uphold the law and are generally motivated by a desire to uphold justice. Although work of detective may involve spying, detectives are not spies.
_
-21. Espionage and treason are two distinct but closely related concepts in the realm of national security and intelligence. Espionage and treason are two terms often associated with acts of betrayal and secrecy. While they both involve activities that undermine national security, they differ in their nature, intent, and legal implications. Espionage refers to the act of gathering and transmitting classified or sensitive information ‘from or for’ a foreign government or entity without authorization. It involves covert operations, spying, and infiltration of organizations. On the other hand, treason refers to the betrayal of one’s own country or government by actively aiding or collaborating with an enemy state or engaging in acts that undermine national security. Treason can take various forms, including espionage, but it extends beyond mere spying. Espionage against one’s own country can become treason. While espionage focuses on the collection and transmission of information, treason involves actively working against one’s own country. Espionage can become treason while treason can exist without espionage.
_
-22. Cover refers to the false identity or persona an agent adopts to conceal their true affiliation and activities during a covert operation. It’s a crucial element in espionage, allowing agents to operate undetected and gather information or conduct sabotage. In espionage, an official cover operative is one who assumes a position in an organization with diplomatic ties to the government for which the operative works such as an embassy or consulate. This provides the agent with official diplomatic immunity, thus protecting them from the steep punishments normally meted out to captured spies. In espionage, operatives under non-official cover (NOC) are operatives without official ties to the government for which they work who assume covert roles in organizations. Operatives under non-official cover do not have ‘safety net’, and if captured and charged as spies are subject to severe criminal punishments, up to and including execution.
_
-23. The U.S. government defines covert action as activities aimed at influencing political, economic, or military conditions abroad, all while concealing the U.S. role. Covert action hinges on the principle of plausible deniability, which enables governments to deny involvement in specific measures. The CIA has long served as the primary agency behind U.S. covert action. Those activities have included assassination attempts, efforts to spark coups, cyberattacks, and drone strikes. Many countries use covert action to achieve foreign policy goals. In a covert operation the identity of the sponsor is concealed, while in a clandestine operation the operation itself is concealed. Put differently, clandestine means ‘hidden’, where the aim is for the operation to not be noticed at all. Covert means ‘deniable’, such that if the operation is noticed, it is not attributed to a group.
_
-24. The old way of spying has become obsolete due to technology. Technology significantly enhances espionage methods including cyber espionage, providing innovative tools for intelligence gathering and political influence. Advanced surveillance systems, data analytics, and artificial intelligence facilitate the collection and analysis of vast amounts of information, enabling operatives to anticipate political movements effectively. With the Internet of Things connecting numerous devices, espionage actors exploit these connections to infiltrate government and corporate systems, jeopardizing sensitive data.
On the other hand, the devastating penetrations of CIA spying networks in recent years were not mainly about incompetence or inattention but due to technology revolution that makes it all but impossible to maintain false identities and disguise relationships. Everyone spews “digital dust” that reveals key facts about their movements, patterns of life and associations.
_
-25. Spies spy on bad guys. That seems like the no.1 rule of spying. But everybody spies on everybody, including friends on friends. All countries spy; however, some countries are better equipped for the practice than others. One expert said the United States, for instance, has the equivalent of a “nuclear weapon” in its intelligence armoury compared to most other countries, which are stuck with the equivalent of cannons.
_
-26. Little is publicly known about spies; espionage is by nature secret, and much of what the public “knows” about the life of a spy comes from fiction and film. This secrecy is by necessity a major part of a spy’s life; they must lie to close friends and family in order to keep their occupation secret. One of the most challenging aspects of being a spy is maintaining a double life. Whether working undercover abroad or operating domestically, spies must live in constant secrecy. Protecting their identity is a crucial part of a spy’s job, and there are several techniques spies use to keep their true identity a secret. First, spies often adopt a “cover identity”. Second, spies adhere to strict information security standards. In addition, spies use a variety of techniques to avoid detection and surveillance. This can include changing their appearance and routine frequently, using counter-surveillance (techniques to detect and evade surveillance), and using secure and encrypted communications.
_
-27. Espionage involves actions that would be unacceptable in other contexts, such as lying, betraying, stealing, or even assassination. Spies have a terrible reputation. As agents of deception and theft, they arouse suspicion and anger wherever they go. While not all spies are involved in high-stakes missions, the job is inherently dangerous. Operatives working undercover face the constant threat of burnout, exposure, imprisonment, torture or worse.
_
-28. The spy will usually have contact with no one else except his handler, never learning the names of any other spies or officials. This is known as compartmentalization. Each spy works within his own compartment, so if he is captured and interrogated, he can’t reveal vital information or the identities of other spies.
_
-29. As long as wars have been waged on this earth, captors have taken the right to question captives. As long as POWs are interrogated, they will talk. No patriotism, no self-control, no logic gives any man enough strength to repel relentlessly pressed attacks utilizing accumulated combinations of facts and circumstantial evidence.
Scharff Technique entails carefully orchestrated, outwardly friendly exchanges with prisoners rather than compelling prisoners to reveal classified data through the employment of coercive methods. Scharff’s approach bears strong similarities to the psychological concept of perspective taking: the cognitive capacity to consider the world from another’s viewpoint, which facilitates the anticipation of other people’s behavior and reactions. The ability to take the perspective of others is predictive of success in negotiations, and, due to their inherent similarities, likely to be of importance also for interrogators.
_
-30. Soviets were unparalleled in their attempts at subversion. Agents ran worldwide peace congresses, festivals, women’s movements, and so forth, with the intention of creating discord and weakening the West. Many spies were responsible for disseminating fake information, forgeries, and rumours, such as the rumour that AIDS was invented by the CIA.
_
-31. What motivates someone to become spy:
Different things motivated different spies: money, ideology, patriotism, achievement, coercion, compromise, ego, disgruntlement, revenge, disenchantment, ingratiation, thrill, excitement, self-importance, affiliation, personal failure, etc.
People aren’t spying for ideology anymore because there’s not really any ideology there to spy for. It’s just money. For some, espionage is an opportunity to secretly manipulate people around them and to prove their superiority. Foreign intelligence organizations often target and turn individuals to pass classified material who have become romantically involved with a foreign agent. Unlike coercive “Honey Traps,” the espionage is often based on genuine bonds of affection between the target and her “Romeo.”
_
-32. Spy tactics:
Espionage techniques encompass a wide range of methods used to gather information secretly. These include covert surveillance, eavesdropping, and the use of various technologies and strategies like steganography, dead drops, and cyber espionage. Deception and psychological manipulation are also employed, such as false flag operations and honey trapping. At its core, spy tactics involve skills such as disguise, source cultivation, secret communication, physical training, observation, analysis, counterintelligence, operational security, and technical proficiency. These skills collectively enable spies to blend into their surroundings, gather valuable intelligence, and carry out missions undetected.
_
-33. Spies spend as much time feeding false information to their enemies as they do gathering information. This keeps enemy guessing, forces them to miscalculate military capabilities and commit forces to the wrong area. A steady stream of misinformation can even damage the real information the enemy has, because they will begin to doubt the authenticity of their own intelligence gathering activities.
_
-34. Sexpionage refers to the use of sexual activity, intimacy, or seduction as a tool in espionage, often involving agents or operatives using their relationships to extract information or manipulate targets. Sexpionage is a potent spying tool. What explains rampant use of sexpionage and honeytraps is the psychology of human vulnerability. Intelligence agencies know that love can often conquer patriotism. Humans are wired for attachment. Emotional bonds, once formed, can override logic and ethical considerations. A target who believes he or she is in love or deeply romantically connected to someone is less likely to question that person’s motives. This emotional fog dulls suspicion and sharpens loyalty — even to the enemy nation’s cause. Illicit sexual encounters can carry with them a burden of secrecy, fear or shame. Spies exploit this by recording liaisons or extracting compromising information during moments of vulnerability. The resulting “kompromat” (compromising material) can be used for blackmail or coercion. On the other hand, spies themselves can also be entrapped by sexual lures.
_
-35. Social engineering is the use of psychological influence of people into performing actions or divulging confidential information. All social engineering techniques are based on exploitable weaknesses in human decision-making known as cognitive biases.
_
-36. Equipped with tiny cameras, spy pigeons could easily access otherwise restricted areas and “take photos” without arousing suspicion before safely returning to home base using their extraordinary homing ability.
_
-37. Fusion technology means all data streams from security cameras, license plate readers, smartphone trackers, and drones are fused into one. Fusion architectures are central to the Chinese government’s campaign against dissidents and minority citizens, particularly the Uighur Muslim group.
_
-38. Corporate or industrial espionage is stealing proprietary information, trade secrets, or intellectual property from a business and giving or selling it to another. The primary intent behind corporate espionage is to use the acquired information to gain a competitive advantage. Ultimately, industrial espionage can harm any business, causing financial losses, hindering competitiveness, and damaging reputation. Reportedly Canada is losing $12 billion and German companies are estimated to be losing about €50 billion ($87 billion) and 30,000 jobs to industrial espionage every year.
Economic espionage is defined as government-directed, sponsored, or coordinated intelligence activity conducted for the purpose of enhancing that country’s or another country’s economic competitiveness. The primary targets are trade secrets, confidential business plans, innovative technologies, manufacturing processes, and other forms of intellectual property. Foreign economic espionage against the United States continues to represent a significant threat to America’s prosperity, security, and competitive advantage. China, Russia, and Iran stand out as three of the most capable and active cyber actors tied to economic espionage and the potential theft of U.S. trade secrets and proprietary information. China’s development in automotive, aircraft, information technology, high-speed trains, and defense industries all benefitted from economic espionage.
Note:
Industrial/corporate espionage is between industries/corporations while economic espionage is between nations and state sponsored.
_
-39. The term academic espionage can be defined as violating core principles of integrity by the practice of obtaining, using, or distributing the information, data, or methods that are used in the university’s research enterprise through unethical, dishonest, or illegal means to unauthorized individuals, companies, or nation states. The blend of cutting-edge research, access to sensitive information, and ambitious scholars makes universities prime targets for espionage. Chinese nationals working at prestigious universities and institutions have repeatedly been caught transferring sensitive data, proprietary algorithms, and advanced research back to China.
_
-40. Nuclear espionage is the purposeful giving of state secrets regarding nuclear weapons to other states without authorization. Soviet spies occupied positions of trust and importance in the Manhattan Project between 1942 to 1947, and passed on valuable information about the atom bomb and its design. It is nuclear espionage that gave Pakistan its atom bomb. In order to tempt nuclear scientists from countries such as Iran or North Korea to defect, US spy agencies routinely send agents to academic conferences – or even host their own fake ones.
_
-41. Alarmingly, 40% of the divorce cases now include instances of one spouse spying on the other. Emails, texts, and Facebook posts are being called on as evidence in an increasing number of divorce proceedings. Recognising the signs of a spying partner can be challenging. The misuse of technology to spy on a spouse is a form of coercive control that disregards people’s right to privacy.
_
-42. Cyber Espionage is the act of using digital tools and techniques to unlawfully obtain sensitive, classified, or proprietary information from an individual, organization, or government. The information targeted typically holds strategic, military, economic, or political value, and its unauthorized access can lead to significant damage to the entity from which it was stolen. Cyberspace has unique qualities that make it appealing to nation-states and non-state actors to indulge in cyber espionage. Cyber espionage is difficult to detect; the perpetrators can hardly be successfully prosecuted. It can take months or years for victim organizations to learn about the attack.
Large enterprises, government agencies, academic institutions, think tanks, and other organizations that have significant intellectual property and technical data that can give another organization or government a competitive edge are the most frequent targets of cyber espionage. But cyber espionage is also a viable tool to combat terrorist groups.
Governments engaging in cyber espionage have sophisticated capabilities and vast resources at their disposal. These nation-state actors can be motivated by a variety of reasons, including national security, economic competition, or geopolitical influence. Prominent nation-states involved in cyber espionage include the United States, China, Russia, and North Korea. Until recently, the United States probably lost between $20 billion and $30 billion annually from Chinese cyber espionage with cumulative cost may reach $600 billion, since this kind of espionage has been going on for more than two decades. North Korea’s cyber espionage has stolen approximately three billion dollars’ worth of cryptocurrency between 2017 and 2023 to fund its nuclear weapons program.
Cyber espionage and cyber intelligence are related but distinct concepts. Cyber espionage is the act of gathering sensitive information, often for strategic advantage, through cyber means. Cyber intelligence, on the other hand, is the process of gathering, analyzing, and disseminating information about cyber threats to improve an organization’s security posture. In essence, cyber espionage is a specific type of malicious activity, while cyber intelligence is a broader field focused on security and defense.
_
-43. Ethics of spying:
Spying can violate privacy rights, undermine trust between individuals and organizations, and create tensions between nations. Espionage involves a set of practices—such as deception, betrayal, and intrusion—that are ethically contentious in most other contexts. Ethically, the practice of espionage can infringe on personal privacy and sovereignty. Ethical considerations include the potential harm caused to innocent individuals and the broader implications on civil rights. The balance between security and privacy emerges as a critical issue in addressing espionage risks. As governments enhance surveillance and intelligence capabilities to counter threats, they must also safeguard individual rights and freedoms, creating a complex dynamic. In light of the ethical complexities surrounding espionage, it is crucial to have robust oversight mechanisms in place to ensure that intelligence agencies operate within legal and ethical boundaries.
_
-44. Open vs closed society:
The United States, Canada, the nations of Western Europe, Japan, Australia, and New Zealand were and are open societies. Nearly all of their political, social, and economic activities are carried out under the glare of public scrutiny and media reporting. Open societies have few secrets except for those they find necessary to classify for security reasons. Under these conditions agents from hostile nations find it relatively easy to establish spy networks. During the Cold War it was easier for spies from the Soviet Union and its allies to work in the United States, Western Europe, and Japan than it was for American or other Western spies to gather information in the Soviet Union, China, and the Eastern-bloc nations. The Soviet Union was a closed society. Every area of public life was under government control, and private lives were always subject to government surveillance. All publications were monitored, and there was little access to information that the government did not want released. For any nation to set up an elaborate spy network within the Soviet Union was virtually impossible.
_
-45. Intelligence failure:
An intelligence failure occurs when intelligence organizations or agencies fail to provide accurate and timely warnings of potential threats or opportunities, leading to strategic miscalculations or inadequate responses. The withdrawal from Afghanistan was an intelligence failure. Not only did the CIA and other U.S. intelligence agencies wildly underestimate the speed of the Taliban advance, they also appeared to have been blind to the political dealings of the Taliban and the military prepositioning the Taliban had achieved. Meeting in the White House in 2002, CIA director George Tenet told President Bush, the evidence that Iraq possesses weapons of mass destruction amounts to a slam dunk case. And of course, America invaded the next year, and WMDs weren’t there. Saddam Hussein had persuaded everyone in Iraq, his generals, his family, that he did have weapons of mass destruction. And if everybody believed something that’s untrue, whether it’s untrue or not, it’s very, very hard for intelligence to pick that up. Observers often claim that successful intelligence operations remain secret, while those that go awry become public knowledge. That argument suggests the world hears far more about instances when spies and other operatives get it wrong than when they get it right.
Too much information:
The history of espionage is a lesson in paradox: the better your intelligence, the dumber your conduct; the more you know, the less you anticipate. In this age of digitalization and technology, intelligence agencies across the globe process massive amounts of information about individuals, sub-state actors, and governments every day. Intelligence experts and military leaders often assume that the goal of intelligence work is to gather as much information as possible in order to formulate a more comprehensive picture of the world. However, this aggressive intelligence gathering does not make for better-informed government agencies or higher quality security policy. Instead, excessive information collection leads to information overload on both the individual and institutional levels, impairing intelligence community’s ability to do its job.
Too much secrecy:
(1. Overclassification occurs either when information is classified but should not be, or when information that is classified should be classified at a lower level. Officials who decide whether to classify documents and how strictly to limit their circulation face virtually no consequences if they classify a document whose contents did not warrant such a designation. On the other hand, those officials are punished severely for failures to classify sensitive information. This leads decision makers to err on the side of caution, choosing to classify documents at higher levels in uncertain cases. The result is massive overclassification and institutional failure to make information available where and when it is needed. Overclassification has become an obstacle to intelligence sharing across agencies, potentially leaving analysts in the CIA without easy access to necessary information gathered by the NSA (or other agencies), and therefore diminished ability to formulate an accurate picture of the world around us. Overclassification prevented US intelligence analysts from making the right connections in the months and days leading up to the terrorist attacks of September 11th, 2001; the 9/11 Commission later blamed those intelligence gaps on “overclassification and excessive compartmentalization of information among agencies.”
(2. Having found a way to collect intelligence yourself, you become convinced that the other side must be doing the same to you, and is therefore feeding you fake information in order to guide you to the wrong decisions. Pervasive secrecy rules out the small, mid-course corrections that are possible in normal social pursuits. When you have to prevent people from finding out what you’re doing and telling you if you’re doing it well, you don’t find out that you didn’t do it well until you realize just how badly you did it.
_
-46. States make decisions about entering, exiting, and preparing for war based on their perceptions of the international system, their views of how power is distributed, and their understandings of what capabilities other states have. All of these assessments are shaped by the intelligence states receive. War is costly for both winners and losers, which seems to suggest that it is irrational for two states to wage war. One prominent explanation for the existence of war, then, is that states act rationally but make mistakes due to imperfect information. Historically, there have been many wars founded on misinformation or incomplete intelligence—conflicts which could have been avoided by better intelligence work.
_
-47. Counterintelligence can be defined as the collective of measures undertaken to identify, deter, exploit, degrade, neutralise, and protect against adversarial intelligence activities deemed as detrimental or potentially detrimental to one’s own interests. It includes gathering information and conducting activities to prevent espionage, sabotage, assassinations or other intelligence activities conducted by, for, or on behalf of foreign powers, organizations or persons.
Conducting intelligence without having a strong counterintelligence program puts an agency, organisation, or nation at a great disadvantage over their adversaries. Intelligence, the art of espionage, seeks to uncover state, corporate, or military secrets, using moles, intercepted signals, or cyber hacks to peer into enemy plans. Counterintelligence, its relentless counterweight, protects those plans, hunting moles, fortifying defences, and planting disinformation to mislead foes. Counterintelligence is also concerned with protecting advanced technology, deterring terrorism, and combating international narcotics trafficking.
_
-48. While “mass surveillance” is often used to refer to government spying on people, today it involves a complex grouping of federal agencies, local police, private companies, and even members of the public. Many reasons why the government spies on citizens include: Fighting terrorism, Preventing and combating crime, Protecting national security, Law enforcement investigations and Political intelligence.
The events of 9/11 have been used to dramatically expand the government’s mass surveillance authorities. The U.S. used post-9/11 terrorist fears to expand its monitoring of U.S. citizens who have nothing to do with terrorism. You don’t have to be on the FBI’s most wanted list, a known terrorist, or an enemy of the state to be monitored by the government. The government collects information about regular citizens, too. That’s why it’s important to be proactive about protecting your privacy.
Mass surveillance can compromise personal privacy, right to freedom of expression & association, civil liberties, and prevents us from progressing as a society. Routine surveillance is corrosive, making us feel like we are always being watched, and it chills the very kind of speech and association on which democracy depends. Surveillance creates an environment of fear and distrust. Such scenarios can exacerbate societal divisions, fostering resentment toward authorities and government institutions.
_
-49. Under international law, the act of spying, or espionage, describes an act of information gathering that is clandestine or takes place under false pretences. Spying, or espionage, is generally illegal under international law and the domestic laws of most countries. Espionage against a nation is a crime under the legal code of many world states. In a world where intelligence can provide significant advantages in diplomacy, military operations, and economic competition, countries often prioritize national security over strict adherence to laws against spying. If a spy is caught, the outcome depends on the country, the severity of the espionage activities, and the relationship between the spy’s home country and the country where they were caught. A spy breaking the host country’s laws may be deported, imprisoned, or even executed. A spy breaking his/her own country’s laws can be imprisoned for espionage or/and treason, or even executed.
_
-50. International law treats spying that occurs during wartime and peacetime differently. The rules on wartime spying focus on whether the information gathering is carried out through false pretences. In peacetime, the analysis centers on whether the methods of spying violate a state’s sovereignty. During an armed conflict, an individual who engages in espionage loses his/her right to prisoner of war status, including the protections around accommodation and access to food, clothing, hygiene and medical care. During peacetime, the position of espionage is more ambiguous. No treaty exists regulating the use of covert agents for the purposes of gathering intelligence. It is even difficult to determine the proper scope of what constitutes ‘espionage’ for the purposes of international law – for instance, whether espionage covers also diplomats that attempt to uncover sensitive information of the receiving state to disclose it, or even journalists that clandestinely leak information to a foreign State.
_
-51. Spy cameras and microphones are relatively inexpensive, accessible, and smaller than ever. Thus, they are also easily installed and hidden. The use, sale and purchase of spy cameras are legal when they are used legally. One can use it for security purposes at home or in offices, to keep an eye on infants at home, record lawful entertainment like pranks, and to collect evidence of any illegal activity.
_
-52. Duality of spying:
Spying is filled with dualities that make it hard to regulate. We have to protect ourselves from surprise attacks in a world where there’s growing uncertainty around safety and security. So spying is a must although lies, cheating, and deceiving do come with espionage. We say it’s illegal to spy in the territory of another state without its consent, but everyone does that. We say it’s illegal to spy from embassies, but every country spies from embassies. We tell our spies to violate the laws of other countries but to comply with ours. We treat spies as heroes at home but traitors abroad. When we spy on someone, it is in national interest but when someone spies on us, it is treachery. All these dualities seem to suggest that there’s just something queer about this practice. Everyone’s doing it, but everyone’s saying it’s illegal under their own domestic legislation. It is hard to imagine how espionage can ever be regulated. For law to be effective, parties must either trust each other to abide by the law or be able to verify each other’s compliance. Given that either alternative is unlikely in the case of espionage, the prospects for future international regulation seem dim.
_
-53. An intelligence agency is a government agency responsible for the collection, analysis, and exploitation of information in support of law enforcement, national security, military, public safety, and foreign policy objectives. Intelligence agencies form the backbone of national security systems worldwide, operating in the shadows to protect their nations’ interests. Their work has shaped history, determined the outcomes of wars, and influenced global politics in profound ways. Examples of intelligence gathering organizations include government agencies like the CIA, MI6, FSB. and MSS, as well as private companies that provide intelligence services to businesses and individuals.
_
-54. Mossad is one of the most secretive and formidable espionage organisations in the world. Operating well beyond Israel’s borders, Mossad is responsible for gathering foreign intelligence, conducting counterterrorism operations, and executing covert missions that influence global geopolitics. Whether through exploding walkie-talkies, doctored toothpaste, or remote hacks, Mossad’s tactics continue to evolve in a world of hybrid warfare.
Israel carried out a surprise attack on Iran recently, targeting high-level military and nuclear assets with extraordinary precision. Using a combination of human intelligence and advanced AI, Israeli forces smuggled drones and launched airstrikes that crippled Iran’s air defences and eliminated key generals and scientists.
_
-55. Pakistan’s ISI is the largest of the country’s three intelligence services and primarily operates as a military intelligence agency. An important ally for Western intelligence with whom it has very close links, the ISI also has a long history of involvement in supporting and promoting terrorism in the name of Pakistan’s geostrategic interests. The ISI has often been accused of playing a role in major terrorist attacks across India. The ISI is also accused of supporting Taliban forces and recruiting and training mujahideen to fight in Afghanistan and Kashmir.
_
-56. The psychology of spying encompasses the study of how spies think, behave, and are motivated, as well as the psychological strategies they employ to gather information and achieve their objectives. Spies often leverage trust, empathy, and vulnerability to build relationships and gain access to secrets. The psychological toll of espionage reaches far beyond the agents themselves, spreading ripples of betrayal, paranoia, and mistrust to the individuals and organizations they target. Chronic stress, compounded by the ever-present threat of exposure, can lead to burnout and post-traumatic stress disorder (PTSD) among spies. Given the immense psychological challenges faced by spies, many intelligence agencies now prioritize mental health support for their operatives. Counselling, decompression programs, and reintegration strategies are increasingly recognized as essential tools for helping spies cope with the demands of their work.
_
-57. Traditional human intelligence gathering — using spies and clandestine operations to pry loose secrets are not irrelevant in AI age. Human intelligence will always be important, but machine learning can free up humans for tasks that they’re better at. Satellites and AI algorithms are good at counting the number of trucks on a bridge, but they can’t tell you what those trucks mean. You need humans to figure out the wishes, intentions, and desires of others. The less time that human analysts spend counting trucks on a bridge, the more time they will have to figure out what those trucks are doing and why. AI not only reduces human error, but can serve to complement human decision-making. The integration of AI into intelligence operations offers the potential for increased efficiency, enhanced data analysis, and improved threat detection.
However, AI also introduces serious concerns about accessible and comprehensive mass spying, enhanced state-sponsored cyber espionage, enhanced scale and accuracy of cyber-attacks, threat to data security, threat to job security, and the human rights risks of unpredictable combat outcomes.
_
-58. US intelligence and law-enforcement agencies have access to all information on all major social networks and many Internet-based companies. Facebook, Google, Yahoo – all these major US organizations have built-in interfaces for US intelligence. Everyone should understand that when they add their friends to Facebook, they are doing free work for United States intelligence agencies in building this database for them. Many governments are spying on smartphone users by compelling Apple and Google to turn over push notification records. Push notifications like news alerts, emails and social media alerts travel through Apple’s and Google’s servers, they can reveal unique insights about how individual people use particular apps.
_
-59. Spyware is malicious software that enters a user’s computer/smartphone, gathers data from the device and user, and sends it to third parties without their consent. Smartphone spyware apps that allow people to spy on each other are not only hard to notice and detect, they also will easily leak the sensitive personal information they collect. When security forces use spyware, it must be within clearly defined borders. The security forces need advanced technological tools in order to face threats such as terrorism, organised crime or attacks against the constitutional order. Spyware must not be used as a political weapon against democratic institutions, politicians or journalists.
_
-60. There’s no concrete evidence of widespread spying by TikTok.
_
-61. Spy vs diplomat:
Espionage has been part of diplomacy since the beginning of statecraft. The main purpose of espionage is to collect information of the host State and communicate it to the sending State. Spies and diplomats are different in four respects. First, spies do not disclose their status to the receiving State, as their operation is covert. Second, unlike diplomats, spies do not only seek to ascertain ‘conditions and developments’ in the receiving State, but also to uncover confidential and highly sensitive information that the receiving State does not make readily available (for instance, national security information). Third, unlike diplomats, spies do not necessarily employ lawful means in that endeavour. Finally, diplomats have multiple functions aside from information collection. But, sending spies under the guise of diplomats is an abuse of diplomatic immunity and privileges.
_
-62. Spy swaps are example of surveillance diplomacy to advance broader political and diplomatic goals. The U.S. and the Russians (and the Soviets before them) have engaged for years in spy swaps.
_
-63. The antidote to secret intelligence is transparent diplomacy. Resisting the urge to hoard secrets helps reduce fear that others are cheating on agreements, shirking their obligations or plotting military aggression. National security does not flow from espionage and subterfuge but from open diplomacy. Trust should be the basis of international relations and not distrust. Trust is better than lies, cheating, and deceiving that come with espionage.
______
Dr. Rajiv Desai. MD.
July 20, 2025
______
Postscript:
Decades ago, a movie star apparently fell in love with me. Her father was opposed to such relationship. He engaged a private detective to spy on me. The private detective found me of loose character because of mistaken identity. Detective spied on another individual resembling my identity. Her father leaked my loose character credential to a media house. That media house started conducting sting operations (spying) against me under pretext of media research and also leaked my loose character credential to other media houses; who also started conducting sting operations (spying) against me under pretext of freedom of press. None of the media houses ever questioned me. This is how my character assassination began due to spying.
_____


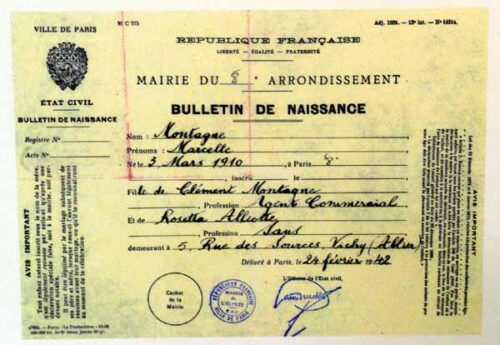


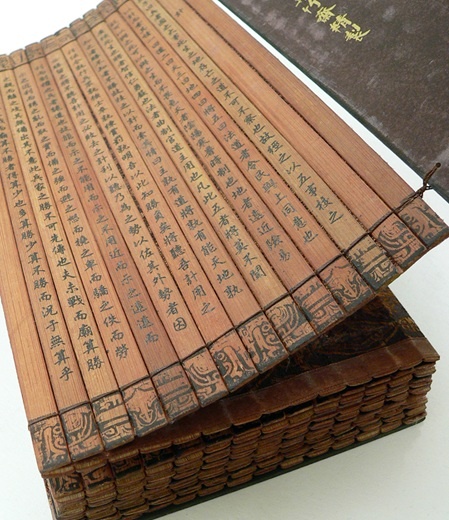
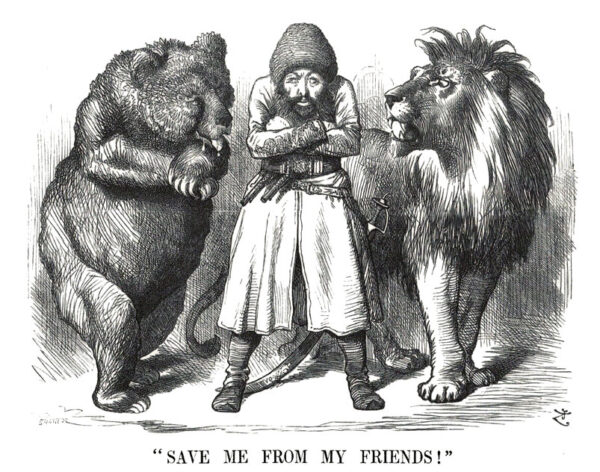


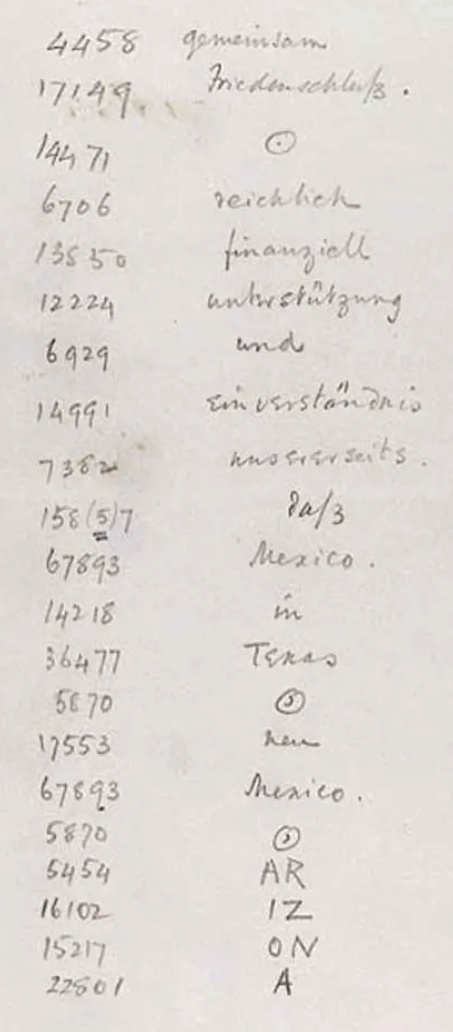
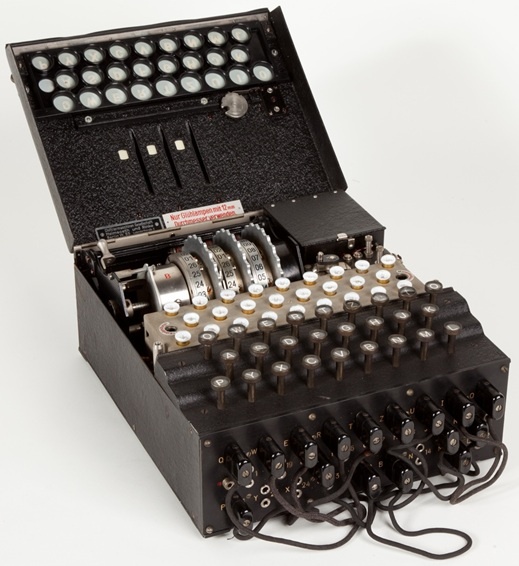
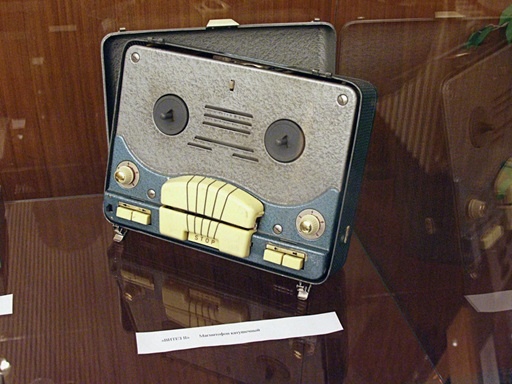

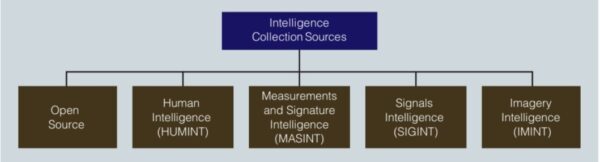
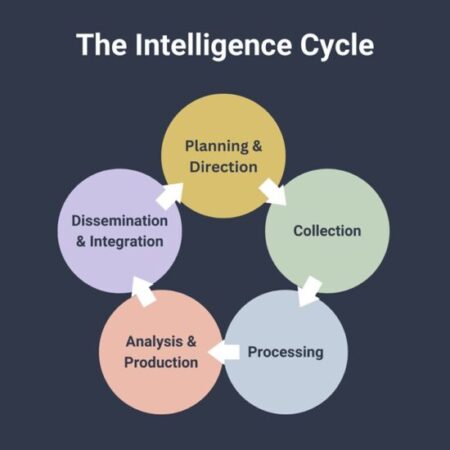
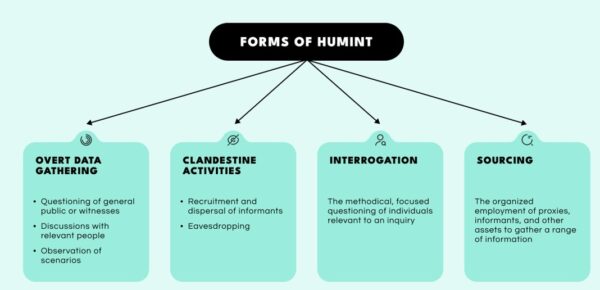
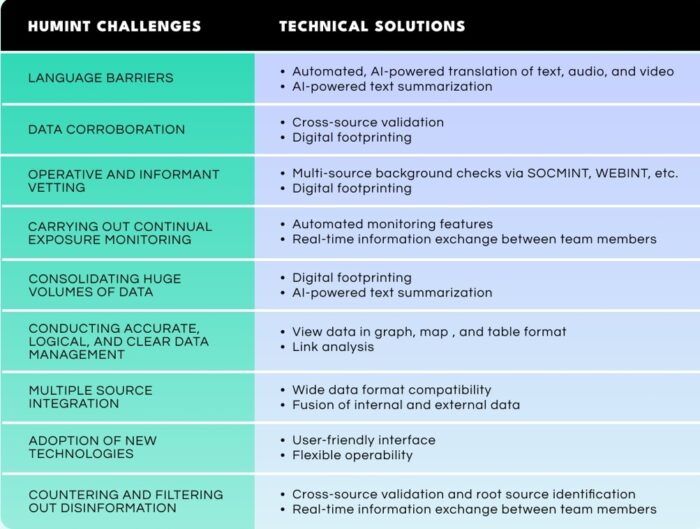
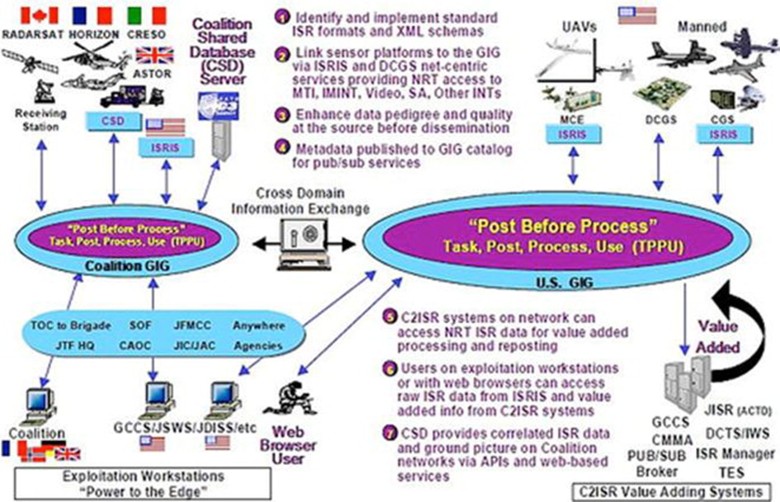
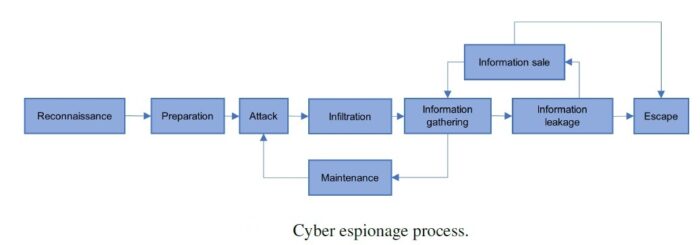
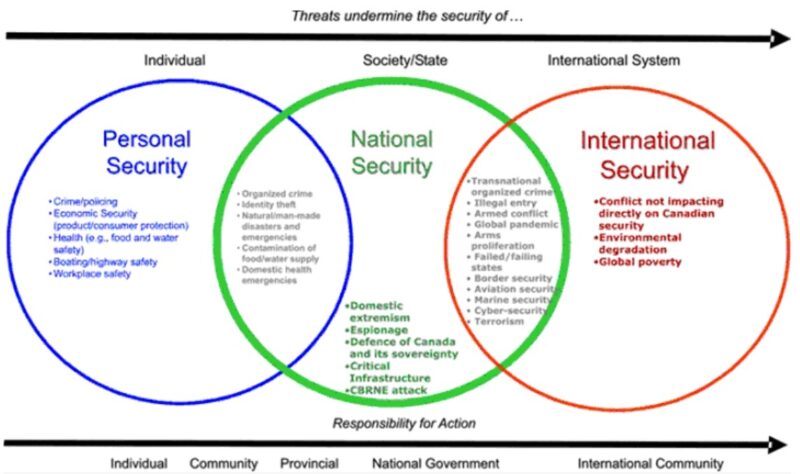
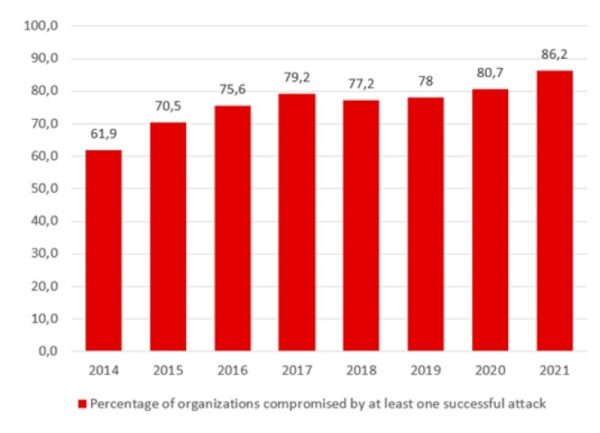

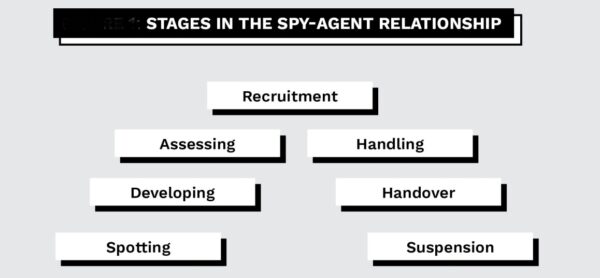
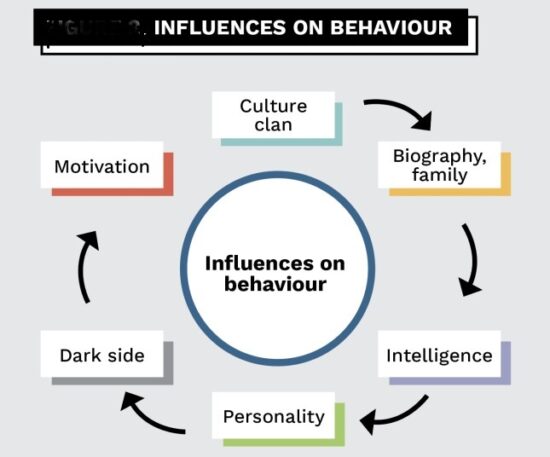
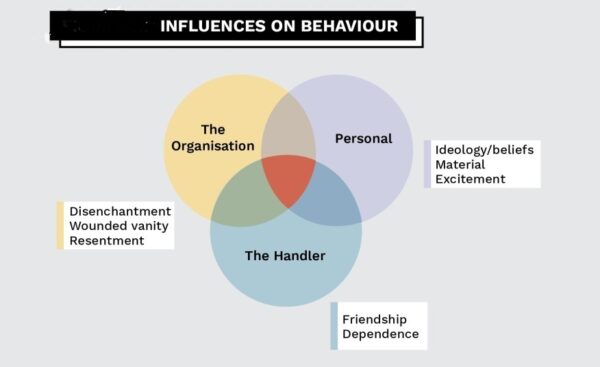
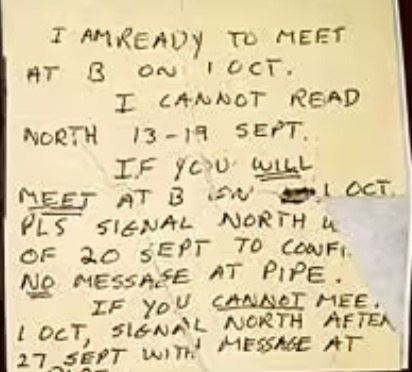
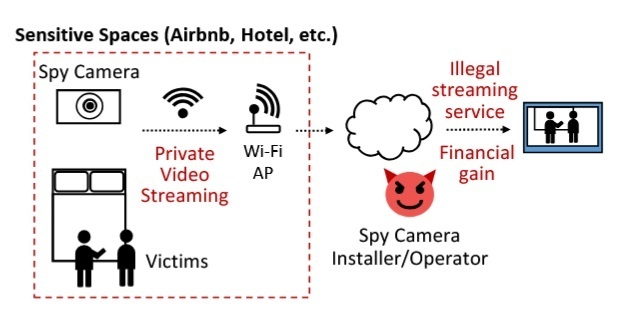

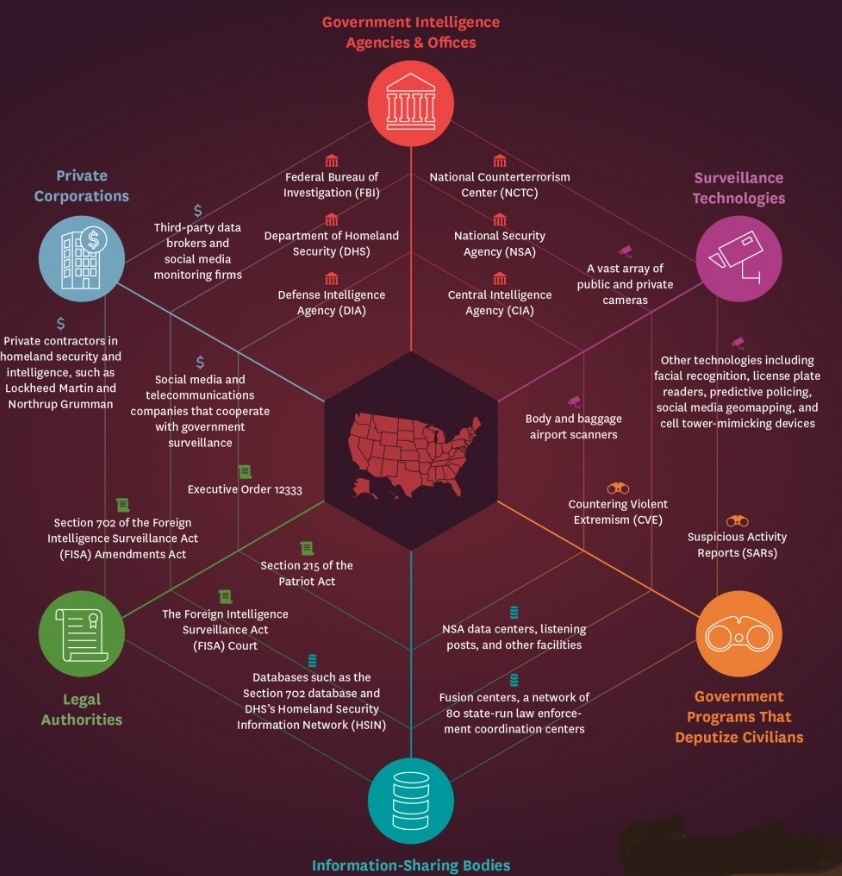


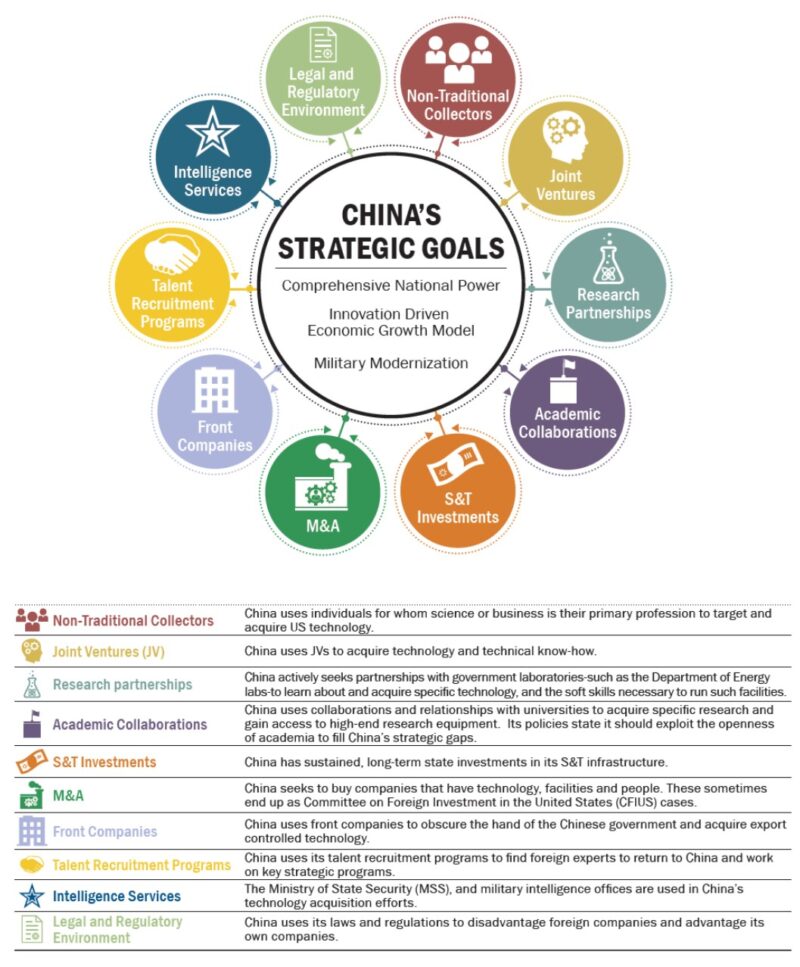

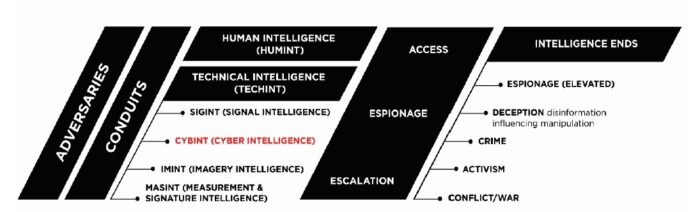

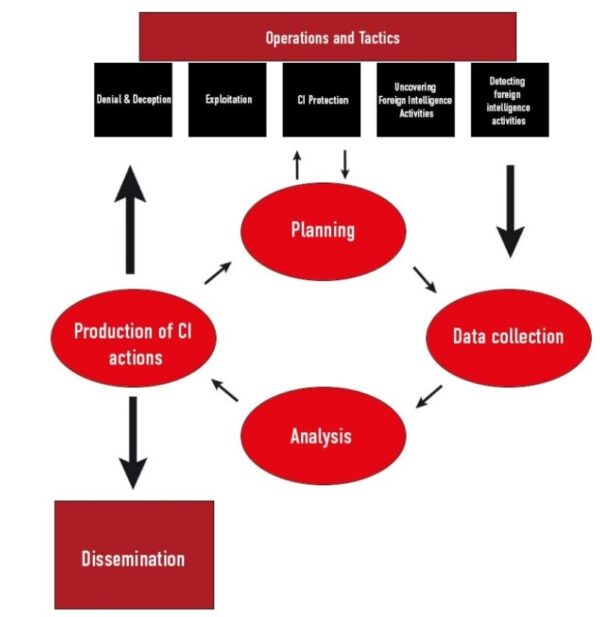

Preparati a vivere l’esperienza Crazy Time al massimo, tra slot, bonus e statistiche live dal cuore dell’Italia.
Crazy Time rimane uno degli spettacoli piu discussi del panorama dei casino online in Italia, grazie alla sua energia, varieta e potenziale payout alto.
crazy time italia live [url=https://www.lenoralivingston.com/]https://lenoralivingston.com/[/url]
[url=https://40superhott.com]40 super hot slots[/url] offers incredible chances to win and an exciting gaming experience!
In conclusion, “40 super hot” is more than just a phrase.
Download [url=https://minecraft-download1.com]1.21.130.26[/url] and immerse yourself in the exciting world of creativity!
Make sure to review the system requirements prior to initiating your download.
Whether you’re a novice or an experienced bettor, the app has something to offer everyone.
1win .com [url=https://www.1win-app-apk.com]https://1win-app-apk.com/[/url]
[url=byfurniture.ry]Дизайнерская мебель премиум класса[/url] — это воплощение изысканного стиля и безукоризненного качества.
Нельзя недооценивать значение премиум класса в дизайне интерьеров. Каждый элемент интерьера должен быть осмысленным и гармонично вписываться в общую концепцию. Инвестиции в качественную мебель — это вложение в комфорт и уют вашего дома.
Этот информативный материал предлагает содержательную информацию по множеству задач и вопросов. Мы призываем вас исследовать различные идеи и факты, обобщая их для более глубокого понимания. Наша цель — сделать обучение доступным и увлекательным.
Получить больше информации – https://quick-vyvod-iz-zapoya-1.ru/
В Москве к вашим услугам скорая наркологическая помощь от Narcology Clinic — выезд врача 24/7, качественная помощь при алкогольной интоксикации, стабилизация состояния и организация дальнейших этапов детоксикации.
Подробнее можно узнать тут – [url=https://skoraya-narkologicheskaya-pomoshch15.ru/]наркологическая помощь телефон москве[/url]
На [url=https://metallicheskij-shtaketnik.ru/]metallicheskij-shtaketnik.ru[/url] вы можете рассчитать стоимость забора с помощью онлайн-калькулятора. Укажите длину, высоту и желаемый цвет – система автоматически покажет итоговую цену. Для точного расчета рекомендуем вызвать замерщика.
5sphgs
What i don’t understood is in reality how you’re not really much more
well-liked than you might be right now. You’re very
intelligent. You recognize thus considerably when it comes to this topic,
produced me in my opinion imagine it from numerous various angles.
Its like men and women are not fascinated except it’s one thing to accomplish with Woman gaga!
Your personal stuffs excellent. Always maintain it up!
Лучшие ИБП для бизнеса, в статье.
Рейтинг лучших ИБП, ознакомьтесь.
Почему стоит купить ИБП, в нашем материале.
Рекомендации по выбору источников бесперебойного питания, в нашем гиде.
Источники бесперебойного питания: что важно знать, разберитесь.
Как не ошибиться при выборе ИБП, в нашем блоге.
Ваш идеальный ИБП, в анализе.
Как работает источник бесперебойного питания, в этой статье.
Эффективное использование ИБП, узнайте.
Тенденции рынка источников бесперебойного питания, узнайте.
Как правильно подключить ИБП, в нашем гиде.
ИБП для дома и офиса: выбор и рекомендации, узнайте.
Источники бесперебойного питания: советы и хитрости, узнайте.
Сравнение ИБП: какой выбрать?, узнайте.
Как установить источник бесперебойного питания?, в нашем материале.
Идеальные решения для бесперебойного питания, в гиде.
Как продлить срок службы ИБП, узнайте.
Как выбрать ИБП для игры, читайте.
Топ-10 источников бесперебойного питания на рынке, в нашем блоге.
источники бесперебойного питания цена [url=https://istochniki-bespereboynogo-pitaniya.ru#источники-бесперебойного-питания-цена]https://istochniki-bespereboynogo-pitaniya.ru[/url] .
You have made some really good points there. I looked on the internet
for additional information about the issue and
found most people will go along with your views on this
web site.
I have been surfing online more than three hours today, yet
I never found any interesting article like yours. It is pretty worth enough for me.
In my view, if all webmasters and bloggers made good content as you did, the net will be much more useful than ever before.
What i do nott realize is in reality how you’re no longer really a
lot more well-liked than you may be right now.
You are so intelligent. You know thus considerably with regards tto
this topic, produced me personally believe it
from a lot of various angles. Its like women and men aren’t interested except iit
is one thing to accomplish with Girl gaga! Your personal stuffs great.
At all times maintain it up!